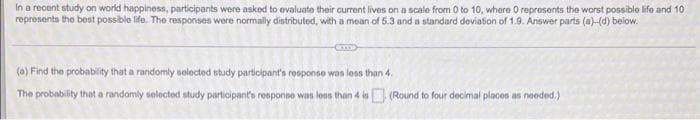
(a) Find the probability that a randomly selected study participant's response was less than 4. The probability that a randomly selected study participant's response was less than 4 is (Round to four decimal places as needed.)
Q: You are to write a boarding system for a Cruise ship in java. The system will print a menu with…
A: The code is given in the below step
Q: A program that turns a high-level language program into a separate machine language program is…
A: A program that turns a high-level language program into a separate machine language program is…
Q: pArray is a pointer to an array of doublewords, therefore declare it as a local variable called…
A: Concurrency: In a multiprogramming environment, it is the process of performing many transactions at…
Q: What is the purpose of target tables? What kind of information do they offer?
A: Intro Purpose and information given by target table Target table is the place where the data is…
Q: List and explain the drawbacks of using big data.
A: Introduction: Big Data & Analytics: It is used to collect and analyse massive amounts of data.It…
Q: Create a firewall configuration.
A: Firewalls: A firewall is a kind of network security device, either hardware- or software-based,…
Q: Write a program that has a counter as a global variable. Spawn 10 threads in the program, and let…
A: When Locking is not used Code: #include <stdio.h>#include <stdlib.h>#include…
Q: Microsoft was working on an RDBS File System named WinFS at one point. What would the advantages of…
A: Microsoft owns WinFS, which stands for window future storage. WinFS was created with the goal of…
Q: dont post existing one answer only u r sure else skip A multiprocessor has a 3.3 GHz clock (0.3…
A: The answer as given below:
Q: Calculate the total time based on the given criteria to access the 31.5 MB if: Seek Time: 1.9 mSec /…
A: We need to calculate total access time for given scenario.
Q: Compare QAM and PSK
A: Ans: Compare QAM and PSK QAM: 1) QAM stands for Quadratic Amplitude Modulation. 2) QAM is having…
Q: Write the HTML, CSS and JS code to design a personalized portfolio website for a sample person X.…
A: this project 3 files- index.html style.css script.js 1 image-profile-1.jpeg in images folder all…
Q: Q1\ Construct DFA equivalent to the following NFA with empty move.
A:
Q: Is encryption a part of biometrics? What is the role of cryptography in biometric technologies?
A: Encryption is transforming an original message into an unreadable form by unauthorized people.…
Q: How much memory is required to store a letter of the alphabet or a tiny number?
A: Introduction Datatype: In the programming language, the data type is used to tell the compiler which…
Q: Problem 1: Find the dual of a logic function F = (X'Y + Z)W'
A: Dual of logic function is obtained by interchanging (and with or) and vice versa. also interchanging…
Q: Computer science 2/ What are the benefits of using a simple batch computer system rather using a…
A: Introduction: What are the benefits of using a simple batch computer system rather using a manual…
Q: Write a Java program that prints rectangles of three different sizes to the screen, with a blank…
A: Answer the above program are as follows:
Q: pose we do a BFS on a connected undirected graph G and T is corresponding depth-first tree. if we…
A: Lets see the solution.
Q: how the parse tree for the sentence "b a a a b" using the following grammar. à a b à b | b…
A: Given Grammar : <S> -> <A> a <B> b <A> -> <A> b I b…
Q: 1- What are the main advantages and disadvantages in ad hoc networks.
A: According to the Bartleby guideline we are suppose to answer only one question at a time. Kindly…
Q: Is splay tree being used by any organizations?Is splay tree being used by any organizations?
A: The solution to the given problem is below.
Q: x86 Assembly Language Programming What will be the final value in EDX after this code e
A: The answer is
Q: One of the most common types of cybercrime is identity theft. Explain how cybercriminals can steal…
A: Introduction: As the digital age progresses, cybercrime has become one of the most widespread…
Q: Assume your employer has given you the task of choosing a corporate DBMS Make a technical check…
A: Corporates DBMS: Oracle, INFORMIX, Microsoft, Ingres, and Sybase SQL-Server, all of which run on…
Q: Proofs: Construct proofs to show that the following symbolic arguments are valid. Commas mark the…
A: Introduction Think about the truth tables.
Q: 1. Write a C++ Program that computes the factorial of an integer number. use (for) loop.
A: C++ Program for above : #include <iostream> using namespace std; int main() { // get…
Q: Create a webpage that works similar to a Calculator, with the following tasks and the appropriate…
A: I have provided HTML CODE (having internal JS ) along with CODE SCREENSHOT and OUTPUT…
Q: Unique answer plz Perl Scripting Explain what effect the CGI::Carp::fatalsToBrowser function has…
A: The answer is
Q: A multiprocessor has a 3.3 GHz clock (0.3 nsec) and CPI = 0.7 when references are satisfied by the…
A: Multiprocessors: It is a computer…
Q: In Java: Write a method that multiplies all elements in the array by 3 and returns it to the main…
A: public class Main{ public static int[] multiply(int arr[]) { int n = arr.length;…
Q: In database management, which of the following is a design case that occurs only when there is an…
A: In database management, there are certain data modeling skills that are required to build design…
Q: What is a Cellular Modem, and how does it work? What are its characteristics, benefits, and…
A: Cellular Modem: It mainly offers cellular connection to PCs, laptops, and tablets. It's mostly sold…
Q: Assume that an input RGB image below is entering a Convolutional Neural Network: 4 6 4. 5 7 4 7 1 3…
A: The answer as given below:
Q: What is the difference between Circuit Switching and Packet Switching?
A: These are the methods by which you can transfer data from one location to another.
Q: Ex plain evrontous Pasitive and negafive bio metric authen-ti Cotion why biomehics is Safer than…
A: In this question, we have to understand erroneous positive and negative biometric authenticate. We…
Q: What exactly is the distinction between a compiler and an interpreter?
A: Intro distinction between a compiler and an interpreter
Q: 1. writing assembler Write assembly code that implements the following C code fragment. This is not…
A: Answer: I have done code in C and also I have attached code as well as code screens shot
Q: Using the Principle of Inclusion-Exclusion, determine the number of binary strings of length…
A: Using principle inclusion - exclusion determine number of binary string of length 13 start with 1111…
Q: Do you know how to code? If so, please provide me an example and explain what it works.
A: Introduction: Actually, assembly code is quite complex because it is a low-level programming…
Q: What portion of the computer may save data even when the machine is not powered
A: The portion of the computer may save data even when the machine is not powered.
Q: Computer science What language does a CPU understand instructions written in?
A: Introduction: Machine language is the only language that the computer understands, and it delivers…
Q: How do Boolean logic and computer circuits relate to one another? What is the significance of…
A: Introduction: The relationship between Boolean logic and computer circuitry is discussed.Logic gates…
Q: Write Python statements that multiply two given numpy arrays of same size element-by-element. Print…
A: The answer as given below steps:
Q: For the following buffer pool, using the LRU replacement heuristic, show the disk block ID of the…
A: According to the information given:- We have to following buffer pool, using the LRU replacement…
Q: d) If the propagation time were less than the transmission delay, where is the first bit of the…
A: The answer is
Q: If 10 devices are added to each network constructed with a star, mesh, ring, or bus topology, what…
A: Topology is the geometrical representation of the network in which computers are connected to each…
Q: Task - 2 Write the ComplexNumber class so that the following code generates the output below. class…
A: Here is the approach : Create the class complex number . Create the init method in the class .…
Q: Where would you put your datacenter? How would you power it? How would you connect it to your other…
A: As per company guidelines we are suppose to answer only first 3 subparts of the question. Kindly…
Q: What are two benefits and two drawbacks of Star topology?
A: What is star topology? A star topology for a Local Area Network (LAN) is one in which each node is…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 4 images

- Three coins are tossed at the same time, each equally likely to come up heads or tails. What is the probability of getting 1 head and 2 tails?Let events A, B, C, and D be given by A = {at least 3 heads}, B = {at most 2 heads}, C = {headson the third toss}, and D = {1 head and 3 tails}. If the probability set function assigns 1/16 toeach outcome in the sample space, find (i) P(A), (ii) P(A ∩ B), (iii) P(B), (iv) P(A∩C), (v) P(D),(vi) P(A∪C), and (vii) P(B ∩ D).CS Fundamentals of AI Learning in agents given the pairs (time, price) (1,3) ,(2,5), (3,8) use linear regression to find the line ax+b that approximate these values. Use that line to calculate the price when the time is 4.
- Consider values shown in the table below:i=1 (cold) i=2 (allergy) i=3 (stomach pain) p(Hi)0.60.30.1 p(E1 |Hi)0.30.80.3 p(E2 |Hi)0.60.90.0Those values represent (hypothetically) three mutually exclusive and exhaustive hypotheses for the patient’s condition. For example, H1: the patient has a cold, H2: the patient has an allergy, and H3: the patient has stomach pain with their prior probabilities, p(Hi)’s and two conditionally independent pieces of evidence (E1, patient sneezes and E2, patient coughs) which support these hypotheses to differing degrees. Therefore;a) Compute the posterior probabilities for the hypothesis if the patient sneezes. What is the conclusion that can be derived from this condition?b) Based on the answer from the previous result, as the patient coughs are now observed, compute the posterior probabilities for this condition. Explain the results.A police academy has just brought in a batch of new recruits. All recruits are given an aptitude test and a fitness test. Suppose a researcher wants to know if there is a significant difference in aptitude scores based on a recruits’ fitness level. Recruits are ranked on a scale of 1 – 3 for fitness (1 = lowest fitness category, 3 = highest fitness category). Using “ApScore” as your dependent variable and “FitGroup” as your independent variable, conduct a One-Way, Between Subjects, ANOVA, at α = 0.05, to see if there is a significant difference on the aptitude test between fitness groups. Identify the correct values for dfbetween and dfwithin A. dfbetween = 7 dfwithin = 7 B. dfbetween = 13 dfwithin = 2 C. dfbetween = 2 dfwithin = 13 D. dfbetween = 2 dfwithin = 2Assume that your hypothesis function is of the form f(x) = w0 + w1x and that the current values of w0 and w1 are 1 and 2 respectively. Further assume that you are using a learning rate (alpha) of 0.001 What is the gradient update for w0 (only the change) associated with the point (1, 12)?
- To train a binary logistic regression model, we used the delta rule to learn the weight of feature i using a training case j: ∆Wij = −ηxij yj (1 − yj )(tj − yj ), where η is the tunable learning rate. Please write down the delta rule for mini-batch gradient descent update assuming the size of mini-batch is n.Please answer the following question from above: What about the linear perceptron classi?er? (hint: activation function now changes from sigmoid to sign)For a HMM, the hidden states are {bull, bear}, the observation variables are {rise, fall}, the initial state probability distribution is [0.5 0.5]¹, the transition probability distribution A is [0.4 0.7; 0.6 0.3], and the observation probability distribution B is [0.8 0.1;0.2 0.9]. If the observation sequence is {fall fall rise}, please show the computation procedure for estimating the most likely state sequence?Suppose you have two boxes A and B. Box A contains 7 black marbles, 4 white marbles. Box B contains 7 white and 4 black marbles. A random experiment is performed in two sequential trials by first drawing a marble randomly from box A and putting into Box B. In the second trial after the first trial, a marble is drawn randomly from box B. If we reverse the scenario, then what is the probability of drawing a black marble from box A given that a white marble is drawn from box B.
- What is the code in Stata for this question? Run the linear regression given by wages = β0 +β1education+β2workexp+β3unionmember +β4south+ β5−9occupation + β10female + u where wages=hourly wage in US dollars; education=years of schooling; workexp=years of work experience; unionmember=a dummy variable equal to ”1” if a person is a union member, and ”0” otherwise; south=a dummy variable equal to ”1” if a person lives in the south, and ”0” otherwise; occupation=a categorical variable equal to ”1” if a person’s occupation is ”management”; ”2” if it is ”sales”; ”3” if it is ”clerical”, ”4” if it is ”service”, ”5” if it is ”professional” and ”6” if it is ”other”. Please make sure to use ”other” as the base category; female =a dummy variable equal to ”1” if a person is female, and ”0” if a person is male.This question involves data from which nothing interesting can be learned about frequent itemsets, because there are no sets of items that are correlated. Suppose the items are numbered 1 to 10, and each basket is constructed by including item i with probability 1/i, each decision being made independently of all other decisions. That is, all the baskets contain item 1, half contain item 2, a third contain item 3, and so on. Assume the number of baskets is sufficiently large that the baskets collectively behave as one would expect statistically. Let the support threshold be 1% of the baskets.(a) Find the frequent itemsets.(b) Prove that in this data there are no interesting association rules, i.e., the interest of every association rule is 0.A group of 15 students made up of 9 females and 6 males form a committee of 5 What is the probability the committee is made up of 3 females and 2 males?

