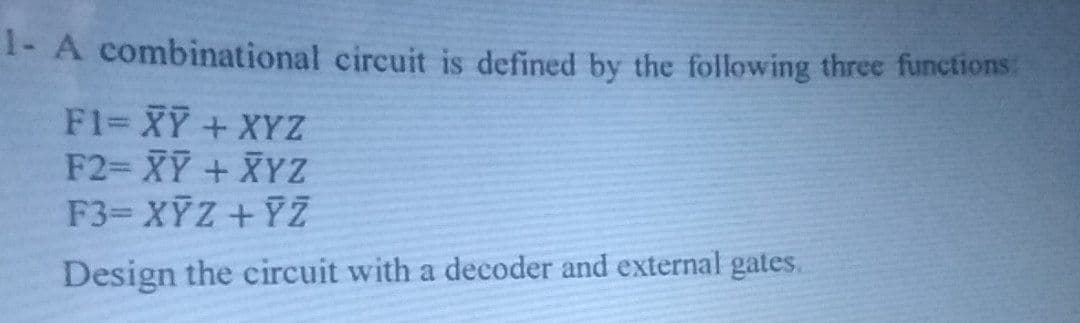
A combinational circuit is defined by the following three functions F1= XY + XYZ F2= XY + XYZ F3= XYZ +YZ Design the circuit with a decoder and external gates.
Q: Explain the function of the wait() process in relation to process termination in the full explanatio...
A: The wait() function is a very important function in case of multithreading.
Q: other error-detection techniques are available? How do they compare to parity
A: Simple Parity check Two-dimensional Parity check Checksum Cyclic redundancy check These are the avai...
Q: Computer science What issues do you believe may occur in extreme programming teams when many manage...
A: Introduction: Extreme Programming (XP) is an agile software development approach that attempts to de...
Q: C language 3. Develop a complete program that consists of three function name as triangle, rectangle...
A: As per the requirement program is completed. Algorithm: Step 1: Write the main() method Step 2: By u...
Q: hat is the effect of data mining on individual privacy and secu
A: Lets see the solution.
Q: Write a C++ program to take an array of ints, print true if the sequence of numbers 1, 2, 3 appears ...
A: C++ Program: #include <iostream>using namespace std; /* sequence() function of boolean type fo...
Q: Describe and provide examples of the three main file management methods.
A: Introduction: The practise of administering a system that correctly handles digital data is known as...
Q: How many memory accesses does the CPU need to perform during the instruction cycle while executing t...
A: Introduction: A programme is a set of instructions stored in the memory unit of a computer.
Q: What is software re-engineering?
A: To define software reengineering.
Q: next time you connect to a Wi-Fi, and use WhatsApp to make a VoIP call, while roaming out of country...
A: Lets see the solution.
Q: Which of the following strategy profiles are subgame perfect Nash equilibria in this game? O (AH,CF,...
A: A subgame perfect equilibrium (also known as a subgame perfect Nash equilibrium) is a refinement of ...
Q: Explain how requirements might act as a restriction on the system's development process using an exa...
A: Requirement Engineering is the process of defining, documenting and maintaining the requirements. It...
Q: What is one intriguing use of data or text mining that you can research and describe?
A: Text mining: Text mining, otherwise called text information mining, is the method of separating gr...
Q: What exactly is technical documentation? What are the four main distinctions between technical docum...
A: Documentation Techniques The phrase "technical documentation" refers to a variety of publications th...
Q: I am a student in a deep learning class. Q1. We want to use a 1-layer NN for MNIST classificatio...
A: from numpy import loadtxt from keras.models import Sequential from keras.layers import Dense # load ...
Q: Computer Organization Single Cycle Data Path Assembly in RISC-V Draw a picture showing the ...
A: Draw a picture showing the data path add t2, t1, t0 Explain what is happening in each functional un...
Q: Windows 2016 system requirements
A: Introduction: CPU (Central Processing Unit) Requirements Minimum: • 64-bit 1.4GHz processor • Should...
Q: What function do design patterns play in software engineering, and how may they be effectively appli...
A: A design pattern is a generic, reusable solution to a problem that often arises in software developm...
Q: In the story "To build a fire", What is the man's main fear on this trip? a) Getting wet b) The dog...
A: In the story "To build a fire", What is the man's main fear on this trip?
Q: describe how to setup a switch to monitor traffic passing across its ports.
A: Introduction: Using specialized gear and software, traffic monitoring, also known as network monitor...
Q: Look up "Announcing the Advanced Encryption Standard (AES)" on the Internet. Read this FIPS 197- com...
A: INTRODUCTION: Advanced Encryption Standard: This is a cipher technique that the US government has c...
Q: Computer science In terms of detection approach, list and compare two types of intrusion detection ...
A: Introduction: IDPs analyze network traffic for indicators of an attack and alert administrators. IDP...
Q: computer science - Contrast the transactional and analytical data management methodologies.
A: Introduction: Compare and contrast transactional and analytical data management approaches.
Q: Simplify the following Boolean expressions to a minimum number of literals: (a + b+ c')(a'b' + c) (a...
A:
Q: What is the role of the operating system in processor management?
A: Introduction: Process management in operating systems comprises tasks associated with processing suc...
Q: Explain and describe the fundamental goals of artificial intelligence (AI) systems.
A: Given To describe the primary objective of artificial intelligence (AI) systems.
Q: Rewrite the following loops, using the enhanced for loop construct. Here, values is an array of floa...
A: Enhanced for loop is used to iterate through elements of array. It’s also called for-each loop. This...
Q: As part of the discussion forum for this unit, you will be solving a programming problem from the bo...
A: Modulus operator(%) is used to remainder of division.
Q: Describe briefly why the usual Method (Non-Formal) of software development will not be effective for...
A: Introduction: Non-formal software development is a way of software development that relies on the vi...
Q: 4: Write C++ program to find the sum of all integer between 100 and 200 which are divisible by 9.
A: The answer of this question is as follows:
Q: What does "virtualization" entail exactly?
A: This question explains exactly does "virtualization" imply :
Q: What do you mean by Rate Limiting?
A: Rate Limiting: Rate limiting is the concepts of computer networking which is used to direct rate of ...
Q: Create the state transition table for the NFA, Create the state transition table for the DFA, Draw t...
A: As per guidelines I can answer only three sub-parts. I hope you will understand. Thank You.
Q: Scenario Fill in the blanks in a program. After this, test your program (just run it). Your version ...
A: As per the requirement program is completed. Algorithm: Step 1: Write the main() method Step 2: Defi...
Q: What are the main components of a data governance programme, and what is the relationship between da...
A: Introduction: Data stewardship refers to the practises required to guarantee that data is correct, u...
Q: 9. IF BL=57H, C;=1 ,show the content of BL after the ROL BL,1 instruction executes. 10. IF BL=57H, C...
A:
Q: lass C” network is div
A: Subnet Mask and IP Address On an IP network, a 32-bit IP address uniquely identifies a single device...
Q: making use of Mafiaboy's web-based research techniques When and how did he comprmise his sites was t...
A: Introduction: Michael Calce (born 1984, alias MafiaBoy) is a security expert and former computer hac...
Q: Which of the following will help evenly distribute traffic to each device in a cluster so every devi...
A: Load balancing is a process where network traffic is distributed across two or more instances of a w...
Q: 1. What's "Bayes Decision Rule"? Explain with presenting formula(s) for a hypothetical two-class exa...
A: Bayes Decision Rule
Q: What are the many types of wireless security methods?
A: Various types of wireless security protocols have been developed for the safety of home wireless net...
Q: ii) Input a string single from the user and form a string triple in which all characters of the stri...
A: Required: ii) Input a string single from the user and form a string triple in which all characters o...
Q: When it comes to Ethernet LANs, what is the maximum transmission rate?
A: A LAN is a network of computers and other electronic devices that covers a small area such as a room...
Q: Explain Gentoo and its features in the context of server operating systems.
A: Answer: Gentoo is a meta-distribution based on FreeBSD. Its popularity stems from the fact that it m...
Q: n a few words, explain passing by reference.
A: Introduction: Passing the reference of an argument in the calling function to the equivalent formal ...
Q: Find the compliment 1 (A+B')C = ?
A:
Q: Explain why in the case above, when the parent of a node k is updated to a node in a higher-rank gro...
A: Consider a situation with a number of persons and following tasks to be performed on them. Add a n...
Q: Differentiate between fully associative caches and direct-mapped caches.
A: Associative Mapping :Here the mapping of the main memory block can be done with any of the cache blo...
Q: Discuss the process of contradiction proof. Give an example to illustrate your point.
A:
Q: House +numberRoom:int +tyee:String. +Displaxlnto(); Bungalow +location:String +gwnerName:Striog. Ris...
A: Here is The Solution. public class House{ public int numberRoom; public String type; ...
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

- 3. A COMBINATIONAL CIRCUIT IS DEFINED BY THE FOLLOWING THREE BOOLEAN FUNCTIONS. DESIGN THE CIRCUIT WITH A DECODER AND EXTERNAL GATES F1= X'Y'Z' + XZ F2= XY'Z' + X'Y F3= X'Y'Z + XYA combinational circuit is defined by the following three Boolean functions. Design the circuit with a decoder and external gates. F1 = x' y' z' + xzF2 = x y' z' + x'yF3 = x' y' z + xy1. DESIGN A COMBINATIONAL CIRCUIT THAT GENERATES THE 9'S COMPLEMENT OF A BCD DIGIT.2 DESING A COMBINATIONAL CIRCUIT THAT COMPARES TWO 4-BIT NUMBERS B AND C TO CHECK IF THEY ARE EQUAL. THE CIRCUIT HAS ONE OUTPUT, Z, SO THAT Z = 1 IF B = C AND Z = 0 IF B IS NOT EQUAL TO B.3. A COMBINATIONAL CIRCUIT IS DEFINED BY THE FOLLOWING THREE BOOLEAN FUNCTIONS. DESIGN THE CIRCUIT WITH A DECODER AND EXTERNAL GATES F1= X'Y'Z' + XZ F2= XY'Z' + X'Y F3= X'Y'Z + XY *HINT: OBTAIN THE KMAP AND TRUTH TABLE
- Q1 Using a multiplexer design a combinational circuit design defined by the following boolean expression: F= y'z'+x'y+yzA combinational logic circuit has inputs A, B, C, D and E. The output Y is given by: fΠ M(15,31) where A is the Most Significant Bit. Give Y in terms of inputs A, B, C, D and E in a Product of Sum format.Using a decoder and external gates, design the combinational circuit defined by the following three Boolean functions:1. (a) F 1 = x ′ y z ′ + x z F 2 = x y ′ z ′ + x ′ y F 3 = x ′ y ′ z ′ + x y2. (b) F 1 = ( y ′ + x ) z F 2 = y ′ z ′ + x ′ y + y z ′ F 3 = ( x + y ) z
- A 1bit 4 to 1 multiplexer, the 4 inputs of the multiplexer will be the output of another combinational circuit with A and B as an input:00 = 1bit Adder01 = 1bit Subtractor10 = 1bit Comparator (equals)11 = XOR • truth table• Boolean Expression• Logic Circuit Here is the truth table guide:Draw the logic circuit of the full adder circuit block. the circuit that will perform the operation given below. Implement using a minimum number of full adder circuit blocks and a minimum number of logic gates. Here a1a0, b1b0 and c1c0 are two-bit binary numbers.A majority circuit is a combinational circuit whose output is equal to 1 if the input variables have more 1’s than 0’s. The output is 0 otherwise.1. (a) Design a three-input majority circuit by finding the circuit’s truth table, Boolean equation, and a logic diagram.2. (b) Write and verify a HDL gate-level model of the circuit.
- Computer Science 1. Write VHDL modules for the following gates and simulate them. a) Inverter (tplh=tphl=2ns) b) NAND (tplh=tphl=2ns) c) NOR (tplh=tphl=3ns) d) XOR (tplh=tphl=5ns)Design circuit that has an input w and an output z. The circuit is a sequence detector that produces z = 1 when the previous two values of w were 00 or 11; otherwise z = 0. Use W=0101100010101110101011100010 a) For this problem design the circuit using JK flipflops, draw the state diagram, true table, logic circuit.b) Do the same that as part A but this time use D flipflops: draw the state diagram, true table, logic circuit.B) redraw the circuit from (a) using only NAND gates.

