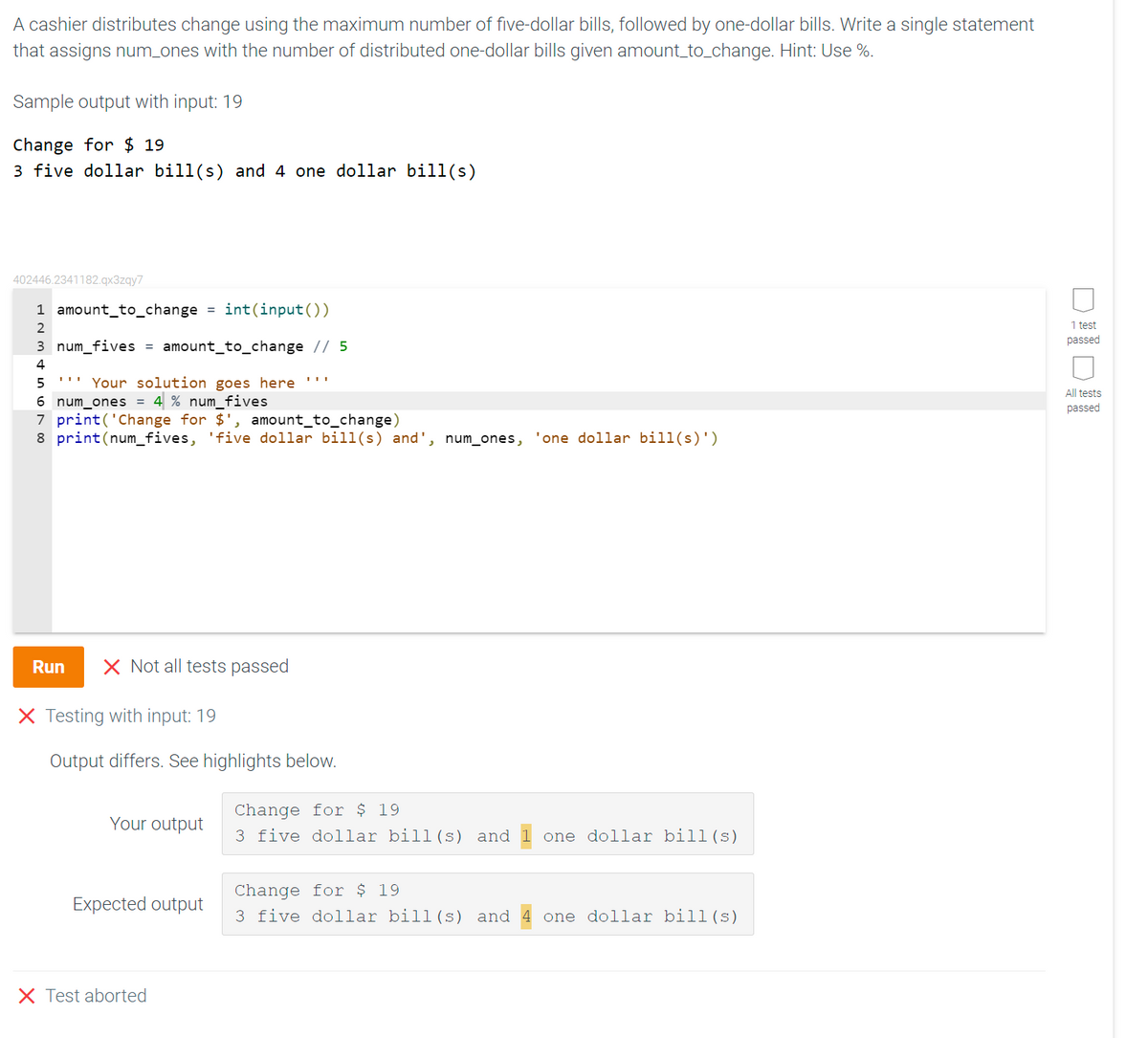
A cashier distributes change using the maximum number of five-dollar bills, followed by one-dollar bills. Write a single statement that assigns num_ones with the number of distributed one-dollar bills given amount_to_change. Hint: Use %. Sample output with input: 19 Change for $ 19 3 five dollar bill(s) and 4 one dollar bill(s)
Q: Which VLAN is intended to provide administrative access to network devices?
A: answer is
Q: As a software developer, you'll have to help your customers understand how to collect requirements.…
A: As a Software Engineer, you will be in charge of recommending the best way to get our clients'…
Q: How do you show the suffix trie T for eight suffixes of string "maximize" and compact representation…
A: We need to draw the suffix trie T for given string.
Q: What is returned when invoking the method call myFun (4)? int myFun (int n) if (n > 0) 2)); return…
A: Your answer is given below with an explanation.
Q: Analyzing a system is a challenging task. What are the challenges? When examining a system to see…
A: 1. Analyzing a system is a challenging task. What are the challenges? Challenges: When working on…
Q: 18. Given a piece of code below, which of the following will most likely cause an error? public…
A: extends keyword is used to extend the functionality of the parent class to the subclass. The…
Q: Draw W7 . Be able to draw 10 of its subgraphs.
A: We need to draw W7 and it's 10 subgraphs.
Q: There are a lot of questions about routing, therefore here are some answers: Two popular methods of…
A: Define: Moving from one page to another is known as routing. It may be used to create a Single Page…
Q: What are embedded systems, embedded controllers, and instruction set processors? Define these words…
A: An embedded system is a computer system: that serves a predetermined purpose inside a broader…
Q: As a software engineer, you'll be expected to recommend the best method for gathering customer…
A: Requirement Engineering is the process of defining, documenting and maintaining the requirements. It…
Q: What does MVC do in the way web applications are put together? In what ways is an MVC architecture…
A: Definition: Model-View-Controller (MVC) is an architectural pattern that divides an application into…
Q: buffer pool of size 4 pages and will access this access pattern in the given order: RDBMSTHEORY. At…
A: Introduction: Below the CLOCK algorithm as the buffer replacement policy.
Q: Given an integer n and an array a of length n, your task is to apply the following mutation to a:…
A: We need to write a program to mutate an array as per the given condition. * Language used is C
Q: Scrum is being used in the development of an agile methodology for the ACME Company, and you are a…
A: Model of flexibility: Agile approach is a development and testing strategy that encourages…
Q: Which of the following statements is TRUE about trees? O Performing a post-order traversal on an…
A: Ans: The following statements that is TRUE about trees is:
Q: Top-down data security is preferred over bottom-up security for what reasons?
A: answer is
Q: 3. Write a C program containing a recursive function that will get the whole number quotient result…
A: Given: To write a C program to find quotient of two numbers.
Q: Note: Use Ruby language to write your code. Task Assigned: Write a program to read input two strings…
A: Code: puts "Enter sp_top= "sp_top = gets.chomp puts "Enter sp_bottom= "sp_bottom = gets.chomp…
Q: Given array A = [145, 251, 283, 960, 350, 231, 520, 152, 412, 280]. Do the following tasks. %3D a.…
A: Answer is given below-
Q: What are the advantages of doing regular backups in systems administration?
A: The advantages of regular backups in system administration are: Security Ease of management…
Q: The Cloud Computing Movement has had an effect on collaboration, however the degree to which this…
A: Cloud migration is the process of shifting digital business operations to the cloud. As with any…
Q: What steps may be taken to avoid man-in-the-middle (MITM) attacks? Answer the question step-by-step.
A: A man-in-the-middle attack is a type of eavesdropping attack: Every workplace application, including…
Q: What are some examples of Link State Protocols?
A: Given: People who use link state protocols look for the best way to get somewhere by taking into…
Q: een the computer network concepts of dependability and availability. It has become outdated because…
A: In a network, reliability implies that the PC performs as planned. Reliability is an equivalent word…
Q: library (ISLR) library (boot) attach (Auto) boot.fn=function (mydata, idx) {…
A: Which of the following statement is false about the code above. Answer is None of the above Because…
Q: The benefits and drawbacks of connectionless protocols are contrasted with those of connection-based…
A: Solution: When comparing connectionless protocols to connection-based systems, the advantages and…
Q: a. Given the above adjacency matrix: i. Draw the equivalent adjacency list. [2] ii. Draw the…
A: Adjacency Matrix: Adjacency Matrix is a 2D array of size V x V where V is the number of vertices in…
Q: Consider the int Array below and determine the values of A and B so that Array[0] has an integer in…
A: We have no inbuilt function to produce the number in range usig the rand function . Hence we have to…
Q: a). Given that a directed graph has 17 edges, and 5 vertices, and the following indegrees of the…
A: Introduction: Here we are required to explain what will be the degree of a vertex e for the given…
Q: Explanation of the acronym CRC ( Class Responsibility Collaborator). Which brings us to our next…
A: You can see that a Class Responsibility Collaborator (CRC) model is made up of a collection of…
Q: What database backup tools are available?
A: A backup is a copy of data from your database that can be used to reconstruct that data.
Q: How did the term "spool" come to refer to the output from a printer?
A: Answer:
Q: Meetings through the internet MS Video Calls on the Internet Teams from virtual classrooms recorded…
A: Introduction Workplace conversations, collaboration, teamwork, video chats, and document sharing are…
Q: What is congestion management in the Computer Neetwork, and why is it important? End-to-end…
A: Congestion Control: To comprehend congestion management, you must first comprehend what congestion…
Q: When an organisation is trying to keep its data safe, what is the goal? What are the benefits of…
A: Answer:
Q: Asynchronous Transfer Mode (ATM) traffic management features that are performed to prevent…
A: The ATM Network concept is a compromise: between the audio, video, and computer data transfer needs…
Q: What is routing, and how does it operate in real-world situations? We'll examine and contrast two…
A: Routing: Network routing is the process of choosing a path between two or more networks. All…
Q: Create, compile, and run a recursive program. Choose one of the labs listed below and program it.…
A: Answer :
Q: Instruction: Create a java program that generates elements (randomly from 10 – 75) of a…
A: Logic :- (I) To generate random number in range:- arr[i][j]= Min + (int)(Math.random() * ((Max -…
Q: 6.- Write a C function to count the number of events (rising edges) in the TOCKI pin of the…
A: Answer : #include<reg51.h> sbit T1 = P3^5; void main(void) { T1 = 1; TMOD = 0x60; TH1 = 0;…
Q: What are some of the qualities of a central processing unit? It's important to know what an…
A: CPU: Programming is carried out on a computer's Central Processing Unit (CPU, central processor, or…
Q: What is this page's purpose? An full book may be printed in under a minute using a high-speed,…
A: Purpose: The objective is to create pages that are visually appealing and capture the reader's…
Q: We discussed doubling the timeout period after a timeout event. By using this strategy, congestion…
A: TCP : The Idle Timeout parameter in the TCP profile specifies how long a connection may be idle…
Q: Your firm has decided to shut a number of locations in order to save money and lessen the…
A: Encryption: Several offices at your firm are being closed, and employees are being encouraged to…
Q: When a change is made to the database schema, why is it beneficial for the DBMS to automatically…
A: Start: System tables are specific tables that the system employs to control data and the system in…
Q: Let, a1 = 3 and for n > 2, an 2an-1+5, express an in terms of n.
A: We are going to solve given recurrence relation and express an in terms of n. Using substitution…
Q: When a change is made to the database schema, why is it beneficial for the DBMS to automatically…
A: Database schema: System tables are specific tables that the system employs to regulate data and the…
Q: using c++ .. - Implement a function string convertToBinary(int) that uses a stack to convert a…
A: The c++ code is given below with screenshots Stack is used here..
Q: What exactly is routing, and how does it operate? This article compares and contrasts two commonly…
A: Network routing is the process of selecting a path across one or more networks. The principles of…
Q: Computer science Short answer What do you understand by the fuzzy logic
A: answer is
I can not figure out why this code will not run. Thank you.
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

- For example, the input: S 1 100.00C 2 200.00S 5 500.00C 4 20.00q1 D 50.002 W 250.002 W 50.005 W 450.005 W 200.002 D 50.002 D 100.004 W 10.00-1must generate the following output: Error: withdrawal from account No.2 not allowedError: withdrawal from account No.5 not allowedError: deposit into account No.2 not allowedSavings Account Number: 1 Balance = 150.0Credit Account Number: 2 Balance = 0.0 limit = 200.0Savings Account Number: 5 Balance = 50.0v Credit Account Number: 4 Balance = 10.0 limit = 20.0v import java.util.ArrayList;import java.util.Scanner; public class LabProgram { public static int find(ArrayList<Account> accounts, int acctNo) { for (int i = 0; i < accounts.size(); i++) if (accounts.get(i).getAcctNo() == acctNo) return (i); return (-1); } public static void display(ArrayList<Account> accounts) { /* Displays account information for eaach account in accounts */ /* Type your code here */…Write a program that takes a **string** as input and outputs “Binary Number” if the string contains only 0s or 1s. Otherwise, outputs “Not a Binary Number”. ===================================================================== **Sample Input 1:**\01101101101 **Sample Output 1:**\Binary Number ===================================================================== **Sample Input 2:**\12344ab0 **Sample Output 2:**\Not a Binary Number ===================================================================== **Sample Input 3:**\10127490111 **Sample Output 3:**\Not a Binary Number ===================================================================== **Sample Input 4:**\Binary Number **Sample Output 4:**\Not a Binary Number #todo#assign the result string to variable "out_str"def task3(in_str): # YOUR CODE HERE return out_strAsk the user for an account balance. Show, in descending order, all the accounts that have a balance greater than what the user input. Each entry is int, string, long, double, boolean (name length, name, credit card number, balance, cashback). required output Enter a balance\n9000ENTERAccounts with a balance of at least $9000.00 (sorted by balance)\n Name Account Number Balance Cash Back\n Brand Hallam 3573877643495486 9985.21 No\n Paco Verty 4508271490627227 9890.51 No\n Stanislaw Dhenin 4405942746261912 9869.27 No\nEachelle Balderstone 30526110612015 9866.30 No\n Reube Worsnop 3551244602153760 9409.97 Yes\n Tiphanie Oland 5100172198301454 9315.15 No\n Jordan Rylstone 201715141501700 9135.90 Yes\n7 results\n ---- Enter a balance\n8000ENTERAccounts with a balance of at least $8000.00 (sorted by balance)\n Name…
- Sites like Zillow get input about house prices from a database and provide nice summaries for readers. Write a program with two inputs, current price and last month's price (both integers). Then, output a summary listing the price, the change since last month, and the estimated monthly mortgage computed as (currentPrice * 0.051) / 12 (Note: Output directly. Do not store in a variable.). Ex: If the input is: 200000 210000 the output is: This house is $200000. The change is $-10000 since last month. The estimated monthly mortgage is $850.0. Note: Getting the precise spacing, punctuation, and newlines exactly right is a key point of this assignment. Such precision is an important part of programming.Write a program that asks the user to enter 10 numbers, that range from 0-100. Make sure that you do not accept any numbers less than 0, if a user enters a number that is less than 0 then ask him again. Once the user enters all 10 numbers, find and print out the median. How to calculate the Median The median is the middle score of a distribution. To calculate the median Arrange your numbers in numerical order. Count how many numbers you have. If you have an odd number, divide by 2 and round up to get the position of the median number. If you have an even number, divide by 2. Go to the number in that position and average it with the number in the next higher position to get the median. Consider this set of numbers: 5, 7, 9, 9, 11. Since you have an odd number of scores, the median would be 9. You have five numbers, so you divide 5 by 2 to get 2.5, and round up to 3 (to round numbers in C#, use Math.Round()). The number in the third position is the median. In this case, the mean…(JAVA) Write a program that allows the user to enter the last names of five candidates in a local election and the number of votes received by each candidate. The program should then output each candidate’s name, the number of votes received, and the percentage of the total votes received by the candidate. Your program should also output the winner of the election. A sample output is: Candidate Votes Received % of Total Votes Johnson 5000 25.91 Miller 4000 20.73 Duffy 6000 31.09 Robinson 2500 12.95 Ashtony 1800 9.33 Total 19300 The Winner of the Election is Duffy
- Write a program sequence.cc that prompts the user to enter the value of x, the pro- gram outputs the integer k such that ak = 1, the numbers a0, a1, a2, ..., ak, the largest number of the sequence a0, a1, a2, ..., ak, and the position of the largest number in the sequence.Write a program that calculates and prints the total bill at a restaurant. Prompt the user for the cost of the meal and then ask if a tip will be added. If it is, prompt for the tip percent as an integer. Of course, the tip percent should not be requested if no tip will be added. Finish by printing the meal cost, tip amount, and total bill. Sample OutputEnter total cost of the meal 80Are you adding a tip? y/n yEnter the tip percent as an integer 25Here is your bill.Meal cost $80.00Tip $20.00Total cost $100.00Using Paython Write a program that asks a student for his grade (out of 100) in 3 exams and then print out his final grade (out of 100), given that the weight of the first exam is 30%, the second 30%, and the third 40%.Example Input:Exam1: 70Exam2: 80Exam3: 90Example Output:Total Grade = 81Explanation: 0.3 * 70 + 0.3 * 80 + 0.4 * 90 = 81
- You are to write a simple program that asks the user for input, processes theinput, and then outputs a result back to theuser. Read in the following Name of customer Car Type (Compact, Midsize, Sedan) Number of week days Number of weekend days(Weekends are Saturday, Sunday) Amount customer paid for Rental Use the standard national average for car rental to calculate the national cost of rental based on car selection and days used by customer Compare your result with what the customer paid and determine whether the rental was. a.Expensive(the rental is expensive if it costs $5 morethan national average)b.Bargain(the rental is a bargain if it costs $5 less thannational average)c.Average(the rental is average if it is atthe $5 range plus or minus from thenational average)(This is how the output should come and please answer it as soon as possible) Output: 1.==================================== Hogwart's Dragons is a Quidditch team. Number of players in Hogwart's Dragons is 2 The Players are: Seeker: Player name: Harry Potter, House: Gryffindor Chaser: Player name: Katie Bell, House: Gryffindor 2.==================================== We do not have enough players to form a squad. 3.==================================== 4.==================================== Hogwart's Dragons is a Quidditch team. Number of players in Hogwart's Dragons is 4 The Players are: Seeker: Player name: Harry Potter, House: Gryffindor Chaser: Player name: Katie Bell, House: Gryffindor Beater: Player name: Vincent Crabbe, House: Slytherin Keeper: Player name: Miles Bletchley, House: Slytherin 5.==================================== We do not have enough players to form a squad. 6.==================================== We have enough players to form a squad. But we cannot form a perfect…An automobile insurance company provides accident insurance if the vebicle’s model year is greater ot equal to 2000 and the number of accidens is less or equal to 6, Write & program that prompts the user to cnter his/her vehicle’s model year and the number of accidents. The program then checks whether or not the client s elgible for an insurance and prints the messages as shown in the sample run. Sample Run 1 | Enter your vehicle’s model yea;x: 010 R A ‘( Enter the number of accidents: 3 I You are eligible for an insurance for your vehicle’s model 2010. Sample Run 2: Enter your vehicle's model year: 2005 Enter the number of accidents: 7 You are not eligible for an insurance for your vehicle's model 2005.

