aximum memc addressable an the size of the
Q: Investigate if Structured English may be used to describe processes that aren't directly related to…
A: When there aren't too many difficult decisions to make or iterations in the reasoning that's already…
Q: her understand RAID 5, we need to know more about the technology. When is RAID 5 better than one of…
A: It is defined as RAID redundant array of inexpensive/independent disks. It is a data storage…
Q: Is it still required to back up an Oracle database when using RAID storage devices? Typing instead…
A: Foundation: RAID is an acronym that stands for Low-Cost Redundant Array. Thus, RAID is a viable…
Q: Consider an ART network with nine input (F1) units and two cluster (F2) units. After some training,…
A: Adaptive resonance theory is the type of the neural network technique which is developed by the…
Q: The------is a nature of z in this .;command >>surf(x, y, z)
A:
Q: The organization's users rely significantly on three protocols that are vulnerable or unsecure.
A: According to the information given:- We have to define the organization's users rely significantly…
Q: Write a C program to find the range of a set of numbers. Range is the difference between the…
A:
Q: b) Draw the decoder circuit for a systematic linear cyclic code that has a code length n = 7 and a…
A:
Q: Q3) Design a perceptron neural network to distinguish patterns between bananas and pineapples, based…
A: According to the information given:- We have to design a perception neural network to distinguish…
Q: Fragmentation is defined as what? Internal and external fragmentation must be distinguished.
A: The Answer is in step2
Q: There is a reason for this: computers have become so powerful. How can we establish that computers…
A: Computers: Computers have been reliable ever since they were first developed, but today they are…
Q: Describe the internet of things in your own words. This distinction is what separates these two…
A: The Internet of Things is described by computer technology as the notion of linking ordinary things…
Q: What determines event order in text-based environments like the command line?
A: Given: The issue focuses on the progression of activities that takes place whenever a user runs a…
Q: What is the data transfer rate of Ethernet local area networks?
A: The solution to the given question is: INTRODUCTION Ethernet is a popular network technology in…
Q: 4. Write a Matlab program to compute the value of 30*10 without using the operator. Attach the…
A:
Q: ING Chess Moves Mapper using Shortest path algorithm As the title indicates, you will need to…
A: It is defined as a interpreted, object-oriented, high-level programming language with dynamic…
Q: B: List the steps in a typical read cycle? C: What is the meaning of HMA, and how the 8086 CPU deals…
A: B: There are 5 steps in Typical Read Cycle and they are : 1. Place the address of the location on…
Q: Do you have three protocols that are vulnerable since the network is so important to the users of…
A: Network Protocols are a set of defined rules that control and govern the exchange of data in a…
Q: What kinds of Database Schemas and Designs have we become familiar with so far? What are our goals…
A: A well-designed database allows for quick access to data. When picking a database architecture,…
Q: What is the significance of an IP address? An easy-to-remember address is called a mnemonic address.…
A: What is the significance of an IP address?An easy-to-remember address is called a mnemonic address.…
Q: Match each abbreviation with its correspondence: GPIO Choose... UART Choose... NOOBS Choose...…
A: Please find the answer below step.
Q: What is meant by the term "TCP/IP stack"?
A: TCP/IP stack: The TCP/IP Stack, or the web show suite, is a lot of correspondence shows used by the…
Q: Open the command prompt window and give the command “ping –n 5 www.freebsd.org”. Answer the…
A: Ans-1 ping –n 5 The -n option tells the ping command to send 5 ICMP Echo Requests instead of the…
Q: To save cod and reusing it at any time, it is prefer writing cod in ----- .-window command O Editor…
A: To save code and reusing it at any time, it is prefer writing code in workspace window.
Q: Given the following truth table: Inputs ABC 000 0 001 1 010 0 011 0 100 1 101 1 110 0 111 1 e.…
A: K- map is used to simplify the boolean expression.
Q: Simply put, what are the three primary types of software maintenance? How come they can be so hard…
A: The answer of this question is as follows:
Q: Do you have three protocols that are vulnerable since the network is so important to the users of…
A: Three Protocol vulnerable to attacks are given below:
Q: What is the nearest neighbor algorithn to find the Hamilton circuit that begins of vertex B
A: Given graph contains, Vertices= {A, B, C, D, E} There are many weighted undirected edges between the…
Q: All of our information systems include operational databases as part of their backend…
A: All of our information systems include operational databases as part of their backend…
Q: In order to demonstrate your grasp of the second level of threat modeling, select technology and…
A: The second step of threat modeling is identifying trust zones, potential adversaries, and threats.…
Q: Problem 2 Assume that you are implementing a heap using a fixed size array. 1- Illustrate how the…
A: Assume that you are implementing a heap using a fixed size array. 1- Illustrate how the following…
Q: 6. What is the addressing mode for the above [BX+DI+2080H]? 7. Determine the data in AL after the…
A: Note: Answering the first question as per the guidelines. Task : Given the instruction [BX + DI +…
Q: What do you name software that scans for viruses, compresses data, or backs up files?
A: Introduction: Computer software, sometimes referred to as software, is a set of instructions and…
Q: What is a restoration hardware?
A: While repairing a Victorian property in Eureka, California, Stephen Gordon founded Restoration…
Q: Show the differences between the prevention and avoidance of deadlock. What are strategies to be…
A: Answer: Introduction: Deadlock Prevention: It guarantees that more than one of the essential…
Q: Use Input to print "< =" and stop the program until the user enters a value and presses the Enter…
A: #include <iostream> using namespace std; int main() { cout<<"Do you want to stop :…
Q: When you throw a rock at some elevation part of its potential energy is converted to kinetic energy…
A: Answer is in next step
Q: True/False Questions (. 1. If the "Primal" objective function is a "maximization" problem, then the…
A:
Q: Find the true statement from the following list of statements. Application software includes a…
A: First of all, application software is program to complete specific tasks. For example, Microsoft…
Q: Create a program that implements a music playlist using structure and files. The program must…
A: // An object of type Song will store information about a single // digitally recorded song file.…
Q: Answer time left: 02:53:31 * Please use the mouse to highlight where the specific question text is…
A: Each article with its techniques and properties contains an interior and secret property known as…
Q: Discuss how regressors can be added to reduce the error variance
A: Understanding the fundamental reasons for the system's predictions and actions is one of the…
Q: RAID-capable storage reduces the need for Oracle database backups in today's environment. Written…
A: RAID RAID, an acronym for redundant array of independent disks or redundant array of inexpensive…
Q: How and in what locations will the network's physical and virtual networking hardware be deployed…
A: Given: Networks are made up of a variety of pieces of hardware that enable information to be sent…
Q: parallel and running programs concurrently
A: Hey there, I hope you find my solution helpful.
Q: Identify three protocols that are vulnerable or unprotected while evaluating the network's relevance…
A: Introduction: Network Protocols are a set of defined rules that control and govern the exchange of…
Q: Write a Java program to create menu driven calculator that performs basic arithmetic operations…
A: JAVA Program: import java.util.Scanner; public class Calculator { public static void main(String[]…
Q: Question 3 Convert binary 10011111 to decimal. The answer should be scale to a byte size storage. O…
A: 1) In a signed binary, first bit (the leftmost) is reserved for the sign, 1 = negative, 0 =…
Q: describe your understanding of hash tables in your own words. Give examples whenever possible.
A: The solution for the above given question is given below:
Q: The statement "PLL_Init();" is used to set clock to 16 MHz Select one: O True O False
A: Given question are true or false based question.
Step by step
Solved in 2 steps with 2 images

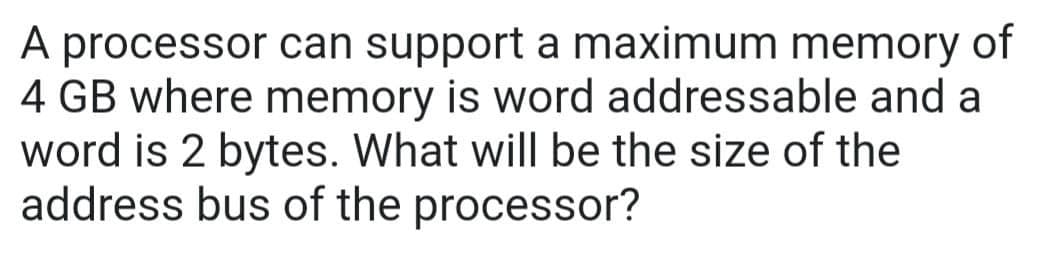
- Processor R is a 64-bit RISC processor with a 2 GHz clock rate. The average instruction requires one cycle to complete, assuming zero wait state memory accesses. Processor C is a CISC processor with a 1.8 GHz clock rate. The average simple instruction requires one cycle to complete, assuming zero wait state memory accesses. The average complex instruction requires two cycles to complete, assuming zero wait state memory accesses. Processor R can’t directly implement the complex processing instructions of Processor C. Executing an equivalent set of simple instructions requires an average of three cycles to complete, assuming zero wait state memory accesses. Program S contains nothing but simple instructions. Program C executes 70% simple instructions and 30% complex instructions. Which processor will execute program S more quickly? Which processor will execute program C more quickly? At what percentage of complex instructions will the performance of the two processors be equal?A processor can support a maximum memory of 4 GB, where the memory is word-addressable (a word consists of two bytes). The size of the address bus of the processor is at least___(bits)?.We have a computer with a Direct Mapped Memory Cache. The main memory is 16GB and the cache is 64KB. The size of a block is 512B. Explain what a Direct Mapped Memory Cache is and how it works in this particular example.
- If a 2 GHz processor graduates an instruction every third cycle, how many instructions are there in a program that runs for 10 seconds?The connection between the central processing unit and the memory might be a synchronous or an asynchronous bus. Which one is more nimble and quick? Please detail your reasoning process.The 20-bit address bus has a memory addressing capability of 20 megabytes. microcontroller?
- CPU and memory connections should be made over a synchronous or asynchronous bus. Which one has the edge in terms of acceleration and dexterity? Step by step instructions on how you came up with the outcome you did.The length of a computer instruction is 10 bits, and the size of an address field is 3 bits. FIFTEEN 2-address instructions and SEVEN 1-address instructions have already been created by the system architect. How many 0-address instructions can the instruction set architecture support?A computer has 512 MB (megabytes) of memory. Assum the memory is byte addressable, how many bits are needed to address each loaction?



