Add the following IEEE 754 single-precision floating-point numbers. (a) COD20004+ 72407020
Q: Consider the scenario in which one computer sends a packet to another computer by using the…
A: The issue at the transport layer concerns the exchange of packets between two computers. A package…
Q: What kinds of troubleshooting strategies and simple network commands have you utilized in the past…
A: The following are some troubleshooting methods for a basic network: Check whether the Wi-Fi switch…
Q: There are several disadvantages of cloud computing that are seldom highlighted.
A: Introduction: The phrase "cloud computing" refers to the process of storing and accessing data via…
Q: What are some of the numerous aspects of the process of designing software systems that need to be…
A: Software design process: SDP is a high-level, technology-neutral concept that describes a system…
Q: It should be a top priority to identify and communicate at least three best practices to companies,…
A: Computing In The Cloud: Cloud computing is the process of storing an organization's or an…
Q: What are the key differences between authenticating a distant user and authenticating a local user?…
A: What is the difference between remote and local user authentication? Which one was the most…
Q: Define the message that an SNMP trap sends.
A: Define the trap message in SNMP: At network monitoring, the Simple Network Management Protocol…
Q: The last question I have is this: what exactly is the point of artificial intelligence? I would…
A: Create the AI's goals: Academics in the past created algorithms that imitated humans' step-by-step…
Q: Suppose three algorithms A, B, and C, can be implemented to perform a task. The
A: The answer is
Q: Shrek has guessed three positive integers a, b, and c. He keeps these numbers in secret, but he…
A: import java.util.Scanner; public class Input{ protected int num1, num2, num3, num4; //declaring…
Q: What are we trying to accomplish with artificial intelligence in the end? Please provide a synopsis…
A: Artificial intelligence is everywhere in our lives today. Whether it’s our favorite Instagram…
Q: Is it prudent to delegate all technical requirements to software service providers? Why do you…
A: Start: The process of contracting external contractors for certain operations and duties is known as…
Q: Why is the internet considered to be one of the most outstanding examples of ICT? Every contention…
A: The Internet is an excellent instrument for social movements. It is perhaps the most effective…
Q: What kinds of artificial intelligence are there? Define artificial intelligence fields and provide…
A: Cognitive artificial is the simulation of human intelligence processes by a computer. Specific AI…
Q: Time left 0:4 Assume the following declarations: char name [21]; char yourName [21]; char…
A: Valid statements are://cin>>name;//bool x=strcmp(yourName,studentName);…
Q: Given the following input (4322, 1334, 1471, 9679, 1989, 6171, 6173 and 4199) and the hash function…
A: In the given question, we have given some input integer values. We have to find the hash values of…
Q: Demonstrate with the help of "Command Prompt" and Display all the files and folders in the directory…
A: The command to list all the files and directories in the current directory you are working on varies…
Q: When a child process utilizes unnamed pipes to read the parent's message buffer, what happens…
A: The answer is given in the below step
Q: What's the difference between ScoutSuite, Pacu, and Powler, three popular cloud security solutions?…
A: The Scout Suite is a multi-cloud security auditing solution that is open source and enables security…
Q: mming: chess - pawn movement Input: s1, s2, x1, y1, pawn s1,s2 - horizontal size and vertical size…
A: It is defined as a powerful general-purpose programming language. It is used in web development,…
Q: Make an algorithm and flowchart of the following problem set. 3. Draw a flowchart that calculates…
A: ALGORITHM: Declare the required variables. Start the loop by taking the value of loop variable from…
Q: write a program that will take an integer value as input and do the following task, - If the value…
A: Code: In java import java.util.*;public class Main{ public static void main(String[] args) { int…
Q: What are some of the first examples of cryptography being put to use?
A: We'll have to create some cryptography apps.
Q: Write C++ program to create class name ticket enter the name of person, ticket price, movie name.…
A: Write C++ program to create class name ticket enter the name of person, ticket price, movie name.…
Q: What's the difference between a software development process and a business process? Give an example…
A: Despite their apparent dissimilarity, business processes and software development processes are…
Q: What is Linux distribution life-cycle management and what does it do?
A: Other operating systems, such as Microsoft's Windows, combine all the code into one package. One of…
Q: The CPU is linked to a number of I/O devices, any of which might produce an interrupt at any moment.…
A: Introduction: Cypher block chaining is the technique used by DES (Data Encryption Standard). In…
Q: A wide variety of guises for artificial intelligence are all within the realm of possibility. Give…
A: What are the many types of artificial intelligence? Artificial intelligence is categorized into two…
Q: Design a class named Square that defines a square geometric shape. The class needs to have a data…
A: The program is written in C Programming. Check the program screenshot for the correct indentation.…
Q: Given an analog signal sampled at a rate of 8,000 Hz, x(t) = 5 cos (2π 1500t), for t≥0, a. sketch…
A: (a) Program code: fs1=8000; %Very high sampling rate 8000 Hz nCyle=1; %cycle 1 t1=0:1/fs1:nCyle*1;…
Q: What are the most critical factors for developers to consider throughout the system development…
A: Consideration Create a system for breaking down tasks. Finish job on time. Make a project strategy.…
Q: Exactly what are some of the goals of the authentication process? Analyze how various methods of…
A: Launch: Authentication identifies a process or entity logging into a secure domain. Unauthenticated…
Q: As the network administrator for a growing ISP, you want to make efficient use of your network…
A: ANSWER:-
Q: What are some of the reasons that have led to the development of computer security into the…
A: The following elements have been essential contributors to the development of computer security into…
Q: What kinds of troubleshooting strategies and simple network commands have you utilized in the past…
A: The following is a list of troubleshooting methods for the basic network: - In the settings, check…
Q: Which regulatory guidelines are currently in effect for the protection of personally identifiable…
A: Explanation: Information breach notification regulations demand persons or organisations harmed by…
Q: t abilities are necessary to have in order to work as a database developer o
A: Database programmer or database developer A database programmer, often known as a database…
Q: Which of the following I/O technique is appropriate to use for wireless printer? Select the correct…
A: d.DMA
Q: The infrastructure that grid and cloud computing rely on differs. I'm attempting to figure out what…
A: Start: Grid computing and cloud computing have similar concepts and are frequently mistaken. Both…
Q: C programming code to check whether a number is an Armstrong number or not. Sample Input: 371…
A: ALGORITHM:- 1. Take the input for the number from the user. 2. Count the number of digits in the…
Q: In the goodness-of-fit measures, interpret the coefficient of determination for Earnings with Model…
A: For model coefficient of determination R2=0.7005 Interpretation of coefficient of…
Q: Which strategies does the department use in order to ensure that users can always have access to the…
A: Which strategies does the department use in order to ensure that users can always have access to the…
Q: Given k sorted lists and the total number of elements in all lists is n, please design an algorithm…
A:
Q: https://pastebin.com/raw/zpnrNqpJ Fix the Replace function in this C project and make sure it…
A: C programming is a general-purpose programming language. It is considered to be a high-level…
Q: Write c program to calculate answer of below expression x²+5x+6 Ask user for value of x…
A: Given: Write c program to calculate answer of below expression x²+5x+6 Ask user for value of x
Q: Make an algorithm and flowchart of the following problem set. 3. Draw a flowchart that calculates…
A: Your algorithm and flowchart is given below as you required.
Q: Windows 10 and Linux have different methods for installing, uninstalling, and updating applications.
A: In Windows OS, the following are true: To Install: You must have the installation file on a disc or…
Q: For those who aren't familiar with the technology, explain why and how cloud computing is…
A: Introduction: Cloud computing, as the name implies, is a service that provides customers with…
Q: What are the existing legislative obligations for securing personal information and responding with…
A: Data protection is a set of privacy laws, rules, and procedures that try to limit how much personal…
Q: Make an algorithm and flowchart of the following problem set. 4. Draw a flowchart which will read…
A: Answer: Algorithm: Start Declare the variables of type int scores[100],avg,total,i,sum; Declare…
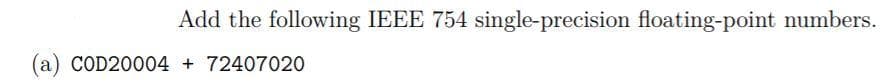
Step by step
Solved in 2 steps with 3 images

- Data represented in ________ is transmitted accurately between computer equipment from different manufacturers if each computer’s CPU represents real numbers by using an IEEE standard notation.H - For the IEEE 754 single-precision floating point, write the hexadecimal representation for the following decimal values: (i)–1.0 (ii)– 0.0 (iii)256.015625Express the following numbers in hexadecimal IEEE 32-bit floating-point format.a. 320b. -12
- For IEEE 754 single-precision floating point, write the hexadecimal representation for positive zero, the smallest positive denormalized number and the largest positive normalized numberPerform the following conversions using IEEE 754 floating point notation. Show your work. a. represent 52.21875 in 32-bit binary floating-point format b. convert 32-bit binary floating-point number 0100 0000 0110 0000 0000 0000 0000 0000 to decimalComputer Architecture Convert the following IEEE single-precision floating-point numbers to their decimal counterparts. a. (6589 0000)16 b. (807B 0000)16 c. (CDEF 0000)16
- Convert the following from base 10 to IEEE 754 Single Precision Floating Point. Show all the steps. Give your final answer in Hexadecimal form.a. -67.3125b. 45.6875Express the following numbers in IEEE 32-bit floating-point format:a. -5 b. -6 c. -1.5 d. 384 e. 1/16 f. -1/321. Floating Point Numbersa. Show the difference between IEEE 16, 32, 64, 128-bit floating-point numbers.b. Express the following numbers in hexadecimal IEEE 32-bit floating-pointformat. i. 320ii. -62
- Express number –62 in hexadecimal IEEE-754 32-bit floating-point format. Show all the steps.(b) Convert the following decimal number to IEEE 32-bit floating-point format i) -16.625 X 10 ^ 4 ii) -3013.3125Answer the following questions on floating-point representation: a) Convert AD510010 16 to an IEEE single-precision floating-point number b) Convert the following IEEE single-precision floating-point number to a decimal number: 10111111110100000000000000000000

