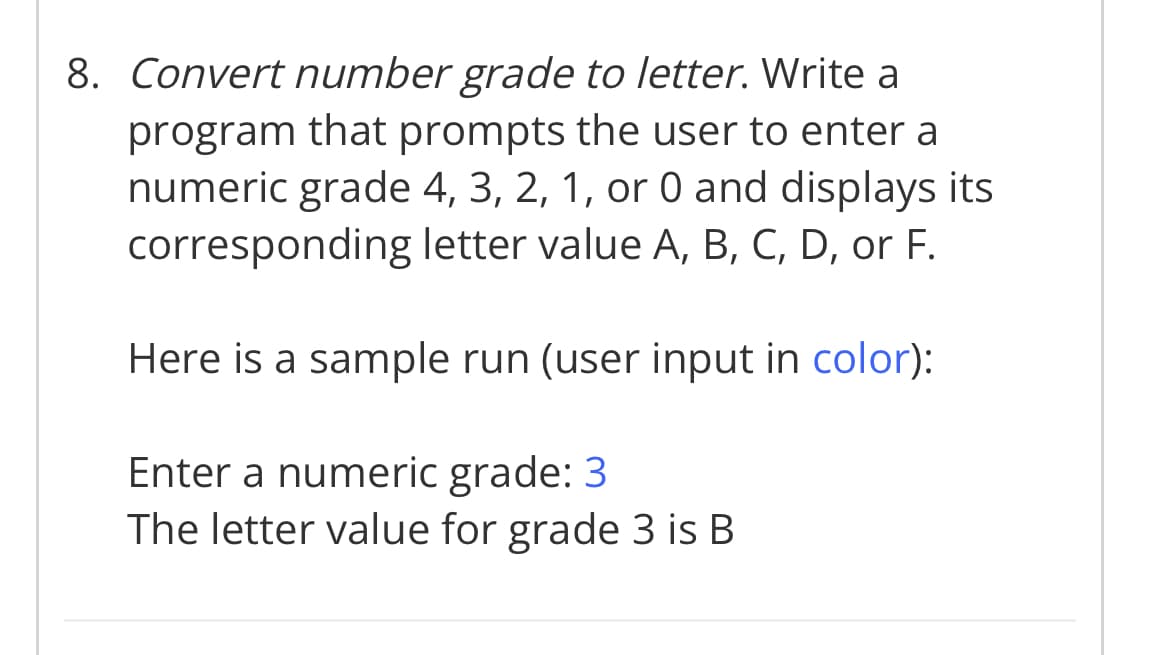
8. Convert number grade to letter. Write a program that prompts the user to enter a numeric grade 4, 3, 2, 1, or 0 and displays its corresponding letter value A, B, C, D, or F. Here is a sample run (user input in color): Enter a numeric grade: 3 The letter value for grade 3 is B
Q: Defining Data Ownership: What Is It?
A: Data Ownership: Data owners are responsible for enforcing policies and managing risks associated…
Q: What is the notion of greedy perimeter stateless routing and how does it work?
A: GPSR is a routing method for mobile, wireless networks that is both responsive and efficient..…
Q: g mean
A: In computer programming and software design, code refactoring is the most common way of rebuilding…
Q: marily
A: Generally, master file contain moderately long-lasting records about specific things or passages,…
Q: Expert systems are information retrieval systems that are capable of simulating human cognitive…
A: Cognitive capacity, also called general intelligence (g), is necessary for human adaptability and…
Q: i. Define a two-dimensional, 3 x 3 integer array called M. ii. Assign the values 1, 3, 5, 7, 9, 11,…
A: Code: #include<stdio.h>int main() { int M[3][3]; int k=1; float sum=0,count=0;…
Q: . Count the number of per character in a given sentence/paragraph. (“Hello World!” H-1, e-1, l-3,…
A: As there is no programming language mentioned so program is attempted in python language. In…
Q: What is a distributed denial-of-service attack, notwithstanding the fact that an individual cannot…
A: DDoS attacks are a major concern in Internet security today. Denial of service (DoS) attacks occur…
Q: What is the notion of greedy perimeter stateless routing and how does it work?
A:
Q: What is the complete form of the URL?
A: The link address on the internet is the URL.
Q: What is the purpose of a master file containing mostly permanent data?
A: Computer Processing System In Computer Science, a File Processing System (FPS) is a method of…
Q: When establishing backup procedures, many companies make certain that daily copies are stored off…
A: Answer
Q: Create a list of and explain the five primary areas/fields involved with internet governance, as…
A: Governance Models for the Internet: Institutional economics, which outlines three major kinds of…
Q: Make a comparison between the standard method of building software engineering architecture and the…
A: Software architecture: While a system's architecture discloses its overall structure, it hides the…
Q: (a) List the primary differences between a general-purpose OS (GPOS) and a real-time OS (RTOS). List…
A: General Purpose Operating Systems (GPOS) can deal with numerous errands proficiently, they normally…
Q: • Q1: After doing a thorough research, discuss the risks associated with ransomware attack on health…
A: In this question we have to understand the risk associated with Ransomware attack on health…
Q: Given the CRC7 polynomial X7 + X6 + x3 + x2 + X¹ and input hex data 767B calculate the CRC. Choose…
A: Answer in step 2
Q: I need to convert the drawing from a handwritten drawing to a typeface on a computer or computer in…
A: We need to draw the given image using computer tools.
Q: Why should you study software engineering ideas if you already know how to program?
A: Software Engineering: Software engineering is a method to software development that is based on a…
Q: Architect vs. organisation: what's the difference in computer terms?
A:
Q: Question 18 Retransmissions are the data link layer occur because of network congestion. Select one:…
A: Given: 18.) Retransmission are the data link layer Occurr because of network Congestion. As…
Q: Computer Science Propose your own SDN analysis, exploratory or research-question oriented, with…
A: Answer
Q: What is the purpose of a computer's cooling system? What are the different cooling methods?
A: During its use, the computer continuously generates heat which is why all computers, these days,…
Q: Is there a reason why DFDs have become so prevalent in data and processing models?
A: There are many reasons and advantages because of which the DFD's or the Data flow diagrams have been…
Q: What exactly is computer science?
A: According to the question computer science is that subject in which the computation of the math play…
Q: Where does TCP differ from UDP in terms of these three characteristics?
A: Encryption: UDP is a connectionless protocol, whereas TCP is a connection-oriented protocol. TCP has…
Q: What is the status of the literature review on rumors on social media?
A: Social Media: Websites and programmes that emphasize on communication, community-based input,…
Q: ROM vs. RAM: What's the difference?
A: The Answer is in given below steps
Q: Example Solve for minimum detectable effect (MDE): of 8 = (ta+t₁-B)*. no Let's assume σ=10 calls 100…
A: Answer:
Q: #2 Explain the following terminologies: Binary State Multi State Hard failure Soft failure
A:
Q: Does the infected machine have a way to hide the presence of an attacker's equipment?
A: Explanation: Insider vengeance: While hostile insider attacks are less common than other forms of…
Q: What is the initial value of the product for a 4 multiplication. 1011 x 1001?
A: Example of multiplying (1011)2 and(1001)2 The decimal equivalent of (1011)2 is 11 and the…
Q: Explain why using a packaged data model for a data modeling project differs from beginning with a…
A: let us see the answer;- INTRODUCTION:- Packaged data models are prepackaged data models that are not…
Q: Question 2 ( following Boolean expression to the simplest form possible B'A'+(B'+A'R + R s): Use the…
A:
Q: Why is the Waterfall technique bette registration system?
A: Waterfall Model: Waterfall model is partner illustration of a sequential model. during this model,…
Q: ROM vs. RAM: What's the difference?
A: They both are used to store the data and computer instructions.
Q: Write true if (p → r) ∧ (q → r) and (p ∨ q) → r are logically equivalent, otherwise false.
A: The answer of this question is as follows:
Q: What are the disadvantages of technology?
A: Technology is the way we apply scientific knowledge for practical purposes.
Q: Burger Shop Create an HTML page with a form for ordering burgers 1. The form should ask for the…
A: The answer is given below.
Q: How can you tell the difference between main and secondary memory?
A: Memory Memory is the storage space or brain of the computer that are used to store and retrieve the…
Q: Create a list of and explain the five primary areas/fields involved with internet governance, as…
A: Today, there are a lot of rules that govern how groups protect their data, how money is spent, how…
Q: Explain why using a packaged data model for a data modeling project differs from beginning with a…
A: Data Modeling: Data models are graphical representations of an organization's data items and the…
Q: Discuss the meaning of the phrase encryption, as well as its benefits and drawbacks.
A: Solution Encryption The act of transforming data into a secret code that hides the data's true…
Q: The following Communication Channel's Benefits and Drawbacks Simples Half-Duplex Duplex, Full
A: Transmission mode in a Computer Network: The process of exchanging data between two devices is…
Q: Understand how process synchronization is accomplished and examine the issues that occur when…
A:
Q: Explain the distinctions between variables and properties in three pages of writing
A: Given: Variables Properties
Q: python Write an expression whose value is the string that consists of the second through fifth…
A: Solution: s[2:5] Expression: String s second through fifth characters means 2-5 s[2:5] using…
Q: Differentiate between the many types of cooling systems and their roles in a computer system.
A: CPU Cooling In a computer system, there are fundamentally two types of cooling systems: Case…
Q: Traditional file processing has a lot of problems, so I'll show you a few of them
A: Introduction: The Traditional file processing systems include both manual and computer-based file…
Q: How does being a White Hat Hacker benefit one?
A: A white-hat hacker may readily test the constancy of your cyber security Portland pros in…
Step by step
Solved in 4 steps with 2 images

- (Display Magic Numbers) Display the first N magic numbers, where N is a positive number that the user provides as input. Here, a magic number is a number whose sum of its digits eventually leads to 1. For example, 1234 is a magic number because 1 + 2 + 3 + 4 = 10 and 1 + 0 = 1, while 1235 is not (1 + 2 + 3 + 5 = 11 and 1 + 1 = 2). Write a program that prints out the first N magic numbers, seven on each line. Here is the sample output: You are required to use the following function prototype: bool isMagic(int value); // Returns true if value is a magic number The outline of this function will be as follows: Step 1: Calculate the sum of digits of value Step 2: Repeat Step 1 until we get a single digit Step 3: If the resulting sum is equal to 1 then it is a magic number, otherwise notWrite a program that converts U.S. dollars toCanadian dollars, German marks, and British pounds, as shown in Figure .The user enters the U.S. dollar amount and the conversion rate, and clicks the Convertbutton to display the converted amount.2. Write a program that takes as input two opposite corners of a rectangle: the lower left-hand corner (x1,y1) and the upper right-hand corner (x2,y2). Finally, the user is prompted for the coordinates of a third point (x,y). The program should print Boolean value True orFalse based on whether the point (x,y) lies within the rectangle.>>> ========================= RESTART=========================>>>Enter x1: 1Enter y1: 3Enter x2: 10Enter y2: 6Enter x: 4Enter y: 4True>>> ========================= RESTART=========================>>>Enter x1: 1Enter y1: 3Enter x2: 10Enter y2: 6Enter x: 4Enter y: 2False
- Write a program that converts U.S. dollars to Canadian dollars, German marks, and British pounds, as shown in Figure 36.18. The user enters the U.S. dollar amount and the conversion rate, and clicks the Convert button to display the converted amount.Suppose a right triangle is placed in a plane asshown below. The right-angle point is placed at (0, 0), and the other two pointsare placed at (200, 0) and (0, 100). Write a program that prompts the user to entera point with x- and y-coordinates and determines whether the point is inside thetriangle. Here are the sample runs: Enter a point’s x- and y-coordinates: 100.5 25.5 ↵EnterThe point is in the triangle1. Write a program that asks the user to enter two positive integers, the height and length of a parallelogram and prints a parallelogram of that size with stars to the screen.
- compare loans with various interest rates) Write a programthat lets the user enter the loan amount and loan period in number of years anddisplays the monthly and total payments for each interest rate starting from 5% to10%, with an increment of 1/4. Here is a sample run: Loan Amount: 10000Number of Years: 5Interest Rate Monthly Payment Total Payment5.000% 188.71 11322.745.250% 189.86 11391.595.500% 191.01 11460.70...9.750% 211.24 12674.5510.000% 212.47 12748.23Write a program that prompts the user to enter an integer from 1 to 15 and displays a pyramid, as shown in the following sample run:. Many companies use telephone numbers like 555-GET-FOOD so the number is easier for their customers to remember. On a standard telephone, the alphabetic letters are mapped to numbers in the following fashion: A, B and C = 2 D, E and F = 3 G, H and I = 4 J, K and L = 5 M, N and O = 6 P, Q, R and S = 7 T, U and V = 8 W, X, Y and Z = 9 Write a program that asks the user to enter a 10-character number in the format XXX-XXX-XXXX. The application should display the telephone number with any alphabetic characters that appeared in the original translated to their numeric equivalent. For example, if the user enters 555-GET-FOOD, the application should display 555-438-3663. After displaying the translated telephone number, ask the user if they’d like to enter another number. If the user enters “y”, run the program again. If not, terminate the program. (10 points)Note: the sentence the program reads SHOULD NOT be hardcoded. Allow the user to enter the sentence the program reads PYTHON
- With the conversion and BMI interpretation on the image below, Using python, write a program that computes and interprets the Body Mass Index (BMI). The program prompts the user to enter his/her weight in pounds and his/her height in inches. The program then calculates the bmi using the formula: BMI = Weight(kilograms)/(height(meters))2. To convert weight in pounds(p) to kilograms(kg) use the formula: weight(kg) = weight(p) * 0.4536. To convert inches(in) into meters(m) use the formula: height(m) = height(in) * 0.0254.C++ In this task, you are required to write a code that converts an Octal number into its equivalent Decimal value or vice versa. The user first selects the conversion choice by inserting 1 or 2. Choice 1 is followed by inserting an Octal integer and getting its Decimal equivalent value as an output. Choice 2 requires inserting a Decimal integer and prints out its Octal equivalent. The Octal numeral system, is the base-8 number system, and uses the digits 0 to 7, that is to say 10 octal represents 8 Decimal and 100 octal represents 64 Decimal. Convertion from an Octal integer into Decimal In the Decimal system, each number is the digit multiplied by 10 to the power of its location (starting from 0). For example: 74 decimal = 7 x 10^1 + 4 x 10^0 1252 decimal = 1 x 10^3 + 2 x 10^2 + 5 x 10^1 + 2 x 10^0 each number is the digit multiplied by 8 to the power of its location (starting from 0). For example: 112 octal = 1 x 8^2 + 1 x 8^1 + 2 x 8^0 Converting an Octal integer into…Write a program that prompts the user to enter an integer from 1 to 7 and displays a pyramid, as presented in the following sample run ---

