// a) int sum = 0; for (int i = 1; i <= N + 2; i++) { sum++; } for (int j = 1; j <= N ⋆ 2; j++) { sum += 5; } cout << sum << endl; // b) int sum = 0; for (int i = 1; i <= N 5; i++) { for (int j = 1; j <= N 5; j+= 2) { sum++; } } cout << sum << endl; answer: answer:
Q: Give two instances of how you'd really utilize a menu in an application, and explain why you'd…
A: Menu-driven interface: Simple and easy to use. It has sub-menus. On touch-screen devices, users push…
Q: What kind of foundational network design would you recommend? Why?
A: The topology of your network describes the physical and logical relationships between your network's…
Q: WPA2 might be the best wireless access method for your needs. Just what makes this option better…
A: WPA2 (Wi-Fi Protected Access II) is considered the best wireless access method because it provides a…
Q: Despite the fact that the debugging procedure was performed, the problem could not be resolved. What…
A: Please refer to the following step for the complete solution to the problem above.
Q: Create a software that uses the name as the key to store names and phone numbers from a text file in…
A: Given: A text file containing a list of names and phone numbers, separated by a space. Task: Create…
Q: Derive generalized expressions for arc-connectivity, diameter, bisection-width, and link cost of a…
A: Arc-Connectivity: min(M,N) Diameter: max(M,N)-1 Bisection-Width: min(M,N)/2 Link Cost: max(M,N) -…
Q: For the sake of cyber safety and network safety, firewalls are crucial. Describe the concept and…
A: Firewall is a security system that monitors and controls incoming and outgoing network traffic based…
Q: give an example of a network with no more than 6 nodes and define all the data structure used by a…
A: Distence vector The distence vector is nothing but the distributed, iterative and asynchronous.…
Q: For example, wireless networks are becoming more important in the world's poorest nations. In many…
A: Wireless technology It refers to the use of wireless communication to transfer data, voice, or…
Q: Exists a method to use technology to improve the education of pupils today? My ICT education has had…
A: ICT (Information and Communications Technology): The term "information and communications…
Q: Why is it so vital to include technology into the teaching-learning process in the contemporary…
A: It is crucial for our educational system to include technology in the teaching-learning process…
Q: In what two parts of your application do you make use of menus, and can you explain why you would do…
A: Imagine that it is now three o'clock in the afternoon, and you have just gotten out of class. You…
Q: What do you expect from team leadership? Which components of management do you find appealing, and…
A: Below are the abilities needed of a manager: • Must be able to establish a vision for the…
Q: Without using truth tables, show that ¬p (q r) and q (p r) are logically equivalent. Prove that…
A: Without using truth tables, show that ¬p (q r) and q (p r) are logically equivalent. To show…
Q: Throughout the course of the software development process, what role did software development kits,…
A: Please find the answer in next step
Q: 2. The given program segment is supposed to perform the swap, but does not use a temporary variable.…
A: Introduction: The program segment is an attempt to swap the values of two variables, x and y,…
Q: Exists a method for preventing tampering with class fields?
A: Preventing unintentional field corruption In order to avoid class fields from being unintentionally…
Q: This article addresses the recommended practices for vulnerability detection and evaluation
A: Vulnerability detection and evaluation is a process of identifying, assessing, and prioritizing…
Q: What distinguishes a shallow copy from a deep one in terms of copywriting?
A: Please refer to the following step for the complete solution to the problem above.
Q: What exactly is it that a computer programmer does all day?
A: Introduction To do a given computation, a computer programme must be programmed (or, more broadly,…
Q: Where do the dangers lie in moving data from one server to another?
A: Introduction : A server is a computer or piece of software that provides resources, data, services,…
Q: The contrasts between Windows Defender and another free anti-malware tool are highlighted.
A: Introduction: An integrated, free anti-malware program for Windows operating systems is called…
Q: Imagine that you are developing a piece of software in Java to maintain a record of the names and…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: Sign up for a class that teaches a computer programming language the next semester. How do you…
A: Many programming languages are accessible for study, including Java, C#, Python, and Javascript.…
Q: The many forms and purposes of malware may be catalogued in detail.
A: Introduction: Software that is specifically made to harm a computer system is known as malware. It…
Q: AM is an abbreviation for "random-access memory" in computer jargon. It's recommended to create two…
A: Random-Access Memory (RAM) plays a critical role in the software installation process of an embedded…
Q: Explain how each Microsoft program may be utilized for a variety of objectives as you go through…
A: Microsoft offers a wide range of software products, each with its own set of features and functions…
Q: How closely are linear and logical address related to one another?
A: What are logical and linear addresses, and what is their relationship? RELATION BETWEEN LOGICAL AND…
Q: What does the term "system changeover" mean in the context of computers? here?
A: If we talk about, system change over in computers , it is basically done by parallel running…
Q: Translate each of these statements into logical expressions using predicates, quantifiers, and…
A: Let T(x) be "x is a tool." Let C(x) be "x is in the correct place." Let E(x) be "x is in excellent…
Q: There must be a minimum of five distinct topologies that may be used for typical network…
A: Network Topology Types Topology of stars Each device in a star topology is connected to a single hub…
Q: A student is doing research on her assignment on her computer right now. Is she primarily a core…
A: 1) A core operator and an edge operator are two different concepts in the context of networking. 2)…
Q: How might companies that rely heavily on information systems profit from using the deep web?
A: Encryption: Business processes, operations, intelligence, and information technology are all…
Q: There are two main characteristics of today's educational technology curricula. Explain the…
A: 1) Educational technology curricula refer to the course of study in educational institutions that…
Q: Identify the key differences between procedural and object-oriented programming languages and…
A: In this question we need to answer some questions related to programming and cloud services like…
Q: ake a 1,000-item array of random numbers using the SeqSearch and BinSearch methods of the CArray…
A: Here is an example of a CArray class in C++ with a 1,000-item array of random numbers:- #include…
Q: Give some examples of the benefits that a paperless government might bring.
A: Answer:-
Q: What was the driving force behind the development of different languages for use in computer…
A: System language: Reasoning for this is because HTML is not a programming language. Regrettably, you…
Q: To clarify, what does it mean to "debug" something?
A: Debugging: Debugging is the process of finding and eliminating flaws in software code, both actual…
Q: If you need to back up or restore data, what are the most important considerations?
A: Introduction : Making copies of data and files so that the originals can be restored in the event of…
Q: In the field of computer science, there are several approaches that may be taken to solve a variety…
A: Please refer to the following step for the complete solution to the problem above.
Q: Specifically, what is it that makes up random access memory? Two groups should be created. Could the…
A: Computer memory It is a type of computer storage that is used to keep data and instructions that the…
Q: How should a proper routing table be set up on each router?
A: Introduction : The process of choosing the most efficient route for data to take within a computer…
Q: How would I fill out the Gant Chart for this using the Shortest Remaining Time to Finish (SRTF)…
A: Shortest Remaining Time to Finish (SRTF) operating system algorithm is used to execute processes…
Q: For this problem, you will implement divide and conquer algorithms: the maximum subarray. I have…
A: The JAVA code is given in the below step
Q: Express the following function as a sum of minterms and as a product of maxterms:…
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: How do the benefits and drawbacks of using open source software products and commercial software…
A: What are the pros and cons of open-source software vs. proprietary application packages? (based on…
Q: Is there any way that technology has improved our way of living?
A: Introduction : Technology is the practical application of scientific knowledge, particularly in the…
Q: Suppose that Smartphone A has 4GB RAM and 128 GB ROM, and the resolution of its camera is 14 MP;…
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: In order to evaluate whether or not a pattern does in fact exist, this kind of virus scan checks for…
A: Yes, that's correct. Signature-based antivirus scanning is a method used to detect malware by…
Give a tight bound of the nearest runtime complexity class for each of the following code fragments in Big-Oh notation, in terms of the variable N. In other words, write the code's growth rate as N grows. Write a simple expression that gives only a power of N using a caret ^character for exponentiation, such as O(N^2) to represent O(N2) or O(log N) to represent O(log2 N). Do not write an exact calculation of the runtime such as O(2N3 + 4N + 14).
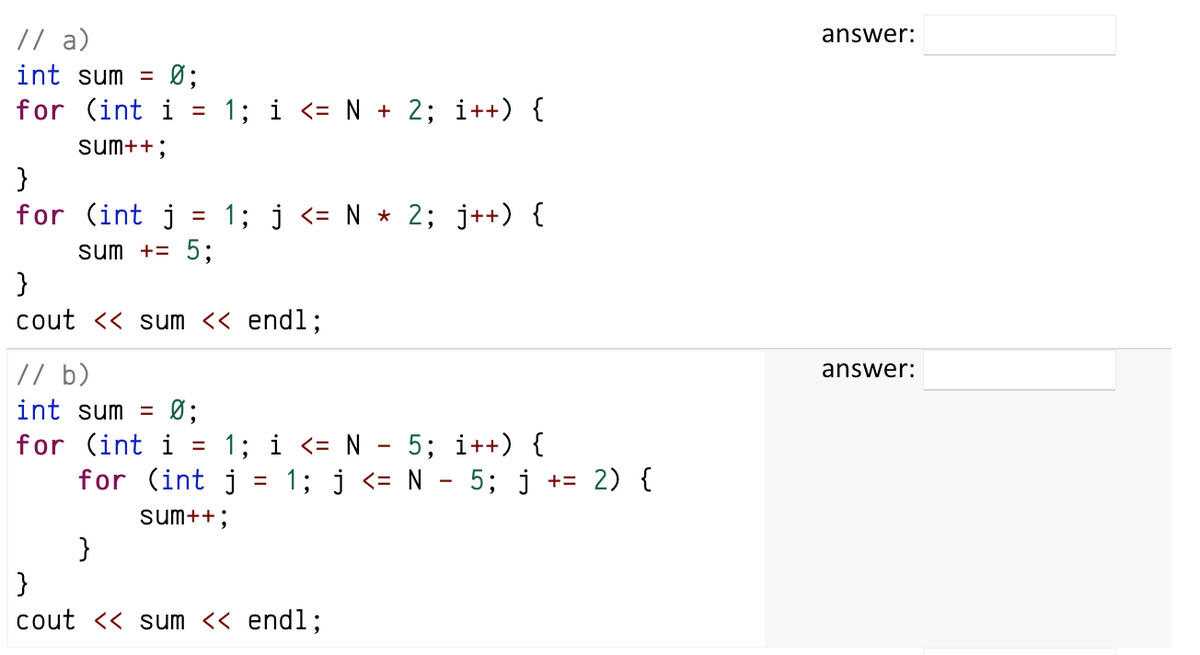
In this question, it is asked to calculate the Big-Oh notation for the following code segments.
The exponential complexity must be defined with ^.
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Code in C++ Language As a cashier, you would always hate those times when customers choose to take back their order since you'd always summon your manager and yell, "Ma'am pa-void!" No matter how you hate it, you always have to do it since you have no other choice. Given (1) an array of prices of the items, (2) another array of the items the customer wishes to take back, and (3) the customer's payment, print the change of the customer. Input: The first number indicates the number of items "n" brought to the cashier. The next "n" numbers are the prices of the items. The next number indicates the number of items "m" that the customer wants to take back and not proceed. It is assured that 0 <= m <= n. The next "m" numbers are the items to be void that ranges from item 1 to item "n". The final number is the customer's payment. It is also assured that the given payment >= final price of items. INPUT: 5 103.65 650.95 10.25 1067.30 65.18 2 1 5 2000.00 Output: The change…Transcribed Image Text JAVA Programming Problem: In the game of "Assassin's Creed", you control a ship with a cannon which is attacking a large enemy Assassin's Creed, armed with many guns. Your goal is to destroy as many of the guns as possible. The battle field is a 2D Cartesian grid, where your cannon is located at the origin. The enemy Assassin's Creed is a horizontal line segment located from the coordinates (X1, Y) to (X2, Y). There are exactly (X2 - X1 + 1) guns on the ship, located at the integer points (X1, Y), (X1+1, Y), ..., (X2, Y). However, the problem is, you cannot always fire at a gun. There are supernatural rocks located at all points of the battlefield whose X and Y coordinates are both integers. In order to fire successfully at an enemy's gun, the line connecting your cannon and that gun must not go through any rocks. Develop a JAVA code to output the number of the enemy battleship's guns that your cannon can destroy. Test Case Result 1 2 2 -2In java there must be at least two calls to the function with different arguments and the output must clearly show the task being performed. Develop a function that accepts an array and returns true if the array contains any duplicate values or false if none of the values are repeated. Develop a function that returns true if the elements are in decreasing order and false otherwise. A “peak” is a value in an array that is preceded and followed by a strictly lower value. For example, in the array {2, 12, 9, 8, 5, 7, 3, 9} the values 12 and 7 are peaks. Develop a function that returns the number of peaks in an array of integers. Note that the first element does not have a preceding element and the last element is not followed by anything, so neither the first nor last elements can be peaks. Develop a function that finds the starting index of the longest subsequence of values that is strictly increasing. For example, given the array {12, 3, 7, 5, 9, 8, 1, 4, 6}, the function…
- please code in python Forbidden concepts: arrays/lists (data structures), recursion, custom classes You have been asked to take a small icon that appears on the screen of a smart telephone and scale it up so it looks bigger on a regular computer screen.The icon will be encoded as characters (x and *) in a 3 x 3 grid as follows: (refer image1 ) Write a program that accepts a positive integer scaling factor and outputs the scaled icon. A scaling factor of k means that each character is replaced by a k X k grid consisting only of that character. Input Specification:The input will be an integer such that 0 < k ≤ 10. Output Specification:The output will be 3k lines, which represent each individual line scaled by a factor of k and repeated k times. A line is scaled by a factor of k by replacing each character in the line with k copies of the character. [refer image2](Coding Language C++) Dynamic Programs Hoskins College offers both curriculum and continuing education courses. Write a program that dynamically tracks these courses using an array of object pointers. Every course (both curriculum and continuing education) has a course id, title, room number, and number of contact hours. A curriculum course has credit hours and tuition rate. Tuition is calculated by multiplying the course's credit hours by tuition rate. A continuing education course has a flat fee (cost). Implement a show() function in every class that displays the data in the object. Part A: Create an inheritance-based collection of classes to represent these different courses. Include code in main to test your work by instantiating objects of the two derived classes. Part B: Modify your program. Remove the objects you created in main to test the classes. Modify the base class so that show() becomes a virtual class. In main, create a single array capable of holding pointers to…C++ Dynamic Programs Hoskins College offers both curriculum and continuing education courses. Write a program that dynamically tracks these courses using an array of object pointers. Every course (both curriculum and continuing education) has a course id, title, room number, and number of contact hours. A curriculum course has credit hours and tuition rate. Tuition is calculated by multiplying the course's credit hours by tuition rate. A continuing education course has a flat fee (cost). Implement a show() function in every class that displays the data in the object. Part A: Create an inheritance-based collection of classes to represent these different courses. Include code in main to test your work by instantiating objects of the two derived classes. Part B: Modify your program. Remove the objects you created in main to test the classes. Modify the base class so that show() becomes a virtual class. In main, create a single array capable of holding pointers to objects of both…
- Explain following code segment:int [] a = new int [3];int [] b = new int [3];a = b;Language: JAVA Script Your company is giving every employee earning less than $50,000 a 10% raise! *Write a function 'employeeRaises(peopleObj)' that takes an array of objects s containing employee names and their salaries and returns an array containing the employees that need raises, along with their new salaries. Example: employees [ {name: "Alice", salary: 80000}, {name: "Bob", salary: 48000 }, {name: "Carol", salary: 60000}, {name: "Dan", salary: 78000}, {name: "Ellen", salary: 100000}, console.log(employeeRaises (employees) ); // [ { name: 'Bob', salary: 44000 } ] funcation emplyeeRaises(employees){ |// Your code here} /****DO NOT MODIFY ANYTHING UNDER THIS LINE****/ try{| module.exports = employeeRaises;}catch (e) {|module.exports=null;}Java Questions - (Has 2 Parts). Based on each code, which answer out of the choices "A,B,C,D,E" is correct. Each question has one correct answer. Thank you. Part 1 - 3. Given the following code, the output is __. class Base { private int x = 5; }class Derived extends Base { x = 6; }public class Sample { public static void main(String[] args) { int x = 7; Derived d1 = new Derived(); System.out.print(d1.x); }} A. 0B. 5C. 6D. 7E. Error message Part 2 - 4. A class Animal has a subclass Mammal. Which of the following is true? A. class Animal extends Mammal { }B. class Mammal extends Animal { }C. class Animal implements Mammal { }D. class Mammal implements Animal { }E. class Mammal { Animal a1 = new Animal(); }
- Java Functions with Array Create a function named palindrome that asks the user an integer input if called. If the number is a palindrome, print “{input} is a palindrome!”, otherwise print “{input} is not a palindrome!”. In the main function, call the palindrome function. Input 1. One line containing an integer Output Enter a number: 121 121 is a palindrome!Please correct the error for this code: import java.util.Scanner; // import Scanner class required to accept input from userpublic class Main // To declare 3 variables for employee ID, Name and Salary{ public static void main(String[] args) { int i; int num; Scanner obj = new Scanner(System.in); System.out.print("Enter number of employees: "); // user should enter the number of employees int num = obj.nextInt(); Employee emp[] = new Employee[num]; // create an array of num for (i = 0; i < num; i++) { Employee e = new Employee(ID, Name, Sal); emp[i] = e; System.out.println("Employee details: "); // To store the employees details System.out.print("Enter ID: "); int ID = obj.nextInt(); System.out.print("Enter Name: "); String Name = obj.nextLine(); System.out.print("Enter Salary: "); double Sal =…In java Develop a function that accepts an array and returns true if the array contains any duplicate values or false if none of the values are repeated. Develop a function that returns true if the elements are in decreasing order and false otherwise. A “peak” is a value in an array that is preceded and followed by a strictly lower value. For example, in the array {2, 12, 9, 8, 5, 7, 3, 9} the values 12 and 7 are peaks. Develop a function that returns the number of peaks in an array of integers. Note that the first element does not have a preceding element and the last element is not followed by anything, so neither the first nor last elements can be peaks. Develop a function that finds the starting index of the longest subsequence of values that is strictly increasing. For example, given the array {12, 3, 7, 5, 9, 8, 1, 4, 6}, the function would return 6, since the subsequence {1, 4, 6} is the longest that is strictly increasing. Develop a function that takes a string…



