8. Suppose you have a single burst of 14 bit errors (bit flips) within a packet and no other errors. Which of the following error detection schemes will detect the packet is corrupted with 100% probability? A. 8-bit checksum B. 16-bit checksum C. 8-bit CRC D. 16-bit CRC E. 16-bit MAC F. 32-bit MAC no of tho abovo
8. Suppose you have a single burst of 14 bit errors (bit flips) within a packet and no other errors. Which of the following error detection schemes will detect the packet is corrupted with 100% probability? A. 8-bit checksum B. 16-bit checksum C. 8-bit CRC D. 16-bit CRC E. 16-bit MAC F. 32-bit MAC no of tho abovo
Chapter14: Security, Troubleshooting, And Performance
Section: Chapter Questions
Problem 3RQ: Network latency issues are often caused by SELinux or AppArmor restrictions. True or False?
Related questions
Question
DO NOT COPY FROM OTHER WEBSITES
Upvote guarenteed for a correct and detailed answer. Thank you!!!
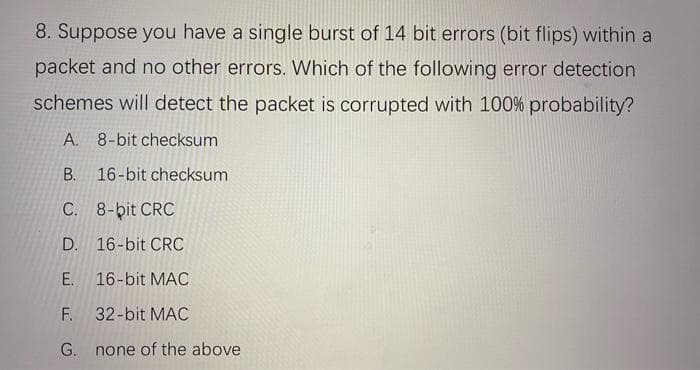
Transcribed Image Text:8. Suppose you have a single burst of 14 bit errors (bit flips) within a
packet and no other errors. Which of the following error detection
schemes will detect the packet is corrupted with 100% probability?
A. 8-bit checksum
В.
16-bit checksum
C. 8-bit CRC
D. 16-bit CRC
E. 16-bit MAC
F.
32-bit MAC
G. none of the above
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L