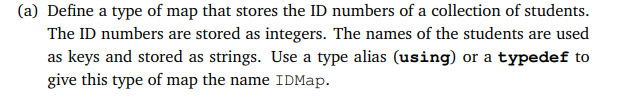
(a) Define a type of map that stores the ID numbers of a collection of students. The ID numbers are stored as integers. The names of the students are used as keys and stored as strings. Use a type alias (using) or a typedef to give this type of map the name IDMap.
Q: b) Consider the following ten usability heuristics: (UH1) Visibility of system status; (UH2) Match…
A: Heuristic evaluation is the inspection methods which denotes usability for the computer software…
Q: Crack The Password? 8 A numeric lock has a 3 digit key HINT 682 One number is correct and well…
A: Below is the answer to above question. I hope this will be helpful for you..
Q: For the purpose of argument, let us imagine that an airline has a database that employs a technique…
A: Introduction: Let us take a database system that uses snapshot isolation in context of airline.…
Q: Q4) Write a program by using MATLAB to enter 8 subjects, give a grade and evaluate each subject, and…
A: Code: marks=zeros(1,8); for i = 1:8 marks(i)= randi([0 100],1,1); if marks(i) >= 91…
Q: A) Write program in C++ to solve the equation y = [ (x^2 + x + 1) when x values increased 0.2 from…
A: 5 A. Code: #include <iostream>using namespace std;int main() { float x=1.8,y=0; do{…
Q: What exactly is meant by the word "Access Point"? What exactly is the process that's going on here?
A: Access Point: A WLAN, or wireless local area network, is created by an access point, often in an…
Q: A database is a collection of information that is organised into a logical structure.
A: Start: A database is an organized collection of structured data that is often saved electronically…
Q: It is important to consider the security risks and advantages of protecting data on the Cloud. When…
A: Introduction: A new paradigm for providing IT services has arisen with the introduction of cloud…
Q: For example, public key cryptography uses asymmetric encryption techniques. What is the procedure…
A: Given: The procedure for encrypting the public key consists of five steps: A pair of keys that…
Q: A MOV instruction asks for two operands: source and destination.
A: Introduction: The "MOV" instruction, which is a data transfer instruction, makes it possible to copy…
Q: Q2\ Build row vector elements from a (8×1) vector, (2×1) vector by using random vectors 1- Display…
A: The Answer start from step-2.
Q: Draw the State diagram of Muscat Sheraton Hotel Reservation System for the below given case study…
A: Introduction: State Diagram: A state diagram is used to represent the condition of the system or…
Q: ne mobile app interface shown in Figure 4, identify an appropriate type of virtual keyboard that uld…
A: Keyboard can be of multiple types but two major types mostly used are:- 1. Qwerty keyboard 2. Numpad…
Q: QS\ Write a program using MATLAB to calculate the square of numbers (4 9 14) ?
A: I give the code in Matlab along with output and code screenshot
Q: How does remote/ online learning work?
A: Distance learning is simply being when the student and teacher are not literally in the traditional…
Q: The distinction between the von Neumann and Harvard computer architectures, if feasible, what is the…
A: Below is a comparison of the von Neumann and Harvard computer architectures: Architecture by VON…
Q: Please provide an example for each of the three most common methods of file management in use.
A: Ordinary files, sometimes known as simple files, can be found in numerous applications, including…
Q: Q1) (A) If y is (2,4,......, 10) Write a program to print the values of x. X = Write the values of x…
A: no programming language is mentioned, I am using Matlab. Code: y=2:2:10…
Q: Each paragraph in a business letter can deal with O One point only OTwo points only O Three points…
A:
Q: Is there a formal definition of what it means to use a cloud backup service? Is there a website that…
A: Cloud backup: Cloud backup, also known as online backup or remote backup, is a method for moving a…
Q: Draw the State diagram of Muscat Sheraton Hotel Reservation System for the below given case study…
A: Here is the State diagram:
Q: Each slide in a PowerPoint can contain * No more than five words per line O No more than three words…
A: PowerPoint incorporates each of the highlights you want to create proficient looking introductions.…
Q: Is Moore's law applicable to supercomputers, grids, and other distributed computing systems?
A: Answer:
Q: Caching may be divided into two categories: "logical" and "physical."
A: Each process maintains its page table, which contains the frame number for the corresponding page…
Q: Task 7 (5 points) Write a Python code that will calculate the value of y if the expression of y is…
A: Here we have given the python code for the given question. You can find the solution in step2.
Q: What are the options for cloud backup? Where can I find a place to store my data for free on the…
A: Cloud backup is the process of creating a backup of specific data and putting it away in a cloud…
Q: Write the correct output (C++) #include using namespace std; int main(){ int num=1;…
A: Let us see the answer below,
Q: Could you kindly explain network topologies to me?
A: Network Topology: The arrangement or pattern by which computer systems and network devices will be…
Q: Mossaic Tiles, Ltd. Gilbert Moss and Angela Pasaic spent several summers during their college years…
A:
Q: Input-output communication in computer systems employs a variety of methods, including:
A: Given: Talk about the three methods of input-output communication that are used by computer systems.…
Q: Dim val! Declare suffix
A: Given :
Q: When it comes to computer architecture, what is the difference between Harvard and von Neumann?
A: The Answer start from step-2.
Q: Research the best techniques for cloud data backup. Make a case for a practise that resonates with…
A: Answer: Online data backup A copy of the data is sent through the internet to a server off-site as…
Q: What is Google Dorks, and how does it work?
A: Google Dorks:- Google dorks had their foundations in 2002 when a man named Johnny Long began…
Q: What are the many ways to get to a file? What are the benefits and drawbacks of each?
A: The benefits of using a file manager are that you can see all of the files on the computer in one…
Q: 3) Write a program to read math A= [3 5 2 11 6 413 9 1 108 3 7 612 1 1. Maximum Number in each Row.…
A: We are asked to write a program to read matrix A(4,4) , but since no programing language is mention…
Q: Flynn's taxonomy should be increased by one level. At this level, what distinguishes computers?
A: INTRODUCTION: Flynn's scientific classification may be a classification of computer structures,…
Q: Hey, so would i have to make three seperate java files labeled in order EncryptorOne EncryptorTwo…
A: Apart of this file you need one extra file for abstract class Encryptor also in a file. Files in…
Q: Consider the concept of "snapshot isolation" when it comes to airline databases. Does a…
A: The transaction only commits if no other transaction [start timestamp, commit timestamp] writes the…
Q: Subsystemizing computer processes and programmes may or may not be a good idea. Deconstructing this…
A: Introduction: Segmentation Segments of a process are separated. Segments are the units into which a…
Q: Static and dynamic routes may be used for a simple network. The question is, why would you choose…
A: Static and dynamic routes: When using static routing, the routing table makes use of the…
Q: The Java language definition demands that all references to array elements be checked to ensure that…
A: Reliability vs Cost Blank 1: Reliability Blank 2: Cost
Q: What is DHCP and what is use of it?
A: Given that we have to write the definition and use of DHCP protocol in networking.
Q: select pre increment op
A: Solution - In the given question, we have to find the pre-increment operator among the given…
Q: Q1 Find the Inverse of Matrix (5x5) and Prove that the theory of (A x A-¹)-eye is true by using…
A: We need to do the following in Matlab : Find inverse of Matrix (5 x 5) Prove that A x A-1 =…
Q: To illustrate, consider a database for a commercial airline that employs "snapshot isolation." If a…
A: Consider a database: Any kind of data may be stored, maintained, and accessed using databases.They…
Q: Assume you're a systems analyst working on a thorough test strategy for a new product. Describe the…
A: System Analyst: The individual who performs the duties of a system analyst is the one who gathers…
Q: User experience and usability testing focused on how clearly the test's goals were laid out.
A: Answer:
Q: Q3\ Find the Inverse of random Matrix (5 x 5)
A: Hope you require a program to calculate the inverse of a random 5×5 matrix. Let me use MATLAB to…
Q: Can I have the output to look like this?
A: The logic for rotation is correct and thus to match exact output the changed program is as follows
C++
Attached is the question
Step by step
Solved in 3 steps with 1 images

- Static vs Dynamic Objects, Exercise In C++: In programming Assignment 1 at the end of the previous module, lines of text were read from an input file one-by-one, and parsed. The result of parsing was an STL vector of C++ strings . That vector would have one or more tokens, with the zeroth one being the name of a shape (like Square), followed by a list of measurements or "dimensions". Given a vector<string> token , where token[0] is the word "SQUARE", write a code block to do the following: create a dynamic Square object, if there is a token[1] , use it to set the object's side attribute, otherwise set that attribute to zero. Remember that it's possible that the side dimension is missing on the input line. In that case the size of the vector will be one and there will be no token[1] . If you even try to look at token[1] in that case, the program will crash! Write just the code block. Assume that all needed libraries are included and that the name of the attribute in struct…Use the terms "equivalent" and "identical" to distinguish between objects and values. Illustrate the difference further using your own examples with Python lists and the “is” operator. Using your own Python list examples, explain how objects, references, and aliasing relate to one another. Finally, create your own example of a function that modifies a list passed in as an argument. Hence, describe what your function does in terms of arguments, parameters, objects, and references. Create your own unique examples for this assignment. Do not copy them from the textbook or any other source.1. What exactly is a set? Is there a connection? A function?
- Can someone help me with this question in C++ and not any other programming language No library functions that leverage hash and maps can be used except to make it all lowercase List sentence(s) with the maximum no. of occurrences of the word "the" in the entire file and also list the corresponding frequency. List sentence(s) with the maximum no. of occurrences of the word "of" in the entire file and also list the corresponding frequency. List sentence(s) with the maximum no. of occurrences of the word "was" in the entire file and also list the corresponding frequency. here is a link too the file its called tiny1 https://drive.google.com/file/d/1ariNN_rW9c3vijK1hvjObcQJafYQ2gzm/view?usp=sharingSOB 22 – (Block 2)Write up what the properties of sets, lists, vectors and strings are and whether they are mutable or immutable. Then consider the class of problems that they are best for and use some code to illustrate your points. E.g., if you have a function that solves a problem using lists, then you can say why you can/can’t use vectors for it or sets etc.C++ Create a generic function add_bookends(ls, e) that adds a copy of element e to the front and back of list ls.
- In C++, declare a map <int,Student> to store serial number and student object. Student class contain id, name and cgpa. Print all map data.Write a program to implement disjoint set data structures and its operations find and union.?In C++, Suggest appropriate containers for the following applications:• (a) Insertion at the back of a container.• (b) Frequent insertions and deletion at both the ends of a container.• (c) Frequent insertions and deletions in the middle of a container.• (d) Frequent random access of elements.
- Assume that the node of a linked list is in the usual info-link form with the info of the type of int. The following data, as described in parts (a) to (d), is to be inserted into an initially linked list: 72, 43, 8, 12. Suppose that head is a pointer of type nodeType. After the linked list is created, head should point to the first node of the list. Declare additional variables as you need them. Write the C++ code to create the linked list. After the linked list is created, write a code to print the list. What is the output of your code? Insert 72 into an empty linked list. Insert 43 before 72. Insert 8 at the end of the list. Insert 12 after 43C++ Consider the following function as a property of a LinkedBag that contains a Doubly Linked List. Assume a Node has pointers prev and next, which can be read and changed with the standard get and set methods. Assume that the doubly linked list is: 1 <--> 2 <--> 3 <--> 4 <--> 5 <-->6 If you are uncertain what the above diagram depicts, it is a doubly linked list such that: The head of this doubly linked list is the node that contains the value 1. The tail of this doubly linked list is the node that contains the value 6. The 3rd node in this list contains the value 3. The contents of this list are the values 1 through 6 in sequential order. The following questions are regarding the linked list after after the test_function is run. A. The head of the list after the test_function is run contains the value: B. The tail of the list after the test_function is run contains the value: C. The 3rd node in the list after the test_function is run…Assume that the node of a linked list is in the usual info-link form with the info of the type int. The following data, as described in parts (a) to (d), is to be insetred into an initially linked list: 72, 43, 8, 12. Suppose that head is a pointer of type nodeType. After the linked list is created, head should point to the first node of the list. Declare additional variables as you need them. Write the C++ code to create the linked list. After the linked list is created, write a code to print the list. What is the output of your code? a. Insert 72 into an empty linked list.b. Insert 43 before 72.c. Insert 8 at the end of the list.d. Insert 12 after 43.

