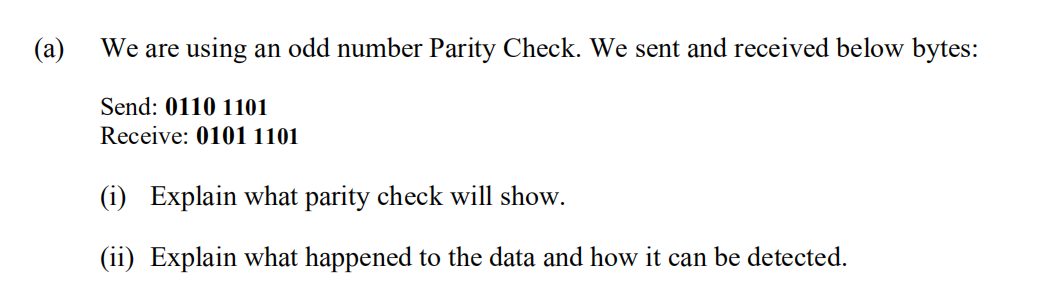
an odd number Parity
Q: Are top managers likely to be more effective if they have IT experience? Why or why not? Will online…
A: Answer 1: Effectiveness of top managers Top-level executives are in charge of an organization's…
Q: Propose five rules for both visual perception and haptic perception, based on what you've learned…
A: Guidelines are just that: they're guidelines: They ensure that an interface has a consistent…
Q: What is the difference between active and passive attacks?
A: Active Attacks: Active attacks are those in which the attacker attempts to alter or change the…
Q: What are some of the most effective methods of firewall management? Explain.'
A: Introduction: Firewall administration entails configuring and monitoring a firewall to keep your…
Q: Distinguish in considerable detail between iterated and non-iterated DNS queries, authoritative and…
A: Intro On the Internet, the Domain Name System (DNS) is referred to as "the phonebook." Humans have…
Q: Assembly language 32 bit MASM Irvine Make a Adventure story that makes the user choose between three…
A: Answer is given below-
Q: Common Multiple (LCM) to schedule? lability of these tasks using RMS and confirm whether or 1 e the…
A:
Q: Create a function that will calculate the total amount after tax (note: total amount after tax =…
A: Find the required function given as below :
Q: Research TCP/IP and OSI and how they are related to network security. Network security is aided by…
A: Network Security protects your network and data from breaches, intrusions and other threats.
Q: Need complete codes of a LIBRARY MANAGEMENT SYSTEM using C Language (PrintF ScanF), structures,…
A: An library management system will contain no.of operations like add book,return book search…
Q: What are the many sorts of data structures that are available?
A: INTRODUCTION: Here we need to tell the many sorts of data structures that are available.
Q: Which of the following server roles is automatically installed when the Active Directory Domain…
A: Introduction Active Directory: It is made to ensure security in the hierarchical organization that…
Q: What is the purpose of authentication? Is it possible to compare and contrast the advantages and…
A: Start: Authentication is the process of identifying users who want to access a system, network, or…
Q: Why are mental models crucial in interface design? Give five notable advancements in virtual display…
A: Mental models are one of the most fundamental ideas in human–computer interaction. Instructions,…
Q: Provide five recommendations on what a system designer can do to reduce the amount of memory a user…
A: Introduction: In this section, we must make five recommendations for what a system designer can do…
Q: Write code in C++ There are two scientists working on set of numbers. The first person is looking…
A: Algorithm: Ask the first person to enter the numbers.then prompt for second user asking how many…
Q: the PDA
A: Given :- In the above question, a push down automata (PDA) is mention in the above given question…
Q: What are some of the most beneficial character attributes for an analyst who is participating in the…
A: Traits of an analyst An analyst is someone who is in charge of acquiring information about a…
Q: You have to create a program in C language in which the user enters the mass M and length L of a…
A: Your C Code is given below as you required with an output.
Q: What do you expect to happen in the Philippines in terms of technology over the next ten years?
A: I will explore the following things in my response: 5G internet: AI(Artificial Intelligence)…
Q: nsic software help investiga
A: Introduction: Below the how forensic software help investigators
Q: database: sql Q1. Create the following tables: Carrier Attribute name Type Size Constraint…
A: here in the question ask for a query to create this tables.
Q: multiplication of the following two floating point numbers using the simple floating point format
A: Answer: First, Do the calculation of the first portion so (-0.75*23) = -17.25 Second, Do the…
Q: Briefly explain why compromises of intellectual property can damage an organization? Enter your…
A: Intro cyber espionage. espionage occur. why a compromise of intellectual property can damage an…
Q: Give an example of why ICT growth is tough, particularly for a company like Uber, which is the…
A: Explain why ICT growth is tough, particularly for a company like Uber, which is the first metered…
Q: In terms of network security, what are the differences between the Red, Blue, and Purple teams?
A: Introduction: Here we are required to explain what are the differences between the Red, Blue, and…
Q: A cross-site scripting (cross-site scripting) assault is just what it sounds like: In your own…
A: Cross-site scripting is known as XSS.
Q: what ways is NRZ Coding unsuitable for transmitting s
A: Lets see the solution.
Q: Given the PDA below determine whether the following string is accepted or not, write A if accepted…
A: 1) abba => NA(Not-accepted) , It would not be accepted by PDA 2) ε => NA, there is no direct…
Q: I would like to ask something. What may happen to customer if you didn't follow the 8 Laws of…
A: The 8 laws of software evolution are applicable to only e-type of software i.e. the software which…
Q: Any protocols or features that are mentioned when an error message reading "404 Not Found" appears…
A: Answer:
Q: What are the benefits and drawbacks of utilizing IPSec in compared to other network security…
A: SOLUTION: It basically encrypts and validates data packets delivered over the internet. IPSec brings…
Q: When it comes to transferability, how may the blockchain work?
A: Introduction: Blockchain is a secure system that uses a complicated encoding method to transfer and…
Q: What distinguishes a hacktivist from a cyberterrorist in your opinion? Is using hacktivists against…
A: Let's take a closer look at the solution. Hacktivism is the peaceful use of unlawful or legally…
Q: Discussion of iterative and non-iterative DNS queries, authoritative servers, root servers (if…
A: Intro Non-iterative Query ->In a non-iterative name query, the DNS client requires that the DNS…
Q: 1. The causal sequence x(n) in z- transform means the limited of summation taken from n= -o0 to n= 0…
A: Answer : False In case of causal sequence x(n) in z - transform limited of summation taken from n=0…
Q: explain the problem. Write like essay and explain in detail. Like 1 or 2 page 2.4 Prove that for any…
A:
Q: Data Structures What is placement new?
A: You use the placement new when you want to call a constructor directly. When you have some raw…
Q: What factors influence managers' decisions on which alternative design approach to pursue?
A: Introduction: To proceed with the design approach, the management should consider the following…
Q: hat are the objectives of authentication? Is it possible to compare and contrast the advantages and…
A: Lets see the solution.
Q: I'm interested in knowing what the theories are on cybercrime. Provide references in response to…
A: what the theories are on cybercrime? Provide references in response to this question.
Q: What would cause the current instruction to be reset if an error occurred?
A: Usually, at Intel as a minimum, an interrupt is something that comes from the outside global.…
Q: Based on the previous question (UNIX passwords are derived
A: The average time to crack a password with brute force on a UNIX system is approximately 1.5 days.
Q: What exactly is a cactus stack? What is its function?
A: Introduction: Data structure is the systematic structuring of information so that it can be used…
Q: Put another way, what does wavelength division multiplexing do?
A: Wavelength division multiplexing (WDM): Wavelength division multiplexing (WDM) is a technique for…
Q: reate tables for the following, where the first 2 are entity-types and the last one is relationship.…
A: Q: Code the given problem
Q: Exercise 2: 1. Draw the PERT Diagram related to the following tasks. Identify the critical path Task…
A:
Q: Explain, in your capacity as a programmer, when it would be appropriate to employ static and dynamic…
A: Place of coding where we can use static array and dynamic array
Q: Why are input/output instructions often regarded as privileged instructions?
A: Indeed, the Privileged instructions are the instructions which are only executed in kernel mode. If…
Q: What are the main goals of authentication, and why is it necessary? In what ways are alternative…
A: Password-based authentication : Let us look at the solution. Identifying an individual process or…
Step by step
Solved in 2 steps with 2 images

- 1-A system has received 2 bytes of transmission, with the first bit being an extra odd parity bit: 100001111, 001010101. Is there detectable error? 2- A digital recording of audio file is 120 seconds, with bitrate 44 Kbps. Write down the exact number of KB needed for this recording. 3-Write down the smallest number in decimal, that can be represented by 11bit signed binary1. One way of detecting errors is to transmit data as a block of n rows of k bits per row and add parity bits to each row and each column (for this problem k is >=5). The bit in the lower-right corner is a parity bit that checks its row and its column. This scheme will detect burst errors of length 5? (A) TRUE (B) FALSE 2. According to Shannon, if the amount of Signal is increased on a transmission medium, everything else constant, the expected theoretical bitrate would (A) increase (B) decrease (C) remain the same (D) cannot determine 3. In nonpersistent CSMA, if a transmitter ready to transmit senses the channel is busy, the transmitter waits a random amount of time, and senses the line again. If it’s still busy it repeats the process, otherwise it transmits the data. (A) True (B) False2) Compute data sent for a bit stream of 101011 with CRC using a generator 1010 Randomly assume any bit to have been corrupted, Illustrate how the receiver can detect if the data was corrupted.
- We want to transmit 1000 characters with each character encoded as 8 bits. a. Find the number of transmitted bits for synchronous transmission. b. Find the number of transmitted bits for asynchronous transmission. c. Find the redundancy percent in each case."Parity bits" are used for which of the following purposes? A. Encryption of data B. To transmit faster C. To detect errors D. To identify the userPlease provide assistance with the following question: When it comes to parity bits, what is the maximum number of mistakes that may be detected in a message?
- Please help with the following question: What is the parity bit for each of the following messages using even parity? a. 10011101100110110 b. 01000101110101011 c. 01110111100100010 d. 00101101011100100What are the CRC bits (R) associated with the payload containing first four bit 1101 and last four bit is the last digit of your reg number (i.e. 5, payload = 1101 0101). Suppose that the 4-bit generator (G) is 0101, and r = 3Beginning with one start bit followed by 21 data bits, 2 parity bits and 1 stop bit: a) What are the total number of bits in the frame? b) What would the overhead and throughput be (answer in percent)?
- In CRC, if the dataword is 5 bits and the codeword is 8 bits, how many 0s need to be added to the dataword to make the dividend? What is the size of the remainder? What is the size of the divisor? What is the maximum effect of a 2-ms burst of noise on data transmitted at the following rates?With the use of a Checksum Method, show the transmission of “m” and “n” from the sender to destination side. The following block is sent: 00001111 11110000 11001100 10101010. With the use of a two-dimensional parity check and assuming that no single/multiple-bit or burst error have occurred, what will be received in the receiver side? NOTE: Put a space after each frame.Computer Network : Suppose 3 blocks of 16 bits need to be sent, using Checksum method proves the following cases: When there is no error When there is a burst error and detected. When there is a burst error and remains undetected Block 1: 1011101110101011 Block 2: 0101000011111010 Block 3: 0111010110101010

