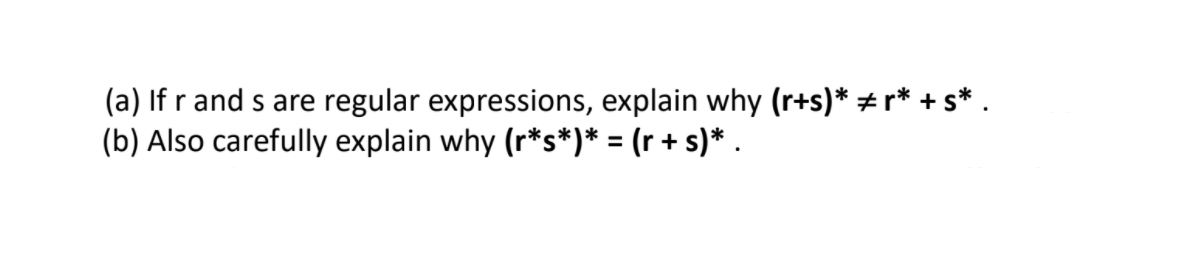
(a) If r and s are regular expressions, explain why (r+s)* + r* + s* . (b) Also carefully explain why (r*s*)* = (r + s)* .
Q: The user decides whether 1. Trapezoid, 2. Ellipse, or 3. Equilateral Triangle. Compute the area of t...
A: The Code is given below.
Q: What kind of worries and challenges arise from the use of an unintegrated information system?
A: Introduction: Computer failure and loss are key issues resulting in unnecessarily high costs and cos...
Q: 1. Write a program to get the first and last element for the linked list. The Elements are (100,200,...
A: As per our guidelines we are supposed to answer only one question. Kindly repost other questions as ...
Q: Computer science Is there a distinction between a logical division and a system subsystem?
A: Introduction: The common plate joints serve as a logical divide between the blocks. Power enters a s...
Q: JAVA PROGRAMMING - Create a class whose main() holds an array containing 10 integers. Create two m...
A: Introduction JAVA PROGRAMMING - Create a class whose main() holds an array containing 10 integers...
Q: 15. (11>11) OR (16>12) in Boolean 16. (2 29) in Boolean %3D 17. 9DAF + OACD= in hex IF 18. F31D – OB...
A: Here in this question we have asked to calculate boolean value , hexadecimal addition, subtraction ...
Q: Write a recursive function recursiveMinimum that takes an integer array, a starting subscript, and a...
A: Program Explanation:- Using the header file. Define the main function. The location is used to swap...
Q: Interpreter and compiler are two different things.
A: INTRODUCTION: Compiler: It is a computer program that converts high-level programming code to machin...
Q: Construct a pushdown automaton which accepts the set of bit strings with 2/3 as many 0 bits as 1 bit...
A: Introduction Construct a pushdown automaton which accepts the set of bit strings with 2/3 as many 0 ...
Q: What exactly is the ToString method?
A: A function toString() method is a built-in Java method that returns the value passed to it in string...
Q: The several methods of file access are listed here. I'm wondering about the benefits and drawbacks o...
A: Introduction: The most basic file access method is: File organization is nothing more than gathering...
Q: What is the definition of a ForkJoinTask? In what ways are RecursiveAction and RecursiveTask differe...
A: The ForkJoinTask class is not easily separated without this mass. All things considered, you can put...
Q: Laboratory Exercises – Java Lesson 5: Creating Classes and Objects 1 a . Create a class named Pizza...
A: Java is a compiled language that follows the concept of oops to make projects. It is used to build v...
Q: Explain briefly with the aid of examples the uses and importance of the following technologies i)Bl...
A: The Answer is given below step.
Q: Explain the stages of Donald Norman's model of interaction in a few sentences
A: A model of how people interact with the real world is one of the themes covered by usability researc...
Q: This assignment requires you to conduct research and compile a list of typical anti-patterns that ar...
A: Introduction: If a "pattern" is merely a solution that is proven to work for a common software engin...
Q: Q19 (C++) int x = 5 create a reference "a" equal to x and output a create a pointer (address type) "...
A: Pointer: Pointers are variables that store the memory addresses of other variables. In C++, pointer...
Q: What exactly is the Named constant?
A: Named constant: Named constant is a constant value that cannot be changed during the execution of a...
Q: Lesson 9: Database - Java programming 1. Create a database of salesman: a. Table Descripti...
A: As per the requirement created a table When we enter the record in a table at the starting commissio...
Q: Consider the role of wireless networks in the growth of today's developing nations. Wireless technol...
A: Introduction: The word "WLAN" refers to a wireless computer network that establishes a local area ne...
Q: A disk stores 512 bytes per sectors, 13 sectors per track, 55 tracks per side and has 2 sides. What ...
A: Given a disk is having 2 sides Each side is having 55 tracks Each track is having 13 sectors Each se...
Q: 6. What is the binary equivalence of decimal 287, in WORD size? 10
A: Here in this question we have asked that what is the binary equivalence of decimal number 287 in wor...
Q: In designing infographics, how can you make it understandable and attractive?
A: 1. Make it helpful to your main interest group:Maybe your infographic is for teaching clients, or ma...
Q: For this question, you will be required to use the binary search to find the root of some function f...
A: import numpy as npdef binary_search(f,domain, MAX = 1000): start ,end = domain # get the start and e...
Q: Which of the following are incorrect statements to create a Lock? O a Lock lock new ReentrantLock(tr...
A:
Q: Case Scenario: Assume a company hires you as a Quality Assurance Engineer. The company asks you to p...
A: Solution: a) The quality assurance mainly focus on the process standard, project audit and procedur...
Q: What is a firewall's principal purpose? What are the general guidelines for using packet filtering?
A: Introduction: A firewall can be defined as a special type of network security device or a software p...
Q: List the five key qualities of cloud computing as specified by the National Institute of Standards a...
A: The five key qualities of cloud computing as specified by the National Institute of Standards and Te...
Q: The most basic peer-to-peer networks are made up of two computers that are directly connected over a...
A: A peer-to-peer network is used for connecting two networks together. The communication between netwo...
Q: A system program is to generate a "1" if the given binary number A3A2A1A0 has a decimal value of eit...
A:
Q: What is the best way to get around an IP block?
A: Introduction: IP blocking refers to prohibiting external connections from specific IP addresses or r...
Q: Is there a point to Big-existence? O's What is the most dire scenario for Big-O? Why should you be c...
A: Introduction: Big-purpose: O's The big-O notation is used to express how the time required to execut...
Q: Express the switching circuit into binary logic notation and contruct logic diagram. Construct the t...
A: In the switching circuit when the switches are connected in series then we have the OR in boolen An...
Q: Computer science On a local area network, what protocol is used to allocate dynamic IP addresses to...
A: Introduction Computer science On a local area network, what protocol is used to allocate dynamic I...
Q: USE PYTHON (GOOGLE COLLABORATORY IS POSSIBLE) Using variables and input functions, make a slambook ...
A: I give the code in Python along with output and code screenshot
Q: Discuss the physical storage and access of files in the schedule management system, as well as how t...
A: Introduction: What is a File Management System, and how does it work?A file management system is a p...
Q: Write a secure Bounded Stack module, for a stack of strings, in C. Fail fast by crashing with an err...
A: Error handling could be a pain, and it’s simple to urge by for an extended time in Node.js while not...
Q: Total = a + b + c; Average = Total / 6; A. Logic Errors Run-time Errors None of the above D. Syntax ...
A: A programming language must follow rules and regulations to execute task successfully. Logical erro...
Q: A palindrome is a word or a phrase that is the same when read both forward and backward. Examples ar...
A: Simple Algorithm: Step1: Start. Step2:Read the string from the user. Step3: Calculate length of the...
Q: What kind of data leak has Facebook/Cambridge Analytica experienced?
A: introduction The ICO determined that Facebook violated data protection regulations by neglecting to ...
Q: Distinguish the fundamental differences between synchronous and isochronous connections, and give an...
A: Asynchronous Connection: In communication, data is exchanged from one end to the other. Asynchronou...
Q: In the code, you are provided with a main() code that asks for an integer input from the user and st...
A: Program Approach:- 1. Include header file 2. Declare a variable of data type integer 3. Take the inp...
Q: pervisors across multiple physical servers located in a data center. If the be extended across multi...
A: Lets see the solution.
Q: Name three websites that employ the MVC design, which allows users to switch between different views...
A: Introduction: MVC is a software design pattern often used to create user interfaces. It divides link...
Q: What are the primary components of the database system
A: Introduction: A database management system (or DBMS) is simply a computerized data storage system. U...
Q: Write a short remark about IPv6, the Internet, virtual private networks, and voice over internet pro...
A: Introduction: IP is the abbreviation for Internet Protocol.
Q: List four different types of external disk interfaces.
A: Introduction: In general, hard disc interfaces are classified as follows: parallel ATA (PATA, also k...
Q: Write a Python program to input an integer t and print the sum of all multiples of t and 5 in the ou...
A: Algorithm: Start Read a number and store it in t Initialize t to 1 and sum to 0 If t*i<500 and (...
Q: Java Write a Java to Implement Prim's and DIJKSTRA's algorithm for Single Source Shortest Path Probl...
A: Dijkstra's approach for least spanning tree is quite similar to Prim's algorithm. We create an SPT (...
Q: What exactly is a data race?
A: Introduction: A data race happens when two or more threads in the same process simultaneously visit ...
Step by step
Solved in 3 steps

- Please give me only the solution to Question-4 solve it by c programming, and please give me the output of the code also!write the code in c++ solve all problems please and do not use std::rand()(Practice) For the following correct algebraic expressions and corresponding incorrect C++ expressions, find the errors and write corrected C++ expressions: Algebra C++ Expression a.(2)(3)+(4)(5)(2)(3)+(4)(5) b. 6+1826+18/2 c. 4.512.23.1S4.5/12.23.1 d. 4.6(3.0+14.9)4.6(3.0+14.9) e. (12.1+18.9)(15.33.8)(12.1+18.9)(15.33.8)
- If () statements in R.Write the following in C++.take the input from the user(infix,postfix and prefix). and then display all three forms(infix,postfix and prefix) of the expression. write the code in c++. step-by-step explanation will be appreciated. please try to implement before sending as I am getting a run-time error when i try to run the code myself.
- y one difference while taking input a int array and char array in C++ with the helpUsing only the variables x and y and the functions cons, car, cdr, & reverse, provide Lisp ; S-expressions for generating the following: 2a create (1 2 c d) (print nil ) 2b create ((d c) (4 3)) (print nil ) (terpri) (terpri)2) Simplify the following Boolean expressions, using three-variable K-maps:F(x,y,z) = x′y′ + yz + x′yz′ PS:Please type instead of paper writing



