Shrek has guessed three positive integers a, b, and c. He keeps these numbers in secret, but he writes down four numbers on a board in arbitrary order their pairwise sums (three numbers) and sum of all three numbers (one number). So, there are four numbers on a board in random order: a + b, a+ c, b + c and a+b+c. You have to guess three numbers a, b, and c using given numbers. Print three guessed integers in any order. Pay attention that some given numbers a, b and c can be equal (it is also possible that a-b=c). Instruction: Create a Java program that will perform the algorithm that will solve the problem using inheritance as shown in the figure. It must satisfy the 3-sample output as shown below. Explain your codes using comments.
Shrek has guessed three positive integers a, b, and c. He keeps these numbers in secret, but he writes down four numbers on a board in arbitrary order their pairwise sums (three numbers) and sum of all three numbers (one number). So, there are four numbers on a board in random order: a + b, a+ c, b + c and a+b+c. You have to guess three numbers a, b, and c using given numbers. Print three guessed integers in any order. Pay attention that some given numbers a, b and c can be equal (it is also possible that a-b=c). Instruction: Create a Java program that will perform the algorithm that will solve the problem using inheritance as shown in the figure. It must satisfy the 3-sample output as shown below. Explain your codes using comments.
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter8: Arrays And Strings
Section: Chapter Questions
Problem 24PE
Related questions
Question
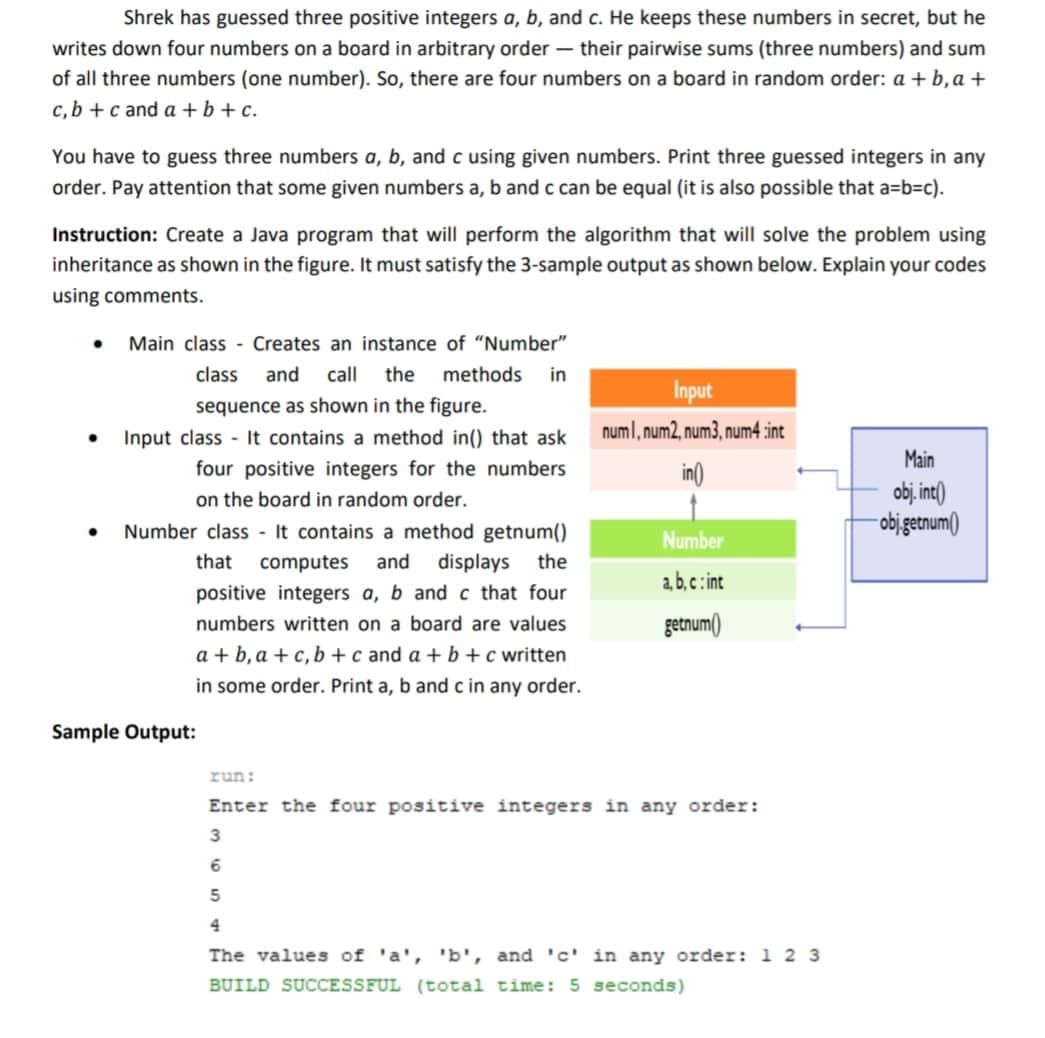
Transcribed Image Text:Shrek has guessed three positive integers a, b, and c. He keeps these numbers in secret, but he
writes down four numbers on a board in arbitrary order their pairwise sums (three numbers) and sum
of all three numbers (one number). So, there are four numbers on a board in random order: a + b, a+
c, b + c and a+b+c.
You have to guess three numbers a, b, and c using given numbers. Print three guessed integers in any
order. Pay attention that some given numbers a, b and c can be equal (it is also possible that a-b=c).
Instruction: Create a Java program that will perform the algorithm that will solve the problem using
inheritance as shown in the figure. It must satisfy the 3-sample output as shown below. Explain your codes
using comments.
Main class Creates an instance of "Number"
class and call the methods. in
Input
sequence as shown in the figure.
numl, num2, num3, num4 :int
●
Main
Input class - It contains a method in() that ask
four positive integers for the numbers
on the board in random order.
in()
obj. int()
obj.getnum()
●
Number
a,b,c: int
Number class It contains a method getnum()
that computes and displays the
positive integers a, b and c that four
numbers written on a board are values
a+b, a+c, b + c and a + b + c written
in some order. Print a, b and c in any order.
getnum()
Sample Output:
run:
Enter the four positive integers in any order:
3
6
5
4
The values of 'a', 'b', and 'c' in any order: 1 2 3
BUILD SUCCESSFUL (total time: 5 seconds)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole