A data structure is only an idea, while an ADT is a way to code the data structure in a program. O True O False
Q: SVM and kNN are very similar in the way that the "models" are a collection of training data points. ...
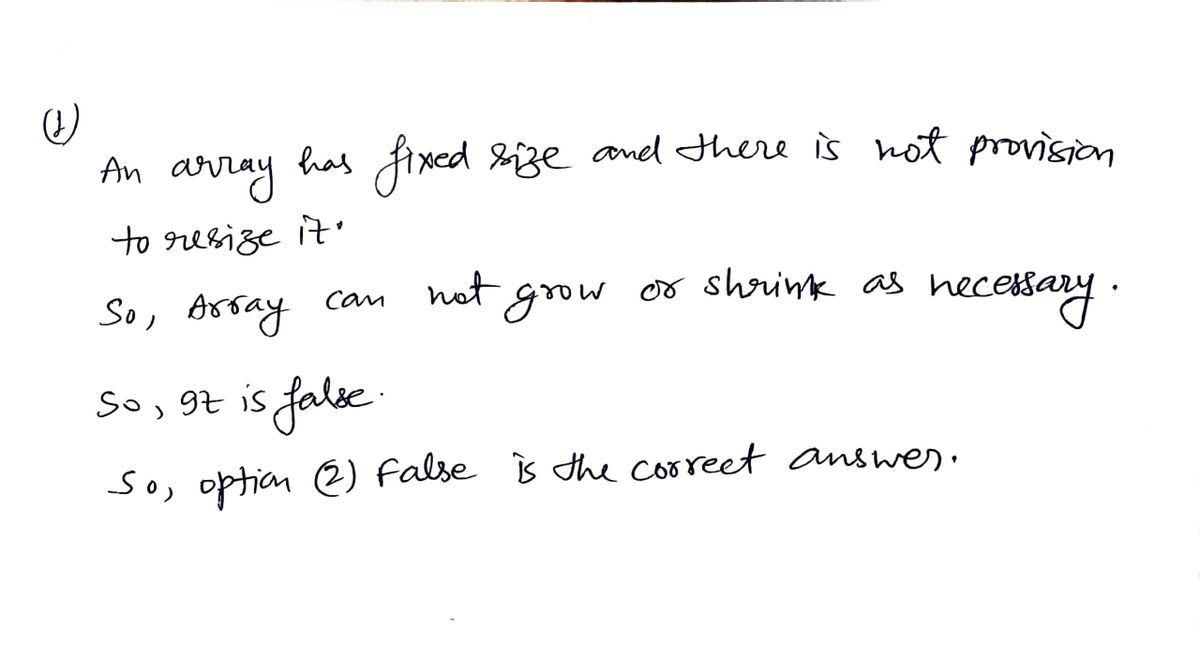
A: Defined the given statement as true or false
Q: Remove all errors from the C++ program given below asap #include using namespace std; int main(){ in...
A: Given: A C++ program is given in which two variables are declared and then a for loop is given in wh...
Q: Chinese Wall model: consider following COIs and CDs: Bank COI class: Chase Bank, US Bank, Citi Bank ...
A: Chinese Wall model: consider following COIs and CDs: Bank COI class: Chase Bank, US Bank, Citi Bank ...
Q: Suppose we use six bits to represent a two's complement binary number. (a) What is the largest numbe...
A: Two's complement is the most popular way of representing signed binary numbers in computers. For a g...
Q: What is output? #include #include #include using namespace std; int main () { setnumber; i...
A: Ans: The output of code: #include <iostream>#include <set>#include <string>using n...
Q: 1. What is Failover-Clustering and why do you think it is so widely used?
A: To define Failover-Clustering.
Q: In C, How Is Memory Allocated/Deallocated? What about C++?
A: Introduction: Dynamic memory is allocated from the heap in C using standard library methods. The two...
Q: work security conce
A: given - Define some of the most significant network security concerns.
Q: Machine language refers to the language that a computer can comprehend and execute.
A: Introduction: Machine language refers to the language that a computer can comprehend and execute sin...
Q: Consider the challenges associated with both the creation and the use of an online mapping app: All...
A: It is divided into three sections, and is underpinned by the five fundamental principles of Integrit...
Q: ,D),and(5,E),inthisorder, into an initially empty binary search tree, what will it look like?
A: given - If we insert the entries(1,A),(2,B),(3,C),(4,D),and(5,E),in this order, into an initially e...
Q: Question 4 While connecting the inputs and the outputs of a circuit in a stick diagram, which type o...
A: A stick diagram is a diagram which is used to plan the layout of a transistor cell. Sticks or lines ...
Q: Explain What Is Difference Between Baseband And Broadband Transmission?
A: Given :- Explain What Is Difference Between Baseband And Broadband Transmission?
Q: Translate trhe following C code to MIPS. Assume that the variables f, g, h, i, and j are assigned to...
A: Step 1 The answer is given in the below step
Q: 4. Write a Python program to remove all the occurrences of the strings other than "Python" from the ...
A: Write a Python program to remove all the occurrences of the strings other than "Python" from the lis...
Q: iven 2 numbers which are the measurement of a distance in feet and inches, for example 3 feet 7 inch...
A: import java.util.Scanner; public class FeetInchesToMeters { public static void main(String[] arg...
Q: ow can i sign up for free I am 13 years old
A: Given how can i sign up for free I am 13 years old
Q: II. Finite automaton is given by canonical equations (under the binary alphabet A = Represent it in ...
A: Given logic can be simplified with boolean logic gates as : y(t) = NOT(q1(t-1)) + x(t) + q2(t-1) ( s...
Q: Explain why the choice of data structure used for the event queue is important in discrete event sim...
A: Event Queue : Exemplary round exhibit execution Pointers to event base class Sizes of the event lin...
Q: .A GSM syatem uses 124 channels and each channel is divided into time slots. What is the maimum numb...
A: The answer is
Q: No stable storage can be achieved. a. State why it can't. b. Describe how database systems handle th...
A: No stable storage can be achieved because: In stable storage data is never lost as it is replicated ...
Q: What is the different between authentication and access control?
A: Difference between authentication and access control.
Q: Alice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a = 6. Let Bob’...
A: Alice and Bob use the EIGamal scheme with a common prime q= 131 and a primitive root a = 6. Let Bob'...
Q: Using a HTML5 Canvas & JavaScript, draw some cartoon on the screen using moveTo, lineTo, fill, strok...
A: The answer is given below:-
Q: In your own words, describe four properties that are not visible at runtime.
A: Intro The attributes that are not observable at run time are: 1. Easiness of testing 2. Modificatio...
Q: DESIGN AND SIMULATE A MULTI-THREADING SCENERIO using pyton please show and explain each step
A: I give the code along with explanation in Python with output and code screenshot
Q: Signed integers are represented by the following 16-bit hexadecimal numerals. Each should be convert...
A: To convert hexadecimal to decimal just sum of all the digits multiplied with power of 16. For exampl...
Q: Why is a token a small message that passes through a communication channel in a computer network?
A: What are TOKENS? A token is a particular frame that is sent from node to node in a ring network. Whe...
Q: Which fibre is utilised to protect the inner core and prevent the cable from straining in fiber-opti...
A: Introduction: Fiber optic cable is a form of network cable that is commonly used to carry data. It i...
Q: Log-based recovery and the shadow-copy scheme have different overheads when data are added to new di...
A: answer is
Q: A small insurance company has an online application system that allows its customers to interactwith...
A: Whereas if the file format is too huge, the Libreoffice software may become unresponsive, especially...
Q: MINI-CASE ON BROADCOM LIMITED (AVGO) HOW COULD A BALANCE SCORECARD BENEFIT BROADCOM? Jointly headqua...
A: The advantages of ratio analysis for Chipsets: Microsoft uses performance management to interpret an...
Q: Suppose the implementation of an instruction set architecture uses three classes of instructions, wh...
A: Intro Suppose the implementation of an instruction set architecture uses three classes of instruct...
Q: What are the issues that can prevent a transaction processing system from scaling up linearly? In ea...
A: This parallel database system aims to boost performance by parallelizing numerous tasks involving da...
Q: What are the four distinct design considerations in a multiprocessor operating system?
A: Introduction: A multiprocessing operating system is one in which the computer's operations are contr...
Q: Write a Java program to find the sum of digits of a user entered number till that number becomes one...
A: Coded using Java.
Q: properties of sets, lists, vectors and strings are and whether they are mutable or immutable.
A: The given question is to discusses the data structures sets, lists, vectors and strings in the conte...
Q: What are the issues that can prevent a transaction processing system from scaling up linearly? In ea...
A: issues that can prevent a transaction processing system from scaling up linearly can be anyone of t...
Q: IEEE is the organization that sets standards for computer components, signaling protocols, and data ...
A: Given: IEEE is the organization that sets standards for computer components, signaling protocols, an...
Q: Pléašė ģivė the machine code (not the assembly) för asking the user for a number and adding 10 to it
A: You can program the LMC using 'machine code'. Machine code is normally binary numbers that represent...
Q: The goal of regularization techniques such as L2-norm or limiting the depth of the tree is to lower ...
A: L2 Regularization technique used to reduce the overfitting of the model for the given training set. ...
Q: Consider the best way to count how many bits are set in a bitmap. Keeping the size of the cache in m...
A: Map of Bits and Bytes Bit It is the smallest piece of information contained inside a computer. Typic...
Q: Watch the video "Microsoft's Agile Transformation Story" by Donovan Brown. https://youtu.be/nno6Dwev...
A:
Q: What exactly is a pipe, and when is it used?
A: Introduction: A pipe is a conceptual link between two processes that allows the standard output of o...
Q: te a query that returns th ayment for those invoices nd 2000$ and sort the res ast to maximum values...
A: Query - Create- create table invoice(invoice_number varchar(30),invoice_date date,payment_total floa...
Q: - Using all the characters in your full name Name: Alsaafani Muaadh a. Using the characters in your ...
A: Here is the detailed explanation of the solution.
Q: Assume a major database vendor makes its database system (for example, Oracle or SQL Server DB2) ava...
A: Cloud service database has three main component A rapid development and deployment tool, applicatio...
Q: in Java eclipse ide Read from console a 2-digit integer number, save it in variable vz. Check this...
A: import java.util.Scanner; public class Main{ public static void main(String[] args) { Scanner s...
Q: How many Matlab seat licenses are required for there to be a ~1% steady state probability
A: The answer is
Q: Explain the differences between volatile, nonvolatile, and stable storage in terms of I/O cost.
A: Given The answer is given below.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- language: HTML design a simple shopping cart with only 3 items (names can be left as placeholders like "Item 1", "Item 2"). There should be a quantity adder as well as a function that enables the user to see the subtotal of all the item prices together (prices can be a random number)Design a program that asks the user for a series of names (in no particular order). After the final person's name has been entered, the program should display the name that is first alphabetically and the name that is last alphabetically. For example, if the user enters the names Kristin, Joel, Adam, Beth, Zeb, and Chris, the program would display Adam and Zeb. Programming Language: PYTHON TOPIC: Repetition StructuresIn C programing complete the prompt in the picture: This is the code we are given to start with: void printTour(const tourType dest);tourType getData(); int main(){ }
- C language 1. What is the value of x and y for the following code: int y = 10; int x = ++y;C++ programming Create the game hangman as a windows form program. Use a pre-made list of words.IN C LANGUAGE CODE:Write a code snippet that can arrange the alphabets of a name entered by user in alternate cases.Note: Ignore white spaces. Input String:Timothy Olyphant Output String :TiMoThY OLyPhAnT Input String: Olga Kurylenko Output string: OlGa KuRyLeNkO

