An organization is to divide the network 192.168.1.0/24 into six subnets. The largest division has 32 hosts. What is the main problem if CLSM is Used? • Subnet addresses may not be assigned to point-to-point connections O Broadcast storms O CLSM addressing scheme is not feasible R Too many IP addresses are wasted O Too many subnets are wasted O No problem with using CLSM
An organization is to divide the network 192.168.1.0/24 into six subnets. The largest division has 32 hosts. What is the main problem if CLSM is Used? • Subnet addresses may not be assigned to point-to-point connections O Broadcast storms O CLSM addressing scheme is not feasible R Too many IP addresses are wasted O Too many subnets are wasted O No problem with using CLSM
Comptia A+ Core 1 Exam: Guide To Computing Infrastructure (mindtap Course List)
10th Edition
ISBN:9780357108376
Author:Jean Andrews, Joy Dark, Jill West
Publisher:Jean Andrews, Joy Dark, Jill West
Chapter8: Network Infrastructure And Troubleshooting
Section: Chapter Questions
Problem 8TC
Related questions
Question
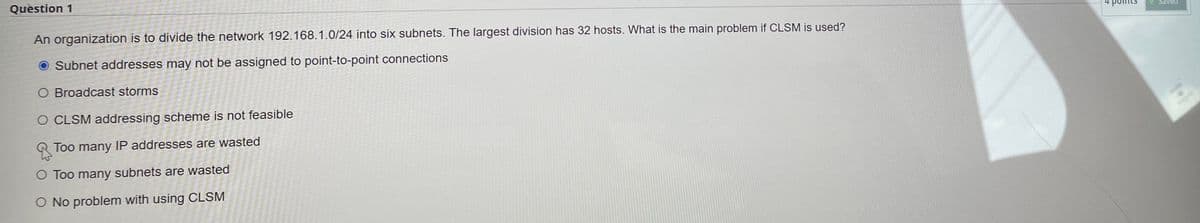
Transcribed Image Text:Question 1
An organization is to divide the network 192.168.1.0/24 into six subnets. The largest division has 32 hosts. What is the main problem if CLSM is used?
O Subnet addresses may not be assigned to point-to-point connections
O Broadcast storms
O CLSM addressing scheme is not feasible
Too many IP addresses are wasted
O Too many subnets are wasted
O No problem with using CLSM
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning