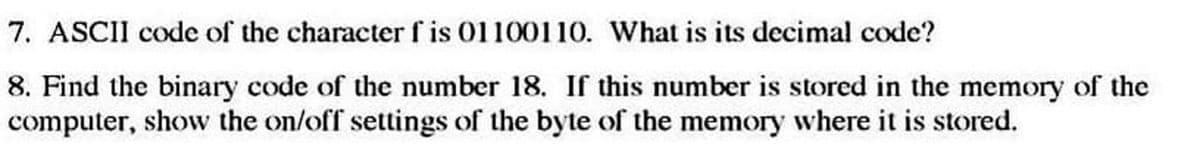
7. ASCII code of the character f is 01100110. What is its decimal code? 8. Find the binary code of the number 18. If this number is stored in the memory of the computer, show the on/off settings of the byte of the memory where it is stored.
Q: ,D),and(5,E),inthisorder, into an initially empty binary search tree, what will it look like?
A: given - If we insert the entries(1,A),(2,B),(3,C),(4,D),and(5,E),in this order, into an initially e...
Q: When was the first desktop computer invented?
A: Intro A computer is an electronic machine that takes input , process it and produces desired output ...
Q: Write a C++ proogram to find the hypotenous of a right angled triangle when taking the base and heig...
A: Required:- Write a C++ program to find the hypotenuse of a right-angled triangle when taking the bas...
Q: Discuss security threats to databases and their respective countermeasures
A: Defined the security threats to databasesand their respective countermeasures
Q: How can a software development team build "artificial walls" that limit their capacity to communicat...
A: Intro Artificial boundaries : A project is a combined activity which is carried out by group of peop...
Q: Why is understanding the users Visual System so important to the design process? Give an example.
A: what users are thinking and feeling As a result, you must always present them the proper things in t...
Q: Create a simple text-based console game that implements at least three (3) interfaces. Below is a sc...
A: The java code is given in the below step with an output screen shot
Q: Write a Python program to remove all the occurrences of the number 1 from the list given below and d...
A: Write a Python program to remove all the occurrences of the number 1 from the list given below and d...
Q: int main() { int i, salary[10], range[9]={0, 0, 0, 0, 0, 0, 0, 0, 0}; double gross[10], total[10];...
A: The regular expression (RE) contains the symbol 0 and 1 only. The expression is: ((00+01)*01)+101(0...
Q: What exactly do you mean when you say "index hunting"?
A: Introduction: An index is a collection of data, such as a set of files or database information. It's...
Q: Write a JAVA program to input the size and elements of an integer array. Then input an integer k fro...
A: Your java program is here with an output.
Q: 1. To keep track of students and their advisors, a university uses the table structure shown below. ...
A: Note: As per our company guidelines we are supposed to answer only first 3 sub parts. Kindly repost ...
Q: Cure 3] The salt of a password is stored in the password file in plaintext. Why is it important to s...
A:
Q: It might be hard for the database to stay up to date if some log records about a block aren't sent t...
A: Find the answer given as below:
Q: Comment on the current status of IPV4 and identify the major emerging problems for IPV4 and disc the...
A: Ipv4 address was published in 1981. The systems or computers at that time were very huge and expensi...
Q: What is the other name for a single byte of data?
A: This question belongs to Computer architecture.
Q: What is the importance of linux partitioning?
A:
Q: given a text file (data1.txt) that consists of different garbage strings. 1.Create a new file, from...
A: Answer: Since file data is not given, I have used some test data. Algorithm: Start Create a class c...
Q: Write a Python program to all the occurences of the strings other than "Java" from the list given be...
A: Required:- Write a Python program to all the occurrences of the strings other than "Java" from the ...
Q: :the output of (Print "a", "b", "c") is abc O ab c abc O
A: As per the requirement given code is executed, this line is executed in python. Third option is corr...
Q: Select one or more: a. We would like to test whether our code work b. We try to avoid a data leakage...
A: Select one or more: a. We would like to test whether our code work b. We try to avoid a data leakag...
Q: How can you aid in preventing internal and external threats?
A: What is threat ? A threat is nothing but a suspicious or malicious activity they can damage the sens...
Q: Describe the following statement and give at least one example: More security measurements might cre...
A: Introduction: 1. Describe the following statement and give at least one example: More security measu...
Q: must be able to identify individual hosts (sUch as a computer, printer, router, etc.) and individual...
A: The answer is
Q: Convert the Tic-Tac-Toe game into a class. Overload the < operator to print the boar Write a test pr...
A: #include<iostream> class ScoreList{private://Structure representing a node in the linked lists...
Q: PYTHON! Solve problem by using PYTHON Program to remove the ith occurrence of the given word in list...
A: Here I have taken input from the user and then stored the input into a list. Next, I have printed th...
Q: Show the representation of -22 (assuming 8-bit registers) using a) Signed-magnitude representation. ...
A: representation of -22 (assuming 8 bit register)
Q: What changes has to be made in the 4X3 memory to make 16X6?
A: Read-Only Memory Identification and Encoding (ROM): And including Memory (RAM), Read-Only Memory (RO...
Q: What are the issues that can prevent a transaction processing system from scaling up linearly? In ea...
A: issues that can prevent a transaction processing system from scaling up linearly can be anyone of t...
Q: :the output of (Print "a", "b", "c") is abc ab c abc
A: given - *:the output of (Print "a", "b", "c") is
Q: ease don't copy Write a lisp function f4 that returns the maximum value of an integer list. Example:...
A: Given Please don't copy Write a lisp function f4 that returns the maximum value of an integer li...
Q: Discuss the internet's evolution and the underlying technological foundations.
A: Intro According to the question, The Internet began in the 1960s as a way for government researchers...
Q: Show the representation of –22 (assuming 8-bit registers) using a) Signed-magnitude representation. ...
A: The question is to show the representation of -22 to the given formats.
Q: 4. Write a Python program to remove all the occurrences of the strings other than "Python" from the ...
A: Write a Python program to remove all the occurrences of the strings other than "Python" from the lis...
Q: Chinese Wall model: consider following COIs and CDs: Bank COI class: Chase Bank, US Bank, Citi Bank ...
A: Chinese Wall model: consider following COIs and CDs: Bank COI class: Chase Bank, US Bank, Citi Bank ...
Q: The turning points in the historical development of computers are based on the echnology incorporate...
A: In the above question, we need to check whether the statement is true or false. The origins of compu...
Q: Assume you want to use shared-nothing parallelism to manage a workload with a large number of tiny t...
A: INTRODUCTION: SHARED-NOTHING-PARALLELISM: No memory or disc space is shared between processors in a ...
Q: Scenario: You are tasked with the development of an E-Scooter ride-share system. It allows registere...
A:
Q: e selected meal, and st
A: Create a new class with name FitnessPlanner1.java, then take the inputs from user. Calculate the VO2...
Q: Create a grammar that allows only identifiers that start with a letter, have at least one but no mor...
A: Intro Create a grammar that allows only identifiers that start with a letter, have at least one but ...
Q: How many bits do quadword data formats consume?
A: 1) The fundamental data types are bytes words doublewords quadwords 2) Number of bits each of the...
Q: When we are away from home, how can we check our e-mail?
A: Introduction: E-mail, often known as electronic mail, is information stored on a computer that is tr...
Q: rite a Python program to all the ocurences of the strings other than "Jav lavascript" , "Java" ,"Jav...
A: The program is to count all elements in list which are not "Java" So simply we will iterate over the...
Q: SolarWinds is a major software company based in the USA, which provides system management tools for ...
A:
Q: d. Perform Shannon-Fano algorithm and display in a table, the count, the entropy, the code, and the ...
A: Shannon-Fano : It is an algorithm is an entropy encoding technique for lossless data compression of...
Q: a. If at the start of the analysis pass, a page is not in the checkpoint dirty page table, will we n...
A: Answer: The ARIES recovery mechanism does not wait for a checkpoint before flushing pages. LSNs are ...
Q: ccess (RDMA) is a significantly faster method of accessing data. Please explain why.
A: given - Remote procedure calls or messages can be used to obtain data from a remote node in a shared...
Q: Given x = [2 45-10 8369-4 14], write a code using For loop to find the largest and the smallest Valu...
A:
Q: What will be the output of the following program? #include void main () { int a[10] = {...
A: Step 1 The answer is given in the below step
Q: iven 2 numbers which are the measurement of a distance in feet and inches, for example 3 feet 7 inch...
A: import java.util.Scanner; public class FeetInchesToMeters { public static void main(String[] arg...
Step by step
Solved in 3 steps

- Computer Science Help please. Only MIPS. Write a program that asks the user to enter an integer and outputs the integer in 32-bit two’s completement binary. There should be a space separating each 4 digits.Fill in the blanks: Q. Least __________________ Byte is Better known as _______________.I need help in learning the binary system and converting decimal numbers to binary. You are given a decimal number to convert into binary. Press the buttons to change their values so that the row represents the decimal number on the left. When a 1 is used, we consider the value to be oN. When a 0 is used, we consider the value to be off.
- 9. Show how the text ‘HelloW’ will be stored in computer using 7-bit ASCII standard. You will need to consult the ASCII table. 10. Fill in the following addition table for base 3.information technology What is the purpose of the scanf() function?a. It creates formatted output.b. It converts binary values into ASCII characters that are put into memory.c. It inputs ASCII characters and converts them into binary values that it copies intovariables.d. It processes keys typed at the keyboard.You have the decimal number 7. It can be stored in the computer memory in one of the two formats below. Format A: 00000111 Format B: 00110111 Explain when do you store it in the format a) ANDwhen do you use format b).
- What is the purpose of the ASCII character set?6. Write a program to display the multiplication table vertically from 1 to n. Your output may resemble the following:Display the multiplication table vertically from 1 to n:-------------------------------------------------------------Input the number of the multiplication table: 5Multiplication table from 1 to 51x1= 1 2x1= 2 3x1= 3 4x1= 4 5x1= 51x2= 2 2x2= 4 3x2= 6 4x2= 8 5x2= 101x3= 3 2x3= 6 3x3= 9 4x3= 12 5x3= 151x4= 4 2x4= 8 3x4= 12 4x4= 16 5x4= 201x5= 5 2x5= 10 3x5= 15 4x5= 20 5x5= 251x6= 6 2x6= 12 3x6= 18 4x6= 24 5x6= 301x7= 7 2x7= 14 3x7= 21 4x7= 28 5x7= 351x8= 8 2x8= 16 3x8= 24 4x8= 32 5x8= 401x9= 9 2x9= 18 3x9= 27 4x9= 36 5x9= 451x10= 10 2x10= 20 3x10= 30.A)The decimal number 162 what is the binary representation of it ? B)the decimal number of -53 what is the binary representation of it ?
- Topic: Binary Operation True or False Under binary operation *, the a * e = e * a = a.5. Declare a 32-bit signed integer variable and initialize it with the value 234 (base 10). In memory, what are the hexadecimal values shown?Use the format SEEMMMM. All digits are decimal. The exponent is stored excess-50. The implied decimal point is at the beginning of the mantissa. The sign is 1 for a positive number, 7 for a negative number. Hint: Note carefully the number of digits in the mantissa! a. Convert the decimal number 28643 to floating point.b. What is the range of numbers that can be stored in this format? c. What is the floating-point representation for: −28569? d. What is the floating-point representation for 0.0000019557?

