As one developer on a team of several developers of a large web application using the Spring framework, you are tasked with implementing an expressive command input function for the application. You are told the team is using version 2.6.5 of the Spring framework, and you want to use the Spring Expression Language to accomplish your task. Using the Vulnerability Assessment Process Flow diagram, identify which of the seven areas of security best apply to the scenario above. Select all that apply. Input Validation: Secure input and representations APIS: Secure API interactions
As one developer on a team of several developers of a large web application using the Spring framework, you are tasked with implementing an expressive command input function for the application. You are told the team is using version 2.6.5 of the Spring framework, and you want to use the Spring Expression Language to accomplish your task. Using the Vulnerability Assessment Process Flow diagram, identify which of the seven areas of security best apply to the scenario above. Select all that apply. Input Validation: Secure input and representations APIS: Secure API interactions
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:James Kurose, Keith Ross
Chapter1: Computer Networks And The Internet
Section: Chapter Questions
Problem R1RQ: What is the difference between a host and an end system? List several different types of end...
Related questions
Question
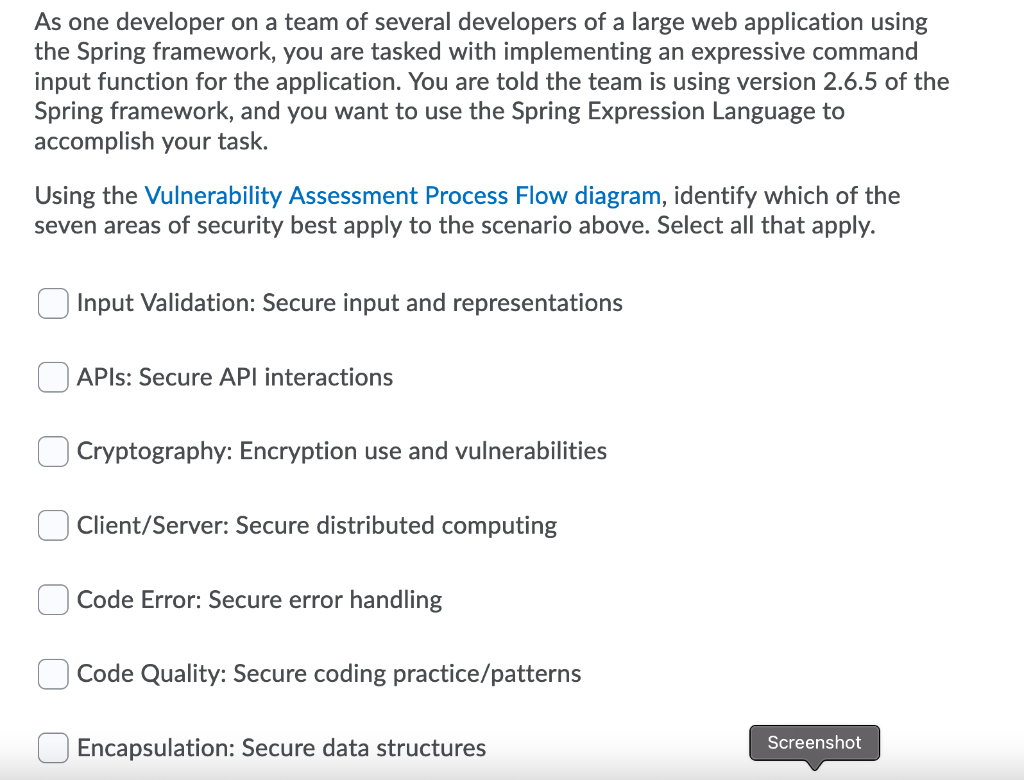
Transcribed Image Text:As one developer on a team of several developers of a large web application using
the Spring framework, you are tasked with implementing an expressive command
input function for the application. You are told the team is using version 2.6.5 of the
Spring framework, and you want to use the Spring Expression Language to
accomplish your task.
Using the Vulnerability Assessment Process Flow diagram, identify which of the
seven areas of security best apply to the scenario above. Select all that apply.
Input Validation: Secure input and representations
APIS: Secure API interactions
Cryptography: Encryption use and vulnerabilities
Client/Server: Secure distributed computing
Code Error: Secure error handling
Code Quality: Secure coding practice/patterns
Encapsulation: Secure data structures
Screenshot
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Recommended textbooks for you

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:
9781337093422
Author:
Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:
Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:
9780133750423
Author:
VENIT, Stewart
Publisher:
Pearson Education

Sc Business Data Communications and Networking, T…
Computer Engineering
ISBN:
9781119368830
Author:
FITZGERALD
Publisher:
WILEY