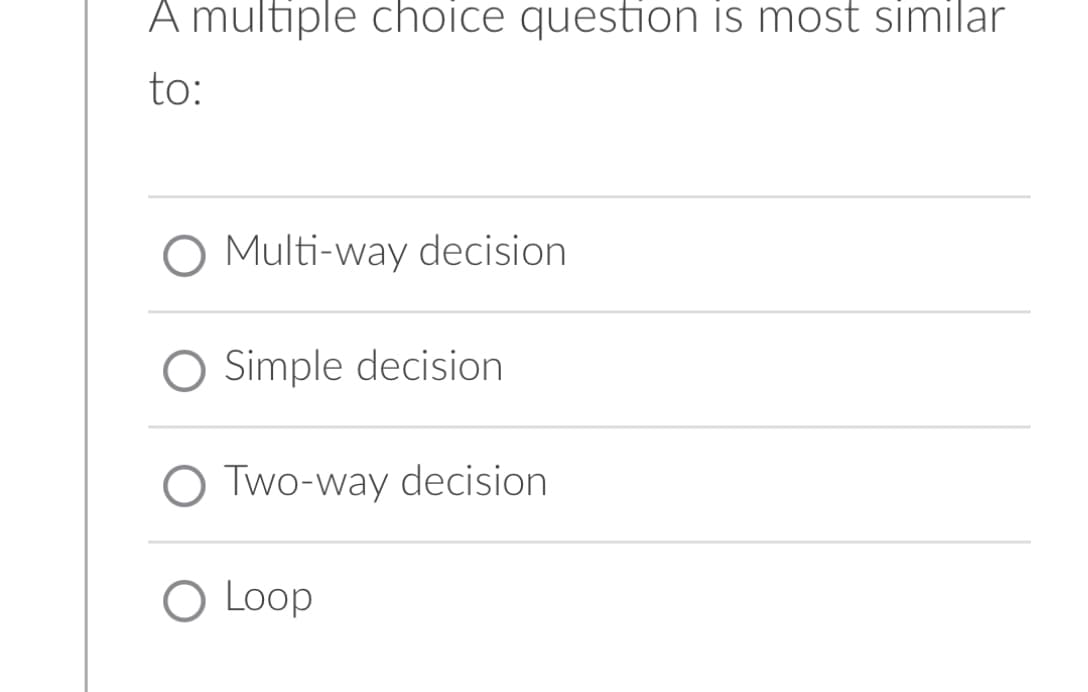
A multiple choice question is most similar to: Multi-way decision O Simple decision O Two-way decision O Loop
Q: What is the name of the SSH client file that an administrator must use in order to pre-configure an…
A: Basics: A cryptographic protocol known as Secure Shell is used to operate business functions…
Q: s used to encrypt data sent between a web browse
A: Solution - In the given question, we have to tell which protocol among SSL or TLS, is used to…
Q: Do user-level threads have any benefits over kernel-level threads? How different are threads created…
A: There are no user-level threads known to the OS. Their execution is limited to the time slots given…
Q: Do you feel that each virtual machine thread utilizes the same JVM method area?
A: The Java Virtual Machine, or JVM, loads, validates, and executes Java bytecode. It is known as the…
Q: An organization has a class C network 196.10.10 and wants to f
A: The answer is
Q: The telephone network, the oldest and most well-known (wired) communication network in the world,…
A: Networks for telecommunications involve circuit switching. Two network nodes may interact after…
Q: Let's say the IT department at your company wants to construct a server room that won't need any…
A: Given: In light of the issue that was presented before, we are obligated to discuss the…
Q: Why do we rely on MATLAB while trying to solve challenges when working in computational geometry?
A: The following are some advantages gained by utilising MATLAB: The first and most crucial thing to…
Q: We contrast and compare DMA and cache memory.
A: Answer: We need to write the what are the comparison between the Dynamic Memory Allocation (DMA) and…
Q: Simplify the following Boolean Expression and create the logical diagram usingNAND or NOR…
A: Given, F(A, B, C, D) = ∑m {1,3,5,7,8,10,12,14} First we need to find an expression using K-map As we…
Q: What exactly does it mean to normalize a database management system?
A: Normalization in Database Administration: It is a procedure contained in a relational model of a…
Q: Both b and d The tendency of aqueous liquids to rise in narrow glass tubes (a phenomenon called…
A: Here in this question we have asked that tendency of aqueous liquid to rise in narrow glass tubes in…
Q: We believe that Flynn's taxonomy may benefit from an additional level of classification. What are…
A: The acceptance of Flynn's taxonomy on a broad scale is based on two criteria. These include: - The…
Q: Do you feel that each virtual machine thread utilizes the same JVM method area?
A: Introduction: The Java Virtual Machine (JVM) is what powers Java code. Java bytecode is transformed…
Q: Given a neural network, its structure is shown below. z;" is the output of the linear part of th…
A: Answer: We have written how many parameter is required of the given diagram so we have explain in…
Q: mice equipped with an optical sensor that is able to detect every movement made by the mouse.
A: The optical mouse uses an optical sensor to track mouse movement. Visual mouse: It uses an optical…
Q: How does the generation and verification process work for the ElGamal Digital Signature, if you…
A: The above question is solved in step 2 :-
Q: Please describe, with regard to transparency, the following minimal desirable qualities of a…
A: Introduction: It is not necessary to have just one single logical database in order to have a…
Q: "During the production phase of the CBS, it is important to measure a vendor's response to system…
A: Answer is
Q: Consider where you stand in a value chain and act accordingly. What is the purpose of the value…
A: Start: The value chain is made up of a set of activities that are used to turn input into output in…
Q: Wireless networks' fundamental properties raise several problems. Describe three of these issues and…
A: Wireless networks:- Wireless networks are computer networks that are not wired together. The…
Q: Are MAC addresses able to be shared across two different network interfaces? Or not? Is it possible…
A: Introduction: Can MAC addresses on two network interfaces be shared? A local network (LAN) should…
Q: List 4 common vulnerabilities found in an industrial network. For each vulnerability provide an…
A: Introduction: Industrial Network: An industrial network is a broad term encompassing the various…
Q: heap-dynamic variables, when it is appropriate to do so, and the many benefits associated with doing…
A: Introduction: The variable is attached to heap storage when a worth is relegated to an IMPLICIT…
Q: Find vertical and horizontal asymptotic
A: Write the function for which you are looking for the vertical asymptote first. This function will…
Q: Write Algorithm for Interchange Base Points Input : a group G; a base [131,132 ..... 13k] for G and…
A: Please find the algorithm in the following steps. given data: Input: a group G; a base [131, 132…
Q: In the realm of computers, architecture and computer-based organization are two separate but related…
A: Structural layout: Architecture design describes the way a computer system's hardware is put…
Q: What are some examples of the many kinds of data that may be kept in the various kinds of databases,…
A: Introduction: The acronym SQL stands for Structured Query Language, which is used for tasks like…
Q: What is the primary difference between restarting a service and reloading it?
A: Introduction: The following is an explanation of the distinction between restarting a service and…
Q: Python
A: I have used Python 3 in showing the result of the above options. These are considered a epressions…
Q: Discuss Finite Automata Representing a Regular Expression
A: In this question we have to discuss Finite Automata Representing a Regular Expression Let's…
Q: Continue your discussion of how the convergence of computers, telecommunications, and media has led…
A: A ground-breaking product that establishes an entirely new industry is an example of disruptive…
Q: 2. Convert the following symbolic microoperations into register transfer statements and to binary.…
A: Here is the complete explanation of the above problem. see below steps.
Q: My IDE is BlueJ, and when I run the main method it does not write to a text file.
A: In this we have to address the issue with the blueJ Let's discuss and solve
Q: 8. Identify the authors of the books Becca Nelson ordered. Perform the search using the customer…
A: The question is to write SQL query for the given problem.
Q: It is important to be aware of the distinction between programming in parallel and programming in…
A: Complete Regression: All potential models or all potential regressions are other names for it. Once…
Q: Short Answer: Explain segmentation vs segregation in relation to ICS network design and…
A: INTRODUCTION: ICS: Industrial Control Systems (ICS) have transitioned from stand-alone isolated…
Q: What objectives do computer operating systems have?
A: An operating system is the program that acts as the interface between the software and computer…
Q: Define the language that computers use.
A: Machine language is the language that a computer understands. It is really difficult to comprehend,…
Q: When a thread is active on a Java virtual machine (JVM), the JVM only permits that thread to execute…
A: Introduction: A thread can only execute one function at a time while it is operating on a Java…
Q: The cost function of a general neural network is defined as J(ŷ,y) 1 m L(VW), y() The loss function…
A: Answer: We have explain what is the differences between the Stochastic, Batch and Mini Batch…
Q: How to Insert Data into the Workshop Applet
A: A Workshop applet's buttons relate to steps that an algorithm takes with each click. The length of…
Q: In pythion with numpy I have code in a for loop that creates a vecor of 12 elements: x = 1 2 3 4 5…
A: Answer: Algorithms: Step1: we have import numpy as np as module Step2: we have print the 1 to 12 by…
Q: You have been given the sales receipt (see the file sales_receipt.pdf in the extra folder) created…
A: Here is the html code of the above problem. See below steps for code and output.
Q: True or false, and please provide a short explanation for how you feel about each of the following…
A: Alternating-Bit Protocol and the SR Protocol: With a sender and receiver window size of 1, the…
Q: This function will be able to determine the fields in a log entry it needs to look at in order to do…
A: A log document is a file that records events that occur in an operating system or other programs or…
Q: When compared to beginning a data modeling project with a blank sheet of paper, what are the…
A: Introduction: A data model aids in conceptual, physical, and logical database architecture. Though…
Q: Write a method quicksort that takes in an ArrayList of integers and returns them in ascending order,…
A: Start An element from the list is chosen as pivot which is used it to divide the list into two…
Q: It is now possible to look at the benefits and drawbacks of shared and private L2 caches for…
A: Introduction: Execution of a single series of instructions is what happens in a single-threaded…
Q: How can the data that was lost in a backup that was made using double parity in RAID systems be…
A: Introduction: In light of the information provided, we must clarify how lost data may be recovered…
Step by step
Solved in 2 steps

- A decision is based on a(n) ____________ value.write this in pseudocode #4 – In pseudocode, write a for-loop that decreases from 100 to 2 by 2s. Inside the loop, print the value of the loop variable unless the value is from 60 to 80 (inclusive). Use only 1 if-statement. Do NOT write Python code! Write your answer below: #5 – Review the decision structure given below. If myAnswer > 20 Then myAnswer = myAnswer - 25Else If myAnswer <= 5 Then If myAnswer < 0 Then myAnswer = 10 If myAnswer < 3 Then myAnswer += 10 Else myAnswer += 1Else myAnswer = 9 If myAnswer < 10 ThenmyAnswer += 1 Display myAnswer What are the results displayed when the decision structure above executes for each given value below:If myAnswer = 6 then myAnswer = myAnswer = 15 then myAnswer = myAnswer = 30 then myAnswer = myAnswer = 2 then myAnswer = myAnswer = -1 then myAnswer = #6 – 2-dimensional arrays can be thought of as containing rows…Fill in the blank question: Q. IVR is also known as _______________ Response.
- If a person is 17 years old, what will be the outcome if the following snippet of code is executed.“ if NOT(age < 18) thenoutput “The person can vote”elseoutput “The person cannot vote”endif”The program shall be solved either by using if else ladder or switch only. No marks will be awarded if the problem is solved using any other technique. Problem: Read your name and one numeric value [Omani Rial], print the following menu as shown in below output, read user choice. Find and print equivalent currency value. Formulas: 1 Omani Rial = 2.60 US Dollars 1 Omani Rial = 2.18 Euros 1 Omani Rial = 1.86 British pounds 1 Omani Rial = 9.55 UAE DirhamsAnswer only if you are 100% sure . Correct and detailed answer will be Upvoted else downvoted. Thank you! Nested loops are problematic areas for testers. Comment on this.
- Implement the ff. decision table using a nested if statement. Assumethat the grade point average is within the range 0.0 through 4.0 GRADE POINT AVERAGE TRANSCRIPT MESSAGE 0.0 – 0.99 Failed semester – registration suspended1.0 – 1.99 On probation for next semester2.0 – 2.99 ( no message )3.0 – 3.49 Dean’s list for semester3.5 – 4.00 Highest honors for semesterFor this homework assignment, you are asked to design an algorithm to compute the employee's bonus using the rules shown below: Bonus Schedule Overtime - (2/3) * Absent Bonus Paid greater than 40 hours = $50 ,greater than 30 but less than 40 hours =$40 ,greater than 20 but less than 30 hours =$30, greater than 10 but less than 20 hours= $20 ,less than 10 hours =$10The answer is one of the options below please solve carefully and circle the correct option Please write clear .



