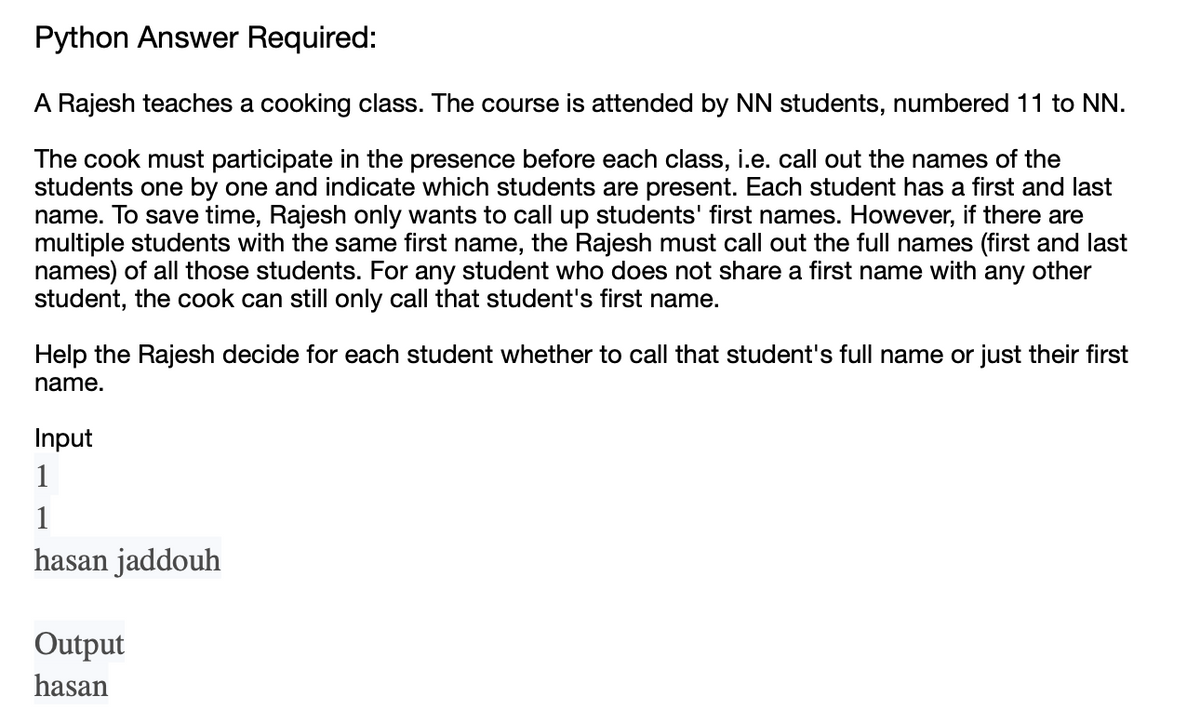
A Rajesh teaches a cooking class. The course is attended by NN students, numbered 11 to NN. The cook must participate in the presence before each class, i.e. call out the names of the students one by one and indicate which students are present. Each student has a first and last name. To save time, Rajesh only wants to call up students' first names. However, if there are multiple students with the same first name, the Rajesh must call out the full names (first and last names) of all those students. For any student who does not share a first name with any other student, the cook can still only call that student's first name. Help the Rajesh decide for each student whether to call that student's full name or just their first name.
A Rajesh teaches a cooking class. The course is attended by NN students, numbered 11 to NN. The cook must participate in the presence before each class, i.e. call out the names of the students one by one and indicate which students are present. Each student has a first and last name. To save time, Rajesh only wants to call up students' first names. However, if there are multiple students with the same first name, the Rajesh must call out the full names (first and last names) of all those students. For any student who does not share a first name with any other student, the cook can still only call that student's first name. Help the Rajesh decide for each student whether to call that student's full name or just their first name.
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter8: Arrays And Strings
Section: Chapter Questions
Problem 21PE
Related questions
Question
Transcribed Image Text:Python Answer Required:
A Rajesh teaches a cooking class. The course is attended by NN students, numbered 11 to NN.
The cook must participate in the presence before each class, i.e. call out the names of the
students one by one and indicate which students are present. Each student has a first and last
name. To save time, Rajesh only wants to call up students' first names. However, if there are
multiple students with the same first name, the Rajesh must call out the full names (first and last
names) of all those students. For any student who does not share a first name with any other
student, the cook can still only call that student's first name.
Help the Rajesh decide for each student whether to call that student's full name or just their first
name.
Input
1
1
hasan jaddouh
Output
hasan
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning