Here is a Snap script. for i 1 to 4 pen down N -gon size (L pen up change x by 200 The user-defined block (N)-gon size (L) draws a polygon with N sides, whose side length is L. You want this script to draw a row of five shapes: 1. a triangle (3 sides) of side length 150, 2. a pentagon (5 sides) of side length 135, 3. a septagon (7 sides) of side length 120, 4. a nonagon (9 sides) of side length 105. In terms of i, what expressions should be put in place of N and L?
Here is a Snap script. for i 1 to 4 pen down N -gon size (L pen up change x by 200 The user-defined block (N)-gon size (L) draws a polygon with N sides, whose side length is L. You want this script to draw a row of five shapes: 1. a triangle (3 sides) of side length 150, 2. a pentagon (5 sides) of side length 135, 3. a septagon (7 sides) of side length 120, 4. a nonagon (9 sides) of side length 105. In terms of i, what expressions should be put in place of N and L?
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter8: Arrays And Strings
Section: Chapter Questions
Problem 24PE
Related questions
Question
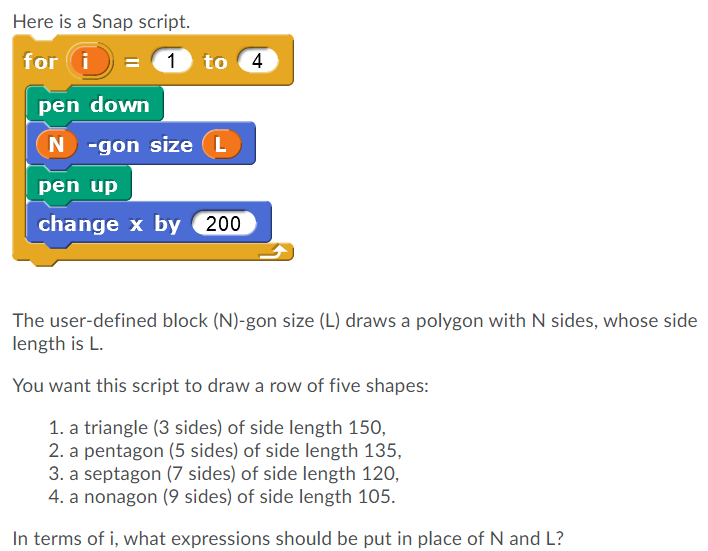
Transcribed Image Text:Here is a Snap script.
for i
1 to 4
pen down
N -gon size (L
pen up
change x by 200
The user-defined block (N)-gon size (L) draws a polygon with N sides, whose side
length is L.
You want this script to draw a row of five shapes:
1. a triangle (3 sides) of side length 150,
2. a pentagon (5 sides) of side length 135,
3. a septagon (7 sides) of side length 120,
4. a nonagon (9 sides) of side length 105.
In terms of i, what expressions should be put in place of N and L?
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning