AUTHENTICATION SYSTEM HHHH PK Loginld INTEGER password VARCHAR(20) PUBLISHER login +H manages A STAFF PK staff_id INTEGER name VARCHAR(50) maintains BOOK HP REPORTS Reg_no Userld Book no Issue/Retum date keeps track of + K RESERVE/RETURN PK NUMBER NUMBER NUMBER DATE HH +H 7 READER
Q: What is the name of the memory resident components of the operating system? When are these elements…
A: Introduction: Drivers for the kernel and other components of the system
Q: . When compared to the probabilistic IR model, how does the vector space IR model fare?
A: One of the earliest model in IR is probabilistic approaches.They were hailed as the easiest way to…
Q: What precisely does "programming a computer" imply? What factors should be considered before…
A: . Computer programming is a way of giving computers instructions about what they should do next.…
Q: What exactly is the distinction between MIME and S/MIME in the world of cryptography?
A: Intro S/MIME, or Secure/Multipurpose Internet Mail Extensions, is a technology that is generally…
Q: When someone mentions "programming a computer," what exactly do they mean? What elements must be…
A: Intro A programming language is a set of rules for translating text to machine code, or graphical…
Q: What types of data does a business keep track of? Should people be concerned about their online…
A: Companies, however, collect data not just via your online browser, but also through cellphones and…
Q: Explain why making use of the normalised Index metadata relation will result in a decrease in the…
A: There are different typical structures in the RDBMS, for example, 1NF, 2NF and so on and there is an…
Q: What actions are taken to ensure the data's integrity?
A: The steps involved in ensuring the integrity of the data is listed below.
Q: Introduce object-oriented analysis by emphasising the importance prototypes play in the process and…
A: Intro The object-oriented analysis will be the topic of our conversation on the provided challenge.
Q: In the context of computers, what exactly is the difference between architecture and organisation?
A: Computer Architecture: The contrast between computer architecture and computer organisation that…
Q: As a result of advances in technology, almost all modern appliances are equipped to communicate…
A: Wireless communication is the transport of information between two or more sites without a physical…
Q: Compared to stepwise regression, all-subsets regression offers many advantages.
A: Introduction: Best subsets regression is sometimes called "all possible regressions" The procedure's…
Q: We are going to investigate Windows Service Control Manager and discover what benefits it offers to…
A: Encryption: An OS feature named Service Control Manager (SCM) launches, stops, and interacts with…
Q: Discuss the security threats in depth and explain why some of them are specific to wireless systems.
A: Introduction: A security threat is a malicious act designed to harm or steal data from an…
Q: Jump to level 1 valsTable: o 10 1 2 3 4 5 6 7 8 9 38 Empty-since-start Empty-after-removal Occupied…
A: Given Has function is key % 10 Hence when we put key in slot we put at place of key % 10 th place.…
Q: A cassette drive is a classic cassette recorder that is used for storing data on a computer or…
A: Intro A cassette drive is a classic cassette recorder that is used for storing data on a computer…
Q: Could you kindly point me in the direction of the appropriate site so that I may learn more about…
A: Launch: Service Control Manager (SCM) is a unique process in the Windows NT family of operating…
Q: The expansion bus connects the CPU to peripheral devices that are attached to it via interface…
A: Introduction: A computer's extension bus transfers data between the computer's internal hardware…
Q: The development of an application that makes use of a range of distinct techniques is something that…
A: Beginning: As websites and web applications have become more powerful and intricate, the necessity…
Q: What does it mean to reap a process, and why does it need to be reaped?
A: Introduction: Reap the benefits of a process while also understanding why you're reaping the…
Q: Explain when, and why, you would prefer time-sharing processing over batch processing.
A: The Answer is in step2
Q: The idea of a memory hierarchy is broken down into its component parts in this section. How did you…
A: The strategy by which elite execution is given by prudent means by current PCs through the…
Q: You will find a breakdown, for your convenience, of the differences between Java's Entity Beans and…
A: Session Beans in this article: A component of an enterprise bean written in EJB 3.0 or EJB 2.1 that…
Q: Too many services running and too many icons in the taskbar's notification area may cause problems…
A: The following will be determined: If too many services are operating on the Windows system, as…
Q: How has the advent of technology altered human behaviour with regard to the protection of digital…
A: Overview: Consider how the internet has altered our social relationships. We now communicate mostly…
Q: What is the name given to the ASCII letter capital G when written in both hexadecimal and decimal…
A: The Answer is in step2
Q: What is it about dialogue design that makes it so popular?
A: Let's have a look at the interface design first. Design of the user interface The element of the…
Q: What processes are required in obtaining Application Software? Please submit a full description of…
A: Intro Pricing is a crucial factor to consider when choosing a firm, but it should not be the only…
Q: When should you schedule a network update, and how long should it take?
A: Introduction: The time frame in which the network evolved.
Q: How can I determine which frequencies are being used in the primary frequency bands that wireless…
A: Intro Shopping online exposes you to several hazards, most notably the chance of your personal…
Q: When does cloud computing make sense for a major firm with an existing IT department?
A: Introduction: (i) Businesses spend a lot of money developing and implementing software to improve…
Q: Discuss the benefits of moving to an enterprise-level analytics solution if you are used to working…
A: Data generation tool: Load, performance, stress, and database testing are all made easier with test…
Q: A group of objects that have been piled atop one another is known as a stack. Which kinds of…
A: Foundation This question originates from the Data Structure paper that is part of the Computer…
Q: Every information retrieval (IR) system is either directly or indirectly connected to a certain…
A: Information Retrieval (IR) is the dealing with the storage, retrieval and evaluation of information…
Q: What is the definition of a fitness motion sensor?
A: Introduction: One of the detecting devices that may collect input from various things is the sensor.
Q: What are the benefits and drawbacks of utilising IPSec in comparison to alternative methods to…
A: Given: IPsec, which stands for "Internet Protocol Security," is a collection of protocols that was…
Q: What is the distinction between a String and a primitive data type (for example, an int, a double,…
A: It's worth noting that, while the String object is immutable, its reference variable is not. String…
Q: Is the scheduling of threads consistent across processes, or does it vary for each individual…
A: Intro The order in which threads are executed is determined by their priority. Despite the fact that…
Q: What do you believe is the most critical aspect of transitioning from a serial to a batch processing…
A: Introduction: Using a serial processing strategy, FIFO is utilised for all tasks:
Q: What are the top six reasons why someone should learn about compilers?
A:
Q: Please provide three examples of why it is essential to design a user interface before beginning any…
A: Start: Before we begin coding, we need to determine the reasons for designing the user interface for…
Q: Networked security cameras are not at danger the great majority of the time
A: Intro One: It's Easier to Manage Security Access to Separate IP Camera Networks. Cameras on a…
Q: What are the benefits of High Language in comparison to Machine Language?
A: The question has been answered in step2
Q: Are you able to provide a detailed explanation of what Transactions and Concurrency involve in…
A: Introduction A transaction is a collection of database commands, which execute as a package and…
Q: uestion 1 of 8 For the following image, determine if it is a NDFA or DFA. What are valid inputs? 0-9…
A:
Q: Regarding the topic of cyber security, has a correlation been established between the development of…
A: Overview: Through the application of technologies, processes, and controls, systems, networks,…
Q: Given numPQueue: 29, 38, 76 What does Peek(numPQueue) return? Ex: 100 After the following…
A: The solutions are given below with code and output peek, enqueue, dequeue operations are performed…
Q: I would appreciate it if you could provide me with a list of the top five security weaknesses in my…
A: Intro Network security: Network security vulnerabilities are defects or weaknesses in the system's…
Q: Compatibility Mode or Microsoft Windows XP Should be utilised as a first resort in the event that a…
A: Dear Student, The reason why compatibility mode is used for older version of windows os in our case…
Q: Using dynamic scoping has performance ramifications, which this article discusses, as well as tips…
A: The scope of a variable x in the region of the program in which the use of x refers to its…
Please explain this Enhanced entity-relationship (EER) Diagram (see attached photo)
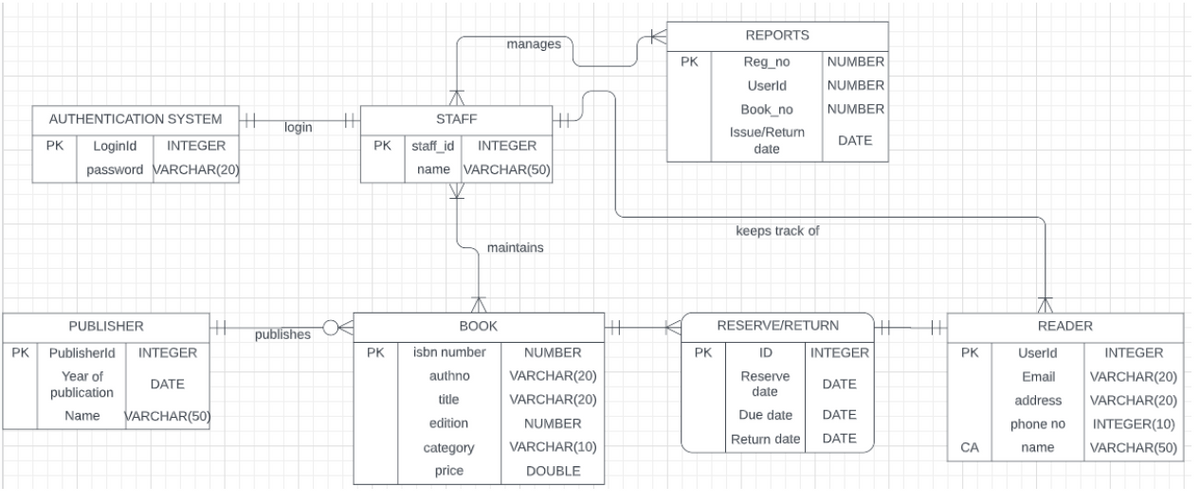
Step by step
Solved in 2 steps

- myBytes BYTE 10h,20h,30h,40hmyWords WORD 8Ah,3Bh,72h,44h,66hmyDoubles DWORD 1,2,3,4,5myPointer DWORD myDoublesvoting application app c# it would ask if the person would like to login as a admin or voter if admin 1. Add/Delete Candidate and automatically generate candidate ID. 2. Add/Delete Voters and automatically generate voter ID. 3. ask for an user and password if voter 1. it would ask them to login and register 2. Allow voters to vote using registered ID and an ID which has not voted yet. 3. When voter ID is deleted, its vote will also be deleted.The Pizza Ordering System allows the user of a web browser to order pizza forhome delivery. To place an order, a shopper searches to find items to purchase,adds items one at a time to a shopping cart, and possibly searches again for moreitems. When all items have been chosen, the shopper provides a delivery address.If not paying with cash, the shopper also provides credit card information. Thesystem has an option for shoppers to register with the pizza shop. They can thensave their name and address information, so that they do not have to enter thisinformation every time that they place an order.Develop a use case diagram, for a use case for placing an order, PlaceOrder. Theuse case should show a relationship to two previously specified use cases,IdentifyCustomer, which allows a user to register and log in, and PaybyCredit,which models credit card payments.
- psueducode of any task that you usually do like this ExampleTask: create CCS 102 session lessonSteps:1) Get topic from the lesson outline2) Find some resources/ references3) If there is a very good video resource from Youtube thendownload the videoelseCreate an outline of the discussionCreate the Powerpoint presentationCreate a script based from the slides of the presentationRecord the presentation with narrationCreate a video of the presentation4) If video is too largeCompress the video5) Post the video as a material in Google Classroom# Lab 2 ## Scenario Code&Code is a small company dedicated to Software Development. Their engineering team, to which you belong, is working on writing a Web Application as an MVP for a new customer. The code name for this App is “Loggy”, which is meant to offer functionality for a personal journal where users can log their daily activities through text, voice and video. The first step will be to write the main functionality, which is essentially a Microblogging System where all the posts are automatically annotated with voice, video or text. As an initial step, you must create the skeleton of the back-end service for performing the automatic closed captioning under these assumptions: - The closed captioning is performed through an external service (AWS or GCloud). - There should be an internal controller that: - Receives the recordings to be processed from a requester - Sends the recordings to the external service - Receives its response - Updates the recoding with the resulting…Create a small library management system. Thisapplication will help the librarians manage the book catalogs fortheir library. You have been asked to build the classes required to meet thegiven requirements: The library identifies each item that it checks outs as alibraryItem. A libraryItem can be either a book, or a video. A library item has the following attributes: a numericcallNumber, title and availability status. No libraryItem should be created without a callNumber- and thatmeans there are no default constructors for this class. In addition to the getters and setters there are two methods:checkout() and return() that sets the availability to false andtrue, respectively. The book entity is defined by the following attributes: ISBN,Book author, book publisher The video entity is defined by the following attributes: studio,artist. A catalog is a collection of all the libraryItems belonging tothe library. The catalog class will contain a reference variable pointing tothe collection…
- HTML passcode issue 79 Online banking security sometimes demands three random passcode characters. If the passcode was 531278, they may request the 2nd, 3rd, and 5th characters and expect 317. Keylog.txt had 50 successful logins. Study the file to get the shortest unknown-length secret passcode.Annexure BUse Case Name Purchase a bookScenario Purchase a book Triggering Event A buyer decides to purchase a book from EyesHaveIt.com.Brief Description Customer searches for a book(s) on EyesHaveIt.com. Customer selects from search results and adds a book(s) to the shopping cart. Customer then proceeds to checkout. If an account exists, the customer confirms purchase, and the system sends a confirmation e-mail to the customer. If an account doesn’t exist, an account is created, the purchase is confirmed, and the confirmation e-mail is sent.Actors BuyerComputer Science Create a session variable called SProot and assign the generated positive root valueto it in Oroots.php. Display this session variable in PosRoot,php page.
- Medical Unlimited Medical Unlimited (the brainchild of a group of young philanthropic medical professionals) is interested in setting up a mobile medical unit that provides free medical services for students. The mobile medical unit will require a patient record and scheduling application that will be used by the medical staff (doctors/nurses) and receptionists working there. The receptionists will use the system to capture new patient information when firsttime patients visit the doctor. Receptionists will also be responsible for scheduling all appointments. Nurses on the other hand will use the s ystem to keep track of the results of each visit including diagnosis, medications, prescription and treatment. Multiple medications may be prescribed during each visit. The nurses can also access the information to print out a history of patient visits. Th e doctors will primarily use the system to view patient history. The doctors may enter some patient treatment information and…Medical Unlimited Medical Unlimited (the brainchild of a group of young philanthropic medical professionals) is interested in setting up a mobile medical unit that provides free medical services for students. The mobile medical unit will require a patient record and scheduling application that will be used by the medical staff (doctors/nurses) and receptionists working there. The receptionists will use the system to capture new patient information when firsttime patients visit the doctor. Receptionists will also be responsible for scheduling all appointments. Nurses on the other hand will use the s ystem to keep track of the results of each visit including diagnosis, medications, prescription and treatment. Multiple medications may be prescribed during each visit. The nurses can also access the information to print out a history of patient visits. Th e doctors will primarily use the system to view patient history. The doctors may enter some patient treatment information and…Project: Covid-19 Vaccination Appointment Group members: 1 You need to follow the MVC architectural pattern to develop an online Covid-19 vaccination appointment system using Java Servlets and JSPs. Requirements: The user shall enter his National ID number (then submit the request) The system shall determine if the user: Fully vaccinated – boosted (a person who received two doses, and a booster shot). Fully vaccinated (Two doses) ? (can go for a third shot (vaccine booster shot), see Req 6 below). Already received the first dose ? Allow the user to book an appointment for the second dose Didn’t take any dose ? Allow the user to book an appointment for the first dose The user shall be able to determine the vaccination type (for the first dose only) The user shall be able to select the date/time for the appointment If the user is booking an appointment for the second dose, the time between the first and second dose shall not be less than N weeks (N is configurable in the database based…



