9. Consider the code example for allocating and releasing processes as shown below. #define MAX PROCESSES 255 int number.of-processes = 0; /+ the implementation of fork() calls this function / int allocate.process () { int new.pid; if (number.of.processes - MAX PROCESSES) return -1; else { /* allocate necessary process resources / ++number.of.processes; return new.pid; /+ the implementation of exit () calls this function / void release.process () { /* release process resources +/ --number.of.processes; Figure 5.23 Allocating and releasing processes. a. Identify the race condition(s). b. Assume you have a mutex lock named mutex with the operations acquire() and release(). Indicate where the locking needs to be placed to prevent the race condition(s).
9. Consider the code example for allocating and releasing processes as shown below. #define MAX PROCESSES 255 int number.of-processes = 0; /+ the implementation of fork() calls this function / int allocate.process () { int new.pid; if (number.of.processes - MAX PROCESSES) return -1; else { /* allocate necessary process resources / ++number.of.processes; return new.pid; /+ the implementation of exit () calls this function / void release.process () { /* release process resources +/ --number.of.processes; Figure 5.23 Allocating and releasing processes. a. Identify the race condition(s). b. Assume you have a mutex lock named mutex with the operations acquire() and release(). Indicate where the locking needs to be placed to prevent the race condition(s).
Chapter8: Advanced Method Concepts
Section: Chapter Questions
Problem 7RQ
Related questions
Question
100%
Don't copied please i will upvote.
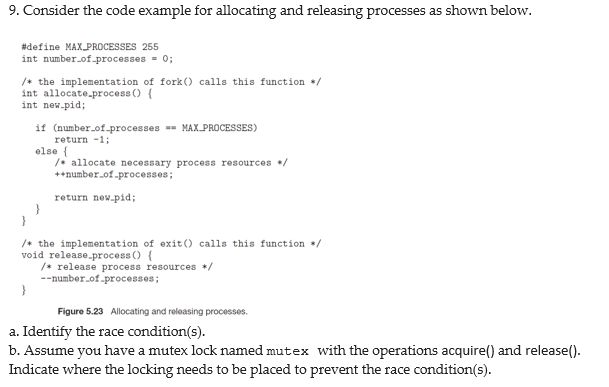
Transcribed Image Text:9. Consider the code example for allocating and releasing processes as shown below.
#define MAXPROCESSES 255
int number.of-processes = 0;
/+ the implementation of fork () calls this function /
int allocate.process () {
int new-pid;
if (number_of-processes - MAX PROCESSES)
return -1;
else {
/* allocate necessary process resources */
++number.of.processes;
return new.pid;
+ the implementation of exit() calls this function /
void release.process () {
/* release process resources */
--number.of.processes;
Figure 5.23 Allocating and releasing processes.
a. Identify the race condition(s).
b. Assume you have a mutex lock named mutex with the operations acquire() and release().
Indicate where the locking needs to be placed to prevent the race condition(s).
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,