b) Determine all values of x for which [p(x) ^q(x)]^r(x) results in a true statement.
b) Determine all values of x for which [p(x) ^q(x)]^r(x) results in a true statement.
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter2: Basic Linear Algebra
Section: Chapter Questions
Problem 15RP
Related questions
Question
Additional information: r(x) is the open statement "x>0". The universe is integers.
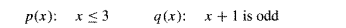
Transcribed Image Text:p(x): x≤3
q(x): x +1 is odd
![b) Determine all values of x for which
[p(x) ^q(x)]^r(x) results in a true statement.](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2F533810fa-4d07-45bb-8130-109ce090576c%2F9013fd06-f2c6-4e43-b554-8f8ad044527c%2Fz0jybq_processed.png&w=3840&q=75)
Transcribed Image Text:b) Determine all values of x for which
[p(x) ^q(x)]^r(x) results in a true statement.
Expert Solution
Step 1
Given additional information:
r(x): x>0 (open statement, true for all positive integers) p(x): x < 3 (true for x=1, 2 and false for all other integers) q(x): x + 1 is odd (true for odd integers and false for even integers)
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage