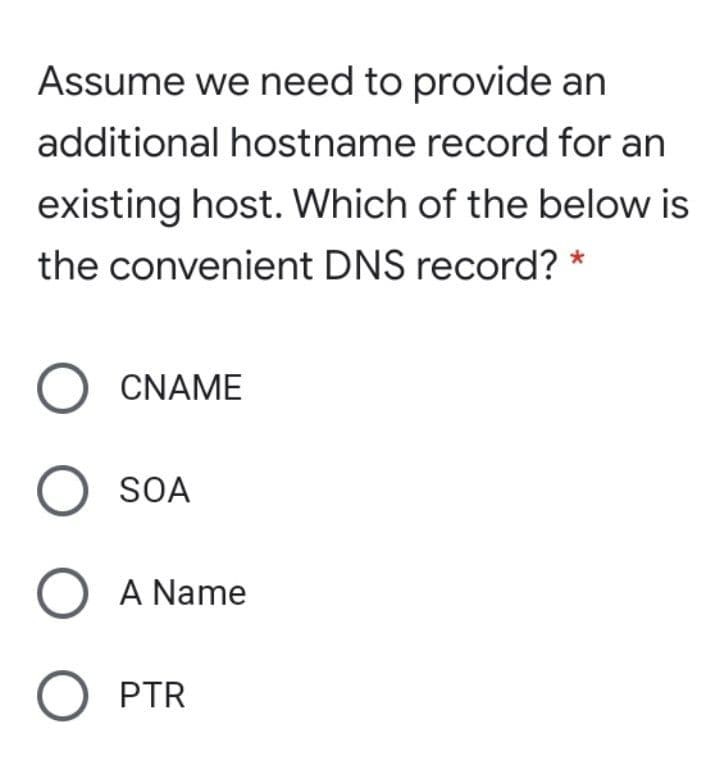
Assume we need to provide an additional hostname record for an existing host. Which of the below is the convenient DNS record?
Q: Consider the case when two end hosts communicate remotely, through multiple intermediate network…
A: Here the correct option is Information the router's CPU uses to select the best path between the…
Q: What does a datagram header's Time-to-Live (TTL) field indicate? O The time in which a HTTP cookie…
A: Solution:
Q: In which of the following scenarios, the packet will be forwarded directly to the destination host…
A: In computer networking, a default gateway helps in passing signals through the default route between…
Q: Q9- DHCP Operation between Client and Server is done in the following sequence: * a. DHCP Discover,…
A: As per our policy, "Since you have asked multiple questions, we will solve the first question for…
Q: Host A sends a UDP datagram containing 8880 bytes of user data to host B over an Ethernet LAN.…
A: Given: UDP data= 8880 bytes UDP header= 8 bytes IP header= 20 bytes
Q: Assume that routing works in the diagram shown below. PC1 sends an ICMP ECHO request to PC2. Which…
A: For sending data packets from one system to another system, intermediate routers are used. These…
Q: We have the information shown below. Show the contents of the IP datagram header sent from the…
A: IP datagram is that Carries an IP packet from network to network and it is the essential element of…
Q: In which of the following ICMP messages, the possible sender is the destination host. 1.type:…
A: type 1 - host is unreachable type 2 - protocol is unreachable type 3 - port is unreachable
Q: The Secure Sockets Layer (SSL) protocol may handle a broad variety of different protocols. Are…
A: Support for HTTPS in SSL and Transport layer security.TLS is a network protocol that establishes a…
Q: In order to move packets from host A to host F, we need: End Intermediate system system End Link…
A: the host A will send the data to host F having the IP address of host F as well as it's own IP…
Q: Assuming NKU has a subnet in Griffin Hall with subnet mask 255.255.255.224. What is the maximum…
A:
Q: a. Find the subnet mask b. How many valid hosts are created? c. Find the first and last host address…
A: The answer is
Q: Which of these HTTP headers is used by a web cache in deciding whether an object needs to be…
A: The answer is given below:-
Q: Suppose a user has a webserver running at a machine with the name www.nadir.edu.net.pk and IP…
A: Suppose a user has a webserver running at a machine with the name www.nadir.edu.net.pk and IP…
Q: An organization is granted the block 150.100.50.0 /24. The administrator wants to create 64 subnets,…
A:
Q: Write client-side code that asynchronously makes a request to obtain json data from local host…
A: Write client-side code that asynchronously makes a request to obtain json data from local host…
Q: associated with the link contains a small amount of HTML text, and it references to 8 very small…
A:
Q: Assume Host C runs a Web server on port 80. Assume that this Web server accepts requests from Hosts…
A: INTRODUCTION: WEB SERVER: It connects to the Internet and facilitates the exchange of biological…
Q: Host h5 10.3.0.5 OpenFlow controller Host h6 10.3.0.6 Host h7 10.4.0.7 s3 $4 Host h4 10.2.0.4 Host…
A: Answer: Our instruction is answer the first three part from the first part and we have given answer…
Q: Lapfopo Lapop2 120 hosts Switcho 61 Hosts vitch 1 30 Hosts 15 Hosts Swich2 Swich3 R2 R3 Sample MAC…
A: Given the following topology.By calculating a network address yourself(Calculation process:First…
Q: 2. Based on the number of hosts in the topology, you need to calculate the NIDS and FHID,LHID, BID,…
A: 172.16.0.0/16 Here we will assign one by one bits for each subnet. Here the number of network bits…
Q: The following packet captured by Tcpdump shows "win 512" which indicates ___________________.…
A: 09:32:43:9147882 This is the time stamp in the format of two digits for hours, two digits for…
Q: Host A sends a UDP datagram containing 8880 bytes of user data to host B over an Ethernet LAN.…
A: The Answer is in Below steps
Q: Assume that hosts S1 and S2 have IP addresses, 200.100.50.10 and 200.100.50.32 respectively. They…
A: An Internet Protocol (IP) address is used to connect to the Internet and identify devices so that…
Q: What does it mean when someone refers to DHCP, or dynamic host configuration protocol
A: Please find the answer below
Q: The maximum value of a TTL for a DNS resource record (RR) is 2147483647 seconds. What is the primary…
A: The answer is
Q: Suppose a DNS resource record has the type of MX. Then the value of the record is .
A: Introduction: DNS represents the domain name system, it is nothing but like a phonebook of the…
Q: Question 1: Which of the followings are characteristics for RADIUS or TACACS+ servers? It uses TCP…
A: Question 1 and Question 2 answers are given below
Q: Check all of the phrases below that state a true property of a local DNS server. Group of answer…
A: Following are the True Property of a local DNS server : 1) The local DNS server can decrease the…
Q: When running a scan on your computer, you find that a session has been established with a host at…
A: Application Layer: In the Open Systems Interconnection (OSI) model and Transfer Control Protocol/…
Q: What is the maximum number of IP addresses that can be assigned to hosts on a local subnet that uses…
A: In this question we are asked give the answer of three MCQs Given: 1st MCQ is related to IP…
Q: An attacker is sending packets to the target with the URG flag set in order to scan the target…
A: a) type of scanning b) target port respondence if port is open c) response if target is closed
Q: Q10: Complete the frames (x & y) given below with appropriate port, IP and MAC addresses. The sender…
A: Actually, IP stands for Internet Protocol.
Q: Complete the frames (x & y) given below with appropriate port, IP and MAC addresses. The sender Host…
A: NOTE: IP has been assumed as shown in the question. For actual IPs. We can make 3 subnets, each with…
Q: In Class B, If the subnet mask is 255.255.128. 0, Explain in detail how you will find the CIDR…
A: Given : Class of network : Class B Subnet Mask : 255.255.128.0 For class B, IP addresses are in…
Q: What are the source and destination IP addresses of the frame's network-layer header? Is this an…
A: Source IP: 192.168.1.121Destination IP: 52.114.128.71
Q: If DNS searching happens once every 10 minutes, and each time the HTTP file references 8 items, how…
A: Introduction : HTTP mostly relies on TCP for its transport protocol , providing a…
Q: e a session with a host at 208.85.40.44:443. For this session, what protocol is being used?
A: HTTP HyperText Transfer Protocol (HTTP) is an acronym that stands for HyperText Transfer…
Q: What is the purpose of including the 'Host' attribute in the communication specified by the HTTP1.1…
A: Introduction: The Host request-header specifies that the server to which the request is being…
Q: Which one of the following is a cryptographic protocol used to secure http connection ? a) Stream…
A: cryptographic protocol is an abstract or concrete protocol that uses for a security-related function…
Q: What is the MAC address associating with your default gateway? Please provide a snapshot to show how…
A: It is defined as Media Access Control which is the physical address, which uniquely identifies each…
Step by step
Solved in 2 steps

- Write a small program/script to resolve all DNS hostnames of Southeastern's ranging from 0 to 255 for the third and fourth octet in 147.174.$i.$j/16. Use any language you like (Bash, PowerShell, Python, Java). Paste the contents of your program below.To test DNS configuration by resolving a host name to an IP address, which commandor commands can you use? (Choose all that apply.)a. nslookup hostnameb. dig hostnamec. host hostnamed. resolve hostnameYou have sent a file from Host A to Host B, in which format that file will be received at Application layer? a. Packets b. Segments c. Data d. Frames
- A.Which of the following protocols keeps all potential paths active while managing the flow of data across the paths to prevent loops? 1.TRILL 2.CARP 3.SPB 4.RSTPDistinguish between DNS records of different kinds. Each of them will be briefly discussed, with examples and arguments provided for their application. Having the same hostname alias for both your web and mail servers is feasible inside the same company.Write client-side code that asynchronously makes a request to obtain json data from local host running at port 3456 at url “/books” using a saga.
- Write a snort rule to generate an alert for the following: search for the word “HTTP” in the first 20bytes of the payload of a packet that is originating in subnet (192.168.34.0/24) and going toyour subnet (192.168.56.0/24). The alert should read: “HTTP detected”. Could you please also include the nmap command used to scan the target?A single link between two hosts can be used to send more than one file. Please tell me when shipments can be cleared. Is there a set amount of time for one wait and some flexibility with the other?Suppose a client sends an HTTP request message with the If-modified-since header. Sup- pose the object in a server has not changed since the last time a client retrieved the object. Then the server will send a response message with the status code: A. 200 OK B. 404 Not Found C. 304 Not Modified D. none of the above
- Assume a web server can only receive TCP connections on port 80 (HTTP) and 22 (SSH), but not on any other ports. The web server can only establish connection to a database server hosted on private IP 192.168.100.100 on port 3000, but to no other machines inside or outside the network. Imagine this web server is running Linux, and we’re using iptables to define host-based firewall rules for it. Show the set of iptables commands to install necessary rules for this security policy.An attacker tries to do banner grabbing on a remote web server and executes the following command:$ nmap -sV hackme.com -p 80 He gets the following output:Starting Nmap 7.90 ( http://nmap.org ) at 2020-09-26 22:47 ESTNmap scan report for hackme.com (108.58.137.114)Host is up (0.048s latency).PORT STATE SERVICE VERSION80/tcp open http Apache httpdService detection performed. Please report any incorrect results at http://nmap.org/submit/.Nmap done: 1 IP address (1 host up) scanned in 7.36 seconds What did the hacker accomplish? nmap can’t retrieve the version number of any running remote service. The hacker successfully completed the banner grabbing. The hacker should have used nmap -O host.domain.com. The hacker failed to do banner grabbing as he didn’t get the version of the Apache web server.Suppose a user has a webserver running at a machine with the name nadir.edu.net.pk and IP address 10.10.10.10. The authoritative DNS address for this web server is with the name dns.nadir.edu.net.pk and with IP address 11.11.11.11. Write all the steps involved in retrieving the IP address of nadir.edu.net.pk

