A microprocessor's functionality has to be tested: 1. Temperature: 100C, 150C and 200C. 2. Pressure : 2 psi,5psi and 8psi 3. Doping Amount : 4%,6% and 8% 4. Deposition Rate: 0.1mg/s, 0.2 mg/s and 0.3mg/s Find all factors (2), levels (2) and identify size of required orthogonal array (6). Map the identified values to appropriate orthogonal array and make test cases. A A A A Aa B A9 BBA JDUJE b b a Ba b b a a b b a a a b b a b b a b B baa a a A b aaa bb a с bb a с A10 ba b a 566 b b a a с b a a b b OO с с b a a с b с b a b caba A11 aa b C a b с a b с a a b b b с с с a a b с с a a b b b a с C a с b C b
A microprocessor's functionality has to be tested: 1. Temperature: 100C, 150C and 200C. 2. Pressure : 2 psi,5psi and 8psi 3. Doping Amount : 4%,6% and 8% 4. Deposition Rate: 0.1mg/s, 0.2 mg/s and 0.3mg/s Find all factors (2), levels (2) and identify size of required orthogonal array (6). Map the identified values to appropriate orthogonal array and make test cases. A A A A Aa B A9 BBA JDUJE b b a Ba b b a a b b a a a b b a b b a b B baa a a A b aaa bb a с bb a с A10 ba b a 566 b b a a с b a a b b OO с с b a a с b с b a b caba A11 aa b C a b с a b с a a b b b с с с a a b с с a a b b b a с C a с b C b
Chapter4: Processor Technology And Architecture
Section: Chapter Questions
Problem 2PE: If a microprocessor has a cycle time of 0.5 nanoseconds, what’s the processor clock rate? If the...
Related questions
Topic Video
Question
Software Quality Engineering question
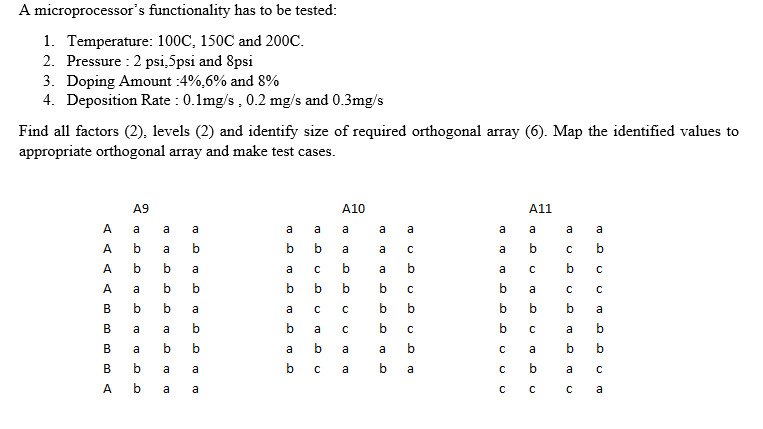
Transcribed Image Text:A microprocessor's functionality has to be tested:
1. Temperature: 100C, 150C and 200C.
2. Pressure : 2 psi,5psi and 8psi
3. Doping Amount : 4%,6% and 8%
4. Deposition Rate : 0.1mg/s, 0.2 mg/s and 0.3mg/s
Find all factors (2). levels (2) and identify size of required orthogonal array (6). Map the identified values to
appropriate orthogonal array and make test cases.
A A A
A9
A a
BBA
a
b a
b
b
b
A b
A
B
B a
a
b
a
a b
b a
a
А b
a
b
a
b
a
b
b
a
a
a a
b
b
a
b
a
b
a
b
C
b
с
a
b
с
A10
a
a
b
U
b
с
C
a
a
a
a
a
b
b
b
a
b
a
C
b
с
b
с
b
a
a
a
a
b
b
b
с
C
с
A11
a
b
с
a
b
с
a
b
с
a a
C b
b
C
b
C
C
a
b
a
b b
a
с
с
a
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 5 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning