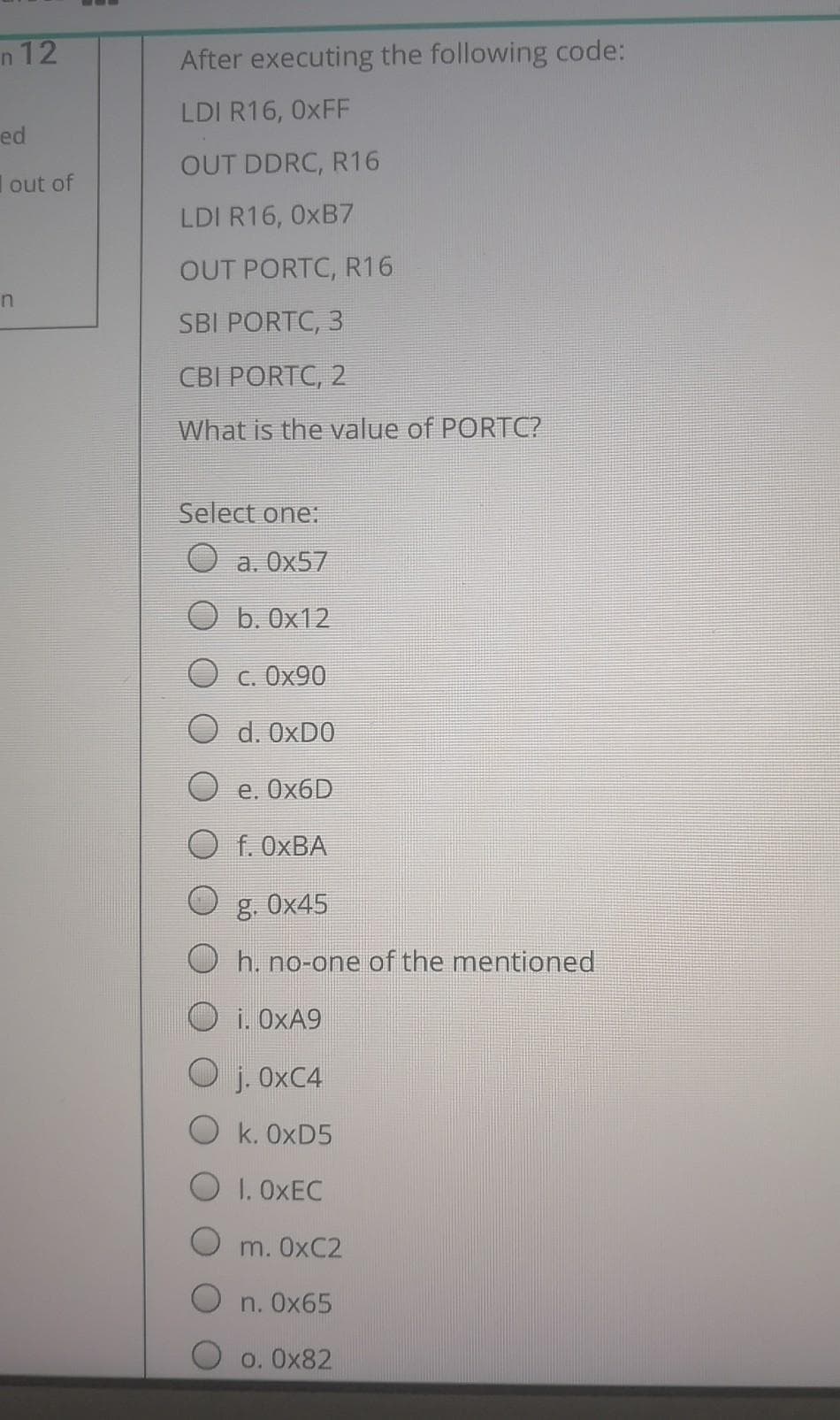
After executing the following code: LDI R16, 0XFF OUT DDRC, R16 LDI R16, 0XB7 OUT PORTC, R16 SBI PORTC, 3 CBI PORTC, 2 What is the value of PORTC?
Q: Which of the following is a hardware-bases synchronization tool? Monitor O Binary semaphore Atomic…
A: Synchronization is needed to enforce the proper sequence of processes and also ensure mutually…
Q: 2) What will be the value in EAX after the following lines execute? mov eax, 30020000h dec ax
A: Complete answer is below..
Q: . Which of the following information is specified by a bitcoin transaction? Is it C? A. A number of…
A: Actually, answer has given below:
Q: omputer Science Control an LED Remotely using TCPDUMP Must be implemented on the RPI 3B+ using…
A: TCPDUMP utility is the premier network analysis tool. It is very similar to Wireshark but it is…
Q: After executing the following code: LDI R16, OXFF OUT DDRC, R16 LDI R16, Ox12 OUT PORTC, R16 SBI…
A: Hey there, I am writing the required solution based on the above given question. Please do find the…
Q: fter executing the following code: LDI R16, 0xFF OUT DDRC, R16 LDI R16, 0xB7 OUT PORTC, R16 SBI…
A: after executing the following code: LDI R16, 0xFF OUT DDRC, R16 LDI R16, 0xB7 OUT PORTC, R16 SBI…
Q: vart SBYTE war2 WORD war3 SWORD 16, -27 ward DWORD 15,14,13,12,11 -20, -1, 1, 29 OFEO0H, OC900H,…
A: The following is the solution
Q: Modify the program so that the writer process passes the output of “ls” command to the upstream end…
A: Modify the program so that the writer process passes the output of “ls” command to the upstream end…
Q: • I the user enters 4, prompts the user and inputs a decimal MAC address, Enter Decimal Integer: 207…
A: Introduction: Algorithm: Creating the program to convert binary to decimal number and vice versa.…
Q: What is the full command line for the loopback address test command
A: To be determine: What is the full command line for the loopback address test command
Q: What will be the value in EAX after the following lines execute?mov eax,30020000hdec ax
A: Explanation: AX is the lower 16 bits of EAX. So, decrementing AX will decrement the lower 16 bits…
Q: 21. Which interrupt is unmaskable…?? a. RST 5.5 b. RST 7.5 c. TRAP d. Both a and b
A: Here is the solution which is mentioned below:
Q: If r0 = 0x20000004, r1 = 0xC3B2A and r2 = 0x02, after executing STR r1, [r0, r2, LSL #2] command,…
A: Lets see the solution.
Q: Which statement is true about what will happen when the example code runs?1: main PROC2: mov…
A: In line “4”, there is a jump statement. So, it jumps to the defined line. But, in line “10”, it is…
Q: Which one of the following signal combinations will be set when the MPU is to perform a write? DT/R*…
A:
Q: what is the purpose of the following code? SBI DDRB, 4 CBI DDRB, 7 loop: SBIS PINB, 7 JMP next SBI…
A: Option (C) is correct
Q: Which of the following will display the message welcome home if the cd /home/user1command is…
A: cd command: The cd command is used to change the current working directory. Syntax: cd…
Q: amming The .sh script can be run with either 0, 2, 3, or 5 command-line arguments. As a basic…
A: Penetration programming The .sh script can be run with either 0, 2, 3, or 5 command-line arguments.…
Q: R0 = 0x20000004, r1 = 0x72EAB1 ve r2 = 0x20 ise STR r1, [r0, r2, LSR #2] after run this command,…
A: R0 = 0x20000004, r1 = 0x72EAB1 ve r2 = 0x20 ise STR r1, [r0, r2, LSR #2] after run this command, the…
Q: what is the purpose of the following code? CBI DDRB, 4 LDI R16, OXFF OUT DDRC, R16 again: SBIS PINB,…
A: option (a) is correct.
Q: What will be the final value in EDX after this code executes?mov edx,1mov eax,7FFFhcmp eax,8000hjb…
A: Explanation of the above-given code segment: mov edx,1 This instruction will load the…
Q: Which statement is true about what will happen when the example code runs?1: main PROC2: push 103:…
A: When the example code runs the program will halt with a runtime error on Line 11. Therefore, the…
Q: Q 10 - Which of the following preprocessor directive allows generating a level one warning from a…
A: Given: Q 10 - Which of the following preprocessor directive allows generating a level one warning…
Q: Write a statement that will dynamically allocate an integer variable and store its address in ip
A: Answer :
Q: 1x10 2 ye20 3 1ot "xSxSy 4 Jet "Sx"Sy" "Sx Sx $x the above shell script will give: Answer.
A: The problem is based on the basics of arithmetic operations in bash.
Q: Only the processer can send addresses? a. True O b. false
A: Answer b. False
Q: Which statement can you put in your ~/.tcshrc file to prevent accidentally overwriting a file when…
A: Solution: Tcsh shell variables are the enhancement of unix C Shell system.They consume less time…
Q: what is the purpose of the following code? CBI DDRB, 4 SBI DDRB, 7 loop: SBIS PINB, 4 JMP next CBI…
A: option (a) is correct.
Q: The write UDPsocket programming code is rdt2 in python where: #Client: 1)function get data from…
A: Answer: Python Source Code: client.py: import socket clientMessage = "Send OK" sendBytes =…
Q: Hi i made this code myself but there are some errors coming in this code i have attached screenshot…
A: Note: Modified code is highlighted in bold Code: #!/bin/shmutex=1full=0empty=3x=0 function…
Q: Consider three machines A, B, C arranged logically in a cyclical order (clockwise: A, B, C) • You…
A: Write associate degree application victimisation UDP socket programming to attain the subsequent…
Q: Which constructor of Datagram Socket class is used to create a datagram socket? Select one: O a.…
A: Constructor is an OOPS concept. Constructor is a special type of method. It is used to initialize…
Q: Which of the following options will produce the same output? tupli (5, 3, 1, 9, 0) = #options i, ii,…
A: The answer is
Q: The IPC facility can do which of the following two operations? * a) write & delete message b) delete…
A: An Operating System also abbreviated as OS is an interface that exists between a computer user and…
Q: What will be the final value in EDX after this code executes?…
A: mov edx, 1 ;This instruction loads the value 1 in edx register. mov eax, 7FFFh…
Q: After executing the following code: LDI R16, 0xFF OUT DDRC, R16 LDI R16, 0x12 OUT PORTC, R16 SBI…
A: The value of PORTC is 0 x 45.
Q: 2. What is the value of CX after execution the following codes? STR DB "ABCDE" MOV DI, OFFSET…
A: While processing, the CPU stores the data as well as instructions in its local memory called…
Q: Open the command prompt window and give the command “ping –n 5 freebsd.org”. Answer the following…
A: I have given the command “ping –n 5 freebsd.org”
Q: When data at the source changes, the adapter gets notified using O a. notifyDatasetChange() O b.…
A: when data at the source changes the adapter gets notified using
Q: What will be the final value in EDX after this code executes? mov edx,1 mov eax,7FFFh cmp eax,8000h…
A: The final value of edx after the execution of code is 1.Question
Q: Which of the following Assembly instructions copy the content of the accumulator to an I/O port? a.…
A: Which of the following Assembly instructions copy the content of the accumulator to an I/O port?
Q: qu 0x0d status equ 0x03 org 0x00 main movlw 0xff tris portb movlw 0x00 tris porta clrf porta start…
A: Make a system flowchart of this code. porta equ 0x05 portb equ 0x06 left equ 0x0c right equ 0x0d…
Q: I get the erroR message: Enter a remote host to scan: 172.0.0.1 Traceback (most recent call last):…
A: To do : reason for the error
Q: Open the command prompt window and give the command “ping –n 5 freebsd.org”. Answer the following…
A: Please give positive ratings for my efforts. Thanks. ANSWER The ping command is a Command Prompt…
Q: Which access level produces the most rapid output?
A: Which access level produces the most rapid output?
Q: With chmod, you may modify the permissions of a subset of users, add the group's execution bit, and…
A: chmod: This command is used to change the access permissions of a file. Syntax: chmod…
Q: import socket from datetime import datetime #initializing host, port, filename, total time and…
A: We need to complete the Code: import socket from datetime import datetime #initializing host, port,…
Q: what is the purpose of the following code? CBI DDRD, 6 LDI R16, 0xFF OUT DDRB, R16 again: SBIS PIND,…
A: The answer is below:
Q: cd /bin/user/directory/abc is an example of relative pathname. True or false.
A: Q. cd /bin/user/directory/abc is an example of relative pathname. True or false.
Q: Only the processer can send signals? O a. True O b. false
A: There are a number of signals that a computer generate. Other than processor input/output device and…
Plz i want this question quickly
Step by step
Solved in 2 steps

- what is the purpose of the following code? CBI DDRD, 6 LDI R16, 0xFF OUT DDRB, R16 again: SBIS PIND, 6 JMP again OUT PORTB, R16 here: JMP here Select one: a. we keep monitoring D6. When it goes LOW, the program will send 0xFF to PORTB b. no-one of the mentioned c. we keep monitoring D6. When it goes HIGH, the program will send 0xFF to PORTBWhat will be stored into cx after executing the following commands? x1 DW 13 DUP(?),5,4,8 mov cx, LENGTH x1 a.4 b.16 c.32 d.13Recall that only Standard Output can be sent across a pipe to another command. Usingthe information presented in this chapter, how could you send Standard Error across thepipe in the following command?ls /etc/hosts /etc/h | tr h H
- what is the purpose of the following code? SBI DDRB, 4 CBI DDRB, 7 loop: SBIS PINB, 7 JMP next SBI PORTB, 4 JMP loop next: CBI PORTB, 4 JMP loop Select one: a. we monitor B7 if its HIGH we clear B4 and if it is LOW we set B4 b. we monitor B7 if its HIGH we set B4 and if it is LOW we clear B4 c. we monitor B4 if its HIGH we clear B7 and if it is LOW we set B7 d. we monitor B4 if its HIGH we set B7 and if it is LOW we clear B7Configure Manual IP address on your Linux Virtual Machine by modifying the network script file for the enp0s3 interface as follows: IPv4: 192.168.x.1 Netmask: 255.255.255.0 Gateway: 192.168.x.254 DNS: 192.168.x.1 X=the last 2 digits of your student ID. If the digits are 01 then use 101 or 02 use 102 etc. Capture the updated contents of the ifcfg-enp0s3 script file. Paste them in the following space: Display the history of commands in the terminal. Capture the screen and paste the outputOpen the command prompt window and give the command “ping –n 5www.freebsd.org”. Answer the following questions. What is the effect of the argument –n 5 on the ping program? What is the average value of the RTT you have obtained? Explain how wasit calculated? What is the meaning of the acronym TTL and why is it used? (Search theInternet to find out.) What is the value of TTL you have obtained?
- How to modify exitstatus.sh to print a message for each of the three exit statuses described in man ls. 0 - OK 1 - minor problem 2 - serious problem exitstatus.sh #!/bin/bash ls > /dev/null if [ $? -eq 0 ]; then echo "It seems to have worked, exit status 0" fi ls asdf 2> /dev/null if [ $? -eq 0 ]; then echo "It seems to have worked, exit status 0" else echo "An error occured, non-zero exit code." fi Solve fast please1. Explain the following unexpected result:$ whereis datedate: /bin/date ...$ echo $PATH.:/usr/local/bin:/usr/bin:/bin$ cat > dateecho "This is my own version of date."$ ./dateSunday April 14 10:00:49 PDT 2020 2. What are two ways you can execute a shell script when you do not have executepermission for the file containing the script? Can you execute a shellscript if you do not have read permission for the file containing the script? 3. What is the purpose of the PATH variable?a. Set the PATH variable so that it causes the shell to search the followingdirectories in order:• /usr/local/bin• /usr/bin• /bin• /usr/kerberos/bin• The bin directory in your home directory• The working directoryb. If there is a file named doit in /usr/bin and another file with the samename in your ~/bin directory, which one will be executed? (Assume thatyou have execute permission for both files.)c. If your PATH variable is not set to search the working directory, howcan you execute a program located…For this lab, you will write a shell script called nethelper.sh that: 1. Reads in a list of hosts from a host file that is passed in as a parameter 2. Repeatedly, until the user selects quit (q), ask the user if the user wants to ping a host or look up a hosts DNS name 3. Once the user has selected an action, prompts the user for which host and then applies the action. Note that for the ssh action, the script must also ask the user for the user name that will be used to log into the host. Step 1 To accomplish step 1 above (reading in a list of hosts from a file), you will write a function called read_hosts. Functions in bash scripts have the following syntax: function name { # function body goes here } You can put any bash syntax inside the function as the function body. Also, note that the parameters to a function act like the parameters passed in at the command line. In other words, the parameters to the function are place in variable named $1, $2, and so on. So, how do you read the…
- i am writing a nodejs login page ,that can read username and passeord from a json file . but my job cant work ,can someone help me see whats the problem in my code ? app.js const express = require('express'); const app = express(); const bodyParser = require('body-parser'); const fs = require('fs'); var createError = require('http-errors'); var express = require('express'); var path = require('path'); const session = require("express-session"); var cookieParser = require('cookie-parser'); var logger = require('morgan'); var app = express(); app.set('views', path.join(__dirname, 'views')); app.set('view engine', 'hbs'); app.use(logger('dev')); app.use(express.json()); app.use(express.urlencoded({ extended: false })); app.use(cookieParser()); app.use(express.static(path.join(__dirname, 'public'))); app.use(passport.initialize()); app.use(passport.session()); app.use(express.static('./public')); app.use(bodyParser.urlencoded({extended:false})) app.use(bodyParser.json());…1. Which of the following is not usually implemented in the server-side code? a. Routing Code b. All of these are usually implemented in Server-Side Code c. Authentication Logic Code d. User Interface Code 2. True or False. The fetch method can only be used to make GET requests. a. True b. False 3. True or False. Node.js is a asynchronous event-driven framework. This means it can only handle one event at a time a.True b. False 4. When using the router level middleware in express, what must match for the Handler Method to be executed? a. None of these b. Path and URL c. Request and Response d. Method and Pathcan someone fix the following code so it works and the data from the api source import requests # Set API endpoint and parametersurl = "http://api.openweathermap.org/data/2.5/weather"params = { "q": "New York", "appid": "bdc131976a43a5df7074f0aef35fc088", "units": "imperial"} # Make GET request to APIresponse = requests.get(url, params=params) # Check if request was successfulif response.status_code == 200: # Parse JSON data from response data = response.json() # Extract relevant information from data location = data['name'] temp = data['main']['temp'] humidity = data['main']['humidity'] description = data['weather'][0]['description'] # Print weather information print(f"Current weather in {location}:") print(f"Temperature: {temp}°F") print(f"Humidity: {humidity}%") print(f"Description: {description}")else: print("Error retrieving weather information")



