The final result of "records.txt" file will look something like this (depending on the number of students and their courses): Nina Math 1 3 93 Physics 1 3 75.5 Geology 2 80 Sarah Geology 2 90
The final result of "records.txt" file will look something like this (depending on the number of students and their courses): Nina Math 1 3 93 Physics 1 3 75.5 Geology 2 80 Sarah Geology 2 90
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter7: File Handling And Applications
Section: Chapter Questions
Problem 9RQ
Related questions
Question
this code should be in python:
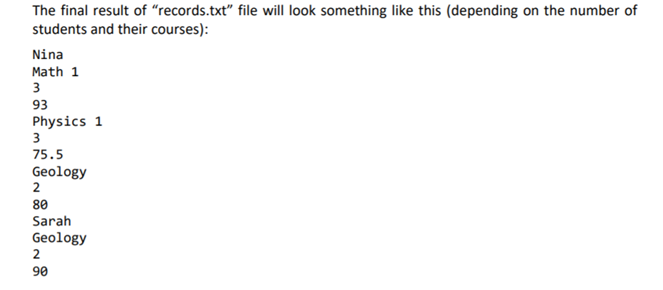
Transcribed Image Text:The final result of "records.txt" file will look something like this (depending on the number of
students and their courses):
Nina
Math 1
3
93
Physics 1
3
75.5
Geology
2
80
Sarah
Geology
90
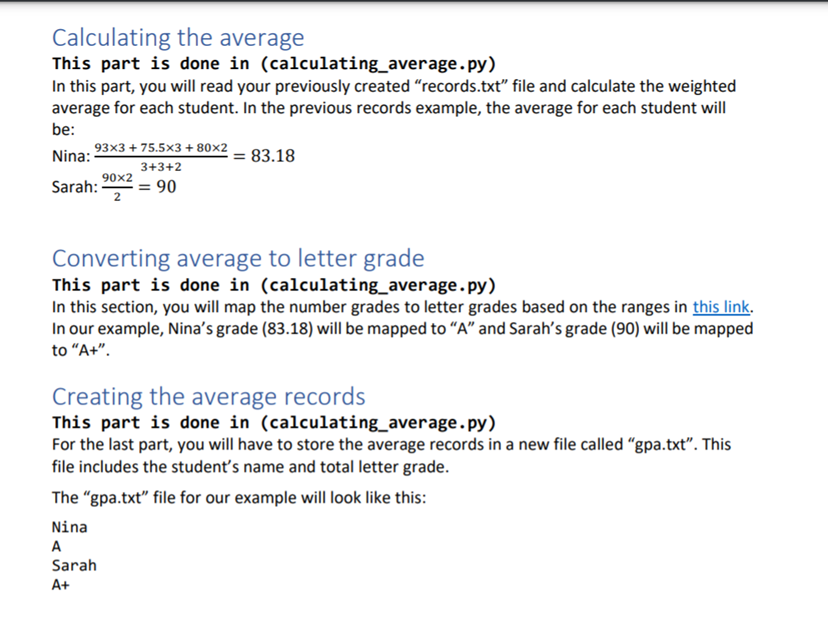
Transcribed Image Text:Calculating the average
This part is done in (calculating_average. py)
In this part, you will read your previously created "records.txt" file and calculate the weighted
average for each student. In the previous records example, the average for each student will
be:
93x3 + 75.5x3 + 80×2
Nina:
= 83.18
3+3+2
90x2
Sarah:
2
= 90
Converting average to letter grade
This part is done in (calculating_average.py)
In this section, you will map the number grades to letter grades based on the ranges in this link.
In our example, Nina's grade (83.18) will be mapped to "A" and Sarah's grade (90) will be mapped
to "A+".
Creating the average records
This part is done in (calculating_average.py)
For the last part, you will have to store the average records in a new file called "gpa.txt". This
file includes the student's name and total letter grade.
The "gpa.txt" file for our example will look like this:
Nina
A
Sarah
A+
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 8 steps with 4 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

A Guide to SQL
Computer Science
ISBN:
9781111527273
Author:
Philip J. Pratt
Publisher:
Course Technology Ptr

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

A Guide to SQL
Computer Science
ISBN:
9781111527273
Author:
Philip J. Pratt
Publisher:
Course Technology Ptr

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage