a) Given f(x)= x³ - 6x +1 Find the exact value of f(1.22) i) ii) Determine the error value, absolute error, and relative error produced from f(1.22) using three decimal points calculation b) Given the following operation 4.232+2.0321+5.43-2.38 Compute the most accurate value for the operation where each number has been rounded to a certain decimal point.
a) Given f(x)= x³ - 6x +1 Find the exact value of f(1.22) i) ii) Determine the error value, absolute error, and relative error produced from f(1.22) using three decimal points calculation b) Given the following operation 4.232+2.0321+5.43-2.38 Compute the most accurate value for the operation where each number has been rounded to a certain decimal point.
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter2: Problem Solving Using C++using
Section2.3: Data Types
Problem 8E: (For thought) Although you have concentrated on operations involving integer and floatingpoint...
Related questions
Question
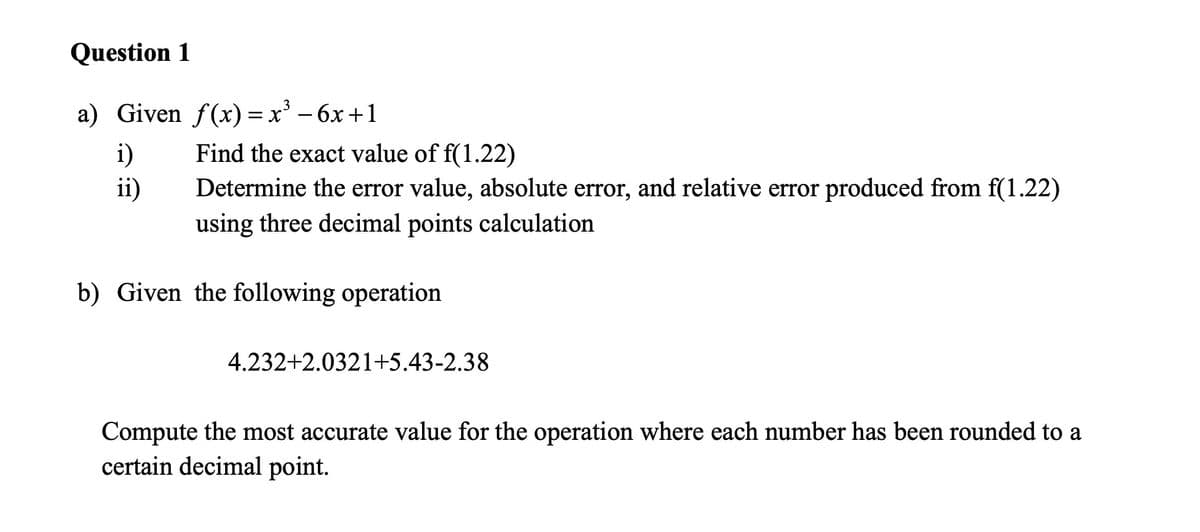
Transcribed Image Text:Question 1
a) Given f(x)=x² - 6x +1
i)
Find the exact value of f(1.22)
ii)
Determine the error value, absolute error, and relative error produced from f(1.22)
using three decimal points calculation
b) Given the following operation
4.232+2.0321+5.43-2.38
Compute the most accurate value for the operation where each number has been rounded to a
certain decimal point.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr