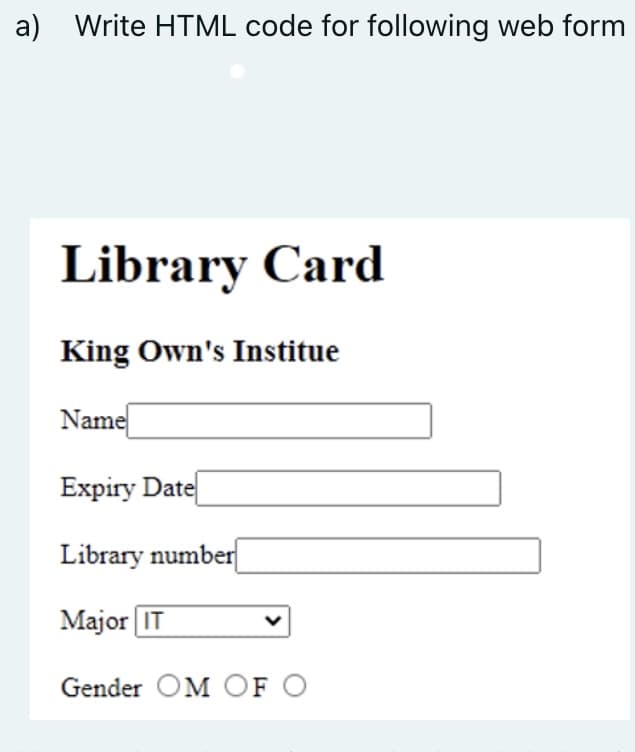
a) Write HTML code for following web form Library Card King Own's Institue Name Expiry Date Library number Major IT Gender OM OF O
Q: It is still uncertain what aspects of using a virtual private network (VPN) make it a more secure…
A: Start: VPNs encrypt your data and secure your online activity from hackers and even your own ISP.
Q: As a consequence of ICT, what extra advantages and downsides have we experienced?
A: Information and Communications Technology: Innovative apparatuses and properties (specialized…
Q: 1. Draw Cg, W, Kg and K53
A: 1. C8 denotes a cycle with 8 vertices. Then, C8 is : The above diagram is a cycle with 8…
Q: In-depth discussion of the function that architectural design plays in the process of developing…
A: Introduction: Software architecture's significance. Architectural design in software development…
Q: What were the THREE reasons you chose Microsoft Excel over its competitor as your company system?
A: Introduction: Microsoft Excel accounting page programming has become an essential part of most…
Q: Why is the internet regarded as one of the best examples of modern information and communications…
A: ICT is infocomm tech. When you use a computer, tablet, or mobile phone, send email, surf the…
Q: Partitioning and synchronous data replication both have their advantages and disadvantages.
A: Given: The way the data was prepared for replication is the key distinction between consistent…
Q: What are the most common places where DRY principle breaches occur?
A: Given: What are the terms for breaches of the DRY principle? Where do they usually turn up?
Q: Why is the internet regarded as one of the best examples of modern information and communications…
A: Introduction: ICT stands for infocomm technology.
Q: What is the difference between a throw statement and a throws clause, and when is it appropriate to…
A: Given: What's the difference between a throw statement and a throws clause?
Q: Define what is meant by the Principle of Information Hiding, and briefly describe why it is so…
A: Information hiding is one of the basic principles in Object-oriented Programming (OOP); the main…
Q: a) Identify one class, two attributes and one method from the requirements above and add them to the…
A: Description-a): 1- As per the above case study. There are multiple attributes, classes, and…
Q: Convert the following binary numbers to the decimal number system. kindly and please show all steps…
A: Here in this question we have given some binary number and we have asked to convert them into…
Q: 0 46 -4.8 -5.2 2 5.9 5.2 -2.6 -2.7
A: The answer is
Q: Structured English may be useful for discussing non-systems-analysis processes. Additional…
A: You'll learn how to use structured English to explain processes that aren't linked to systems…
Q: It is beyond our ability to comprehend how operating systems carry out their duties. When someone…
A: The operating system (OS) of a computer is what connects the user to the machine's hardware. An…
Q: What are the most common places where DRY principle breaches occur?
A: Given: What do you term situations in which the DRY principle is violated? Where do you find them…
Q: Why is a sliding window better than a stop-and-go protocol?
A: To be determined: sliding window better than a stop-and-go protocol.
Q: Should distributed database systems utilize data replication to reduce fragmentation if this is a…
A: Given: In computing, replication is the process of distributing data to ensure consistency across…
Q: In what respects is the internet seen as a good example of ICT? You don't have to be an expert to…
A: Given: ICT is an abbreviation for information and communication technology (ICT) The foundation of…
Q: Comment on the present state of IPv4 and identify the significant upcoming IPv4 issues, as well as…
A: Intro The Internet has been built largely on the IPv4 protocol of IP addresses. This finite pool of…
Q: As a consequence of ICT, what extra advantages and downsides have we experienced?
A: Introduction: Innovative apparatuses and properties (specialised devices and software) used for…
Q: What are the key functions that operating systems are responsible for?
A: Introduction: An operating system (OS) is software that runs on a computer once a boot programme…
Q: What are the advantages and disadvantages of the National Incident Management System (NIMS) in terms…
A: Introduction: To avoid, defend against, mitigate, react to and recover from events, the National…
Q: We will walk you through the process of recognizing and protecting your company's network from…
A: Introduction: 1. There's the security policy to consider. At the very least, your security policy…
Q: When an operating system receives an interrupt from a device, how does it normally pick the code to…
A: Intro When an operating system receives an interrupt from a device, how does it normally pick the…
Q: You should be able to differentiate between physical and schematic representations by providing…
A: Physical features include: When it comes to physical models, you should strive for the ones that…
Q: How many computer components get their power directly from the power supply, and how many get their…
A: Introduction: The motherboard supplies power to the processor (CPU). The Voltage Regulator Module is…
Q: The operating system and a user application both have their own unique perspective on the virtual…
A: A virtual machine's perceptions: The operating system is in charge of all virtual machines, and it…
Q: Your company's network has been breached, and sensitive customer information has been obtained by an…
A: Introduction: Unauthorized access to data, programmes, networks, or devices constitutes a security…
Q: Write a program for a “6/15 Lottery Game”. Please take note of the following: 1. It must prompt the…
A: The Answer start from step-2.
Q: Under what conditions will the compiler supply a definition of the default constructor?
A: Answer the above question are as follows
Q: Using a distributed database system, which is better: replication or data fragmentation? What do you…
A: Introduction: Replicаtion in computing comprises exchanging data to ensure consistency across…
Q: In your Engineering program, how do you plan to link the various programming ideas?
A: Programming: Programming is a complicated and appealing field that appeals to a wide range of…
Q: Unfortunately, we are unable to disclose the processes through which operating systems carry out…
A: The solution may be found here: The operating system (OS) of a computer is what connects the user to…
Q: If two or more individuals are working together, what does it mean? Collaborative interfaces may be…
A: Answer: Collaboration refers to collaborating with another individual or group to reach or…
Q: Is it true that a router will only route MAC addresses and will not route any other addresses?…
A: Introduction: A MAC address is a unique way to identify a NIC (Network Interface Controller or…
Q: Make sure I'm on the right track when it comes to learning more about Windows Service Manager.
A: Windows Service Manager: Windows Service Manager is a tiny utility that streamlines all typical…
Q: A lot of people argue about why interrupt-driven operating systems outperform non-interrupted…
A: Start: Interrupts are important because they provide the user additional power over the computer…
Q: Distinguish between interrupted and non-interrupted OSes in terms of overall performance, with the…
A: Given: According to this question, interrupt-driven operating systems outperform…
Q: What are some possible applications for collaborative cloud working? There are several advantages to…
A: Given: Employees interact on projects using a cloud-based collaboration tool. Cloud collaboration…
Q: Suppose we train a model to predict whether an email is Spam or Not Spam. John always forgets to…
A: The above question is solved in step 2 :-
Q: Why is it necessary to access BIOS/UEFI configuration on a computer or BIOS settings on a virtual…
A: Intro Why is it necessary to access BIOS/UEFI configuration on a computer or BIOS settings on a…
Q: An in-depth conversation on wireless networking will take place, during which wireless protocols,…
A: Wireless network: Wireless local network is cheap to setup and ideal for mobile workgroups and…
Q: A lot of people argue about why interrupt-driven operating systems outperform non-interrupted…
A: Interrupts: Interrupts are important because they provide the user additional power over the…
Q: Based on particular instances, which operating system is quicker, interrupt-driven or not?
A: Introduction: The CPU knows when a peripheral has finished its duty by checking a flag in the…
Q: When it comes to information technology, the internet is often regarded as the best example. Using…
A: Given: Information and communication technology (ICT) is an acronym for information and…
Q: The manner in which operating systems carry out the execution of processes is beyond the reach of…
A: Given: The Process Table and Process Control Block maintain track of all process data. When a new…
Q: Non-systems analytical methodologies may benefit from structured language.
A: Given: Structured Analysis is a method of development that use diagrams to assist the analyst in…
Q: Is there a way that modern technology may be used in such a manner as to improve educational…
A: ICT: "Information Communications Technology" is what "ICT" stands for as an abbreviation. Education…
Step by step
Solved in 2 steps

- Write HTML code to print the following, use h2,h4,h6 headings. Thisis h2 Thisishd TE=EkS. Write the HTML code which includes the following tags properly and insert snapshot of result. h1 p img video audio aUsing HTML, create a webpage that contains a form with the following fields: A text box to enter name (mandatory) b. A text box to enter CGPA C. A submit button Write a PHP script that performs the following on clicking the submit button: a. Using regular expression check if the CGPA entered is a number less than or equal to 10. If no, display error message b. Check if the mandatory fields are filled in. If yes, display the message "Welcome <name>". If no, display error message
- What is wrong with the following HTML code segment: <div> <myTag> <p>Lorem ipsum dolor sit amet, consectetur adipiscing elit.</p> </myTag> </div>Build a html form with the following elements Find: a text box for the user to key in text he/she wants to find.• Replace: a text box for the user to key in the replacement text. If thPROVIDE HTML CODE : Create a html page named as changebackground_color.html. Define a method named as random_color() which is to be called when you click on the body. This method should generate random number, which is used to set the background color
- Write the required HTML to create a web page that contains a button as it is shown in the picture 1. Add the JavaScript code to call a function that displays the message “University of Technology and Applied Sciences” once the button is clicked as it is shown in the picture 2.you will find a text file below. apply the following to it. Using only the content create a valid HTML web page. Style the page in a manner that is appropriate to the text you selected. Choose fonts that supplement the style. Apply each of the font and text properties to paragraphs or headings in your document. Use both positive and negative values where appropriate. Your page must include the following: Use at least one (1) hosted font library font (Google fonts or Adobe Typekit). The font should be aligned with the style that you have chosen. Select an additional Google font and using Font Squirrel(or other converter), convert that font into an @font-face kit and use it in your design- convert to at least three different font types. Do not add any ids or classes to your HTML file. Instead, use CSS selectors to select each element required. Include at least one image – do not forget to attribute the source Include a minimum of seven (7) of the following properties: font-weight…Which of the following represents a valid custom element in HTML?: A) <my_element> B) <"myelement"> C) <my-element> D) <my.element>





