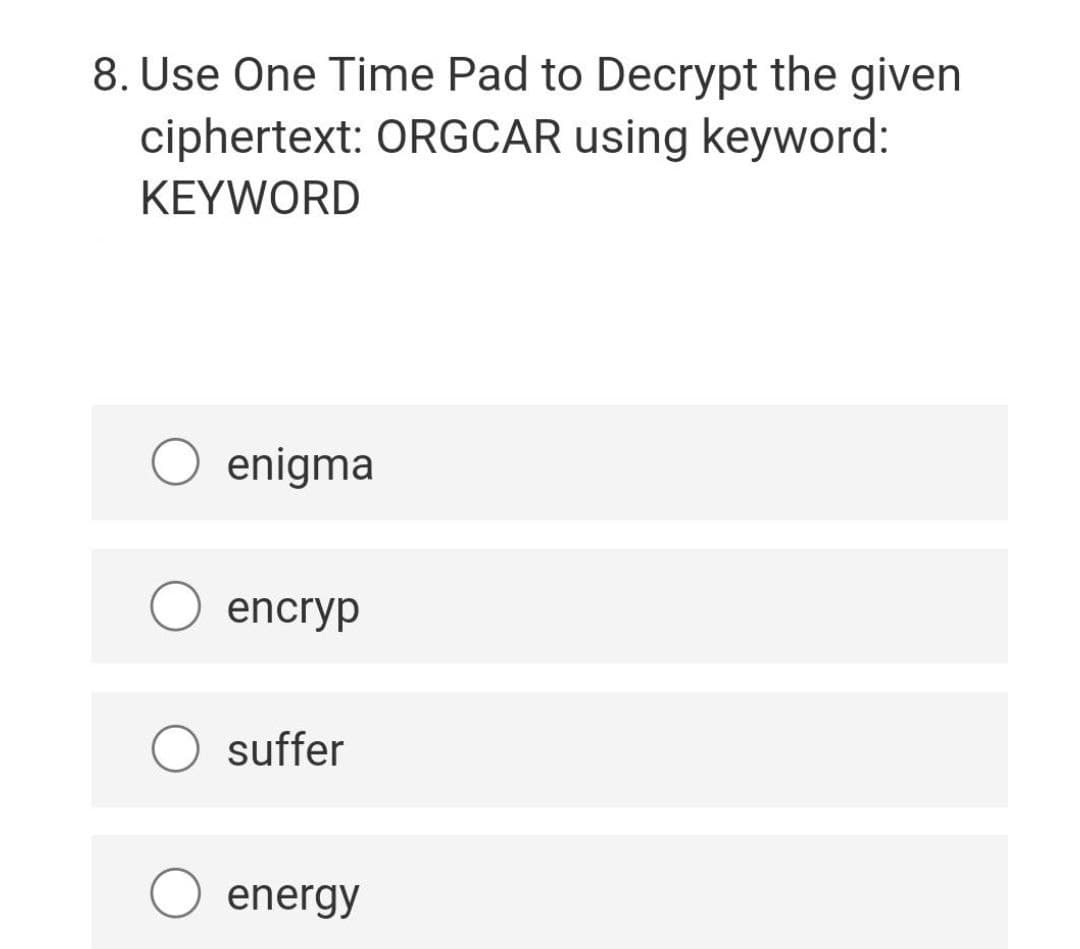
8. Use One Time Pad to Decrypt the given ciphertext: ORGCAR using keyword: KEYWORD
Q: Make an algorithm (Flowchart or pseudocode) for solving systems of linear algebraic equations (Ax=b,...
A: 1. Start 2. Input the Augmented Coefficients Matrix (A): For i = 1 to n For j = 1 to n+1 ...
Q: Q2\ convert Mealy machine to Moore .machine a/0 a/1 b/0 91 q3 b/1 0/9 0/e
A: Below is the answer to above question. I hope this will be helpful for you...
Q: E -> E + T | T T -> T * F | F F -> ( E ) | i 1) Please give the handle for E+(T*i+i) . 2) FIRST(E)...
A: Introduction: Handles: Handles are substrings of sentential forms. 1. A substring that matches the r...
Q: Bob takes medication three times a day. In the morning at 8:00, in the afternoon at 13:00, and in th...
A: The Enum in C is a data type which contains a fixed set of constants. The enum constants are implici...
Q: ascertain if the date format used in the United States is the most often used format
A: Introduction Date Format: Date format varies from region to region and country to country. The basi...
Q: SQL question SQL: employee table (id, salary) return kth highest salary
A: SELECT * FROM (SELECT ID, SALARY, DENSE_RANK()OVER(ORDER BY SALARY DESC) R FROM EMPLOYEE)WHERE R = K...
Q: Computer science What effect do gadgets and technology have on children's studies?
A: Introduction: There are both good and bad effects on children's technology and gadget research. The ...
Q: uld read the information from the file (reversing what writeEmpToFile does), create a new employee a...
A: Here I have some code.... Code:- #include <stdio.h> #include <stdlib.h> #include <str...
Q: readEmpFromFile
A: Programming is given below.
Q: 49810 in hexadecimal 2ED16 in decimal F3B16 in binary
A: Here in this question we have given number and we have to convert it into appropriate base. 49810 i...
Q: What are the primary features of cloud computing?
A: Introduction: Cloud computing is a concept that refers to the omnipotent and omniscient, rapid, and ...
Q: Create a program in c++ that gets quarterly sales from a user, and calculates the total of all four ...
A: Introduction: Here we are required to create a program in C++ that gets quarterly sales from a user,...
Q: What are the many network topologies available, and which would you suggest
A: 1. Bus Topology Bus Topology is the sort of organization geography where each hub, for example each ...
Q: Write a python code that returns the maximum and minimum value in a list using recursion functions....
A: If you are making an function recursive then you have to remember the following cases. A recursive ...
Q: Computer science What is fleet management in Amazon EC2 Auto Scaling?
A: The Amazon EC2 can be denoted as the cloud computing platform that is a part of the amazon web servi...
Q: B. Describe in words what each of these string slices does? Don't just tell me the answer but also t...
A: As per the requirement statements are executed in python. Algorithm: Step 1: Initializing string wit...
Q: Select all of true statements about the interface of partition (the main helper of the quicksort alg...
A: partition mutates its input list. yes it may mutate its input list _partition returns two lists, w...
Q: Discussion what makes Extra-Trees more random than regular Random Forests? How can this extra random...
A: 1. Extra Trees uses the entire original sample, whereas Random Forest uses bootstrap replicas, which...
Q: Explain why domain shuffling is really due to exon shuffling
A: Although certain bacteria have gained domains from eukaryotic species by horizontal gene transfer, p...
Q: Question 3: Design a circuit diagram for the following comparator system that takes three 3-bit bina...
A: Below is the answer to above question. I hope this will meet your requirements..
Q: Computer science Extend your explanation of the notion of holographic storage.
A: Introduction: Three-dimensional (3D) data storage is used in holographic storage, which is a new mea...
Q: Describe the architecture of any two Operating System Services.
A: INtro A structure of Operating System depends on how the various common components of OS are interco...
Q: Create an MVC application that passes the data of the user through a blade and gets the same data in...
A: Introduction Create an MVC application that passes the data of the user through a blade and gets the...
Q: B H) F Fig. 1
A: Here in this question we have given a graph.and we have akes to apply DFS on this graph and find ord...
Q: Make a distinction between assembly code and source code.
A: Introduction: The term "source code" refers to high-level code created by a human/programmer. The so...
Q: What's the best way to make a computer program random? How can the values generated by the rand func...
A: INTRODUCTION: Let's look at the two most common approaches for generating random numbers. The first...
Q: Consider a 5-bit two's complement representation. Fill in the empty boxes in the following table. TM...
A: Below is the answer to above question. I hope this will meet your requirements...
Q: Briefly describe the services provided by the data link layer. Define framing and the reason for its...
A: Introduction Briefly describe the services provided by the data link layer. Define framing and t...
Q: Please answer it in Python write a function word_vers_dictionary(word), which takes a word (string...
A: According to company guidelines we are supposed to answer only one question. Kindly repost other que...
Q: Discuss the services that operating systems offer, as well as the three interfaces that operating sy...
A: Serives that operating system offer anf=d three interfaces explain in below step
Q: What two examples come to mind when it comes to complex passwords?
A: Introduction: A password that is difficult to guess by people as well as machines.
Q: Write a Python script that reads the user's year of birth, then display their age along with one of ...
A: Python code for above : from datetime import date # read users year of birth year = int(input("E...
Q: How many distinct OS states may a process have?
A: « A process is an executing program or series of guidelines. » It goes through various states at the...
Q: Make a mental image of a virtual machine.
A: Intro EXPLANATION : VIRTUAL MACHINE: A software-based system with its operating system on a host se...
Q: Assume the usage of ARM assembly language instruction: STR R0,[R1],#0x8. Assume that Register R0 con...
A: Given: ARM assembly language instruction: R0 Contains 0xA0 and R1 contains 0x7008. STR R0,[R1],#0...
Q: What is the difference between asymmetric and symmetric encryption?
A: Introduction: Asymmetric encryption is sometimes known as public-key cryptography.
Q: What are an operating system's two modes and two primary functions? What is the file system's primar...
A: Introduction: An operating system: OS is a software program that connects a computer user to the har...
Q: Distinguish between the terms "validation" and "verification." Examples should be given.
A: Introduction: The steps of verification and validation are used to ensure that the data given by the...
Q: What Are the Benefits and Drawbacks of Cloud Storage for a Small Business?
A: Introduction What Are the Benefits and Drawbacks of Cloud Storage for a Small Business?
Q: True or false? Justify. (a) 25mod11=3 (b) 3mod25=11 (d) 25≡11 (mod3) (e) 3≡25 (mod11) (c) 11mod3=25 ...
A: Answer the above questions are as follows:
Q: Define reliable communication. Also, discuss the independent sources from which threats to integrity...
A: Introduction: Communication that is dependable: Validity and integrity are used to define reliable c...
Q: What are the objectives of a distributed database system ?
A: Introduction: A distributed database system is a database system in which the data or information is...
Q: What is the difference between a SLA and a hard disk drive (HDD)?
A: Answer is given below :
Q: What are the advantages of a binary search tree over things like a sorted Linked List or a Sorted Ar...
A: A binary tree has a special structure in which each node can have a number of two offspring. A binar...
Q: given this short program:
A: In this question, partially code is given and we have to complete it so that it should give the expe...
Q: Computer Science The draw selection method implementation does not create a dashed box. Instead it ...
A: The concept that could be used over here is overloading.
Q: Implications and Equivalence of Logic and Reasoning Give two examples of statements with ramifica...
A: Introduction The question is: Give two example statements of implications encountered in everyday ...
Q: What security techniques/mechanisms exist to secure vehicular or vehicle-to-vehicle communications? ...
A: Introduction: The communication layer consists of vehicular communications that can take place both ...
Q: Why and how do local minima affect k-means clustering? What are our options for dealing with these...
A: Introduction Computer forensics : Computer Forensics: the process of collecting, preserving, analy...
Q: Which cloud management technique executes a series of tasks in a workflow? Automation IaC SLA Or...
A: -answer is Orchestration -orchestration is a cloud management technique in which ...
Step by step
Solved in 2 steps with 2 images

- Using netbeans, fix the given code below and run it using netbeans. Show the screenshot result. It should be the same as the result picture given belowText line breaks and returns are controlled using which tags?. <b></b> <p></p> <ol></ol> <a></a>Make two edittext, where user can enter 2 numbers. Also make a Button which will add two numbers and display the result in Toast message and in TextView.(Android Application)
- Write a script that calculates the squares and cubes of the numbers from 0 to 5 and outputs HTML5 text that displays the resulting values in an HTML5 table format, as show below. [Note: This script does not require any input from the user.]Which element of the JavaScript expressiondocument.write("<p>The current time in " + cityName + " is " + currentTime + ".</p>");is a literal? a. cityName b. "<p>The current time in " c. document d. writeWhich of the following is used to change the direction of textSelect one:a. Orientationb. Alignmentc. Merge and centerd. Wrap text
- With python When opening a document as csvfile and using: csv.reader(csvfile, delimiter=';') How do I get it to not read the first two lines?Use your specific details like name and email id to generate a full key using gpg tool with and upload the public key on the Ubuntu keyserver (https://keyserver.ubuntu.com/).I try to download the image that I uploaded in the website using Python Selenium, but I get an error code of urllib.error.URLError: <urlopen error unknown url type: blob> How do I download the image file with src url starting with "blob:http"?
- Convert the following infix expressions into their corresponding prefix forms as shown by the screenshot below. The second screenshot show all possible answer for each part of the question, match the correct answer to each question accordingly.3. In the “Desktop” folder, create a symbolic link to the videos folder and verify.In Javascript, Create a mouseOver event function, that will change the colour of an HTML item (i.e. a button or a list item) to green, then to black after 5 seconds



