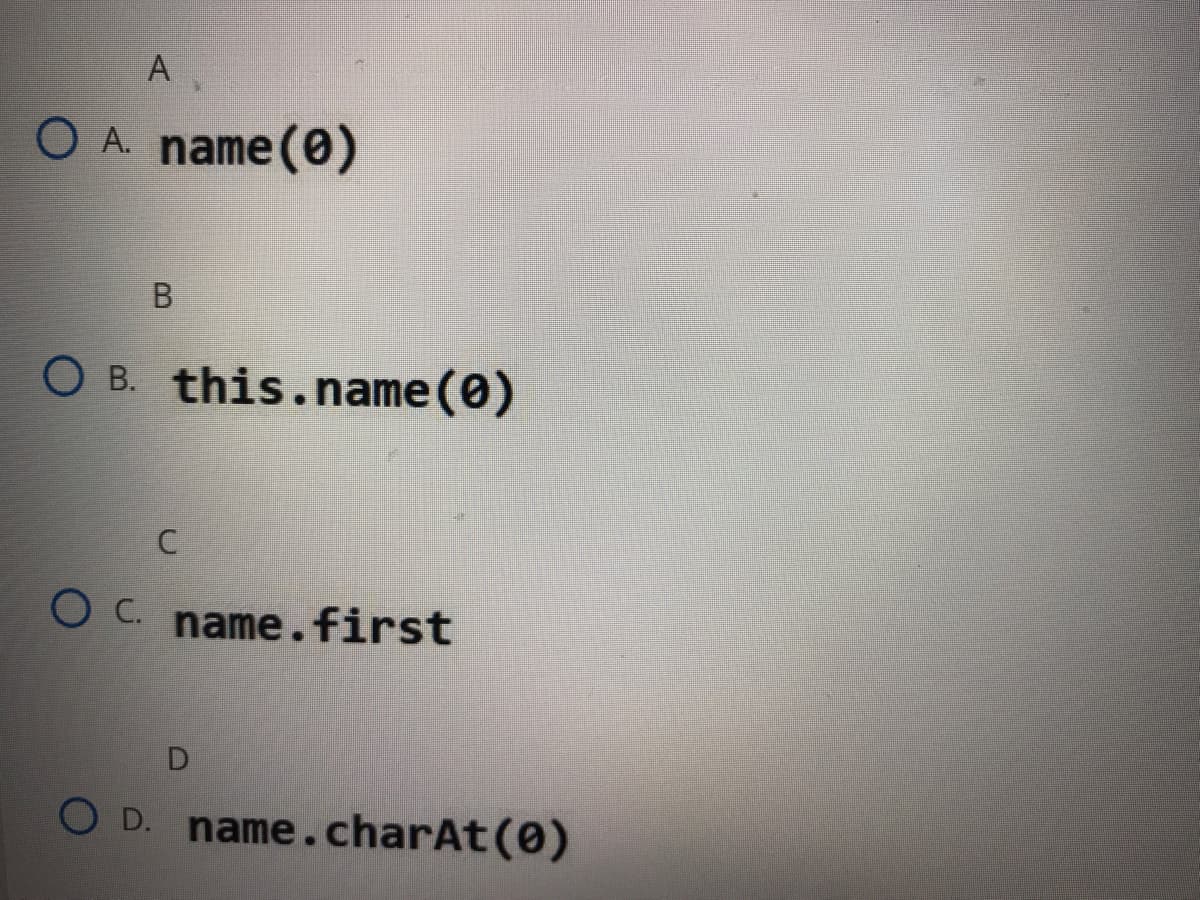
A partial definition of the Account class is shown below. Select the best option to fill in the blank public class Account { private double balance; private String name; //rest of class not shown //assume that all class variables have been initialized //return first initial of the name variable public char getInitial(){return ];}
Q: The study of computers Explain how early computers contributed to the creation of contemporary…
A: Intro The evolution of computing hardware can be traced from the earliest basic calculators to…
Q: Create an ER-Diagram which models the various Departments, Courses, Students, Employees of Manipal…
A: 1. Given entities are:* Students* Department* University* Course* Employees Attributes are the…
Q: What are some of the most recent trends in cybercrime to keep an eye out for? Cybercrime is on the…
A: Definition: Which current cybercrime tendencies should you be aware of? What should law enforcement…
Q: ty's Implic
A: They are utilizing technology to change people's thought process. It improves the local area and…
Q: What are the benefits and drawbacks of using TCP?
A: TCP snooping: The TCP semantic is retained from start to finish. The majority of the improvements…
Q: explain the embedded system's handshake protocol
A: In the transmission of information, there can either be no handshaking, equipment handshaking or…
Q: Covert the following C++ code into set of MIPS instructions: if (x < 10) y = x * x; else y = x/4;…
A: Given code is: if(x<10) y=x*x; else y= x/4;
Q: What do you think about the FSF?
A: Introduction FSF is abbreviated as Free Software Foundation. It is a non profit organization founded…
Q: C# LANGUAGE create a Windows application using Visual Studio then create a simple word-guessing…
A: The solution to the given question is: Using C# Language and Visual Studio Create a simple…
Q: What are the best results for healthcare data/cybersecurity breaches
A: Answer to the given question To characterize data breach: a data breach uncovered secret, touchy, or…
Q: Can you fix the error in the python code. import numpy as np import matplotlib.pyplot as plt N…
A: The division is not done with the Zero. The error in this python code is at line 46. i.e t_thre=…
Q: Show how to modify the all-pairs shortest path algorithm so that it detects negative-weight cycles…
A: Lets first see how is this , negative cycle looks like, below is shown negative cycle is what ? As…
Q: Investigating the mechanisms that enable computers to be so powerful. You may be wondering how…
A: Computers in the education system: Computers are utilised to enhance the learning process of…
Q: When it comes to email, what are the five most important rules and guidelines?
A: Some of the following are essential email etiquette rules that every professional needs to know…
Q: security Define the words substitution and permutation, as well as their roles in DES
A: Introduction Data Encryption Standard (DES) The standard is defined as the symmetric-key block…
Q: ointers or references, how should a programme call the same virtual function in different forms and…
A: Structural: Structural forms, otherwise called structural frameworks, are the instruments that…
Q: Why is a stack utilised in Pushdown Automata?
A: Intro Stacks: A stack is a collection of items or components in a linear data structure format. All…
Q: The following code initializes entire array to zeros int n[10][5] = {0}; %3D Select one: True O…
A: Array Initialization: A comma-separated set of constant expressions enclosed in braces () is an…
Q: When we say that requirements should be specific and logical, what exactly do we mean?
A: Introduction: A useful requirements document will always include a development plan that includes…
Q: Consider the following C program. # include int main() { char s3; float s2; int s1; scanf("%d %f…
A: Explore and analyze the given options such as “5 H 1.2”, “H”, and “1.2” and check whether they are…
Q: The usage of mobile phones in the workplace is a hot-button issue for many firms.
A: It Is very obvious that you know What The Mobile Phone is but let just go into it to understand it…
Q: What does it mean when we talk about "system security"
A: Introduction A system's security is a critical duty. It is a technique for protecting the…
Q: Choose six consumer products that are likely to be regulated by safety-critical software systems.
A: Six consumer products that are likely to be controlled by safety-critical software systems are:
Q: Predict the return type of the below method. public static _______ calculate(int a , double b) {…
A: The options “int”, “float”, and “boolean”, are not the correct answers as the given method doesn’t…
Q: What is the stability of the BIOS?
A: Intro Generally speaking, you shouldn't have to update your BIOS very frequently. Installing (or…
Q: What are the vulnerabilities of wireless networks?
A: The basic definition of Wireless network is the computer network that are not connected by the use…
Q: In terms of cyber assaults, there are several subtypes. Is it possible to be secure when using the…
A: The employment of cyber-attack protection systems, networks, programmers, devices and data…
Q: Using wireless solutions has both benefits and cons. The network should include at least two…
A: Introduction: This is a high-speed option for sharing information over short periods of time or for…
Q: What precautions can a company take to prevent being hacked or infected with a virus?
A: Answer to the given question To get your organization's touchy information and safeguard your…
Q: To what Big-O set will this algorithm belong to? In other words, what is the complexity of this…
A: Time complexity of the program is the total time required by the program to complete it's execution.…
Q: Several rewriting and editing methods were discussed in this lecture. Which editing function do you…
A: Editors' and reviser's : Writing requires revising and editing. After editing, take a second look at…
Q: In what ways does "short stroking" effect SSD prices per gigabyte?
A: Answer
Q: How do you know if your variable should be declared as an enum type or another data type? Give…
A: The solution to the given question is: When declaring a variable as enum type , you must use the…
Q: What is an infinite recursion? What is the definition of a direct recursion? What is the definition…
A: Introduction: It will continue to make repeated calls until the recurrence reaches the default…
Q: Identity theft is a common kind of cybercrime, and it's becoming more common. How can identity…
A: institution: An identity thief may get your personal information in a variety of ways, like…
Q: What is the purpose of dynamic binding in object-oriented programming?
A: Answer. Dynamic binding allows delaying the decision of running the program. Dynamic binding is used…
Q: Explain the many forms of data protection in MS-Excel. Please give instances.
A: Intro MS-Excel provides the following protection types to safeguard data: At the file level, there…
Q: Explain sensor cloud general and protocol architecture in context of block chain loT application.…
A: Definitions A sensor is a gadget which recognizes or quantifies some handy property and data.…
Q: . Consider the following tree: к м R Write down the sequences for: Pre-order, in-order and…
A: 7. Preorder :- • scan the root first • then left subtree •at last right subtree So, Preorder…
Q: 1.1- List out all the default locales using getAvailableLocale() method. 1.2- Count how many of…
A: No Language is specified in question statement So we will be writing our solution in JAVA. We will…
Q: What is the CDC of cybersecurity ?
A: Cybersecurity: It is the use of technology, processes, and policies to prevent cyber assaults on…
Q: Draw use case diagram for online food ordering system?
A: The complete solution is given below:-
Q: computer science Discuss dissimilarities in the two methods for storing archived data in the…
A: Introduction: Discuss dissimilarities in the two methods for storing archived data in the…
Q: What exactly do you mean when you say "stress testing"? Suggestions for stress-testing the Mentcare…
A: In this problem, we will discuss Stress testing and how to stress test Medicare system.
Q: There are four separate forms of Nmap port scanning, so how does the three-way handshake fit in? Is…
A: Solution: A network map was created to help the Network Administrator understand the network that he…
Q: Consider the following C program line of code and identify the function of the code. scanf(“%6s”,…
A: Explore and analyze the given options such as “Read the string with a minimum of six characters”,…
Q: effects of cybercrime and the methods used to perpetrate it What can you do to prevent yourself from…
A: Cybercrime: Cybercrime is a crime committed using a computer and a network. It's possible that the…
Q: What distinguishes an interrupt service routine from a regular subroutine?
A: Introduction: The main distinction is that you know where the subroutine is executed. A subroutine…
Q: What exactly is an open environment?
A: Open environment : An open environment is a system that allows for the free flow of information and…
Q: What is the purpose of authentication? Compare and contrast the benefits and drawbacks of various…
A: Purpose of authentication: Authentication is used by a server to determine who is accessing their…
![A partial definition of the Account class is shown below. Select the best option to fill in the blank.
public class Account {
private double balance;
private String name;
//rest of class not shown
//assume that all class variables have been initialized
//return first initial of the name variable
public char getInitial(){return|
];}
Select one
amazon
B.
w
Word
Topic ..
Die.ja](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2Fc8db0c58-8b17-40ce-ad80-341585b72407%2F8e82ea64-1fe1-4ca5-a1fc-6fa211ff6255%2F0uh8tr_processed.jpeg&w=3840&q=75)
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Complete the Car class below so that it inherits from the given Vehicle class. Cars lose value over time. In this example, you should assume that the value is reduced by 25 cents per mile driven, until it reaches zero. Do not add any instance variables to the Car class. /** Represents a car.*/public class Car // TODO: Inherit from Vehicle{ // Do NOT add any instance variables public Car(double purchasePrice) { // TODO: Complete } // TODO: Override the getValue method}using jave: Create the a Person class with the following: Class Variables:String firstname String lastname int birthmonth int birthday int birthyear String ssn (All variables above should be private) Constructor The main constructor should take in all values and assign them to their respective private class variables MethodsCreate a public getters and setters for firstname and lastname and SSN getFirstname getLastname setFirstname setLastname Create a public getter method called getBirthdate, which will return a String composed of their birthday in month/day/year format. For example, if birthmonth=3, birthday=22, birthyear=2000, it should return the String "3/22/2000" Create a public method called verifySSN that takes in a String parameter and returns a boolean. It will check the parameter against the person's SSN and return true or false based on whether they match.The BankAccount class described below is used to represent a personal savings account with a yearly interest rate, (represented as a percentage, e.g., a 7% rate is represented by .07). The interest is applied monthly, (i.e., at the end of each month 1/12 of the interest is deposited into the account). public class BankAccount { public BankAccount(double rate) public BankAccount(double initBal, double rate) public double getBalance() public double getIntRate() public void setIntRate(double rate) public void deposit(double amount) public void withdraw(double amount) public void addMonthsInterest() private double balance; private double intRate; } Suppose a bank offers to its special customers a new type of savings account, called a “Credit Account”, that allows the customer to withdraw extra money if needed, so that the account balance is allowed to be negative at some times. These accounts award interest at the end of every month, as long as the balance is positive. If the…
- Define the classbankAccountto store a bank customer’s account number and balance. Suppose that account number is of type int, and balance is of type double. Your class should, at least, provide the following operations: set the account number, retrieve the account number, retrieve the balance, deposit,and withdraw money, and print account information. Add appropriate constructors. b.Every bank offers a checking account. Derive the class checkingAccountfrom the classbankAccount(designed in parta). This classinherits members to store the account number and the balance from the base class. A customer with a checking account typically receives interest, maintains a minimum balance, and pays service charges if the balance falls below the minimum balance. Add member variables to store this additional information. In addition to the operations inherited from the base class, this class should provide the following operations: set interest rate, retrieve interest rate, set minimum balance,…Look at the following partial class definition, and then respond to the questions that follow it: public class Student { private String Name; private String ID; private String Email; } a. Write a constructor for this class. The constructor should accept an argument for each of the fields. b. Write a ‘sendEmail” method, that takes one argument of character type called Grade. This method should print output to screen as below replacing the variable with actual values: Dear ‘Name’, You have received grade ‘Grade’. This email is being sent to your email address at “Email”In this exercise, you have to calculate the student's total marks using the concept of Classes Problem Statement# Write a Java class called Student with ● private fields: ○ name(String type) ○ mark1 and mark2 (double type) And methods: ● getMarks(int markNumber), a method which should return mark1 if markNumber equals 1 and mark2 otherwise. ● calcTotal() method should take the two marks entered and return their sum. Also define two constructors: ● A default constructor that takes no parameters and initializes the values to zeros and null. ● A constructor that takes the three variables and sets them as the values of the appropriate fields. Input# Name of the student and the marks obtained in the first and second tests Output# Sum of both marks Sample Input# Student student = new Student("Jack", 60, 70); Sample Output# getMarks(1) => 60 getMarks(2) => 70 calcTotal() => 130.0 Part of solution class Student { // Define private fields here public Student() { // Write…
- In the board game Scrabble, each tile contains a letter, which is used to spell words in rows and columns, and a score, which is used to determine the value of words. The point of this exercise is to practice the mechanical part of creating a new class definition: Write a definition for a class named Tile that represents Scrabble tiles. The instance variables should be a character named "letter" and an integer named "value". Write a constructor that takes parameters named letter and value, and initializes the instance variables. Create getters for both of the attributes. (No setters, so that a Tile is immutable.) Implement the .toString() and .equals methods for a Tile. Your completed Tile class should work with this Main program (Links to an external site.) so that it produces sample output like shown at the end of the program. You can Fork the program to make your own version in Replit, where you can add your Tile.java, or you can copy the program to your own Java development…Suppose you have defined a class such as the following for use in a program:public class YourClass{private int information;private char moreInformation;public YourClass(int newInfo, char moreNewInfo){<Details not shown.>}public YourClass(){H1. Q2 Create a class Account class with balance as a data member. Create two constructors (no argument, and two arguments) and methods to withdraw and deposit balance. Subject: OOP in JAVA Please give typed answer
- In the board game Scrabble, each tile contains a letter, which is used to spell words in rows and columns, and a score, which is used to determine the value of words. The point of this exercise is to practice the mechanical part of creating a new class definition: Write a definition for a class named Tile that represents Scrabble tiles. The instance variables should be a character named "letter" and an integer named "value".CLASS AND OBJECT WRITE! 1.) Write the main class of the given class Animal below that set the number of legs to “4” and display (get) the number of legs. class Animal { private int numberOfLegs; public void setNumberOfLegs(int numberOfLegs) { this.numberOfLegs = numberOfLegs; } public int getNumberOfLegs() { return numberOfLegs; } }Create two public classes: Mammal and Bird. Each should inherit from the Animal class shown below. For each new class, override the giveBirth method to produce the following output: For the Mammal class, the method should return: "I give live birth" For the Bird class, the method should return "I lay eggs" class Animal: """This is an animal""" def giveBirth(self): """Return the birthing method""" return "I don't know how"

