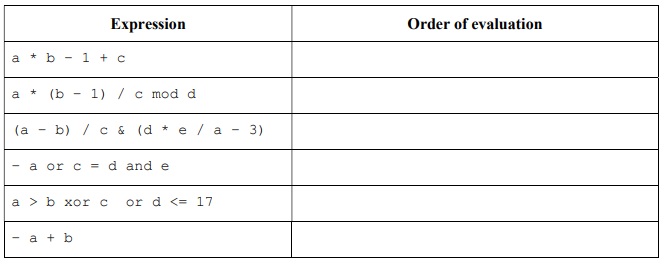
(b) Show the order of evaluation of the expressions, assuming that there are no precedence rules and all operators associate right to left.
Q: Convert 6DE base 16 to binary, decimal, and octal. Show your solutions.
A: (6DE)16 => Binary Binary = 011011011110 [Convert each hex digit to 4 binary digits, 6=0110,…
Q: Write a program using integers userNum and divNum as input, and output userNum divided by divNum…
A: JAVA Program: import java.util.Scanner; class Number { public static void main(String[] args) {…
Q: What resources do you suggest for learning more about Windows Service Control Manager?
A: The Service Control Manager (SCM) is one of the numerous capabilities of Windows NT that may start…
Q: 1 bytes is equal to ….. A. 4 bits B. 10 bits C. 8 bits D. None of the above
A: In this question we have to determine what is the value of 1 byte equals to. Let's compute it and…
Q: What is the best way to schedule processes in a time-sharing environment?
A: Time-sharing environment: Time sharing uses round robin scheduling. CPU schedulers allocate time to…
Q: How can I know which frequencies are utilised in wireless communication systems' main frequency…
A: Mobile phones use a variety of technologies. Nowadays, mobile phones generally rely on three antenna…
Q: According to certain views, people and information systems may be the driving forces behind the…
A: Overview: to figure out why humans and information systems are the driving forces behind information…
Q: Take a closer look at how thread scheduling and processes and threads vary.
A: Thread scheduling and processes: A running programme, often known as an active programme, is what we…
Q: Do you happen to know of any good resources that I might use to learn more about Windows Service…
A: SCM is a Windows NT feature: This function lets users run applications and device drivers in…
Q: Which aspects of the integrity limitations are unique?
A: SQL is the abbreviation for Structured Query Language. It permits access to and management of…
Q: Through taking this class, you will have a deeper understanding of social networking blogs, cloud…
A: Social Networking blogs & Cloud computing: The Definitive Meaning Blogs devoted to social media…
Q: Explain in a nutshell what the key differences are between LL and LR parsing. Which of these is also…
A: Encryption: A left-to-right (LL) parser is the leftmost variation. To generate the leftmost…
Q: It would be helpful if you could provide a summary of some of the most pressing concerns about…
A: We need to discuss some pressing concerns about network security.
Q: 5. The following code has several errors. Find out and circle
A: Errors are circled below
Q: HTTP status code "Not Found" is the most well-known.
A: Not Found: The HTTP 404, 404 Not Found, and 404 error message is a Hypertext Transfer Protocol…
Q: Explain why batch processing is preferable than time-sharing processing in certain situations.
A: An operating system which defines the interface between user and computer systems.
Q: B- Write C++ Program to print the following figure: abcdefgh bcdefgh cdefgh defgh efgh fgh sh b
A: Algorithm/Program Plan: Create a main function Declare j of integer type Initialize the variable…
Q: ge [-5.....5, 3... ation is 100. E ry cells. Calcu blumn maior c
A:
Q: What what is the work that the Windows Service Control Manager is supposed to undertake, and how…
A: Clarification: Service Control Manager, often known as SCM, is an independent system function that…
Q: In the first instance, please explain why compilers use parsing techniques that are only effective…
A: Given: The parser is the compiler step that takes a token string as input and uses existing grammar…
Q: Because wireless networks function lower than traditional networks, what are the elements that…
A: Wireless Networks function: There are a number of factors that lead to wireless networks having a…
Q: Name any three programming languages, together with the characteristics that they provide, that are…
A: Introduction: The programming language is a computer language that programmers use to create…
Q: 04) Write a Thank You letter to the hiring manager of Huawei company, who helped you to find a job…
A: A letter shall represent all the details corresponding to the job requirements.
Q: It is vital to first design the user interface for an application before beginning to develop code…
A: To be determined: What happens in a code editor if the mouse pointer is kept over a jagged line for…
Q: Where can I get further information about the Windows Service Control Manager?
A: During boot up, the service control manager, often known as SCM, is activated. It is a server for…
Q: How does High Language compare to Machine Language in terms of its advantages?
A: How does High Language compare to Machine Language in terms of its advantages?
Q: File structure vs. storage structure: what are the key differences, and how would you explain them?
A: The main distinction between the file structure and the storage structure is that in the storage…
Q: In the context of cybercrime, what are some of the assumptions that are made?
A: Given: Cybercrime, often known as computer crime or computer terrorism, is the use of a computer to…
Q: Code reviews are used to ensure that the code is up to date
A: Code Review: Code review is the process to review and check the code efficiency and correctness of…
Q: Write a C program, which stores information about a date in a structure containing three…
A:
Q: Using a compiled language rather than an interpreted one has what benefits over the other options?…
A: The advantages of using a compiled language instead of an interpreted language are as follows: Those…
Q: Identify and succinctly describe a few worldwide information systems issues.
A: Answer: Global information systems are systems that are used by a number of nations throughout the…
Q: What is automated testing and how does it work?
A: Introduction: Automated testing is used to determine whether the software generated by the developer…
Q: Examine the utility and amount to which interpersonal skills were used in the preparation and…
A: The above question is answered in step 2 :-
Q: es it mean for a software engineer to "debug" an appl
A: Introduction: Debugging is a multistep process in computer programming and engineering that entails…
Q: What does it imply when we talk about "hardware" and "software," and how do they differ?
A: Find the required answer given as below :
Q: Determine the different information security processes and policies, both manual and automated, that…
A: The Answer is given below step.
Q: Explain the distinction between a request for proposal (RFP) and a request for quotation (RFQ) (RFQ)
A: Introduction: A request for quotation (RFQ) is a method through which a corporation solicits bids…
Q: Define software engineering and explain why it's important to use software engineering concepts in…
A: Software Engineering: It is used to develop a software using well known technologies, principals and…
Q: Find out how important wireless networks are to the modern developing world. Only a few physical…
A: Introduction Wireless technology has dramatically enhanced communication between rescue personnel…
Q: When adding or deleting users in Windows 10 and Linux, what issues have you encountered?
A: Among the issues encountered while adding or removing users in Windows 10 are the following: A local…
Q: The vast majority of today's appliances include built-in wireless networking capabilities, thanks to…
A: Wireless networking is defined as the process of telecommunications networks of a connection between…
Q: What is the difference between concurrent and parallel execution?
A: Parallel Execution: => Parallelism refers to an application in which tasks are broken down…
Q: Q2/writhe M-file script code to solve and plot the following system: With all concepts of the…
A: hold on t = 0:2 * pi : 101; % t value from 0 to 101 with step of 2pi x = sin(t); % set sin(t) y =…
Q: f all computers, whe
A: Solution - In the given question, we have to select the correct answer.
Q: Different ways of representing integers in a binary format exists like the sign magnitude and the…
A: There are different methods for representing binary numbers. Some of them are: 1's compliment In…
Q: The following is an explanation of the layered approach to the architecture of operating systems: I…
A: A system structure is the operating system's tiered approach. The operating system services are…
Q: some of the most recent important aspects of Facebook?
A: Introduction : The first of many features is the ability to organize our newsfeed and contacts. If…
Q: Only for issues relating to information technology security will the proposed remedy be developed.
A: overview of IT security concerns: It is described as a collection of cyber security methods that…
Q: What actions do employees take inside an organisation to ensure that knowledge is not forgotten?…
A: The question has been answered in step2
(b) Show the order of evaluation of the expressions, assuming that there are no precedence
rules and all operators associate right to left.
Step by step
Solved in 2 steps with 1 images

- The execution of SUB AL, BL is performed by _____. a. BIU b. both EU and BIU c. neither EU nor BIU d. EUC++ Coding only put the code where it says solution goes here. Don’t change anything else//Test isEqual function cout << endl << "Testing isEqual function"; cout << endl << "------------------------" << endl; if (isEqual(s2, s3)) cout << "s2=\"" << s2 << "\" and s3=\"" << s3 << "\" are equal" << endl; else cout << "s2=\"" << s2 << "\" and s3=\"" << s3 << "\" are not equal" << endl; delete[] s3; s3 = getCopy(s2); if (isEqual(s2, s3)) cout << "s2=\"" << s2 << "\" and s3=\"" << s3 << "\" are equal" << endl; else cout << "s2=\"" << s2 << "\" and s3=\"" << s3 << "\" are not equal" << endl; bool isEqual(const charPtr s1, const charPtr s2){/*returns true if the cstring s1 is equal to the cstring s2Definition: Two c-strings s1 and s2 are equal if they have the same lengthand characters of s1 and s2 at corresponding indexes are the same.*/ }
- Define argumentC++ Language code and explain Zodiac Sign Identifier - Ask the user's birth month and birth day and return the corresponding Zodiac Sign he/she belongs: Evaluate the user's birth month and day by checking the following: If born from, Mar 21 to Apr 19 - Aries Apr 20 to May 20 - Taurus May 21 to Jun 20 - Gemini Jun 21 to Jul 22 - Cancer Jul 23 to Aug 22 - Leo Aug 23 to Sep 22 - Virgo Sep 23 to Oct 22 - Libra Oct 23 to Nov 21 - Scorpio Nov 22 to Dec 21 - Sagittarius Dec 22 to Jan 19 - Capricorn Jan 20 to Feb 18 - Aquarius Feb 19 to Mar 20 - Pisces Example: What is your month of birth? 1 - January (31 days) 2 - February (27 days, if Leap Year 28 days) 3 - March (31 days) 4 - April (30 days) 5 - May (31 days) 6 - June (30 days) 7 - July (31 days) 8 - August (31 days) 9 - September (30 days) 10 - October (31 days) 11 - November (30 days) 12 - December (31 days) Please enter your birth month: 8 Please enter day of your birth: 16 Please enter your year of birth: 1997 Your birthday is every…Briefly explain operator precedence
- flow cgartfactorial function implement program which can calculate factorial number using C or C++Simulate an Elevator-Controller Program in C programming language. The Elevator should be able to travel between five floors namely Ground, 1st, 2nd, 3rd, 4th and 5th floors. The program should have some validation, meaning, only the valid characters should be received by the program(G, 1, 2, 3, 4, 5). If the user keys-in “A” or “-1”, the program should be able to handle such input and not crash and ask for a correct valid input.

