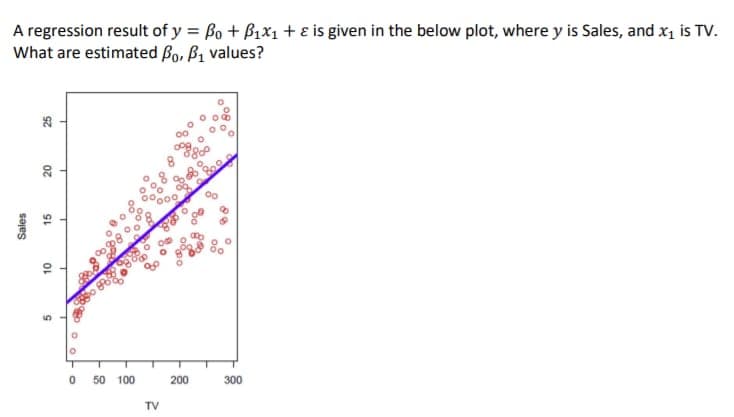
A regression result of y = Bo + B1x1 + ɛ is given in the below plot, where y is Sales, and x, is TV. What are estimated Bo, ß1 values? 0 50 100 200 300 TV Sales 15
Q: ating systems.
A: In processing, a firewall is a network security framework that screens and controls approaching and…
Q: When surfing online, you get some strange data on an apparently secure website, and you realize you…
A: Introduction: A website is a collection of web pages, and related material recognized by a common…
Q: "Rabenstein code was used to send a message with 4 information bits, you receive 100110001
A: The answer is
Q: write a java program to print the mirror image of right angled in x-direction after taking number of…
A: Required:- Write a Java program to print the mirror image of right-angled in x-direction after…
Q: In Sum-of-Products (SOP) form, basic combinational circuits can be directly implemented with None of…
A: Logic Gate: A logic gate is a computation model or physical device that implements a Boolean…
Q: For an intrusion detection system, false positives and false negatives are the worst possible…
A: An Intrusion Detection System (IDS) is a network security device that was designed to detect…
Q: What will be the Inorder traversal of the following tree?* 11, 20, 29, 32, 41, 50, 65, 72,…
A: The answer of the question is given below.
Q: Describe the many search engines and strategies used to narrow down the results returned by a search…
A: So, Describe the tools and tactics used to refine search results. Unstructured key phrases used to…
Q: What is the difference between a fat client and a thin client?
A: A common thin client definition: A thin client is a computer that runs on resources stored on a…
Q: The word "API" refers to a programming interface for applications. What does this mean in terms of…
A: API is a representation of hardware components on the software level, which is generated from a…
Q: Describe the clocking methodology.
A: Please find the detailed explanation and details in the following steps.
Q: When it comes to network and cyber security, what role does intrusion detection and prevention play?
A: An intrusion detection and prevention system (IDPS) scans a network for potential threats and…
Q: Section 2: Program Design 2 Write a C++ program that calculate the area of a circle. • Circle area's…
A: Language is one of the most widely used programming language which has been used to create different…
Q: Create a 1-bit adder circuit. It has three 1-bit inputs: a, b, and carry_in, and two 1-but outputs:…
A: The specifications given for building a 1 bit adder circuit is : It has three 1-bit inputs: a, b,…
Q: What improves the effectiveness of intrusion detection?
A: Intrusion Detection: A network intrusion prevention system (IPS) analyses network traffic patterns…
Q: What kind of worries and challenges arise from the use of an unintegrated information system?
A: Introduction: Computer failure and loss are key issues resulting in unnecessarily high costs and…
Q: re the barriers to m-comme
A: The term mobile commerce was initially instituted in 1997 by Kevin Duffey at the send off of the…
Q: What does the word relAtionAl dAtA MOdel mean?
A: Model of Relational Data: The "collection of relations" in a database is referred to as the…
Q: orta
A: Here we want to tell that is all there is to it necessary for an IT professional to have a…
Q: in javafx This will be a simple drawing program. A Line, a Circle, and a Rectangle. You will need…
A: The Program is implemented below and also the line circle and rectangle code is implemented below:
Q: A number 428 in duodenary (base 12) is to be added to C10 in tredinary (base 13). The sum will from…
A: The answer is
Q: Defintion of "intrusion prevention system" is not provided.
A: Start: The phrase "network security" may refer to various technologies, equipment, and operational…
Q: In configuration management, system building is... a. is the process of creating a complete,…
A: The principles, techniques, and tools for managing evolving software systems are referred to as…
Q: As a computer maker, you confront the difficulty of creating high-quality computers with fast…
A: Computers: A computer stores and processes data. For example, most computers employ a binary system…
Q: What is Onion network?
A: Answer is given below:
Q: 1. If the above list was sorted using Selection sort, which two elements would be swapped first? 2…
A: As per guidelines I can answer only first question. I hope you will understand. Thank You. Given…
Q: does UDP fit?
A: The Open Systems Interconnection model (OSI model) is a theoretical model that portrays the all…
Q: Following the development and testing of individual software modules, they must be combined and…
A: Introduction: Software development refers to computer programming, which is the process of writing…
Q: at are some of the characteristics of O
A: Below are some of the characteristics of OOP
Q: USE PYTHON PROGRAMMING. The expected output per respective input must be achieved (check…
A: The python code is implemented below:
Q: Multithreading techniques on different operating systems (Linux, Windows, Mac, Android, etc.) are…
A: CPU Scheduling: CPU Scheduling determines which process gets the CPU while another is waiting. CPU…
Q: Write a button-click method to retrieve the value from an EditText and send it to another activity…
A: The complete code is given below along with output screenshots. MainActivity XML and JAVA is given…
Q: How crucial is software development? Four more characteristics, in your opinion, should be…
A: Introduction: Software development's ability to create and provide value to its users cannot be…
Q: Consider a system with 80% hit ratio, 50 nano- seconds time to search the associative registers ,…
A: Here in the above problem given hit ratio=80% Time to search associative registers =50ns Time to…
Q: ection softw
A: An intrusion detection system (IDS; also intrusion counteraction system or IPS) is a gadget or…
Q: Identify at least three contemporary tools for building digital logic circuits. Examine five major…
A: Digital logic: Electronic circuit board design is driven by digital logic, which is the underlying…
Q: Defintion of "intrusion prevention system" is not provided.
A: Intrusion Prevention System: An intrusion prevention system (IPS) is a network security instrument…
Q: What is an IDS and how does it work?
A: An Intrusion Detection System (IDS) is a piece of hardware and software that identifies and…
Q: omputer Science Perl Questions Explain what this code is doing: “if(/[a-z]/) { print; } else {…
A: Answer:
Q: What is the physical address of this struction Source operand of MOV BL, [SI +
A: The answer is
Q: dAtA MOdel me
A: The relational model (RM) for database management is an approach to managing data utilizing a…
Q: sheet that shows all the floating-point numbers for the 9-bit floating point numbers with one sign…
A: Below a spreadsheet that shows all the floating-point numbers for the 9-bit floating point numbers…
Q: The nodes represent places and number represent the distance between two places in miles. If you…
A: In the following step, the shortest distance travelled from E to a has been calculated and showed,…
Q: ection system, an
A: An intrusion detection system is a screen just application intended to distinguish and give an…
Q: Please write the following in very simple C++ code: Write a function that calculates the average of…
A: In the above question, the average needs to find out: average=sum of numbers/total numbers; Below is…
Q: Intrusion detection software is referred to as IDS.
A: Intrusion Detection Software: Intrusion detection software may monitor network traffic for…
Q: (W
A: IntroductionSoftware requirements or specifications are understanding and defining what services are…
Q: What is mean by digital envelope.Explain its working.
A: To be determine: Describe about digital envelope
Q: List and discuss four vulnerability intelligence sources. Which seems to be the most efficient? Why?
A: Given: 1. Vendors as the first step2. Organizations affiliated with CERT 3. Access to public…
Q: How can forensic investigators extract volatile and non-volatile data from PCs running Windows?
A: According to the question both are used for makes secure the data at the organization in which they…
Step by step
Solved in 2 steps with 2 images

- Consider the regression model CEOSAL = 2.5 + 0.5 * sales – 0.1 * sales 2Note that salesl 2 = sales*sales. What is the effect of an increase from 1 to 2 in sales on CEOSAL?The table below shows the prediction results from Logistic Regression, which gives results in the range 0 − 1, find the TP, TN, FP, FN, TPR, and FPR for each threshold from 0.1 to 0.9The following data give the starting salary for students who recently graduated from a local university and accepted jobs soon after graduation. The starting salary, grade-point average (GPA), and major (business or other) are provided. SALARY $29,500 $46,000 $39,800 $36,500 GPA 3.1 3.5 3.8 2.9 Major Other Business Business Other SALARY $42,000 $31,500 $36,200 GPA 3.4 2.1 2.5 Major Business Other Business Using a computer, develop a regression model that could be used to predict a starting salary based on GPA and major. Use this model to predict the starting salary for a business major with a GPA of 3.0. What does the model say about the starting salary for a business major compared to a non-business major? Do you believe this model is useful in predicting the starting salary? Justify your answer, using the information provided in the computer output.
- Python Regression Model 1: train MSE = 0.423, test MSE = 0.978 Model 2: train MSE = 0.572, test MSE = 0.644 Model 3: train MSE = 0.218, test MSE = 1.103 Based on this information, which of these models generalises the best to unseen data?In bivariate regression, the regression coefficient will be equal to rXY when:Make a time series analysis about the data in table below. Make 2 or more regression models by using stata!
- Q3: Train a regression model based on the first 200 rows. What is reg.intercept_ value ?The difference between Linear Regression and Logistic Regression. Note: Please make in table and with your own wordTo see how accurate your trend line is, right click the line and select Describe Trend Line. Tableau will show you the regression equation and the p-value for its overall significance. Group of answer choices True False
- When and why do we employ the Binomial, Poisson, and Proportional models of regression?When and why do we use the Proportional, Binomial, and Poisson regression modelsHow and why do each of these models include degrees of freedom?We want to train a binary Logistic Regression classifier for the given trainingdataset:

