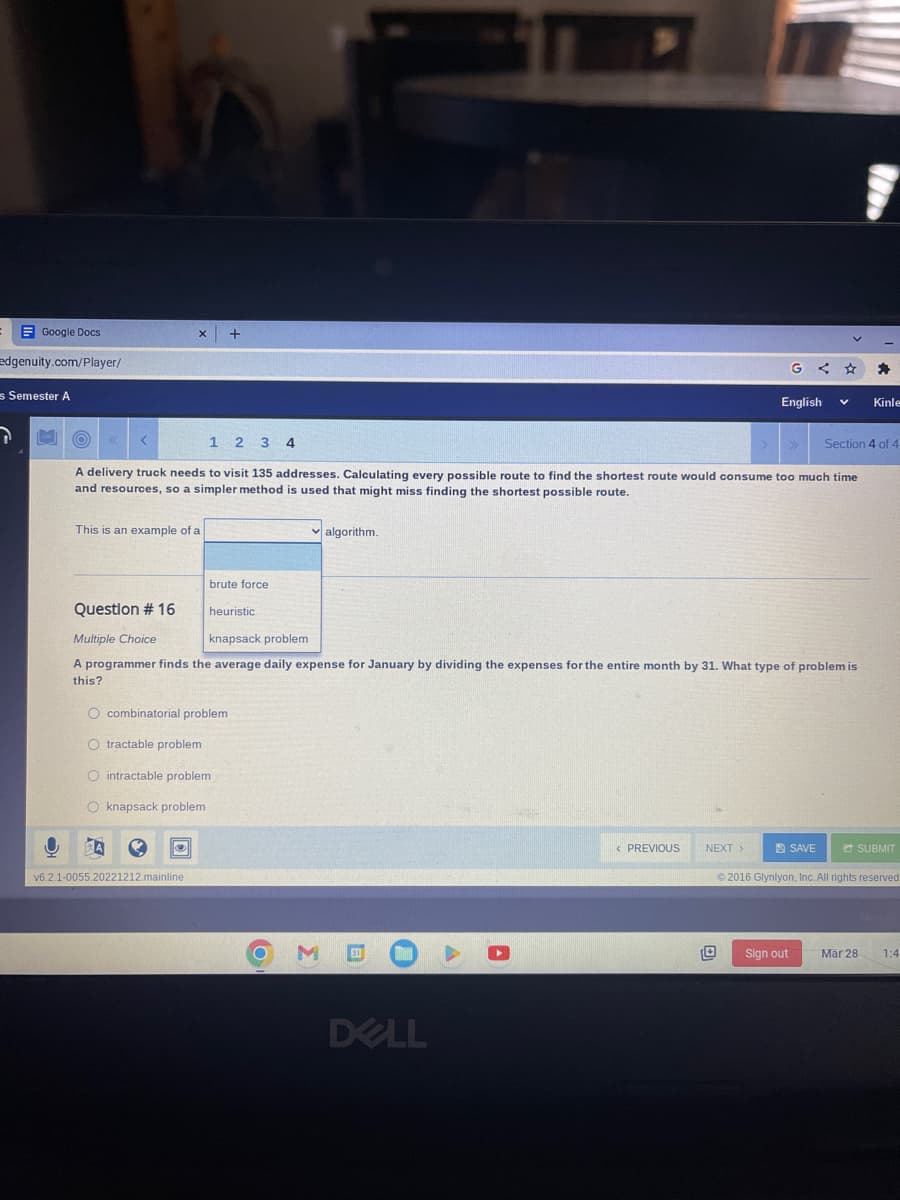
A delivery truck needs to visit 135 addresses. Calculating every possible route to find the shortest route would consume too much time and resources, so a simpler method is used that might miss finding the shortest possible route. This is an example of a brute force ✓algorithm. Question # 16 heuristic Multiple Choice knapsack problem A programmer finds the average daily expense for January by dividing the expenses for the entire month by 31. What type of problem is this? O combinatorial problem O tractable problem O intractable problem O knapsack problem
A delivery truck needs to visit 135 addresses. Calculating every possible route to find the shortest route would consume too much time and resources, so a simpler method is used that might miss finding the shortest possible route. This is an example of a brute force ✓algorithm. Question # 16 heuristic Multiple Choice knapsack problem A programmer finds the average daily expense for January by dividing the expenses for the entire month by 31. What type of problem is this? O combinatorial problem O tractable problem O intractable problem O knapsack problem
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter20: Queuing Theory
Section20.10: Exponential Queues In Series And Open Queuing Networks
Problem 1P
Related questions
Question
Transcribed Image Text:Google Docs
edgenuity.com/Player/
es Semester A
O
This is an example of a
Question # 16
X +
7 HO
1 2 3 4
A delivery truck needs to visit 135 addresses. Calculating every possible route to find the shortest route would consume too much time
and resources, so a simpler method is used that might miss finding the shortest possible route.
A Q
brute force
v6.2.1-0055.20221212.mainline.
heuristic
O combinatorial problem
O tractable problem
O intractable problem
O knapsack problem
✓algorithm.
Multiple Choice
knapsack problem
A programmer finds the average daily expense for January by dividing the expenses for the entire month by 31. What type of problem is
this?
O M
31 FRAN ▶
DELL
A
< PREVIOUS
G
English
NEXT >
V
Sign out
SAVE
Kinle
Section 4 of 4
SUBMIT
©2016 Glynlyon, Inc. All rights reserved
Mar 28 1:4
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole