According to the following code; you are required to draw the flowchart in details with clear sequences
According to the following code; you are required to draw the flowchart in details with clear sequences
Chapter5: Looping
Section: Chapter Questions
Problem 13E
Related questions
Question
According to the following code; you are required to draw the flowchart in details with clear sequences
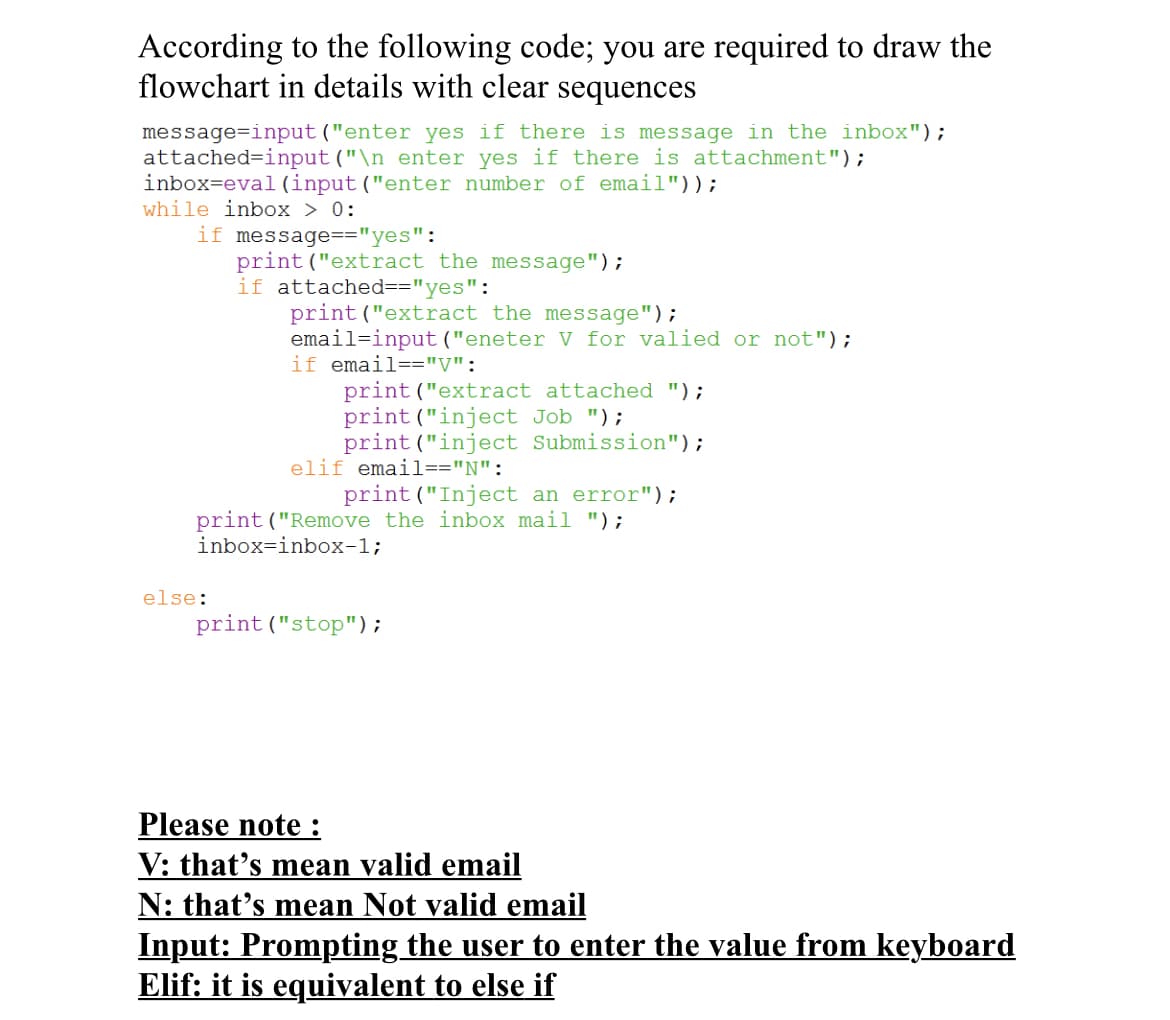
Transcribed Image Text:According to the following code; you are required to draw the
flowchart in details with clear sequences
message=input ("enter yes if there is message in the inbox");
attached=input ("\n enter yes if there is attachment");
inbox=eval (input("enter number of email"));
while inbox > 0:
if message=="yes":
print ("extract the message");
if attached=="yes":
print("extract the message");
email=input ("eneter V for valied or not");
if email=="V":
print("extract attached ");
print ("inject Job ");
print ("inject Submission");
elif email=="N":
print ("Inject an error");
print("Remove the inbox mail ");
inbox=inbox-1;
else:
print ("stop");
Please note:
V: that's mean valid email
N: that's mean Not valid email
Input: Prompting the user to enter the value from keyboard
Elif: it is equivalent to else if
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,