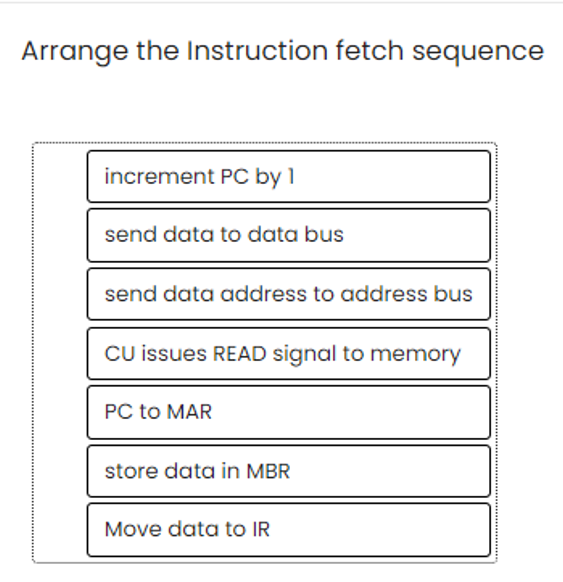
Arrange the Instruction fetch sequence
Q: How do you monitor ospfd in real time to see system status and activity, or debug problems?
A: OSPF (Open Shortest Path First) is a routing protocol that is widely used in enterprise networks.…
Q: What, in your opinion, are the characteristics of a good computer language?
A: A computer language is a system of rules and symbols that enables humans to command computers to…
Q: Suppose that we have the following stack, where the red line is the indicator for sp. The stack…
A: stack downwards in main memory, just as it does in a regular RISC-V main memory. Both Wordo and…
Q: It's possible to illustrate and explain the differences between a low-level programming language and…
A: The answer is given in the below step
Q: Use the eig function from the numpy linalg library in Python to get the eigenvalues and eigenvectors…
A: Python code that uses the numpy linalg library to determine a matrix's eigenvalues and eigenvectors.…
Q: What advantages does using a more advanced word processor like Word 2016 have over using something…
A: Using a more advanced word processor like Word 2016 over something like Notepad has several…
Q: PYTHON/ JUPYTER NOTEBOOKS a) Import the following reaction mechanism for acetaldehyde pyrolysis ,…
A: Introduction: In this question, we are asked to import and display a reaction mechanism for the…
Q: Linux is a piece of software that has its source code available to the public. Using just your own…
A: Open source software is software whose source code is freely available to the public. This means…
Q: Blogs about social networking and cloud computing are both major subjects that need your undivided…
A: Inspection: Learn as much as you can about social networking blogs and cloud computing. Using social…
Q: 1.Which of the following is a type of malware that is designed to spread from one computer to…
A: Worms(3rd Option) are a type of malware that can spread from one computer to another without any…
Q: In the context of a computer with a confined instruction set, what does it mean for anything to be…
A: 1) A computer with a confined instruction set is a type of computer architecture in which the set of…
Q: 2. A box contains three fair coins, and two trick coins that have heads on both sides. (a) What is…
A: We need to first determine the probability of selecting each type of coin, and then use the law of…
Q: To you, the following characteristics are essential in a great programming language.
A: Answer to the given question: There are many characteristics that can make a programming language…
Q: hat was used for the protocol of the Internet of Things. Examine the Internet of Things (IoT)…
A: Introduction: Standardization is a major IoT challenge without global a standards, the complexity of…
Q: Why aren't the most crucial ideas being applied to software development?
A: The process of planning, creating, and testing software applications is known as software…
Q: A A E 0 B B True Bo Numeric 3 stop DE Amay 3 Bur False Which the following answers describes the…
A: While loop is used to execute a block of code repeatedly until a given condition is true. Syntax:…
Q: What difficulties do SPEC CPU benchmarks solve compared to Whetstone, Dhrystone, and Linpack?
A: SPEC CPU benchmark addresses deficiencies in the Dhrystone, Whetstone, and Linpack benchmarks:…
Q: Because of the advent of machine learning, data structures and algorithms are becoming less…
A: The statement is False. The advent of machine learning does not diminish the importance of data…
Q: Nevertheless, most computer systems use fewer layers than what the OSI model recommends. [Reference…
A: The acronym "OSI" refers to the layers of the model used by (Open Systems Interconnection Model).…
Q: Write the program tail, which prints the last n lines of its input. By default, n is 10, let us say,…
A: The following is an example of a software tail: 1. Collect the user's feedback. This can be…
Q: Please elaborate on the distinction between program production and delivery and custom software…
A: Program production and delivery refer to the process of creating a software program that is…
Q: When using Verilog code, what may happen if more than one of the "AN" inputs is activated? Please…
A: A text-based language called Verilog is used to describe electronic circuits and systems. Verilog is…
Q: Linux lets users share time and resources. Does this system protect well
A: LINUX is open source which means you can download it and use it for free. It is mostly used by…
Q: Pandas is a Python library used for working with data sets. It has functions for analyzing,…
A: Yes pandas has both advantage and disadvantage, this has been explained below.
Q: Write versions of the library functions strncpy, strncat, and strncmp; which operate on at most the…
A: Answer :
Q: The OSI model contends that, with a few notable exceptions, most computer systems don't really need…
A: The OSI is the conceptual framework that outlines how network protocols and communication should…
Q: What are the benefits of using a backup solution that is hosted in the cloud?
A: Please find the answer below :
Q: A 'SubWay' sub order has many items that may be included on the order. The order may contain choices…
A: Below is an Entity-Relationship Diagram (ERD) that models the entities, attributes, relationships,…
Q: Just why is it necessary to learn how to code? To what extent should one program at the highest…
A: There are many reasons why it is necessary to learn how to code. Computers are omnipresent and…
Q: The authority that comes with each job or position is different. Moreover, with power comes a heavy…
A: Software engineers should commit to making Software analysis, specification, design, development,…
Q: What do you think are the most fundamental concepts that CS majors should know?
A: Computer science studies computing and its theoretical and practical applications. Computer science…
Q: Whenever is the best moment to improve the network?
A: The best time to improve a network depends on a variety of factors, including the current…
Q: What makes Interrupt stand apart from a regular interruption is its name. Explain why problems with…
A: Interrupts - Interrupts are basically generated by hardware during program execution. They can…
Q: Provide illustrations of data manipulation, fraudulent activity, and online theft.
A: Data diddling: The term "data diddling" refers to the practise of making unauthorised changes to…
Q: Why did engineers develop the RISC architecture?
A: The RISC computer architecture The Reduced Instruction Set Architecture (RISA) standard specifies…
Q: What does a challenge-and-response authentication method mean exactly? (CRAS). Why is this technique…
A: The answer to the question is given below:
Q: It's possible that simulators will be able to accurately represent two major problems.
A: Whether or not simulators can accurately represent various problems depends on factors such as the…
Q: information may go along the address bus?
A: The address bus is a crucial component of the computer's architecture that enables the CPU to…
Q: What is the Prototype Design Pattern, and what are its main characteristics and benefits?
A: performance of your application and reduce the number of object creation requests sent to the…
Q: hat constitutes pl
A: Plagiarism is defined as the illegal use of another's ideas without proper attribution. Plagiarism,…
Q: How does computer science differ from other academic fields, and what does it really entail? How…
A: The differences between computer science and other subjects are addressed below. Computer science…
Q: A more thorough understanding of the metrics related to the software development process would be…
A: Metrics related to the software development process are crucial for understanding and improving the…
Q: it says relation hotel already exist
A: It seems you are trying to create a relation or table in a database, and you are receiving an error…
Q: A box contains three fair coins, and two trick coins that have heads on both sides. (a) What is the…
A: (a) To calculate the probability that a randomly selected coin from the box will come up heads when…
Q: Reading blogs is an excellent way to get knowledgeable about important subjects like cloud…
A: In the branch of computer science known as peer-to-peer social cloud computing, computing resources…
Q: What's the point of being able to define an initial value when you can simply assign a value to a…
A: Dear Student, The detailed answer to your question is given below -
Q: Internet access for disabled? Which new tech will help handicapped people? How?
A: Answer: There are a variety of technologies available that can help people with disabilities access…
Q: How can we best address the most pressing barriers to software reuse, both technological and…
A: Software reuse is crucial for reducing development time and cost, increasing software quality, and…
Q: l in the clear in the code cell beneath for part d, if it's not too much trouble, utilize your own…
A: This code solves a system of linear equations using the NumPy library in Python. The equations are…
Q: Do rookie mistakes occur in the software development process? Explain?
A: Introduction: Reversible software development: The transaction must be finished in its entirety or…
Step by step
Solved in 2 steps

- Two 1-bit values generate a 1 result value when a(n) _____ instruction is executed. All other input pairs generate a 0 result value.Identify the addressing modes used for the source and the destination operands in the instructions thatfollow :(a) MOV AL, BL(b) MOV AX, 0FFH(c) MOV [DI], AX(d) MOV DI, [SI](e) MOV [BX]+0400H, CX(f) MOV [DI]+0400H, AH(g) MOV [BX][DI]+0400H, AL124 An AVR JMP instruction is stored in _____ bytes of on-chip program ROM. An AVR RJMP instruction is stored in _____ bytes of on-chip program ROM. After the execution of the OUT DDRC , 0xED instruction, which pins of PORT C are inputs?
- "When Su is low, it will perfrom subtraction" True False Instruction register accepts data from the Wbus when iLoad is 1 True False When INOUT act as input port, the control signal is" iClk iReset iEnable iLoad The ___ nibble of the instruction register is a three-state output that is read onto the bus when needed.If R12 contains the value 0x4000 and register R8 contains the value 0x20, the effective address (EA) of the instruction LDR R9, [R12, R8, LSL #1] is ___________. A. EA = 0x4000 B. EA = 0x4020 C. EA = 0x4080 D. EA = 0x4040 E. EA = 0x3FC0Give the starting code memory location and the machine code in hexadecimal : The instruction are for the ATmega32 - .ORG 0x0000 - LDI R30, 0x19 - LDI R31, 0xA5 - ADD R30, R31
- Explain the operation of the each of the following instructions of 8051 microcontroller. (i) MOV R1,#35H (ii) XCHD A, @R1 (iii) DEC 15H (iv) SWAP A (v) SETB 00H (vi) CLR Cliomework: Identify the addressing modes used for the source and destination operands, and then compute the physical address for the specified orx•rand in each of the following instructions: a) Mov +XYZ,AH (Destination operand) b) Mov tBX) (Destination operand) Suppose that BX=030016, 010016.Identify the addressing modes used for the source and destination operands, and thencompute the physical address for the specified operand in each of the following instructions:(Assume all missing data.)1. MOV CX, [DI] (Source operand)2. MOV [BP]+BETA, AX (Destination operand)3. XCHG BX, [FF02] (Source operand)
- An ADD instruction stores a value 7308h at offset value 9F71h. If the computed address is 7CB31h, what will be the ending address? Assume real mode operation a. 82BBFH b. 72BC0H c. 73BBFFH d. 7CB31HBuild C program to perform task below. Design its circuit in Proteus. State your observations.a) Make Port D produce 5V. Use bit addressable instructions.b) Make pin RB7, RB5, RB3 and RB1 ON and other Port B pins OFF. Use byte addressableinstruction.c) Make RE0, RA1, RB2, RC3 and RD4 HIGH.result discussion conclusionAn ADD instruction stores a value 7308h at offset value 9F71h. if the computed address is 7CB31h, what will be the starting address? Assume real mode operation a. 72BC0 b. 72BC00 c. 82BBF d. 82BBF0

