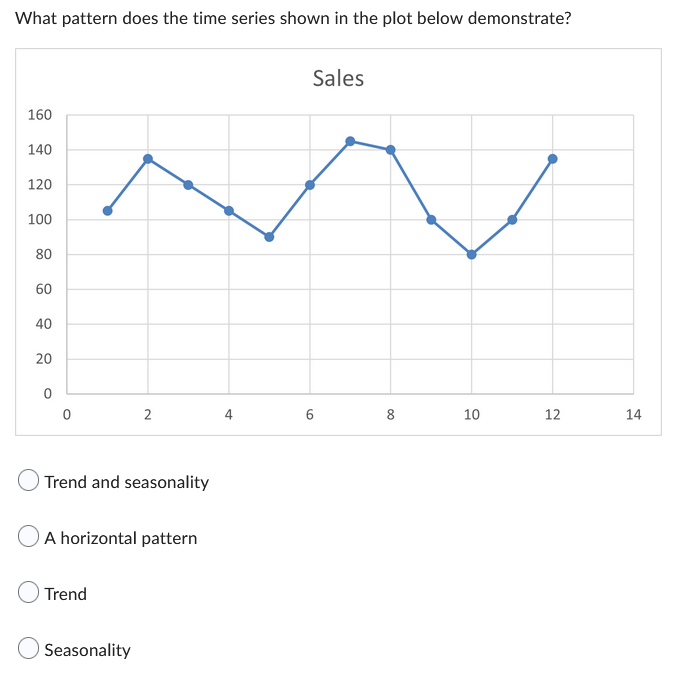
80 60 40 20 0 0 2 Trend and seasonality A horizontal pattern Trend 4 6 8
Q: Discuss the trade off between fairness and throughput of operations in the readers-writers problem.…
A: Definition: This implies that a steady flow of readers may eventually starve all aspiring writers by…
Q: What precisely is multithreading?
A: Threads It is a lightweight procedure that accomplishes a specific job. The concurrent execution of…
Q: Given a CFG G over {a, b}, G: S -> SAB | a | B | A -> a | ABa B-> b | ab (a) Prove that G is…
A: (a) When there are many Left Most Derivation Trees (LMDTs) or Right Most Derivation Trees (RMDTs)…
Q: a. The differences among sequential access, direct access, and random access?
A: Answer. A.The distinction between the consecutive access, direct access and random access.When…
Q: Using layered protocols is prudent for the two reasons listed below.
A: Introduction: Protocol layering creates well-defined interfaces across levels, ensuring that changes…
Q: Q4) Write C++ program that create two objects (A, B) from the queue class, and do the following Add…
A: I have used C++ Queue provided by STL Library to implement your program, Kindly check it out the…
Q: Describe a recent issue you observed with concurrent processing in an operating system.
A: Concurrent processing is a computing method where multiple processes execute instructions…
Q: How is software maintenance measured?
A: Given: In software maintenance, there are five different types of metrics. Compliance with…
Q: In computer science, what is the difference between a process and a thread?
A: Computer science: To research and create computers, networks, hardware, software, databases, and…
Q: Consider a hypothetical microprocessor generating a 16-bit address (for example, assume that the…
A: Answer the above questions are as follows
Q: Create a list of the various types of DNS records. Each should be elucidated with concrete examples…
A: The Answer start from step-2.
Q: one way of detecting errors is to transmit data as a block of n rows of k bits per row and adding…
A: Introduction: Yes. There will also be three mistakes found. They will be caught if they are in the…
Q: Figure shows a sliding window. The input text stream is ikaccbadaccbaccbaccgikmoabe. In part (a) of…
A: a. Answer: - Triple: <6.2, C(c)> - Search buffer of size 9 - Look-ahead buffer of size 6 b.…
Q: A disadvantage of a broadcast subnet is the capacity wasted when multiple hosts attempt to access…
A: The broadcast address is the address that is used to target the systems on a particular subnet…
Q: 6. Write a java program to: a. Declare an array of 10 integers b. Read its values from the user. c.…
A: As per our guidelines, only 3 sub parts will be answered. So, please repost the remaining questions…
Q: one way of detecting errors is to transmit data as a block of n rows of k bits per row and adding…
A:
Q: What occurs if the programmer deletes the member function getBalance () and replaces sac.getBalance…
A: To conceal class data, the private access specifier is utilized. It hides the data from the rest of…
Q: You are required to write a code that requests the user to enter four integer numbers that…
A: Since no programming language is mentioned, I am using python. Code: majors=["Medical…
Q: What does DFR stand for?
A: To specify a declining rate of failure: Reducing the occurrence of errors: Over time, the odds of…
Q: Is the usage of user-level threads superior than kernel-level threads? What is the difference…
A: Definition: What advantages do user-level threads have over kernel-level threads? They are…
Q: ribe in your own words the meaning of the following probler a. The differences among sequential…
A: Lets see the solution.
Q: What model is used to determine how secure software is
A: There are several models available for software testing, including:
Q: How can I import mysql databases using the command line interface using a SQL query?
A: MySQL MySQL is an open-source application for relational database administration. It is one of the…
Q: How does the Compiler traverse the several stages? Is it feasible to offer an example of each step's…
A: Answer:- Compilers are computer programmes that convert high-level source code authored by…
Q: write by Python programing Write a program that prompts the user to enter the amount of cash, then…
A: About python language A high-level, interpreted, the general-purpose programming language is called…
Q: When a signal is received, the CPU suspends its current activity to process the request. The…
A: Introduction via diverse input and output devices, the CPU ought to be capable of talking with its…
Q: Explain the several steps of the SDLC and the deliverables associated with each.
A: Given: The Software Development Life cycle refers the process of developing software applications…
Q: What are the numerous factors to be considered for a compiler that creates accurate and efficient…
A: Actor to Consider Mean: To factor is to take anything into account when coming to a judgement or…
Q: Why do Solaris, Linux, and Windows 2000 use spinlocks as a synchronization mechanism only on…
A:
Q: What are the advantages of doing code reviews as part of the software development process' quality…
A: Having a senior developer look through your code is known as "code review." When the code is…
Q: 1. For the network topology given in Fig. 1, give distance-vector table for nodes A and E. A O- | 5…
A:
Q: Five arguments summarize the significance of generic software updates and patches: In what manner do…
A: These small pop-up windows might be familiar to you: They let you know that there are accessible…
Q: What purpose do coding norms serve? Analyze the Java programming language's coding conventions.
A: Coding conventions: Help people understand the code better, or we can say that they make the code…
Q: Your father purchased 50 nodes to launch a software development company. He instructed you to…
A: There are various kinds of network topology: Asterism Bus Layout TOPOLOGY phylogency Mesh…
Q: Suppose you have been tasked with creating storage devices such as Floppy disk drives and Flash…
A: Devices for storage: The term "storage" is used to refer to all of the many media formats on which a…
Q: Consider the following process for generating binaries. A compiler is used to generate the object…
A:
Q: What is mobile forensics What are the phases of mobile forensic What are the mobile forensic tools…
A: About Mobile forensics Recovery of digital evidence or data from a mobile device is still the…
Q: Is it feasible to make a diagram of the architecture of virtual machines?
A: Definition: Around 1960, the idea of a virtual machine was first suggested. It represents the…
Q: A compiler that is both effective and precise must take into account the following criteria:…
A: enhancing the compiler: A computer programme known as an optimizing compiler aims to minimize or…
Q: In class, you learnt about the many methods through which software may be made available, both for…
A: Introduction: Software is a collection of programmes that have been created with a specific…
Q: What is the difference between a client and a server when it comes to computers?
A: Client A client is a user application that connects to a server to get the right of entry to…
Q: How can you know if the ACL is malfunctioning?
A: Access Control Lists (ACL) is an abbreviation for Access Control Lists: The transmission control…
Q: Exists a problem domain addressed by the workflow management system?
A: Answer:- Two types of actions—the performance of a task and the dissemination of a task's…
Q: signal is received, the CPU suspends its current activity to process the request. hnique used in…
A: Given: The processor must be able to interact with its environment via a variety of input and output…
Q: How does the workflow management system include technology (hardware and/or software)?
A: workflow management A workflow management system is a software application designed to facilitate…
Q: What purpose do protocols serve in network communication? Describe the communication between a web…
A: Definition: Consider the TCP protocol as an example, where reservations are made first and then…
Q: What are the differences between Linux and Windows?
A: Linux: Linux may be a free, open-source operating system that supports operating system standards.…
Q: Describe how the device manager of the operating system regulates the system's efficiency.
A: Device manager in OS The device manager in the operating system functions as a control panel in the…
Q: The apparent overhead of copying at each stage is the most common criticism of layered protocols.…
A: Please find the response to the preceding query below: Here, we should first understand what…
Q: Compiler's phase-based fundamental features are as follows: Define each step and offer an example…
A: Phases of the Compiler: There are several stages in the compilation process. Each step begins with a…
Step by step
Solved in 2 steps

- What but patterns are represented by a. 0x5FD97, b. 0x610A, 0xABCD and 0x0100SYN+ACK segment can carry 2 byte of data only. a) True b) False Note: Select one answer. Course name: Computer Networks.Correct and detailed answer will be Upvoted else downvoted. Thank you!Multiple Comparisons Dependent Variable: Sessions Tukey HSD (I) Group (J) Group Mean Difference (I-J) Std. Error Sig. 95% Confidence Interval Lower Bound Upper Bound 1.00 2.00 -2.33333 .97996 .109 -5.2194 .5527 3.00 -5.91667* .91667 <.001 -8.6163 -3.2170 2.00 1.00 2.33333 .97996 .109 -.5527 5.2194 3.00 -3.58333* .91667 .014 -6.2830 -.8837 3.00 1.00 5.91667* .91667 <.001 3.2170 8.6163 2.00 3.58333* .91667 .014 .8837 6.2830 *. The mean difference is significant at the 0.05 level. Question Why do researchers compute Tukey HSD tests? Between which two groups is there a statically significant difference? If a researcher fails to reject the null hypothesis for the ANOVA f test, should she conduct Tukey HSD tests?
- Upload the attached dataset to Rstudio From the attached dataset: choose a nominal variable and plot its pie chart choose a nominal/ordinal variable and plot its bar chart choose a numerical variable and plot its histogram and its densityIf true, then Codewords (n) and datawords (k) are dissimilar because k=n+FCS (Frame Check Sequence).data2.asm .ORIG x3500HELLO .STRINGZ "+9144827365544332109011\n" data3.asm .ORIG x3500HELLO .STRINGZ "-9144827365544332109011
- What do the four least significant bits of each final color value for each pixel mean?CHOOSE THE CORRECT OPTION If each pixel of an acquired image is represented by 11 bits, the number of distinct gray intensities that are available in the image is given as A. 2048 B. 2047 C. 1023 D. 1024How to print current date in JavaScript with time

