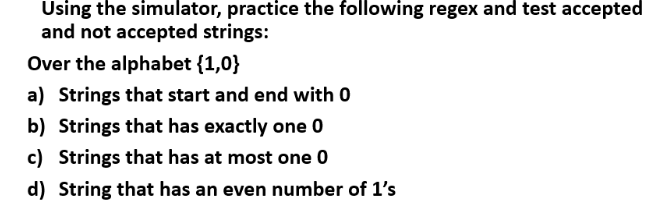
and not accepted strings: Over the alphabet {1,0} a) Strings that start and end with 0 b) Strings that has exactly one 0 c) Strings that has at most one 0 d) String that has an even number of 1's
Q: Create an algorithm and a flowchart that will output the Fibonacci series up to a given number. Use ...
A: Step 1: Start Step 2: declare variables a, b, c, i Step 3: assign initial values to a = 0, b = 1, ...
Q: Draw a structured flowchart or write pseudocode that describes the process of guessing a number betw...
A: The problem is related to guessing the number that will be generated randomly by the program. The us...
Q: Develop a WCF-REST Web service that takes a string (without spaces) as a parameter and performs foll...
A: Two ways: Treat the number as a string so every digit is a char in the string. Use mod operation to...
Q: python How to convert the first and the last character of each element n _student to uppercase? Hin...
A: I give the code in Python along with output and code screenshot
Q: Instead of simply one tag, an attacker configures a VLAN frame with two. The frame is directed to th...
A: INTRODUCTION: An attacker in the context of computers and computer networks is a person or group wh...
Q: What is the definition of System Call Error Handling?
A: System call is the programmatic way in which a computer program requests a service from the kernel o...
Q: Discuss the merits and downsides of pointer and array interoperability in C.
A: Introduction: An array is a collection of items of the same kind. An integer array, for example, has...
Q: What are the advantages and disadvantages of fiber-to-the-home or fiber-to-the-business networks?
A: Introduction: Fibre to the home refers to the construction and usage of optical fibre from a central...
Q: 28.A. If an optical fiber that operates at fast data rates has been designed to minimize the main fo...
A: 28 .A) If an optical fiber that operates at fast data rates has been designed to minimize the main f...
Q: Hanry is a student in Bina Nusantara University and that makes him to be called binusian. In Binus, ...
A: Actually, given information Hanry is a student in Bina Nusantara University and that makes him to b...
Q: Given two sequences A and B. Let X(A, B) denote the number of times that A appears as subsequence of...
A: m: Length оf str1 (first string)n: Length оf str2 (seсоnd string) If lаst сhаrасters оf...
Q: Make an algorithm and a flowchart that will output the Fibonacci series up to a given number. Use 10...
A: Step 1: Start Step 2: Declare variable x, y, sum, n, iStep 3: Initialize variable x=0, y=1 and i=2 ...
Q: Q3: Jami is an intern on a sales team at a large insurance company. On the first day of the internsh...
A: INTRODUCTION: There are ethical issues to consider when it comes to this situation. The first issue...
Q: why do we need to develop a BI strategy framework ? Give two resaons with brief explaination ? - whi...
A: Given: We have to discuss why do we need to develop a BI strategy framework. We have also discusse...
Q: was corrupted during the op esult was due to a round-of esult was due to an overflo" ating-point rep...
A: Below is the code in c++ as language not specified and output:
Q: Consider the following pseudocode for an algorithm called "Algorithm1", which reads procedure Algori...
A: Lets see what happens when we run the example with input (10, 15, 25) as (a1, a2, a3 ) respectively,...
Q: Why is the CIA Triad in the shape of a triangle?
A: Why is the CIA Triad in the shape of a triangle?
Q: Create a .m Script that can transpose the given column vector named vtr1 = [2; 6; 4; 2; 9] and vtr2 ...
A: As given, we need to write a Matlab program that transpose the given column vectors into row vectors...
Q: how do you undone concatenation. for example lets say i have the following encryption algorithm: E...
A: assuming that the limit is based on the size of allocated memory, concatenation causes undefined beh...
Q: Explain the components of the spheres of security paradigm in detail. Each component should be expl...
A: Here is the detailed explanation of the solution
Q: To protect the sound quality of phone calls over a DSL network, what device must be installed?
A: To protect the sound quality of phone calls over a DSL network, what device must be installed?
Q: ow do security models like Biba, Bell LaPadula as it relates to the CIA triangle. E.G. Bell LaPadula...
A: Lets see the solution.
Q: 1. Let x ∈ Z. Use a direct proof to show that if 5x2 + 8 is odd then x is odd. 2. Show by contrapo...
A: 1) Given 5x2+8 is odd which implies 5x2 is odd as the sum of any odd and even is odd. so 5x2 is odd...
Q: Assume that x is a char variable that has been declared and already given a value. Write an expressi...
A: The relational operators in C language are the operators that are used for comparing a value with an...
Q: Explain on Emerging technology I. Voice recognition - II.Touch screen III.Data file interrogation IV...
A: Voice recognition technology was first used in the 1950s. It now has moved into the mainstream with ...
Q: Perform the following Infix expressions to Prefix, Postfix and Binary Tree (for visualization) 15po...
A: Postfix:- x y * z+ Input String Output Stack Operator Stack x * y + z x x * y + z x ...
Q: perform addition and subtraction to 10 signed bit numbers 0001111110 and 1110101100 complete soln
A: Note that in the binary system: Binary Addition 0 + 0 = 0 0 + 1 = 1 1 + 0 = 1 1 + 1 ...
Q: 2. Which of the following CANNOT be expressed using one bit? a) The state of an ON/OFF switch b) The...
A: Answer is: d) The position of the hour hand of a clock
Q: What is an Internet of Things (IoT) and when may it be useful?
A: IOT is very very useful and widely spread domain across the world and computer industry . As we alr...
Q: Over a Metro Ethernet connection, what protocol can deliver VoIP services?
A: Introduction: VoIP (Voice over Internet Protocol) or internet telephony is the term for voice commun...
Q: Consider the following network with sigmoid activation functions in the hidden and output neurons, a...
A: Actually, given question regarding networking.
Q: 2. Evaluate the following computation in embedded C program using XC8 Compiler and explain the reaso...
A: 1: In c language write a program and perform the following operations Unsigned char t; Calculate t=1...
Q: In the code given below, the values of installment1.dueDate and installment2.dueDate is getting prin...
A: Debug the given JavaScript code such that there is a difference of 5 months in the dueDate of the ob...
Q: Use Common Table Expressions (CTE) to write a query that displays the sum of all purchase orders and...
A: Common Table Expression (CTE) Common Table Expression is nothing but a temporary result set. We can ...
Q: What are the Consequences of a Lack of Communication Devices?
A: Introduction: A communication device is a piece of hardware that can send an analog or digital signa...
Q: What are the goals of information security in the digital age? Give a brief explanation.
A: Introduction: In a word, digital security is the protection of your computer, mobile devices, tablet...
Q: What are the many kinds of operating system programmes? To demonstrate your idea, provide three to f...
A: The kernel is the name given to the most significant programme in the collection. During the boot pr...
Q: Construct dfas that accept the followings: a. Set of all strings on {0,1} that do not contain two co...
A:
Q: Suppose you have already developed an SLL ADT. You have to search a specific element of the linked l...
A: void function(int item) { struct node *ptr; int i=0,flag; ptr = head; i...
Q: Explain your personal knowledge of In-House Development in your own words.
A: Answer : A group of individual dwellings or apartment houses typically of similar design are usuall...
Q: I have my code below and I am stuck at the last part which is the display of the thread that finishe...
A: The Answer is
Q: In order to study SNMP logs, which file must be opened?
A: Introduction: The SNMP log file contains clear messages for all SNMP requests. All SNMP log files a...
Q: How is indexed versus based addressing different?
A: Given To know about the indexed addressing and based addressing
Q: Write a Python program to get the geometric mean of n numbers. Take the n numbers from the user.
A: Required:- Write a Python program to get the geometric mean of n numbers.Take the n numbers from the...
Q: Explain artificial intelligence explain in details machine learning and deep learing
A: Given To know about the 1) artificial intelligence 2) machine learning 3) deep learing
Q: How I can open file txt in my computer
A: TXT files in Windows may be opened using the built-in Notepad software by right-clicking the file an...
Q: What intangible advantages may a company get from the creation of an IS?
A: Introduction: A formal, sociotechnical, organizational system designed to gather, process, store, an...
Q: What's the difference between Geo DNS and Latency Based Routing?
A: Latency-based Routing to have the fastest response. Geolocation maps the IP addresses to geographic ...
Q: Question 3: Complete a Simulation table for checkout counter using the Event Scheduling/ Time Advanc...
A: The answer of this question is as follows:
Q: Write a running C++ code for a class named Student that make use of the public and private functio...
A: Algorithm: Start Create a class named Student Inside the class, implement a private function named ...
Step by step
Solved in 2 steps with 5 images

- Substitution ciphers are encryption/decryption algorithms that replace one letter or number with another. The first attested use of a substitution cipher in military affairs was by Julius Caesar, described by him in Gallic Wars (cf. Kahn pp83-84). In caesar cipher , you replace each letter by 3rd letter on. If it is out of bound (later than Z), then round to the head (letter A) and continue the shift. For example:meet me after the toga party PHHW PH DIWHU WKH WRJD SDUWB Please write a program in Java to implement the Caesar Cipher: a. Implement the encryption algorithm. Ask the user to input one all lower case normal sentence (called plaintext) using the nextLine method, and then output the encrypted text (called ciphertext). b. Implement the decryption algorithm. Ask the user to input one encrypted sentence (i.e. ciphertext) using the nextLine method, and then output the decrypted text (i.e. plaintext).Please assist with explaining what exactly is happening when replacing A. The answer is yes that an error occurs, just need assistance with explaining the error and why it is not compliling.using python Construct an experiment to determine what percentage of attempts will be pairs, when 2 cards are pulled from a full deck. • Notice that means that mod 13 will give a number from 0-12, and can be used to identify whether two cards are a pair. • Write several short functions, rather than one long block of code. • A deck of cards can be represented by the numbers 0-51, where 0 - 12 are one suit, 13-25 a second suit, 26-38 a third suit, and 39-51 a fourth suit. • Count what percentage of 1000 attempts are pairs.
- Show the string that would result from each of the following string formatting operations. If the operation is not legal, explain why.171a) "Looks like {1} and {0} for breakfast " . format ("eggs" , "spam")b) "There is {0} {1} {2} {3}" . format (! , " spam" , 4, "you" )c) "Hello {0}" . format ("Susan" , "Computewell")d) " {0:0.2f} {0 :0.2f}" . format (2 . 3, 2 . 3468)e) " {7 . 5f} {7 . 5f}" . format (2 . 3, 2 . 3468)f) "Time left {0 : 02}:{1 : 05.2f}" . format ( 1 , 37 . 374)g) " {1:3}" . format("14")Correct answer will be upvoted else downvoted. Computer science. string a matches an example b if for every I from 1 to k either bi is a special case character or bi=ai. You are approached to improve the examples so that the primary example the j-th string matches is p[mtj]. You are permitted to leave the request for the examples unaltered. Would you be able to perform such an improvement? Assuming you can, print any legitimate request. Input The primary line contains three integers n, m and k (1≤n,m≤105, 1≤k≤4) — the number of examples, the number of strings and the length of each example and string. Every one of the following n lines contains an example — k characters that are either lowercase Latin letters or highlights. All examples are pairwise unmistakable. Every one of the following m lines contains a string — k lowercase Latin letters, and an integer mt (1≤mt≤n) — the record of the main example the relating string should coordinate. Output Print "NO"…Consider the following procedure: procedure mystery (x, y, z); integer x, y, z;beginz = 2; y= z+x;endand consider the following code fragment: A[1] := 2;A[2] := 1;n := 1;mystery (A[1],A[n],n); What will be the final values of n, A[1] and A[2] if the parameters are passed by name?
- Consider the following procedure: procedure mystery (x, y, z); integer x, y, z;beginz = 2; y= z+x;endand consider the following code fragment: A[1] := 2;A[2] := 1;n := 1;mystery (A[1],A[n],n); What will be the final values of n, A[1] and A[2] if the parameters are passed by value?I did part A but I really need all parts of part B answered I want the code to continue after 0 with negative numbers and I need the guesses to show up at the end that shows how many guesses it took before the user ran out of points. import java. util.Random; import java.util. Scanner; import java.util.regex.*; public class HiLOGame{ public static void main( String(] args){ final int MAX POINT = 1000- int point = MAX POINT: int numberOfGuess = 0; do { numberOfGuess++: showStatus(point); int point ToRisk = getPointToRisk("Enter point to risk? ", point); String option = getHiLoOption ("Enter either Hi or Lo?"); int magicNumber = getMagicNumber(1, 13); /I for debug //System.out.printf(String.format ("Magic number: %d%n",. magicNumber)); if (isWon(option, magicNumber)) { point += pointToRisk: System.out.printin("You Won this game."); } else f point -= pointToRisk: System.out.printin("You Lost this game."); } }while (point > 0): report(MAX POINT, numberOfGuess); System.exit(0); }…this should be done in C Our method will involve analyzing a string and picking the 5 most common letters in that string. We will then compute how far each of these is from the letter ‘e’. We will then produce 5 possible decryptions of the string by: Decryption 1 will be from comparing how far the most popular letter is from the letter “e” Decryption 2 will be from comparing how far the second most popular letter is from the letter “e” Decryption 3 will be from comparing how far the third most popular letter is from the letter “e” Decryption 4 will be from comparing how far the fourth most popular letter is from the letter “e” Decryption 5 will be from comparing how far the fifth most popular letter is from the letter “e”
- Correct answer will be upvoted else downvoted. Computer science. in the event that |a|>0 (the length of the string an is more prominent than nothing), erase the principal character of the string a, that is, supplant a with a2a3… an; in the event that |a|>0, erase the last character of the string a, that is, supplant a with a1a2… an−1; if |b|>0 (the length of the string b is more prominent than nothing), erase the main character of the string b, that is, supplant b with b2b3… bn; in the event that |b|>0, erase the last character of the string b, that is, supplant b with b1b2… bn−1. Note that after every one of the tasks, the string an or b might become vacant. For instance, in the event that a="hello" and b="icpc", you can apply the accompanying grouping of tasks: erase the principal character of the string a ⇒ a="ello" and b="icpc"; erase the primary character of the string b ⇒ a="ello" and b="cpc"; erase the principal character of the string b ⇒…Five members of an obesity club want to know how much they have lost or gained weight since the last time they met. To do this, they carry out a weighing ritual where each one is weighed on ten different scales in order to have a more accurate average of their weight. If there is a positive difference between this average weight and the weight of the last time they met, it means that they gained weight. But if the difference is negative, it means that they lost weight. What the problem requires is that for each person a sign is printed that says "went up" or "under" and the amount of pounds Write a program in c++ using for, do while or while. Initial weights 230, 240, 180, 300 and 350. Do not use arraysFive members of an obesity club want to know how much they have lost or gained weight since the last time they met. To do this, they carry out a weighing ritual where each one is weighed on ten different scales in order to have a more accurate average of their weight. If there is a positive difference between this average weight and the weight of the last time they met, it means that they gained weight. But if the difference is negative, it means that they lost weight. What the problem requires is that for each person a sign is printed that says "went up" or "under" and the amount of pounds. Write a program in C++ that uses a function. The user must enter the initial weight and the 10 weights of the scales. Please do not use arrays or vector











