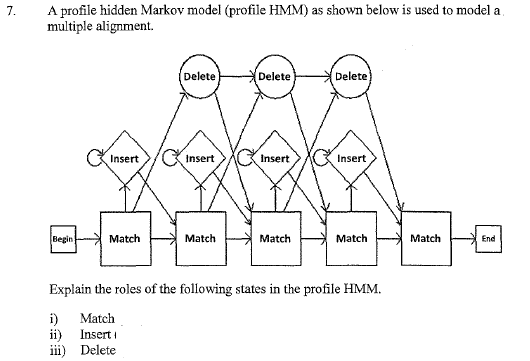
7. A profile hidden Markov model (profile HMM) as shown below is used to model a multiple alignment. Delete Delete Delete Insert Insert Insert Insert Begin Match Match Match Match Match End Explain the roles of the following states in the profile HMM. i) Match ii) Insert iii) Delete
Q: Hi there, I'm struggling with this question because I find the concept of Turing machines…
A: a) {w| w contains an equal number of 0s and 1s} :The Turning Machine should follow the steps:Search…
Q: QUESTION 1 Who was the Intel Executive who said the performance of hardware will double every year…
A: The evolution and growth of the technology industry have been driven by visionary leaders,…
Q: can you help me answer this question because I am struggling, can you help me with this and can you…
A: The objective of the question is to design a Turing machine that can compute the product of two…
Q: Write Java statements to accomplish each of the following tasks: a) Display the value of element 6…
A: The objective of the question is to write Java statements to perform specific tasks on arrays. These…
Q: 1. Use Huffman coding to encode the following symbols with the frequencies listed: A: 18, B: 8, C:…
A: A. Show the sorting process neatly:Arrange the symbols and their frequencies in ascending order:B:…
Q: 1. Consider the following Prolog facts and rules: member (X, (X|_]). member (X, [_T]) :- member (X,…
A: To sum up, the well-placed breaks in the Prolog rules help to streamline the search and guarantee…
Q: 6) Determine the truth table for circuit shown in figure below (you can verify at least one row of…
A: A truth table is a representation of the input circuit gates and the outputs generated with that…
Q: Q2. Let’s have some fun! You can copy and paste my code in blue. Turtle graphics is a classic…
A: For Square :Import turtle packagecreate a turtle objectInside a loop with range 4:Move forward by…
Q: There are n students who studied at a late-night study for final exam. The time has come to order…
A: When ordering pizzas for a group of students studying for their final exams, it's essential to…
Q: wave.h: #include <stdint.h> typedef struct { uint16_t nchannels; uint16_t…
A: To allocate memory for an array in C, you can use dynamic memory allocation functions such as…
Q: Which defines the Global-and-Local-as-View (GLAV) schema mapping? Expressions include a query over…
A: The Global-and-Local-as-View (GLAV) approach to schema mapping is a method used in data integration…
Q: Please help me with this question. I am not understanding what to do. Please complete part 2 for the…
A: //Please note that the code given below is properly executable and testified before passing it to…
Q: SNMP (Simple Network Management Protocol) serves as a network management tool to manage and control…
A: The following are descriptions of the protocol and the error mentioned in the problem:Error Message:…
Q: Please help me with this question. I am not understanding what to do. Please complete part 2 for the…
A: <!DOCTYPE html> <html lang="en"> <head> <meta charset="UTF-8">…
Q: In a two-level cache system, if the hit times for L1 and L2 caches are 5 cycles and 15 cycles…
A: In order to lower latency and boost system performance, frequently accessed or recently used data…
Q: What hurdles, hardware and software technology to use while building a network for a corporate…
A: Designing a network for a global corporate campus is a complex task. Organizations operating across…
Q: Software development Use use case diagram can you draw the actors and use case not just…
A: Key references: Computer Science
Q: Binomial coefficient calculation algorithm is an example of following type of algorithm:…
A: Binomial coefficient calculation involves determining the number of ways to choose k elements from a…
Q: Is the ‘word count’ function in many editing tools for creating documents a goodcryptographic…
A: The "word count" method isn't reliable for checking if something is secure. Here's why:Key…
Q: A byte-addressable system with 16-bit addresses ships with a three-way set associative,…
A: Here's how to find the block size:We know the total size of the tag store is 264 bits.We are also…
Q: In C Sharp, How do I get the output to display the objects : For Example: The area of a Rectangle…
A: A hierarchy of shapes (Circle, Rectangle, and Triangle) that all derive from the abstract class…
Q: Let W be the rectangular window whose lower left corner is (-3, 1) and upper right corner is at (2,…
A: The objective of the question is to apply the Cohen-Sutherland clipping algorithm to clip a line…
Q: the 12 pairs are not correct
A: The question asks for the generation of 12 pairwise distinct permutations of a given set of 10…
Q: Please solve number 2 (1) and show all steps
A: Step 1:a) A + B, where A = 7, B = 6.Step 2:Convert A and B to binary. A = 7 in binary is 0111. B = 6…
Q: Simplify the following query: SELECT ENAME, PNAME FROM EMP, ASG, PROJ WHERE (DUR > 12 OR RESP =…
A: The objective of the question is to simplify the given SQL query and transform it into an optimized…
Q: Write a program in C as follows:- Create an array of integers named “toy” that has 120 rows and 4…
A: The objective of the question is to create a C program that manages a toy bag. The program should be…
Q: Create a variable called NUMBER and assign the value 9 to it 2. Create an IF statement that will…
A: Python's simplicity and readability make it a popular programming language for many purposes. We…
Q: need step by step answe
A: The question asks about the actions needed to maintain data integrity in a cache system using a…
Q: In Matlab code 2. A fibonacci sequence is a sequence such that, beginning with the third element,…
A: Set the Fibonacci sequence's first two terms to their initial values: `a1 = 3` `a2 = 7`Create a…
Q: So this is a java program code please do the code and please follow what in the question says and…
A: Define the GeometricObject class with attributes for color, filled status, and date created. Include…
Q: Introduction to the Organization of Computer Systems If a program accesses memory locations 1000,…
A: The tendency of a program to access memory locations that are close to one another is known as…
Q: implementing a simple binary search tree capable of storing and retrieving student information.…
A: Algorithm for the primary feature:1. Declare a binary seek tree (BST) item named `mytree`.2. Declare…
Q: Create a fortran file called myhello.f90 , that prints out your first and lastnames with some flavor…
A: The objective of the question is to create a Fortran program that prints out your first and last…
Q: Write a C++ computer program that calculates and displays to first 100 numbers in the Fibonacci…
A: The objective of the question is to write a C++ program that calculates and displays the first 100…
Q: Below are some of the mobile OS features. Explain each of them. User interfaces Wi-Fi…
A: User interfacesWi-Fi callingVirtual assistantsSoftware development kitsEmergency CapabilitiesMobile…
Q: Consider the linear system with b = (-1,7, -7) and 3 -1 1 A -1 3 -1 1 -1 3 (a) Verify that the SOR…
A: In this question we have to use Successive Over-Relaxation (SOR) method on a specific matrix…
Q: Question: Write a PLSQL program using functions to print Hello. I am using oracle apex compiler.
A: PL/SQL (Procedural Language/Structured Query Language) is Oracle's proprietary extension of SQL,…
Q: Which of the following statements are true. In a child class, we use the keyword "super" to call a…
A: In object-oriented programming (OOP), a class serves as a guide or template for building objects, or…
Q: Question: Given an array of integers, find the maximum sum of contiguous subarray (containing at…
A: Initialize max_sum and current_sum to the first element of the array.2. Iterate through the array…
Q: Some lines in the file have a line number, as shown in the following figure. A line number is the…
A: The task is to create a Java program called RemoveLineNumber.java that removes line numbers from a…
Q: C 10 5 8 .9 6 Ꭰ -3- E 4 7 the minimum cost spanning tree on graph using Prim's algorithm. What is…
A: Prim's algorithm for graphing minimal spanning tree (MST) is popular. Minimum spanning trees connect…
Q: The following questions should be addressed in a daily scrum meeting. O What can be improved? What…
A: a. What could be made better?Talking on areas for improvement during the daily scrum meeting is…
Q: v1 0 9 0 0 5 0 1 33 9 9 0 9 9 1. Using given matrix P produced by Floyd2 Algorithm restore the path…
A: To explain the process of finding the shortest path from v3 to v2 using the Floyd-Warshall algorithm…
Q: How many keys are needed for pairwise secure communications among 100 users using a a. secret key…
A: A secret key cryptosystem, sometimes called symmetric key encryption, is a type of cryptography in…
Q: Using the MATLAB editor, make a script m-file for the following: The velocity of an object dropped…
A: The script analyzes an object falling vertically from a specified height. It calculates and…
Q: Write a Java method isPalindrome that takes a string as input and returns true if the string is a…
A: Convert the string to lowercase.Remove spaces, punctuation, and any non-alphanumeric…
Q: = 0, Design a sequential circuit with two D flip-flops A and B, and one input x_in. When x_in the…
A: The objective of the question is to design a sequential circuit with two D flip-flops A and B, and…
Q: Algorithm 5.7 The Backtracking Algorithm for the 0-1 Knapsack Problem Problem: Let n items be given,…
A: The 0-1 Knapsack problem aims to maximize the total profit by selecting items with given weights and…
Q: The 8 Key Capabilities - Which 2 of the 8 Key Capabilities is most important and why?
A: The 8 Key Capabilities - Which 2 of the 8 Key Capabilities is most important and why?Selecting the…
Q: Task/Purpose: Modify the code from Q5 to build a different message Instructions: . Modify the code…
A: ```python # Given list fm = [0, 1, 2, 3, 4, 5, 6] # Initialize variables sg_h = 32 sm = 1 sg_c = 29…
Unlock instant AI solutions
Tap the button
to generate a solution
Click the button to generate
a solution
- Consider a knowledge base (KB) shown in Figure4. Assume that the initial fact base from a user is {Q /\ N} and the goal state {S}. Based on the initial facts and goal state, show the backward chaining and forward chaining searchpathsFor historical data sets, it is important to describe the hidden Markov chain.Do the following.i. Generate a four state Markov Chain matrix of your own choice make sure eachrow sum up to one.ii. Draw the state diagram of Markov chain.iii. Create another matrix with 4 states and draw its state diagram. Make sure eachrows sum up to 1.iv. Multiply both matrix and make sure the first matrix should be on the left and thesecond right. Ensure that each row sum up to one.v. Draw the state diagram final state.
- Consider the following knowledge base Prove that Q is true with: 1. P → Q 2. L ∧ M → P 3. B ∧ L → M 4. A ∧ P → L 5. A ∧ B → L 6. A 7. B Forward-Chaining Backward-Chaining Resolution Prove t → s: 1. p → q 2. [q ∧ r] → s 3. [t ∧ u] → r 4. u → w 5. t → y 6. y → u 7. r → p 8. p → m i. Express in clause form ii. Forward-Chaining iii. Backward-Chaining iv. ResolutionThe importance of the hidden Markov chain in a historical data set should be discussed.How many states have a nonsimplified Markov chain for a system consistingof n components? Assume that each component has two states: operationaland failed.
- You are required to create a Julia program that does the following in this problem:Analyze every policy you are given, then tweak it until a solution is discovered. Real-time recording and saving of the Markov decision process (MDP).Consider the following knowledge base in first order logic: p(X) ← q(X) ∧ r(X, Y ) q(X) ← s(X) ∧ r(Y, Y ) s(a) r(a, a) What is the result of the query p(a) using a backward chaining inference algorithm? Show the intermediary queries.If the problem can be addressed by devising optimal subproblem solutions, it has the attribute. Memory, greedy subproblems, overlapping subproblems
- can you please help me understand how resource allocation graph algorithm becomes a deadlock avoidance? no handwritten answers please, no one worded, one phrased, or one sentenced answers too pleaseConstruct an optimal binary search tree for five keys A, B, C, D, E with probabilities p1 = 0.1, p2 = 0.3, p3 = 0.1, p4 = 0.4, p5 = 0.1. Show(1) the main table; (2) the root table; (3) all computations to fill in the main table and the root table; (4) the optimal binary search tree based on the root table; (5) that the average number of comparisons of your optimal binary search tree is indeed C(1,5).Question 15 pap In class we considered the computational complexity of global localization as a hypothesis elimination problem in an idealized setting. What is this problem (briefly), how difficult is it to get an optimal solution (i.e. do you know the complexity?), and what kind of heuristic can be used to achieve a solution?

