AIRLINE RESERVATION SYSTEM USE CASE DIAGRAM Login/Profile <> <<ǝpr View frequent-flier points Create flight reservation public/private flight Assign seat Business/Regular class
AIRLINE RESERVATION SYSTEM USE CASE DIAGRAM Login/Profile <> <<ǝpr View frequent-flier points Create flight reservation public/private flight Assign seat Business/Regular class
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter20: Queuing Theory
Section: Chapter Questions
Problem 17RP
Related questions
Question
MAKE AN ACTIVITY DIAGRAM BASED ON THE SCENARIO ON THE ATTACHED PHOTO
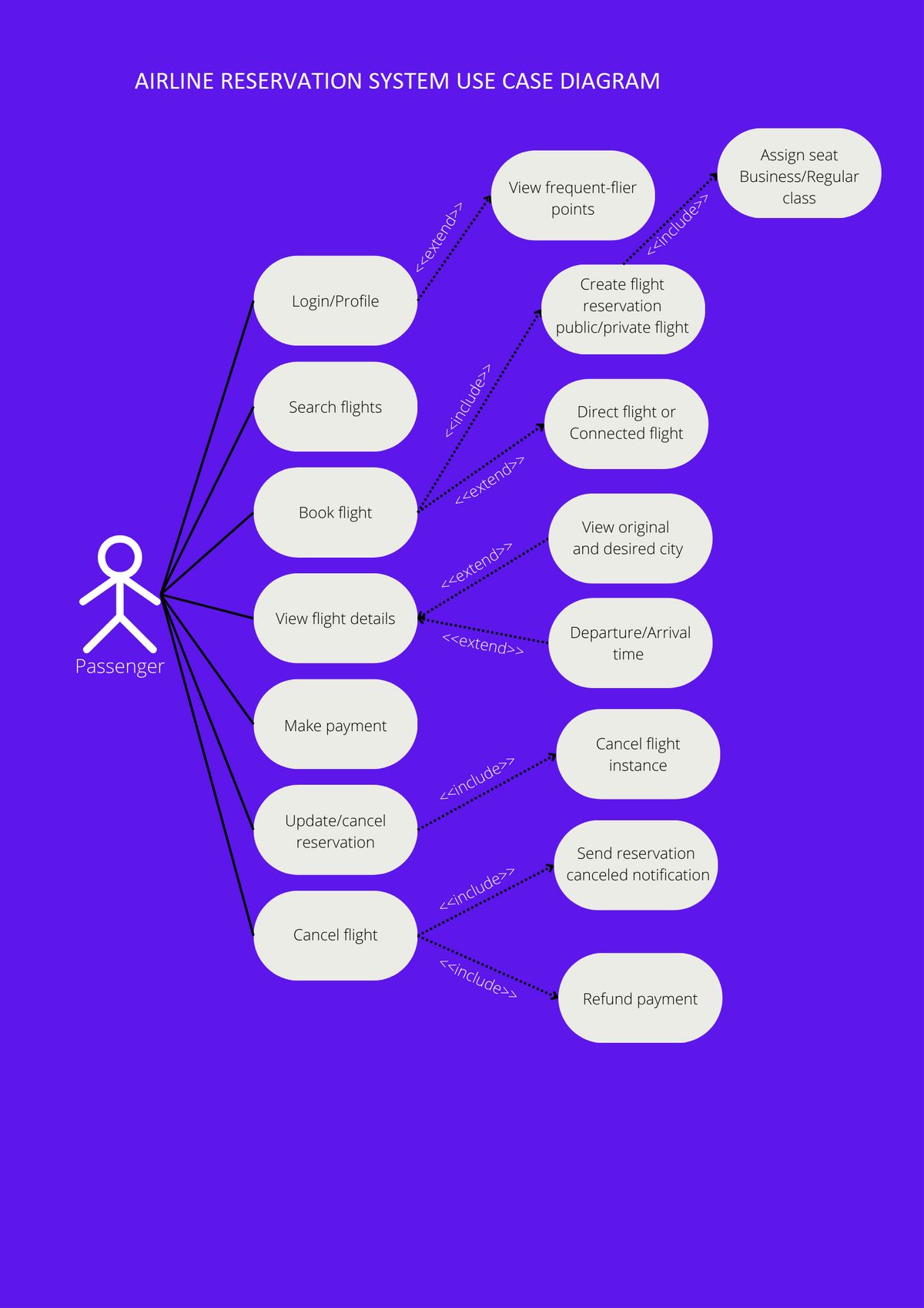
Transcribed Image Text:AIRLINE RESERVATION SYSTEM USE CASE DIAGRAM
웃
Passenger
Login/Profile
00000
Search flights
Book flight
View flight details
Make payment
Update/cancel
reservation
Cancel flight
<<extend>>
<<include>>
View frequent-flier
points
<<extend>>
<<extend>>
<<extend>>
<<include>>
<<include>>
<<include>>
<<include>>
Create flight
reservation
public/private flight
Direct flight or
Connected flight
View original
and desired city
Departure/Arrival
time
Cancel flight
instance
Send reservation
canceled notification
Refund payment
Assign seat
Business/Regular
class
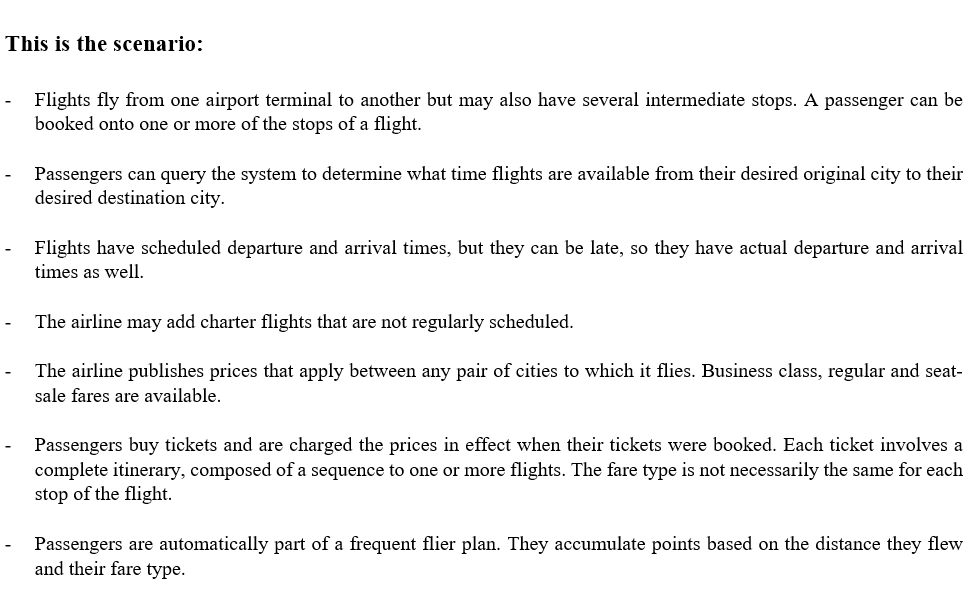
Transcribed Image Text:This is the scenario:
-
-
Flights fly from one airport terminal to another but may also have several intermediate stops. A passenger can be
booked onto one or more of the stops of a flight.
Passengers can query the system to determine what time flights are available from their desired original city to their
desired destination city.
Flights have scheduled departure and arrival times, but they can be late, so they have actual departure and arrival
times as well.
The airline may add charter flights that are not regularly scheduled.
The airline publishes prices that apply between any pair of cities to which it flies. Business class, regular and seat-
sale fares are available.
Passengers buy tickets and are charged the prices in effect when their tickets were booked. Each ticket involves a
complete itinerary, composed of a sequence to one or more flights. The fare type is not necessarily the same for each
stop of the flight.
Passengers are automatically part of a frequent flier plan. They accumulate points based on the distance they flew
and their fare type.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole