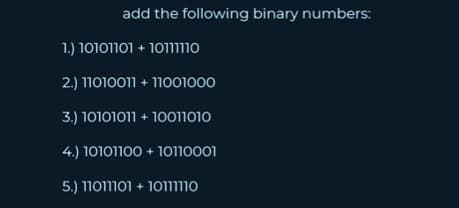
add the following binary numbers: 1.) 1010110110111 2.) 11010011 +11001000 3.) 10101011 +10011010 4.) 10101100 + 10110001 5.) 11011101 +101111
Q: Difference between Numeric notation and symbolic notation.
A: Introduction Notation: A set of written symbols used to represent something, such as music or…
Q: Look at the attached graph. If the graph, doesn't come up correctly, I have it on GitHub. Github…
A: Answer the above question are as follows
Q: Use a while loop to repeatedly take input from the user and print whatever they type in. When the…
A: Introduction While Loop: The while loop in Python is used to execute a piece of code until a…
Q: As the new DirectTocust IT risk manager, how will you ensure that the company's network and physical…
A: What follows is, in fact, the solution: A good IT security strategy safeguards both internal company…
Q: a given file can only be opened once per program-- you cannot close it and open again until after…
A: Introduction: This a great question with a complicated set of responses. There are two fundamental…
Q: Write the code necessary (no more than 4 lines) to insert node 99 into the following link at the…
A: The given below program is in C language.
Q: Insert the following into a red-black tree. I do not need the code. Just a step by step of the…
A: A red-black tree is a self-balancing binary search tree in which each node has an extra bit, which…
Q: State the three (3) ways in which the colour schemes are used in the CSS . Explain and illustrate…
A: Introduction: Web pages are styled and laid up using CSS (Cascading Style Sheets), which may be used…
Q: What steps are needed to go back from the compressed data to YCbCr data. There is a new step needed.…
A: YCbCr is a color space used in the digital image and video processing. It is a luma-chroma color…
Q: Find out how cloud computing stacks up against mobile devices, and why. There are several ways in…
A: Mobile computing lets us access data and information on mobile devices, whereas cloud computing…
Q: Wireless networks have a poor throughput compared to wired ones.
A: A computer network refers to interconnected computing devices that can exchange data and share…
Q: What are the computer abuses or ethical violations that you can think of or can identify that is…
A: Introduction: These engaged(proactive) users are more likely to be publicly targeted since they are…
Q: Question 6 sm .True or False, BindingContext between two objects can be two-way. In that if either…
A: Various features of the XAML are listed below: Developers can prescribe the user interface by using…
Q: It's possible to tell scalar computers apart from superscale computers by comparing and contrasting…
A: Scalar processors process one piece of data concurrently. A vector processor processes many bits…
Q: The aligns the plans and operations of the information systems with the strategic goals of the…
A: The solution for Question A is given in the below step with explanation. I am rejecting Question B…
Q: Which of the following code snippets correctly traverses the contents of a linked list, from…
A: Here we need to traverse a linked list content from beginning till end. So we will need a current…
Q: For a proposition ((A -> B) ^ (B -> ~A)) -> A, determine the truth value if the proposition if A = 1…
A: A statement is a declarative sentence that is either true or false (but not both). Statements are…
Q: No daises are carnation. No daises are roses. Therefore, no carnation are roses a. Fallacy of…
A: Introduction An assertion that all or some components of one classification (the subject word) are…
Q: MATLAB PLEASE Write a general binary search code that can find a target with multiple appear- ances…
A: MATLAB which it is a proprietary multi-paradigm programming language and numeric computing…
Q: WAP c# program creates a string, s1, which deliberately leaves space for a name, much like you’d do…
A: This method takes two Integer arguments: a starting position and a count, which is the number of…
Q: To what extent does your company's network undergo preemptive vulnerability assessment?
A: Preemptive vulnerability assessment is the assessment or a process which checks for any possible…
Q: g a certain level of expertise and engagement. Examp rration and vyp bagepap Invin
A: The answer is
Q: Assignment 4 Write a Python program that will read the data in the file data_numbers.txt and add…
A: Here is the python for finding mean, median, mode, range, standard deviation:
Q: iven that (n) = 2T(n/2) +n for n >= 2, ou can assume n= 2k and T(1) = 1 ind the kth step…
A: Dear Student, The answer to your question is given below -
Q: How do IaaS and PaaS impact business continuity planning?
A: Introduction : IaaS: IaaS (Infrastructure-as-a-Service): IaaS is a type of cloud computing that…
Q: The kind of server in a two-tier architecture that serves clients data stored on disc pages is…
A: Given question is: The kind of server in a two-tier architecture that serves clients data stored on…
Q: Which pattern will match all filenames containing a "b"? [!b]* *b* *b b*
A: The pattern will match all filenames containing a "b" b*
Q: estion 13 sum . Full explain this question and text typing work only We should answer our…
A: Note: As per guidelines I am compelled to solve only one question and that is the first question.…
Q: 2-Create a class named 'Shape' with a method to print "This is This is shape". Then create two other…
A: Introduction: Base class is Shape. Derived classes Rectangle, Circle are the inherited classes of…
Q: tion has the following format: Machine Instruction: 8 Bits OpCode: 3 Bits Oper
A: Dear Student, The answer to your question is given below -
Q: 8051 Assembly Exercise: - what is the assembly for machine code below: 0xE5 0x20 0x7B 0x50 0x2B…
A: The 8051 Microcontroller Assembly Language which refers to the one it is is a combination of…
Q: A relational database for transaction processing(rather than analytical processing) should be…
A: contrast, OLTP systems are designed to process large volumes of transactional data involving…
Q: What is Robotics and Automation?
A: The answer is given below.
Q: How many different objects of type integer exist in the computer’s memory after the following code…
A: Solution: Given, How many different objects of type integer exist in the computer’s memory after…
Q: A computer uses a sixteen bit integer to store the number of days since 1 January 2001. In what year…
A: In this question, the computer uses a 16-bit integer to store number of days. We have to answer in…
Q: What are the costs and benefits of different approaches to constructing massively distributed data…
A: Building scattered data environments have trade-offs.Convenience 2) Cohesion3) data tolerance…
Q: It's impossible to determine how many nodes are in the smallest possible linked list. Is there one…
A: INTRODUCTION: When managing dynamic data items, the linked list is the most common option for a data…
Q: What is the instruction to compute: $s4=$t8-15?
A: In the MIPS assembly language, the instruction to compute the expression $s4=$t8-15 is "sub $s4,…
Q: VGA mode is used for the purpose of displaying visual information on a screen. Where do you get your…
A: VGA mode is utilised for the purpose of displaying visual output on a monitor. The very common type…
Q: In class we considered the computational complexity of global localization as a hypothesis…
A: Dear Student, The answer to your question is given below -
Q: Specify how HTTPS protects users from the wide variety of threats
A: Since the question has mentioned about the list of threats, but the list has not been given. So, we…
Q: What does the command do? What is the expected contents of the names.txt file? awk –F: '$3 ~…
A: In Unix based systems, AWK command is implemented to retrieve the data from the text files and also…
Q: 2-Create a class named 'Shape' with a method to print "This is This is shape". Then create two other…
A: We need to create class as per the requirements. Programming language used is Java.
Q: Several advantages may be gained by switching to a hierarchical database structure from a relational…
A: INTRODUCTION: A data model called a hierarchical database model has the data arranged in a tree-like…
Q: is it correct ? Write a recursive function that returns the nth number in a fibonacci sequence when…
A: Here in this question we have given a code of Fibonacci sequence and we have asked to check weather…
Q: Document databases store documents using Key/Value pair in _____ format with many levels of nesting.…
A: Introduction Document Database: A non-relational database called a document database is made to…
Q: Given the following subnet, what is the subnet mask in binary that will be used by the router to…
A: Dear Student, The answer to your question is given below -
Q: Find context-free grammars for the following languages (with n ≥ 0, m≥ 0, k > 0): (a) I-{ata (b) L=…
A: “Since you have posted a question with multiple sub parts, we will provide the solution only to the…
Q: ures and functionality of BitLocker Drive Encryption and the Encrypti
A: Introduction: Windows 2000 onward, EFS is accessible in all Windows versions with the exception of…
Q: Write a JAVA program that reads an array from input file and invokes two different methods Sort and…
A: The required JAVA code // Program.java import java.io.BufferedReader;import…
Step by step
Solved in 2 steps

- Add the following binary numbers, show your work:101101 + 111000100100 + 1100111111 + 1110110110101 + 1011011111101001 + 1101101001101 + 1101100101010011010 + 110101101Calculate the checksum for the following binary numbers. Give the result in binary. Use the 16-bit format. 11010110 10000100 00110111 10101001 01010100 10100010 01101010 11000101What are the 16-bit 1’s and 2’s complements of the following binary numbers? 01100 100111100001001
- What are the 16-bit 1’s and 2’s complements of the following binary numbers?a. 10000b. 100111100001001c. 0100111000100100What character string does the binary ASCII code1010100 1101000 1101001 1110011 0100000 1101001 11100110100000 1000101 1000001 1010011 1011001 0100001represent?⦁ Compute the checksum for the following data.01101110 11011001 11101101 00101100 11110100 01011010 01111000 11000011 11111000 00001100
- a. What decimal number is represented by the following single precisionfloat?1 0111 1100 0110 0000 0110 0000 0000 000b. What decimal number is represented by the following single precisionfloat?1 0101 1100 0110 0010 0110 0000 0000 000c. How many bits are needed to represent 57B(Hex) in binary?1. Decipher the codes 01000011, 01101000, 01100101, 01000001, 0110100, 01100101, 01010010 2. Convert binary number to decimal 111100110What is the decimal representation of each of the following signed binary numbers? 10110101 00101010 11110000
- HW1:/ convertthe following decimal number to binary number: (879)D HW2:/ convertthe following decimal number to octal number: (675)D HW3:/ convert the following decimal number to hexadecimal: (340)D HW4:/ convert the following binary number to decimal: (11010110)B HW5:/ convertthe following octal number binary: (110001111010110)B HW6:/ convertthe following binary number to Hexadecimal: (11001010010101011110)B HW7:/ convertthe following octal numberto hexadecimal: (2764)o HW8:/ convertthe following hexadecimal numberto octal: (DFE5)HNEED HELP WITH ALL STEPS BY STEPS PLEASE! THANK YOU SO MUCH. 1. Multiply Binary numbers (12 bits, 2’s complement numbers) 10101 * 111111010101 = 2. Subtract Binary numbers (12 bits, 2’s complement numbers) 11000011111 – 11000010011 =1. Convert the following binary numbers to their decimal equivalents:a. 11100.011 b. 111100 c. 10010.1011 d. 101011 2. Convert the following decimal numbers to their binary equivalents:a. 111 b. 34.75 c. 245 d. 43.9375 3. Convert the following decimal numbers to their hexadecimal equivalents:a. 255.875 b. 3000 c. 70 250 d. 304.250 4. Convert the following hexadecimal numbers to their binary equivalents:a. 1C b. 1F.C c. C67 d. 451.4 5. Convert the following binary numbers to their hexadecimal equivalents:a. 1001.1111 b. 110101.011001 c. 10100001.101001 d. 1110001.00111

