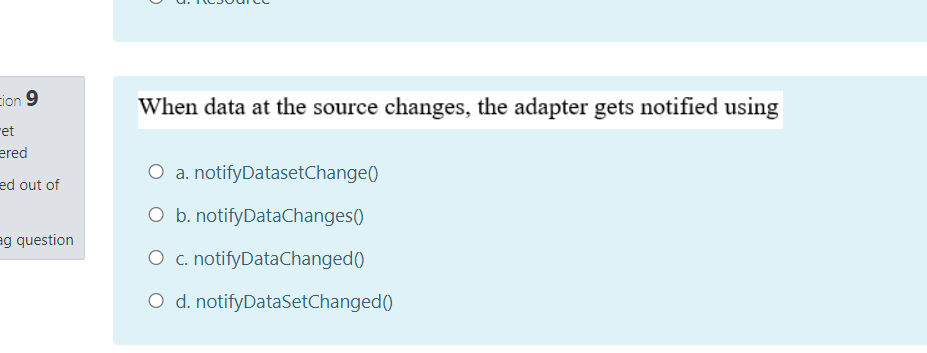
When data at the source changes, the adapter gets notified using O a. notifyDatasetChange() O b. notifyDataChanges() O c. notifyDataChanged() O d. notifyDataSetChanged()
Q: . Which access method uses a “listen before sending” strategy? a. Token passing b. CSMA/CD c. Token…
A: This mcq is belongs to Networking.
Q: What does genrsa and des3 refer to on the following terminal command: openssl genrsa –des3 –out…
A: genrsa and des3 are the encryption commands for openssl that are used to encrypt the server.key…
Q: omputer Science Control an LED Remotely using TCPDUMP Must be implemented on the RPI 3B+ using…
A: TCPDUMP utility is the premier network analysis tool. It is very similar to Wireshark but it is…
Q: 2. Write the outputs from the following IOS CLI commands ( copy & paste from your simulator to a pdf…
A: Given, Set of Cisco IOS CLI commands. To give the function each of these commands perform.
Q: Unlike Modules, Snap-ins are permanently loaded to our PowerShell session, and the only way to…
A: Remove-PSSnapin cmdlet removes a Windows PowerShell snap-in from the current session. You can use it…
Q: Indicate which entry you could add to /etc/rsyslog.conf to:a. Log all critical messages from the…
A: Syslog is an acronym for System Log and is used in Linux for containing event records from the OS…
Q: In relation to RESTCONF methods, Select one or more: If a POST request succeeds, the server responds…
A: The most common codes for RESTCONF are 200 (OK) and 201 (Created). so in the given question get…
Q: Identify whether the following pathnames are absolute or relative. /home/student [ Choose ]…
A: Here is the type of path answered:
Q: accel = OxA4; PORTB = 0x23; What is the value of PORTB after the following mask operation? PORTB =…
A:
Q: File "/Users/foramodedara/Desktop/i2p/assg3_219283662.py", line 17, in wordtomorse code += Mcode…
A: Please refer to the following step for the complete solution of the problem above.
Q: backs in tabular form. (Dear sir and mam please solve this answer, its urgent, 100% accu
A: The model (DAO) is comprised of application data and business rules, while the controller (Servlet)…
Q: command is used to disable the script execution in powershell.
A: Dear Student, To disable script execution in powershell first you need to execute cmd.exe,open…
Q: if [ $(id -u) -eq 0 ];then read -p "enter username:" username read -s -p "enter password:"…
A: The code is correct and runs perfect in the system.
Q: amming The .sh script can be run with either 0, 2, 3, or 5 command-line arguments. As a basic…
A: Penetration programming The .sh script can be run with either 0, 2, 3, or 5 command-line arguments.…
Q: what is the purpose of the following code? CBI DDRB, 4 LDI R16, OXFF OUT DDRC, R16 again: SBIS PINB,…
A: option (a) is correct.
Q: The user credentials in the following screenshot is for GLOBAL Setingu Port Sata Aporithn Setings…
A: correct option A
Q: URL Connection class can be used to read and write data to the specified resource referred by the…
A: Given: The URL Connection class can be used to read and write data to the specified resource…
Q: Assume that you are cuently lo9gged ne 52. Configure the Port security on Switched interface…
A: It is defined as an addresses are useful for network diagnosis because they never change, as opposed…
Q: q20- The process that gets activated when you press Ctrl-Alt-Del on a Windows machine is a.…
A: Authentication protocol prevents unauthorised access by defining set of rules in computer system.…
Q: what is the purpose of the following code? CBI DDRB, 4 SBI DDRB, 7 loop: SBIS PINB, 4 JMP next CBI…
A: option (a) is correct.
Q: re an access point
A: given - Effective way sto secure an access point
Q: A special variable on the system called the umask (user mask) takes away permissions on new files…
A: A special variable on the system called the umask (user mask) takes away permissions on new files…
Q: We want to add an email account to a smartphone using port 143 for the incoming mail server and port…
A:
Q: The line that configures the host name for the computer at boot time can be found in /etc/hostname.…
A: Solution: The path etc/hostname contains information about the machine such as machine…
Q: Using CLI mode implement all commands on your personal computer, if command is not working explain…
A: b) tracert [-d]: Not working Unable to resolve target system name [-d]. c) tracert [-h MaxHops]…
Q: (LINUX) how do i use nmap to discover a hidden port on a listening webserver this is regarding to…
A: Given: how do i use nmap to discover a hidden port on a listening webserver this is regarding to…
Q: The command “#define LED_PORT PORTD” will create LED_PORT constant that can be changed during the…
A: First we have to understand what is the use of the command define in programming . define as the…
Q: While troubleshooting an E-mail client issue on a user’s system, you that the incoming mail server…
A: CORRECT OPTIONS: While troubleshooting an E-mail client issue on a user’s system, you that the…
Q: #write code for the server #write code for the client the Card number = 1000987 password number =…
A: Server - A system that provides services to other systems in its network. Client - A system…
Q: نقطتان )2( Which mode allows the user ?to snap objects SNAP OSNAP POLAR ORTHO نقطتان )2( to move…
A: Your answer is given below.
Q: Which method is used for sending data to URL from memory buffer? a. NPN_PostURL b.…
A: Question. Which method is used for sending data to URL from memory buffer? a. NPN_PostURL b.…
Q: uring which of the following AES transformation, XOR operation is performed? a. Add round key b.…
A: During which of the following AES transformation, XOR operation is performed? a. Add round key b.…
Q: command is used to save the running config to the startup config in Cisco rout
A: copy running-config startup-config command - used to save the current running configuration to the…
Q: Computer Science You work as the IT security administrator for a small corporate network. You need…
A: Complete the lab with following procedure : 1. Select Start. 2. Select Windows Accessories. 3.…
Q: Session data will not be available once the user logged out. O a. TRUE O b. FALSE
A: Answers: 1) True 2) False
Q: Which violation mode should be configuring in the switch interface to protect the switch from…
A: Question which violation mode should be configuring in the switch interface to protect the switch…
Q: Which of the follow statement(s) correctly completes the following sentence fragment The serial…
A: The serial monitor acts as link between the computer and your Arduino . It allows you to send and…
Q: 5. Command1.Enabled = True, false "1" "0" 1,0 O O O
A: Please check the step 2 for answer and step 3 for Explanation.
Q: A port is where there is only one receiver fixed to it. QUESTION 12 Vhen using buffer, the producer…
A: Given :- (a.) A port is-------- where there is only one receiver fixed to it. (b.) When…
Q: SwitchA ROOT Priority 32768 MAC: AAA 34
A: Introduction: When you examine the link between switches B and C, you will notice that the interface…
Q: In switches, which port security action would result in shutting down a port? a. Protect b. Report…
A: We are going to understand which port security action would result in shutting down a port in…
Q: What is the name given to the security attack when an opponent prevents messages from reaching a…
A: Denial-of-service attacks. These attacks are defined as cyberattacks where teh unauthorized users…
Q: Which of the timer is responsible for keeping the window size information flowing even if the other…
A: Given: Which of the timer is responsible for keeping the window size information flowing even if the…
Q: Which DNS resource record is an alias to other records?a. Ab. AAAAc. CNAMEd. NS
A: DNS record alias to other record A Domain Name System records are instructions that provide…
Q: Drop Send Turn off Unknown Syslog Port Frames Protect Restrict Shutdown
A: Dear Student, Since The required diagram for SW2 is not available so, I am answering the question In…
Q: Which log in Event Viewer would you use to find out about attempted logins to a computer?
A: Event viewer holds every single detail of the events that happened in the system, and maintains a…
Q: Give THREE (3) differences between plugin and backups plugin.
A: Give THREE (3) differences between plugin and backups plugin.
Q: Datagram socket is the connectionless socket which uses FTP. Question 2 options: True False
A: The problem is based on the bascis of computer networks.
Step by step
Solved in 2 steps

- A. COPE is a more relaxed version of BYOD where employees can choose from a list of company-approved devices. True False B. A router crushing can be classified as an event True False C. In Linux file systems, a useful tool is the archive bit in each file’s property. True FalseJoshua works as a systems administrator. A computer running Windows 2019 Server crashes. However, he is not able to find the root cause of the problem. If the root cause of the problem is processor overload, which of the following should Joshua investigate to troubleshoot the issue? a). The security event log b) The hardware events log c) The applicatoin event log d) The system event logMust be done in Ubuntu linux commands: 1) Demonstrate how to start a job in the background and then bring it to the foreground. Also show how to send a job from the foreground to the background. 2) Demonstrate how to configure the 'syslogd' messages such that all messages of exactly info are directed to the file /var/log/info-log. 3) Show examples of getting hardware related information from what’s available in the /proc directory
- Between Full, Incremental, and Differential A.) Which one backs up the things that have been changed or added since the Last Full Back Up? B.) Which one backs up the things that have changed or added since any type of backup.Correct and comprehensive answers will be UP VOTED; otherwise, they will be DOWN VOTED. What exactly is scheduler activation? What kinds of events does the kernel notify the user-level scheduler about?Book reference: Windows PowerShell Step by Step 3rd Edition - Ed WilsonChapter 15 8. What is a method to clear current error messages saved in memory? 9. What is the below LDAP script used for? $strClass = "User" $strName = "CN=MyNewUser" $objADSI = [ADSI]"LDAP://ou=myTestOU,dc=nwtraders,dc=msft" $objUser = $objADSI.Create($strClass, $strName) $objUser.Put("sAMAccountName", "MyNewUser") $objUser.SetInfo() a). What is the use of the below command? SetInfo()
- The package delivery monitoring script needs to perform several functions,from listening for and reacting to triggers from the package delivery monitoringhardware to sending an email alert about the event and everything in between.Specifically, the script needs to do the following:1. Listen for threshold exceeded events (i.e., package delivery and removal)sent via the soft serial port communications between the XBee radios.2. Timestamp these events generated by the force sensitive resistor in thedeliverystatus table.3. If a high value is received (i.e., a package is delivered), query trackingnumbers stored in the tracking table. If a low value is received (i.e., apackage is removed), send an email alert stating such and return executionof the script back to listening for delivery events.4. If a high value is received, wait for a specified time before querying thetracking table to allow time for the courier to update the delivery records.5. Iterate over undelivered tracking numbers and…In HomeController.cs, set three session states to get course name, student id and date. Use Course, StudentId and CurrentDate(yyyymmdd) as the session variables. Set these states in the IActionResult Tools ( ) method. ASP.NET MVCMrs. Y forgets her password. He goes to the system administrator's office, and the admin resets her password and gives Alice the new password. Why does the SA reset the password instead of giving Y her previous (forgotten) password? Why should Mrs. Y re-reset her password immediately after the SA has reset it?
- Suppose I want to copy a document to USB Flash drive Using Command in windows computer the document is located in this pc>documents>chapter12 and the user name for the computer is Zat. I have c:\user\zat> what would be rest of the command.Subject code - rcs509 Previously you did it wrong ! This time i will report / downvote you. Don't answer this if you are not good in this subject. Which of the timer is responsible for keeping the window size information flowing even if the other end closes its receiver window? A. Retransmission timer B. Persistent timer C. Keep alive timer D. Time-wait timerThe proposal to send a boot ID along with a message ID for each remote procedure call is to: a) Allow the client to tell if it received a duplicate response to a remote procedure call. b) Enable the client to identify whether the response came from an alternate backup server. c) Allow the server to distinguish among messages coming from different clients. d) Avoid having the server think a message is a duplicate when it is not.





