7. Find the remainder of when divided by a. 2. ь. 5. c. 7. d. 9. 8. Solve the following congruences (describe the general solution). a.. b.. C. d..
7. Find the remainder of when divided by a. 2. ь. 5. c. 7. d. 9. 8. Solve the following congruences (describe the general solution). a.. b.. C. d..
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter18: Deterministic Dynamic Programming
Section18.1: Two Puzzles
Problem 3P
Related questions
Question
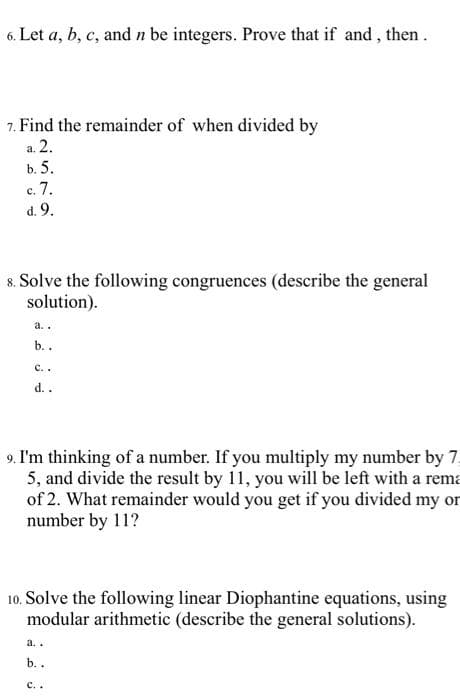
Transcribed Image Text:6. Let a, b, c, and n be integers. Prove that if and, then.
7. Find the remainder of when divided by
a. 2.
b. 5.
с. 7.
d. 9.
8. Solve the following congruences (describe the general
solution).
a..
b..
с..
d..
9. I'm thinking of a number. If you multiply my number by 7.
5, and divide the result by 11, you will be left with a rema
of 2. What remainder would you get if you divided my or
number by 11?
10. Solve the following linear Diophantine equations, using
modular arithmetic (describe the general solutions).
a..
b. .
с..
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole