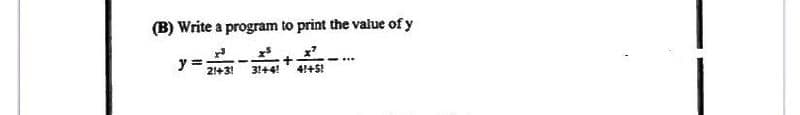
(B) Write a program to print the value of y y= 21+31 31441 + 41+5!
Q: Exercise: I A company pays its employees on a weekly basis. The employees are of four types:…
A: Please refer to the screenshot of the code to understand the indentation of the code. package :…
Q: The layers of a DBMS-based application may be described in a few sentences.
A: Given: A database may be created and maintained using a software programme called a database…
Q: needed p where
A:
Q: In this aspect, how does the agile methodology vary from a typical SDLC
A: Introduction In agile methodology, we are constantly uncertain and aware of our assumptions (as a…
Q: Describe the predictive analytics method and offer an example of how it is applied in practise.
A: Intro Predictive analytics is the process of using using the data analytics to make the data…
Q: Subsystemizing computer processes and programmes may or may not be a good idea. Deconstructing this…
A: Introduction: Segmentation Segments of a process are separated. Segments are the units into which a…
Q: Define the term "Host Address" in networking? Also Give example of it?
A: Given question is asking for the definition of term host address in networking.
Q: code
A: Introduction Java is basically a type of programming language that is very much beneficial and can…
Q: Is there a manner in which data profiling may increase the quality of data?
A: Reviewing source data, comprehending structure, substance, and relationships, and finding…
Q: java Create a static method that: is called appendPosSum returns an ArrayList of Integers takes…
A: public static void main(String[] args) { Scanner in = new Scanner(System.in); int size =…
Q: Explain why you sometimes need to set aside significantly more space for a numeric field than any of…
A: Introduction: The field is the smallest unit of data in the programme. It is the most basic…
Q: Instead than depending only on concerns about performance, demonstrate why deep access is better…
A: Don't only establish a performance case; instead, explain why deep access is preferable to shallow…
Q: Statistics of smart city?
A: Answer:
Q: Are inputs and outputs essential for the different software system design procedures?
A: Given: How Do You Design Software?It seems that while discussing software design, the question "what…
Q: What memory management technique is the most successful, and why?
A: Introduction: Make use of repetition in order to arrange information in your memory, Utilizing flash…
Q: Write the different UNIX file opening modes and operation modes with an example
A: Indeed, the Unix file has different openings that define who can do what. That is, Read, write and…
Q: The logical NOT operator is a unary operator. it takes only one operand .A Three operand .B Two…
A: Here in this question we have asked about logical not operator.is it unary operator .
Q: Which of the following best characterizes the statements, where A, B, and C are sets: A. (An B = C)…
A: The statements given:- (A∩B = C) is a set (A ∪ B / C) is a set
Q: Which one of the following binary search tree operations is NOT based on divide and conquer? O…
A: Here we have given the correct answer with explanation on binary search tree operations is not based…
Q: Arrow tool, Arc tool, Pen tool and Drawing Elements tool are used to add to ChemDraw document. O…
A: Hello student, hope you are doing well. The correct option is the 1st one 1. Shapes
Q: To delete many objects, you need to select them before and choose the "Delete" command or "Delete"…
A: To delete many objects you need to select them before and choose the " Delete " command True
Q: 1+1+12
A: In Arithmetic operations, we use the BODMAS rule, where B acronym for Brackets O acronym for Order…
Q: Use MATLAB to PLOT and CALCULATE the following integrals. Label the x and y axes of the plot.
A: int is used for integrate and plot.
Q: Why are pass-by-value and pass-by-reference features essential in current programming languages? Why…
A: Please find the detailed answer in the following steps.
Q: Cloud computing architectures, such as Big Data Cluster, are increasingly being employed for data…
A: Introduction: Cloud computing is a critical technology that enables the execution of massively…
Q: In computer most processing take place in ?
A: The answer is given in the below step
Q: What would be the output of the following code A = [106]: b = [203]: :c=a./b [0 20.5] O [205] O…
A: Hello student, hope you are doing well. The answer is attached below along with explanation. The…
Q: We ensure that all communication taking place on the present iteration of the Internet between the…
A: Answer : NDN used to protect the data from unauthorized user by encryption of data.
Q: How are empty calculation cycles avoided when a large number of instructions are being processed…
A: Start: The four main parts of a computer are the input devices, output devices, primary memory, and…
Q: The use of forensic software by investigators is intended to aid them in finding evidence; but, what…
A: Investigators can learn information about computer users, locate deleted data, rebuild artefacts,…
Q: Uses of surrogate keys in a data warehouse or data mart are described below.
A: Data Warehouse is a relational database management system construct to meet the requirement of…
Q: A) p -->-q and p V q are logically equivalent B) (q/\ (p --> ~q)) --> ~p is a tautology O Only A is…
A: Here in this question we have given two statements and we have asked that which of them of true
Q: What is a computer network exactly, and what are some of its applications? What are the many…
A: Intro Computer Network: The term "computer network" refers to a connected set of computers and…
Q: A lift calling system is to be programmed for an organization building having 4 floors. The CEO of…
A: ASSUME that lift reaches CEO 3rd floor be A, 1st floor be B and 2 nd floor be C and D Ground floor…
Q: What are the risks of migrating a server database?
A: Introduction: Data Loss RiskDuring the process of migrating the data, there was a loss of data that…
Q: What is the output of this Java program? class Driver { public static void main(String[] args) {…
A: So, we need to find the output of the given java program. Let's run the code in java code editor.…
Q: What is the insert anomaly, update anomaly, and delete anomaly computer?
A: Intro Computer bug: There is no such thing as a flawless operating system or piece of software;…
Q: What are the key differences between a local-area network and a wide-area network in terms of…
A: Introduction: This topic highlights the primary differences between a local area network (LAN) and a…
Q: java In this assignment you will swap a position in an array list with another. swap() gets 3…
A: Coded using Java.
Q: Which of the following best characterizes the two statements, where x and y are natural numbers: A)…
A: Given, that x,y are natural numbers Natural numbers = {1,2,3,4,5,.....} now, A) for every x there…
Q: To delete many objects, you need to select them before and choose the "Delete" command or "Delete"…
A: To delete many objects you need to select then and then press delete. True
Q: The shift between the voltage of Phase A and B in a three phase system is O 120 degree O 0 degree O…
A: Find the required answer with reason given as below :
Q: The project manager uses a variety of Webcam software.
A: Using webcam software, users can capture and share videos, as well as stream the videos online.…
Q: What exactly is a subinterface, and how does it function? Is it feasible for a user interface to…
A: Introduction: A sub-interface is a virtual interface formed by dividing a physical interface into…
Q: Which of the individual components of a high-end gaming computer consumes the most amount of power…
A: The solution to the given question is: A gaming computer is a specially configured personal computer…
Q: Describe what an SCRUM is and why it's so important in the software development process.
A: The evolution of software: SCRUM: Through a series of iterations, the SCRUM team constructs and…
Q: Q.5.2 Argue for and against the establishment of legislations such as the Protection of Personal…
A: 5.2 There are arguments both for and against enacting such legislation. One argument in favor of…
Q: To put it simply, what are the underlying principles of computer graphics?
A: Computer graphic Computer graphics may create images with the use of PCs. Computer graphics are now…
Q: Twisted pair cable and fiber-optic cable have significant differences (at least three).
A: Introduction: The diameter of twisted pair cable is significantly bigger than that of optical fibre…
Q: A community bank may use one of three types of servers.
A: Intro As there are many types of servers used by the bank: Servers: This is the server that runs…
Step by step
Solved in 4 steps with 2 images

- Write a pseudo code for a program which will accept two numbers from the user and calculate the sum and product and display the answer. Subject: C++1. Given that x=5 and y=- 10, what is the output of this code If (x>10 && y<x-5) { If (x || y) x = 9; } else y =10; printf(“%d %d”, y,x); ? (Explain) Answer: write C ReplSolve below problem statement in python Problem Statement For any given temperature input by the user in Fahrenheit , we have to convert the temperature into Celsius.
- Write a C ++ program to find the value x according to the .following equation: x = 5y + 122Print the following output using a C program * * * * * * * * * * * * * * * * * * * * * * * * * * * * *State which values of the control variable x are printed by each of the following for statements:a) for (x = 2; x <= 13; x += 2) {printf("%u\n", x);}b) for (x = 5; x <= 22; x += 7) {printf("%u\n", x);}c) for (x = 3; x <= 15; x += 3) {printf("%u\n", x);}d) for (x = 1; x <= 5; x += 7) {printf("%u\n", x);}e) for (x = 12; x >= 2; x -= 3) {printf("%d\n", x);}



