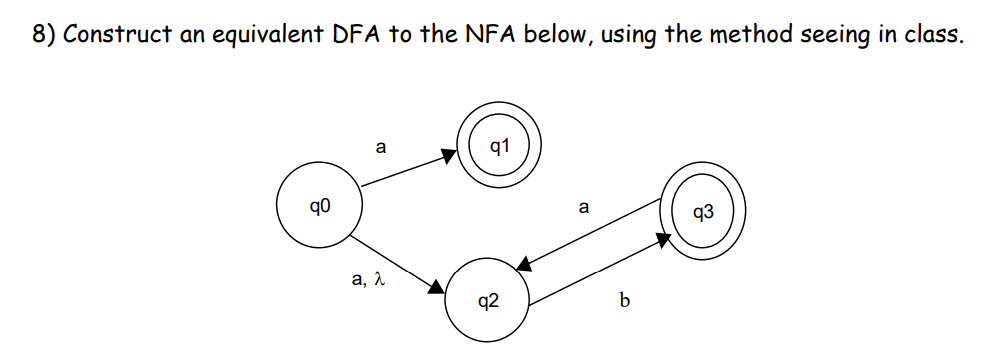
8) Construct an equivalent DFA to the NFA below, using the method seeing in class. 90 a, λ 91 8 a b 93
Q: 6) Use only properties of regular languages, to prove or disapprove the following statement: (You…
A: 6. a. "If L1 and L2 are both regular, then (L1-L2)' is regular": Let L1 and L2 be two regular…
Q: There must be a description of a fictitious scenario for the handling of logins. There are a few…
A: There are different kinds of phishing attacks, each of which takes the user credentials and then…
Q: Does this list contain any systems that have been further categorized into more than one group?
A: Introduction: In data analysis, it is common to categorize data into groups for better understanding…
Q: Write a function max_magnitude() with three integer parameters that returns the largest magnitude…
A: 1) Below is python program that writes a function max_magnitude() with three integers parameter that…
Q: In a nutshell, whatever goals have you set for the authentication method that you want to…
A: In this question we have to we have to understand what type of goals we can set for the…
Q: Given a hash table of size M=10 and a linear probing method, following are the contents of the hash…
A: The solution is given below for the above-given question:
Q: Using the figure in previous problem, list each entity and state what foreign key, if any, would be…
A: In the previous answer, we have identified the business rules. Now we will identify the foreign key…
Q: TODO: Lienar Regression with least Mean Squares (LMS) Optimize the model through gradient descent.…
A: To complete the TODOs for the LeastMeanSquares class, you need to implement the fit and predict…
Q: It would be of great assistance if you could elaborate on what you understand by the phrase "the…
A: Authentication techniques are methods used in computer security to authenticate the identity of a…
Q: Create a new project named lab7_1. You will be implementing a Tacos class. For the class attributes,…
A: Below is the complete solution with explanation in detail for the given question about the…
Q: Is it feasible to differentiate between a prescriptive model and a descriptive model by analyzing…
A: Models that are primarily used for understanding, predicting and communicating are referred to as…
Q: Which system model should be used?
A: 1) A system model is a representation of a system, which can be physical, abstract or conceptual. It…
Q: When you say "the objectives of authentication," what do you mean exactly? Take into account the…
A: The most frequent approach to verify client or data identity is authentication. When a user logs…
Q: How is the implementation of multifactor authentication carried out? To what end does this piece of…
A: Introduction: Multiple Factor Authentication (MFA) is a security solution that requires a user to…
Q: Think about the fundamental processes you are responsible for, and how you plan to implement supply…
A: Introduction: The procedure begins with the supply chain, which is a network connecting the business…
Q: i) SbAaB | 2, A → abas, BbabS Σ = {a,b}
A: The given regular grammar consists of one start symbol S, two non-terminal symbols A and B, and a…
Q: What languages do the expressions {2} and a denote? (Ø: represent the empty set).
A: Please refer to the following steps for the complete solution to the problem above.
Q: To what extent does a data breach compromise cloud security? Can you provide any potential solutions…
A: Justification: Depending on the data, the consequences might include database corruption, the…
Q: The use of non-monotonic reasoning entails an element of uncertainty as well as an imperfect picture…
A: Introduction: Non-monotonic reasoning is a form of reasoning in artificial intelligence that allows…
Q: B.Indicate the value of g, h, and i once the line of code has completed. Assume that the statement…
A: Introduction: - Here is to determine the value of three variables (g, h, and i) after executing…
Q: 7) Use properties of regular languages, to prove or disapprove the following statement: (You may use…
A: 6. a. "If L1 and L2 are both regular, then (L1-L2)' is regular": Let L1 and L2 be two regular…
Q: How are the many possible models for the system narrowed down to the one that offers the best fit?
A: Introduction Model selection is the process of selecting the best model for a system, and it…
Q: An in-depth explanation of how the DNS works, including iterated and non-iterated requests,…
A: Introduction: Iterated and non-iterated requests, authoritative and root servers, and DNS records…
Q: tication may be used? What a
A: Multifactor authentication is a security mechanism that requires a user to provide two or more forms…
Q: How should a business notify its customers and the general public when a data breach occurs
A: When a data breach occurs, it is essential for businesses to promptly notify their customers and the…
Q: Use the provided data to create the Dijkstra Shortest Weighted Path method.Precondition: S is a node…
A: In this question we have to create a dijkstra shortest weighted path method Let's code and hope…
Q: Perform the following binary multiplication. Assume that all values are 2’s complement numbers.…
A: 1. Given that, 1011 * 1101
Q: When you talk about the functions of authentication, I'm not really clear what you mean by that.…
A: Your sign-in process is more secure when authentication techniques are used. Your data is no longer…
Q: This tutorial has all you need to know about DNS records, authoritative servers, and iterated and…
A: DNS transforms domain names into IP addresses to enable web browsers to access Internet resources.…
Q: This is an extensive breakdown of every aspect of the Domain Name System (DNS), from iterative and…
A: Introduction: The Internet's primary phone book is the Domain Name System (DNS). With domain names,…
Q: It is not impossible to explain a challenge-response system using your own words and terminology.…
A: Answer is
Q: To put it another way, what are you hoping to achieve by putting in place authentication procedures?…
A: Introduction Authentication allows organizations to keep their networks secure by allowing only…
Q: If we were successful in obtaining authentication support, which of our goals would we have the most…
A: Authentication support refers to the mechanisms and processes in place to verify the identity of a…
Q: Break out the differences between symmetric and asymmetric multiprocessing. What are the upsides and…
A: Your answer is given below.
Q: Bv In-depth analysis of the Domain Name System (DNS), including such topics as iterative and…
A: Introduction :- Users can access websites and other internet services using domain names that are…
Q: What causes problems with bugs? How is it possible for a mistake to be made in the programming? Use…
A: Answer:- When a developer makes mistakes when coding, it results in a bug. Because of the…
Q: When you talk about the functions of authentication, I'm not really clear what you mean by that.…
A: What is mean by the functions of authentication ? When we have the system , software or the…
Q: What is the relationship between the core processes and the metrics used in the supply chain, and…
A: Supply management, product planning, demand planning, sales and operations planning, and supply…
Q: Take into account a scenario in which the management of login credentials is required, and then make…
A: The scenario of managing login credentials is a common requirement in today's digital world. It is…
Q: When you talk about the functions of authentication, I'm not really clear what you mean by that.…
A: Authentication mechanisms increase the security of your sign-in procedure. Your data are no longer…
Q: Is there any chance that data breaches may compromise cloud infrastructure in a major way? Is there…
A: Since cloud infrastructure has become a top target for attackers due to its scalability and…
Q: What technologies shaped computers and the internet?
A: Introduction: The US research and development efforts to construct and connect computer networks…
Q: In what ways have operations and supply chain strategy been inextricably linked throughout time, and…
A: Introduction: To be determined: the primary objectives connected with the operations and supply…
Q: Cisco's move from a stand-alone access control system to an IP networked solution raises the…
A: 1) A stand-alone access control system is a physical security solution that manages access to a…
Q: System transfers need several considerations. Provide clear examples.
A: System transfers, also known as data migrations, refer to the process of moving data from one system…
Q: What are the goals that the authentication method is intended to achieve? Examine the advantages and…
A: Given 1) Learn why authenticating is done. For two reasons: 2) to weigh the benefits and drawbacks…
Q: An examination of the current situation of IT in Kenyan hospitals is presented here.
A: Using computers in healthcare has significantly impacted the provision of healthcare services in…
Q: One lap around a standard high-school running track is exactly 0.25 miles. Define a function named…
A: Step 1 : Start Step 2 : Take input (laps) from user Step 3 : Calculate miles by using formula…
Q: The use of perioperative computers is essential to modern medicine, but why?
A: INTRODUCTION: The use of computers in hospitals and other healthcare settings has significantly…
Q: In the process of migrating a system, what considerations need to be taken into account? Provide…
A: Introduction Moving a software system or application from one environment to another is referred to…
Step by step
Solved in 3 steps with 1 images

- Language: C++ Explain your answer - True or False? If class A is a friend of class B, then class B is also a friend of class A.The questions should be completed with OCaml. Running screenshots should be provided. The background information is given by the picture. Question 1: Provide 5 good test cases each for eval_success_tests and eval_failure_tests, following the format of: let eval_success_tests : ((truth_assignment * formula) * bool) list = [] let eval_failure_tests : ((truth_assignment * formula) * exn) list = [] Question 2: Implement the function eval : truth_assignment -> formula -> bool. let eval (state : truth_assignment) (formula : formula) : bool = raise Not_implemented You are evaluating boolean formulae instead of float arithmetic. You also need to use the correct boolean value for each variable. We recommend using Variable_map.find_opt to perform lookups in the truth assignment. If a variable is needed but does not appear in the truth assignment, you must raise an Unassigned_variable x exception, where x is the unassigned variable. Once again, you may use any functions you want and…Determine the efficiency class of each of the following issues by designing a sufficiently efficient method.b. You have a file with n student records, each with a number, name, home address, and birth date. Determine the number of pupils from each of the 50 states in the United States.
- Fitt’slaw example?Provide a detailed explanation on the Class Diagram above.Answer the given question with a proper explanation and step-by-step solution. Using Java Create an BankAccount Class that has an account id number (of type integer), balance (of type double), and rate (of type double) as private data. Add get and set methods for these three variables to work with these attributes. Make overloaded constructors to bring in and set all values, and also to just to bring in a customer name and id which uses 0 for the balance. Include error handling in the set for the balance which throws an exception if a change would put the balance below 0. In Main of another class file create 2-3 objects of BankAccount and work with their values and output them to the user to test your new class. Take the BankAccount Class from above and copy it into this program. You will use it as one of the classes in this one. Create a BankCustomer class with 3 BankAccount objects inside it as private variables (of type BankAccount) as well as a customer name (of type String).…
- Using the Java language, write a definition for the PERSON class to represent a person's name and another variable to represent his age, and a constructor method that receives data values upon creation. The definition also includes change methods and retrieval methods for each variable of the class. In addition, the class definition contains a RESET method to change the value of both variables with new values that are received from during transactionsPLZ help with the following: IN JAVA Given the following code (where the function FunTest() and the main method are inside one class in the same file where classes X, Y and Z are), predict what is the output?Draw the Class and Object Diagrams using the following specification of the hotel reservation? 1. For the hotel guest - search available rooms - make a reservation (after registration). Up to 2 reservations are possible for each guest confirm reservation -cancel reservation-pay through credit card or bank transfer
- USE JAVA LANGUAGE to solve this problem Important:- Provide API documentation comments for your class(es), class constructor(s) and method(s) using the Javastandard form for documentation comments discussed in this course.- Use meaningful variable and constant namesAnswer this mcq 12) Java has a way of officially hiding details of a class definition. To hide details, you mark them as _________. public protected private all of the above AnswerGiven the following class diagram, interfaces and classes that model various kinds of animals. What will be the errors in the main method? For each error, indicate the line number of each incorrect statement and explain in one sentence why it is wrong.

