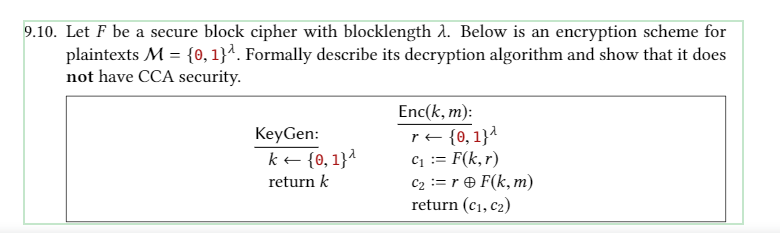
9.10. Let F be a secure block cipher with blocklength 2. Below is an encryption scheme for plaintexts M = {0, 1}². Formally describe its decryption algorithm and show that it does not have CCA security. Enc(k, m): re {0,1}^ c1 := F(k,r) C2 := r O F(k, m) return (c1, c2) KeyGen: k+ {0, 1}^ return k
Q: What role do data models play in database development?
A: Introduction: Data modelling is a method for defining and organising business operations. It allows ...
Q: Please solve in python code! Thanks! A plane flying horizontally with a speed of 300 km/hr passes ov...
A:
Q: How do I write a 7 segments display code in VHDL? Please help
A: According to the information given:- We have to the write VHDL of 7 segments display
Q: As a Python programmer in one company/institution, you are task to create a program that converts te...
A: In this user has to input choice whether user wants to convert Celsius to Fahrenheit or Fahrenheit t...
Q: Which one is true? A) An inner class can be declared public or private subject to the same visibili...
A: All the statements are true. So option A,B,C,D are correct
Q: .3 Computer Problems
A: Irregular Walk (Implementation in Python) Presentation An irregular walk is a numerical item, known ...
Q: Show that a function y = n^4 + 3 can not belong to the set O(1) using the formal definition of Big-O
A: Show that a function y = n^4 + 3 can not belong to the set O(1) using the formal definition of Big-O
Q: In a few words, describe dynamic memory allocation.
A: Dynamic memory allocation is the allocation of the memory by the program at runtime. In simple scena...
Q: Let A be an array of integers of size 10, whose ith entry is represented by A[i] for i = 0 to 9, and...
A: - According to the rules, we have to check for the element 85 position in the array.
Q: Program to demonstrate the inorder, preorder and postorder traversal of a binary tree. root H
A: According to the Bartelby guideline we are suppose to answer only one question at a time Kindly repo...
Q: Plot the following for x = [1:10]. Plot on a linear plot and on a semilog plot (y-axis logarithmic) ...
A: Note: There are different plotting styles for this question. So the answer can vary according to pro...
Q: Compare and contrast the benefits and drawbacks of batch versus online data input methods. There is ...
A: Batch input methods, such as filling out a form by hand, are a much more tedious and time-consuming ...
Q: Create a program that will display a number from 5 to 100. Use iterative structure. Coding using...
A: In this question, we are asked to write a C program which displays from 5 to 100 Explained each line...
Q: # In[ ]: |def minIndexAfter (items, startPos): minIndex = startPos i = startPos + 1 while (i < len (...
A: Note: As per our guidelines we are supposed to answer only one question. Kindly repost other questio...
Q: Explain why the Electronic Communications Privacy Act of 1986 does not apply to you. Communicatio...
A: Intro People in the United States use email on a daily basis, not only for personal communication, b...
Q: x^4-x-10=0 Find the root/s using fixed-point iteration
A:
Q: Please give me recommendations and implementation in Memory Management in Linux. Thank you!
A: The answer is as follows.
Q: (a) How are RAM and ROM different? (b) What are RAM and ROM?
A: Solution:
Q: The relationship between an interface and the class that implements it O Inheritance O None of these...
A: Option 1: Inheritance
Q: Construct a Java program to provide a file named file.txt if it does not exist. Write 100 integers ...
A: 100 integers created randomly into the file using text I/O. Integers are separated by spaces in th...
Q: The Harvard robotics club has organized a Robothon. n robots are placed along the edge of a circular...
A: Introduction: Now we can see that the most outstanding amount of money that the club could end up sp...
Q: b. Modify the array so that (1) every item is shifted one place "to the left" (and the current first...
A: I give the code along with output and code screenshot
Q: O consider the consider the followlng tables :- table names : sales city paris Salesman-id commissio...
A: SQL is used to communicate with the database. It supports several queries to create a table, insert ...
Q: Invoicing.java Create a class named Invoicing (no instance private data fields) that includes three...
A: Here is the detailed explanation of the program
Q: What exactly is a reversible schedule? Why is it desirable for schedules to be recoverable? Is it ev...
A: Introduction: A schedule is said to be recoverable if, for each pair of T1 and T2 transactions, the ...
Q: ing System; mespace HelloWorld { class Hello { static void Main(string[] args) { Console.Writeline("...
A: catchphrases are Namespace Keywords: using
Q: Q-1 Place the following values on the memory given at right side A) Write the memory address of Dark...
A: Q-1 Place the following values on the memory given at right side A) Write the memory address of Dark...
Q: The assembler pseudoinstruction ble $20,$15,Label branches to Label if $20 ≤ $15 in signed integer...
A: To choose right option
Q: Python code Write a function that, given two integers, return the product of every integer between t...
A: As per our guidelines we are suppose to answer only first question. Kindly repost other question sep...
Q: Because microprocessor CPUs are incapable of understanding mnemonics as they are, they must be trans...
A: Introduction: The microprocessor is the heart of a computer system, performing arithmetic and logic ...
Q: Identify, list, and define an information system's six components.
A: Identify, list, and define an information system's six components.
Q: Find error(s) in the following code(if any) and rewrite code and underline each correction: x= i...
A: Introduction: Find error(s) in the following code(if any) and rewrite code and underline each correc...
Q: Write a C program that creates an array of 10 floating values. After accepting the inputs, display a...
A: #include<stdio.h>#include<limits.h> int main(){ float arr[10]; float min = INT_MAX...
Q: If this code runs from its start until the endpo : $0x1,8edx $0x8,%ecx Весх, &есх 0x40107e : mov Ox4...
A:
Q: Memory that is logical is called "memory that is not real."
A: Logical Memory is limited by the size of the hard disk. Generally RAM has also direct access to the ...
Q: Instructions: Underline the infinitive and box the infinitive phrase in each sentence and identify i...
A: Our plan is to go to Cebu in October.
Q: What are some important concerns to consider when backing up and recovering data?
A: When backing up data, it’s important to consider important concerns, such as the backup destination,...
Q: There are multiple ways to prevent from this spyware. There are some that should always keep in mind...
A: Auditing is a mechanism, which is used to record the actions whatever happens on a computer system. ...
Q: I am trying to creat a html/css/javascript page that looks like this.... I am almost done ...
A: html code: <html> <head lang="en"> <meta charset="UTF-8"> <title>Quiz</t...
Q: xplain how the Newton-Raphson Method locates the root of a functio
A: Newton-Raphson Method to locates the root of a function, here is the explanation of Newton-Raphson ...
Q: Write the differences between Von Neumann and Harvard architecture..
A: VON NEUMANN ARCHITECTURE It is an old computer architecture based on the notion of a stored programm...
Q: Based on your understanding, discuss briefly what is censoring in the context of time-to-event data?
A: Given To know about the censoring in the context of time-to-event data
Q: What does this code accomplish? subi $sp,$sp,8 sw $3,4($sp) sw $4,0($sp) push the contents of...
A: push the contents of $3,then $4 onto stack Explanation:- subi $sp,$sp,8 this instruction will make a...
Q: Find the context free rules and hence the Context Free Grammar for the following sentences: 1. I wa...
A: here we given the solution for first three sentences as per the instructions. context free rules for...
Q: What kinds of artificial intelligence are there? Define artificial intelligence domains and provide ...
A: Introduction: The computer simulation of human intelligence processes is known as artificial intelli...
Q: You are to automate some repetitive tasks. The tasks are as follows: 1) Add a new product to the que...
A: Code : #include<bits/stdc++.h> using namespace std; struct node{ int prod_ID; char label...
Q: This question concerns the field GF(256). The modulus is P(x) = x° + x* + x° + x + 1. answer the fol...
A: (0x52)16 (0xA5)16 x7 + x3 + x + 1 x5 + x3 + x2 + 1
Q: What is a correct syntax to output "Hello World" in Python? print("Hello World") echo("Hello World")...
A: In python, For printing, print(" ") is used For commenting, # is used
Q: Write the sum -3+5 – 7+9 – 11+ 13 – 15 + 17 – 19 +21 using sigma notation. The form of your answer w...
A: Given series is, -3+5-7+9-11+13-15+17-19+21 This series contains the odd numbers one one starting fr...
Q: For the following data set. Use Decision Tree classification to build the model to classify the test...
A: The decision tree classification to bulid the model to classify the test records is as follows.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Alice computes the Secret prefix MAC (page 322: secret prefix MAC(x) = h(key || x)) for the message ”GD” (in ASCII) with key “H” (in ASCII) that both Alice and Bob know. The hash function that is used is h(x1x2x3)= g(g(x1 XOR x2) XOR x3 ) where each xi is a character represented as 8 bits, and g(x) is a 8-bit string that is equal to the complement of bits in x. For example, g(10110011) = 01001100. The MAC is 8 bits. (8-bit ASCII representation of characters is available at https://www.asciitable.com/ Take the Hexa equivalent and convert it to 8 bits each. For example character "A" is hexa 41 or 0100 0001 in bits) What is the Secret prefix MAC computed by Alice? Show the MAC as the single character. What information is sent by Alice to Bob?Suppose Alice computes the Secret suffix MAC (page 322: secret suffix MAC(x) = h(x || key)) for the message ”AM” with key “G” that both Alice and Bob know. The hash function that is used is h(x1x2x3)= g(g(x1 XOR x2) XOR x3 ) where each xi is a character represented as 8 bits, and g(x) is a 8-bit string that is equal to the complement of bits in x. For example, g(10110011) = 01001100. The MAC is 8 bits. (8-bit ASCII representation of the characters is given below.) What is the Secret suffix MAC computed by Alice? Show the MAC as the single character. What information is sent by Alice to Bob.Write a Python script that implements the CHF (the Casual Hash Function.) The input data should be split into blocks of 32 bits. If the last block is smaller than 32 bits, the remaining bits should be filled with 1 followed by as many zeros as required. A and B are 2 buffers with specific values (see below). Each block in the message should be combined as shown in the image below. All resulting blocks (i.e. FBI) should be combined with "&" to produce the digest. The size of the digest is 64 bits. Calculate the digest for the string: "Alright, but apart from the sanitation, the medicine, education, wine, public order, irrigation, roads, the fresh-water system, and public health, what have the Romans ever done for us?" steps on how are in the attached pictures
- Write a Python script that implements the CHF (the Casual Hash Function.) The input data should be split into blocks of 32 bits. If the last block is smaller than 32 bits, the remaining bits should be filled with 1 followed by as many zeros as required. A and B are 2 buffers with specific values (see below). Each block in the message should be combined as shown in the image below. All resulting blocks (i.e. FBI) should be combined with "&" to produce the digest. The size of the digest is 64 bits. Calculate the digest for the string: "Alright, but apart from the sanitation, the medicine, education, wine, public order, irrigation, roads, the fresh-water system, and public health, what have the Romans ever done for us?"1. We have defined a symmetric cryptography algorithm using the XOR operator. Assume our messages (before encryption) consist of only uppercase and lowercase letters, digits and blank character. In addition, assume the key size is only one byte which is an integer between 0 and 255 (inclusive). The pseudocode of the proposed encryption algorithm is as follows: Read the message // for example message=”Hi” Read the key // for example key=10 Cipher_text=[] //an empty list for i=1 to len(message): Cipher_text= Cipher_text.append(XOR(message[i],key)) Return Cipher_text Assume XOR function, takes a character and the key, then returns the result of bitwise XOR of ASCII code of the letter with the key as an (one byte) integer. For example, if message=”Hi” and key=10, then we should first calculate the ASCCI code of “H” which is 72 and find the result of (72 XOR 10) which is 66. Then the ASCCI code of “i” is 105, so the result of (105 XOR 10) is 99. Thus the Cipher_text would be…1. We have defined a symmetric cryptography algorithm using the XOR operator. Assume our messages (before encryption) consist of only uppercase and lowercase letters, digits and blank character. In addition, assume the key size is only one byte which is an integer between 0 and 255 (inclusive). The pseudocode of the proposed encryption algorithm is as follows: Read the message // for example message=”Hi” Read the key // for example key=10 Cipher_text=[] //an empty list for i=1 to len(message): Cipher_text= Cipher_text.append(XOR(message[i],key)) Return Cipher_text Assume XOR function, takes a character and the key, then returns the result of bitwise XOR of ASCII code of the letter with the key as an (one byte) integer. For example, if message=”Hi” and key=10, then we should first calculate the ASCCI code of “H” which is 72 and find the result of (72 XOR 10) which is 66. Then the ASCCI code of “i” is 105, so the result of (105 XOR 10) is 99. Thus the Cipher_text would be…
- Now consider the opposite problem: using an encryption algorithm to construct a oneway hash function. Consider using RSA with a known key. Then process a message consisting of a sequence of blocks as follows: Encrypt the first block, XOR the result with the second block and encrypt again, etc. Show that this scheme is not secure by solving the following problem. Given a two-block message B1, B2, and its hash RSAH(B1, B2) = RSA(RSA (B1) +B2) Given an arbitrary block C1, choose C2 so that RSAH(C1, C2) = RSAH(B1, B2). Thus, the hash function does not satisfy weak collision resistance.What is the security requirement on password hashing? Given a password w, its hash is calculated as . This question is about the security requirement on function h. (a) Can we use any function as h for password hashing? For example, can we use the "mod 100" function, which is a common computer science function? (Given any integer value x, "mod 100" function works by "x mod 100," which is a value between [0, 99]; for example, if x = 105, x mod 100 = 5; x = 1000000, x mod 100 = 0;) (b) If not, what is the security requirement on h?The parity function is a very simple hash function producing a one-bit digest, which is 0 if the number of bits in the message is even and 1 if it is odd. Consider a communication system that uses 7 bits out of every byte to transmit data, and reserves the 8th bit (the one on the right) to transmit the parity of the other seven bits, for purposes of error checking. Below is the binary representation of some bytes that were transmitted using this system. For each one, tell whether there is a reason to suspect an error in transmission, giving the reason for your answer. 10110011 11101111 10101100 00110011
- In a special case of a permutation cipher, we take a message, M, and write its letters in an s× t table, in a row-major fashion, and then let the ciphertext be a column-major listing of the entries in the table. For example, to encrypt the message ATTACKATDAWN, using a 3 × 4 table, we would write the message as ATTA CKAT DAWN and then write down the ciphertext as ACDTKATAWATN. The secret key in this cryptosystem is the pair (s, t). How is decryption done in this cryptosystem? Also, how hard would it be to attack this cryptosystem using a ciphertext-only attack?This question relates to hash functions for block ciphers Block size = 4 bits Hash size = 4 bits Encryption function: Divide the key into two halves: LK and RK; Divide the plaintext into two halves: LT and RT; Then ciphertext= LC||RC where LC=LK XOR RT; and RC = RK XOR LT; where LC, RC, LT, and RT are each 2 bits; Plaintext and ciphertext are each 4 bits. g(H) = a 4-bit string that is equal to the complement of bits in H; For example, if H=A (Hexa) = 1010 (binary); then g(H)= 0101 H0 = Initial hash = C (in Hexa) Given message M: D9 (in Hexa); a. Determine the hash (in hexadecimal) of the message M using Martyas-Meyer-Oseas hash function b. Determine the hash (in hexadecimal) of the message M using Davis-Meyer hash function c. Determine the hash (in hexadecimal) of the message M using Migayuchi-Preneel hash functionSuppose the economies of the world use a set of currencies C1, . . . , Cn; think of these as dollars, pounds, Bitcoin, etc. Your bank allows you to trade each currency Ci for any other currency Cj, and finds some way to charge you for this service. Suppose that for each ordered pair of currencies (Ci, Cj ), the bank charges a flat fee of fij > 0 dollars to exchange Ci for Cj (regardless of the quantity of currency being exchanged). Describe an algorithm which, given a starting currency Cs, a target currency Ct, and a list of fees fij for all i, j ∈ {1, . . . , n}, computes the cheapest way (that is, incurring the least in fees) to exchange all of our currency in Cs into currency Ct. Also, justify the its runtime. [A description or pseudocode (either is OK) of the algorithm, as well as a brief justification of its runtime.]











