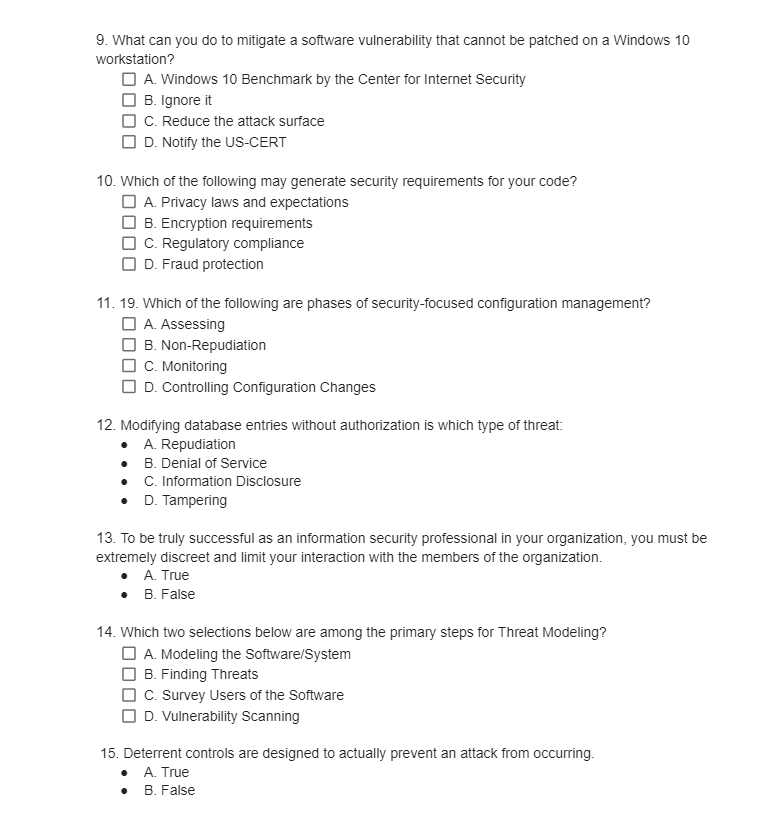
9. What can you do to mitigate a software vulnerability that cannot be patched on a Windows 10 workstation? A. Windows 10 Benchmark by the Center for Internet Security B. Ignore it C. Reduce the attack surface D. Notify the US-CERT 10. Which of the following may generate security requirements for your code? A. Privacy laws and expectations B. Encryption requirements C. Regulatory compliance D. Fraud protection 11. 19. Which of the following are phases of security-focused configuration management? ☐A. Assessing B. Non-Repudiation C. Monitoring D. Controlling Configuration Changes 12. Modifying database entries without authorization is which type of threat: A. Repudiation B. Denial of Service C. Information Disclosure D. Tampering 13. To be truly successful as an information security professional in your organization, you must be extremely discreet and limit your interaction with the members of the organization. A. True B. False 14. Which two selections below are among the primary steps for Threat Modeling? A. Modeling the Software/System B. Finding Threats C. Survey Users of the Software D. Vulnerability Scanning 15. Deterrent controls are designed to actually prevent an attack from occurring. • A. True B. False
9. What can you do to mitigate a software vulnerability that cannot be patched on a Windows 10 workstation? A. Windows 10 Benchmark by the Center for Internet Security B. Ignore it C. Reduce the attack surface D. Notify the US-CERT 10. Which of the following may generate security requirements for your code? A. Privacy laws and expectations B. Encryption requirements C. Regulatory compliance D. Fraud protection 11. 19. Which of the following are phases of security-focused configuration management? ☐A. Assessing B. Non-Repudiation C. Monitoring D. Controlling Configuration Changes 12. Modifying database entries without authorization is which type of threat: A. Repudiation B. Denial of Service C. Information Disclosure D. Tampering 13. To be truly successful as an information security professional in your organization, you must be extremely discreet and limit your interaction with the members of the organization. A. True B. False 14. Which two selections below are among the primary steps for Threat Modeling? A. Modeling the Software/System B. Finding Threats C. Survey Users of the Software D. Vulnerability Scanning 15. Deterrent controls are designed to actually prevent an attack from occurring. • A. True B. False
Chapter5: Advanced Personalization And Customization
Section: Chapter Questions
Problem 1AYK
Related questions
Question
Transcribed Image Text:9. What can you do to mitigate a software vulnerability that cannot be patched on a Windows 10
workstation?
A. Windows 10 Benchmark by the Center for Internet Security
B. Ignore it
C. Reduce the attack surface
D. Notify the US-CERT
10. Which of the following may generate security requirements for your code?
A. Privacy laws and expectations
B. Encryption requirements
C. Regulatory compliance
D. Fraud protection
11. 19. Which of the following are phases of security-focused configuration management?
A. Assessing
B. Non-Repudiation
C. Monitoring
D. Controlling Configuration Changes
12. Modifying database entries without authorization is which type of threat:
A. Repudiation
B. Denial of Service
•
C. Information Disclosure
• D. Tampering
13. To be truly successful as an information security professional in your organization, you must be
extremely discreet and limit your interaction with the members of the organization.
A. True
• B. False
14. Which two selections below are among the primary steps for Threat Modeling?
A. Modeling the Software/System
B. Finding Threats
C. Survey Users of the Software
D. Vulnerability Scanning
15. Deterrent controls are designed to actually prevent an attack from occurring.
A. True
B. False
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Microsoft Windows 10 Comprehensive 2019
Computer Science
ISBN:
9780357392607
Author:
FREUND
Publisher:
Cengage

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,