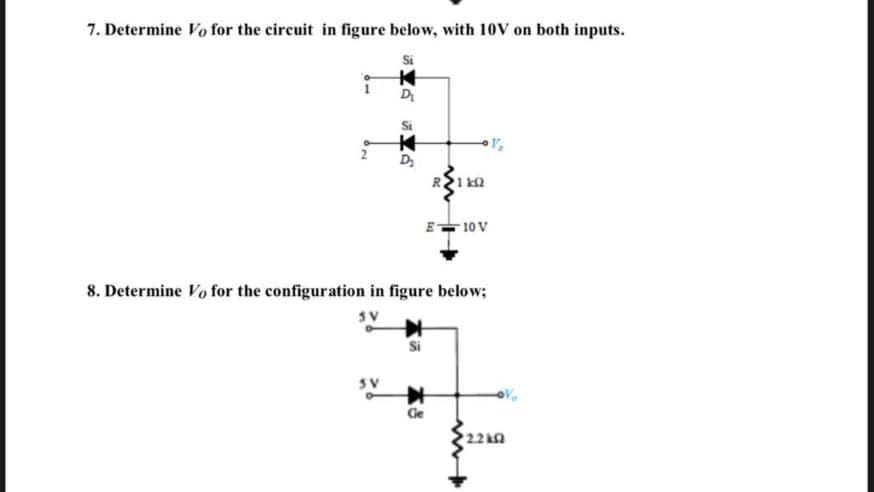
7. Determine Vo for the circuit in figure below, with 10v on both inputs. Si D D A 01 8. Determine Vo for the configuration in figure below; SV Ge 22k
Q: Explain briefly how the weighted technique may be utilised to accomplish a conversion from decimal…
A: Definition: Hello there, I'm writing the required response to the above-mentioned query. Please find…
Q: Total = a + b + c; Average = Total / 6; А. Logic Errors В. Run-time Errors C. None of the above D.…
A: A programming language must follow rules and regulations to execute task successfully. Logical…
Q: How serious is an error in a database system vs an error in another area?
A: Intro An attacker may benefit from minor database: errors since they will know precisely what…
Q: How do the cohesion and coupling of a software design interact?
A: Introduction: "Low coupling and strong cohesion are required for good software design." When the…
Q: Is it more difficult to create Graphical User Interfaces (GUI) using pixel-based coordinates?
A: Graphical User Interfaces (GUI) A graphical user interface (GUI) is a user interface that uses…
Q: Give examples and describe the influence of the Internet of Things on the business world, with an…
A: The IOT stands for Internet of Things: Simply said, it's a network of interconnected devices made up…
Q: Problem 1: Using KMaps, find the simplest SOP expression of F= Ew,x,Y,z(0, 1, 6, 7, 8, 9, 14, 15).
A: I have provided answer with brief explanation------------ I have provided hand-written…
Q: Daemon processes cannot be seen with the ps command alone; the –e option must be used in addition.
A: Introduction: To list system processes, which option is used with the ps command? In addition to…
Q: What are the best practices for integrating suppliers?" is a question that should be considered.
A: 1. Begin The Process with Conducting Due Diligence Picking the right providers is around 50% of the…
Q: on cloud security after a data breach has taken place? Are there any other measures you think could…
A: Yes, it affects An unapproved individual gains access to classified, sensitive, or safeguarded…
Q: developing a programme pe properly observed.
A: Each programming language has its own set of rules that oversee its structure. A program composing…
Q: From the perspective of application developers and consumers, compare the three cloud computing…
A: Please upvote I am providing you the correct answer below. Please please please.
Q: Details on the DNS, from iterations and non-iterations to the authoritative servers and root…
A: Introduction: DNS Operation:DNS is a worldwide system that converts IP addresses into domain names…
Q: e data is stored in memc nemo ack and hean memon
A: Memory alludes to the strategies for getting, putting away, holding, and recovering data. Memory is…
Q: Q1\Design a combinational circuit to compare two number each one consists of 4-bit to have an output…
A: Please upvote I am providing you the correct answer below. Please please please.
Q: Select ALL invalid binary search trees. A)
A: Rule of binary search tree:- Left child node must be less than parent node and right child node…
Q: Read this:Selective Service Registration Registration with the Selective Service is mandatory in…
A:
Q: The disadvantages of the hardwired approach are: O It is less flexible O It is costly less flexible…
A: (c)-option =>less flexible & cannot be used for complex instructions The more complex the…
Q: In a computer with a 32-bit data-bus, how many 4-bit wide memory components are used? the answer to…
A: The answer is
Q: What sets Watson different from other computers?
A: Given: Watson is built to deal with unstructured data, unstructured issues, and natural language…
Q: Is there a way to avoid intrusions?
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Most PC…
Q: Google responds to our inquiry with millions of relevant webpages in a single millisecond?
A: Millisecond: A millisecond (MS) is a thousandth of a second. A human eye blinks between 100 to 400…
Q: What methods are being used to achieve data backup? Make a list of the many forms of data backup.
A: Introduction: We should start by developing a backup strategy for backup data:
Q: A supernet has first address of 205.16.32.0 and a supernet mask of 255.255.248.0. Prove that…
A: The answer is
Q: The term octet is used to describe what size of binary number? O 80 bit O 16 bit O 8 bit O 4 bit
A: Introduction: Here we are required to explain the which of the following size of binary number is…
Q: Explain briefly how the weighted technique may be utilised to accomplish a conversion from decimal…
A: Hello there, I'm writing the required response to the above-mentioned query: find the answer below.
Q: What was the driving force behind Cisco's switch from a standalone access control system to an IP…
A: Access control systems that are simple. These are only used in one place.There are no related sites…
Q: When a collision occurs on a shared Ethernet network, what is the first step in recovery for the two…
A: Option 3
Q: In Excel, what is the difference between creating a workbook and creating a template for something?
A: MICROSOFT EXCEL: It's a spreadsheet with graphing capabilities, pivot tables, and a macro…
Q: The aspects of software quality do not necessarily have a good connection with one another. Answer…
A: Introduction: This property shows whether or not a program will finish its tasks. Topics like…
Q: ge faults using the OPTIMAL, LRU, FIFO page replacement algorithms with pure demand paging. Assume…
A: Solution - In the given question, we have to find the number of page faults using the OPTIMAL, LRU,…
Q: Write the code for the infixprint() function so that it prints the tree in infix order.
A: Let t be the expression tree If t is not null then If t.value is operand then…
Q: Explain the difference between how a primitive data is kept in memory and how a reference data is…
A: Memory: Memory refers to the procedures for acquiring, storing, retaining, and retrieving…
Q: Multiple multithreading strategies are tested on a range of operating systems (Linux, Windows, Mac,…
A: DEFINITION In this paper, we examine and contrast multithreading algorithms for uniprocessor and…
Q: How many words can you use to describe a mobile database?
A: The answer is given below.
Q: 1.) What is a deadlock? Explain and you may use common examples. How does it affect and what can be…
A: We can only answer the first question. Please post the 2nd question separately. Given: 1.) What is a…
Q: o the supply chai
A: Center processes, often known as "main" processes, are the actions that an association must execute…
Q: The protocol is most often used to transfer web pages. О НТТР O HTML SH MIME
A: Systems in the TCP/IP suite: The TCP/IP software is a collection of protocols that are currently…
Q: Before data can be sent using TCP, a connection must be established first. This connection…
A: TCP is connection oriented.This means that a connection is needed to established between the sender…
Q: Write a program that asks the user to enter the number of students, then enter the grades of these…
A: I have provided C++ CODE along with CODE SCREENSHOT and 2 OUTPUT SCREENSHOTS------------
Q: ily_nam
A: Given as, customers - id - name - family_name - address - phone products code name…
Q: On a LAN RJ-45 connector, what name is given to the eight physical connections that make contact…
A: Pins
Q: Examine the classification of access control methods. These gadgets have a wide variety of controls.
A: Given: - Examine the classification methods for access control. Discuss the many controls present in…
Q: and age of t
A: Technology: View each of the videos connected with this subject. Technology is the utilization of…
Q: Use YOUR NAME, SURNAME, and DATE as a variable in your answer. lab6 4. State which of the following…
A: E) True F) False programming the term "pass by reference" means to pass in such a way that the…
Q: During the course of its execution, may a single process get stalled? Your replies should be…
A: Definition: Depending on how quickly your hair grows, you'll need to have a single-process colour…
Q: Provide me with the Matlab code to swap the second and third rows of the matrix given below, m = 987…
A: Write a MATLAB program to swap the second and third rows of the matrix given below, m = 9 8 7…
Q: What do you think of recent changes to the search algorithms of Google?
A: Introduction: What do you think of recent changes to the search algorithms of Google
Q: In the following semantic Network, write two predicate calculus ?
A: Let's derive the statements from the propositional logic given in the semantic network Dog is red…
Q: When it comes to direct competition, why does Pinterest consider Google as the biggest threat? What…
A: Pinterest is a social networking service that uses a software: engine to search and filter…
Step by step
Solved in 2 steps with 2 images

- Draw the circuit diagram to output F given in the expression above by referring to schematics for 2-2) and 2-3). Use the space below to draw both the IC with pin assignments and a circuit schematic. Using a single 7400 IC construct a circuit to output the following Boolean function: F = AB + CD1) Build the truth table for this circuit by cycling through all of the possible input combinations and noting the input. 2) What logical function does this circuit represent? 3) Is it possible to replace this circuit by an equivalent single gate? 4) What would equivalence mean in this case?a) Build your circuit Design and build a state machine that will control the transition between light settings of a traffic light unit as shown in Figure 1. The design should include 3 positive edge triggered D flip-flops. Use 1 flip-flop to control the on and off of a given light, and the state machine should switch from Red (100) -> Red and Amber (110) - > Green (001) -> Amber (010) and repeat the cycle again, with the transition table below.
- Analyse the sequential circuit shown in Figure which has 2 rising edge-triggered flip-flops A and B, one input X, and one output Z. You are required to perform the following tasks: Write the state equations, flip-flop equations and output equation for this circuit. Construct a state table. Draw a state diagram of this circuitwith in 10 min don't copy from internet state diagram and asm chart of mod-6 counterIdentify the state diagram operation and find its output sequence for the following input sequence X=0101-1100-101-0000 the circuit accepts input bits from LSB to MSB
- F =A'BC'+A'CD'+ACD+AB'C'D' Draw the Logic Gates diagram please Need Asap5. Design an appropriate combinational circuit that implements a digital system with the following output functions: ROR, SHL, AND, XOR, ADD, DIV, SUB, MOV using a decoder. 6. Design the circuit diagram and truth table for the Boolean expression : F = (A’B) + (C’B).Referring to the circuit in Figure 2(c), construct the timing diagram in Figure 2(d) by showing the Q output (which initially LOW). Consider also the given PRE and CLR Inputs.
- I. Write down the state equations.II. Write down the output equations.III. Derive the state table for the sequential circuit.IV. Draw the state diagram for the sequential circuit.68. In ______signaling, the same circuit is used for both signaling and data. a. in-band b. out-of-band c. mixed d. none of the above3) Comment on the functionality of the two circuits given in Figures 1.7 and 1.8.

