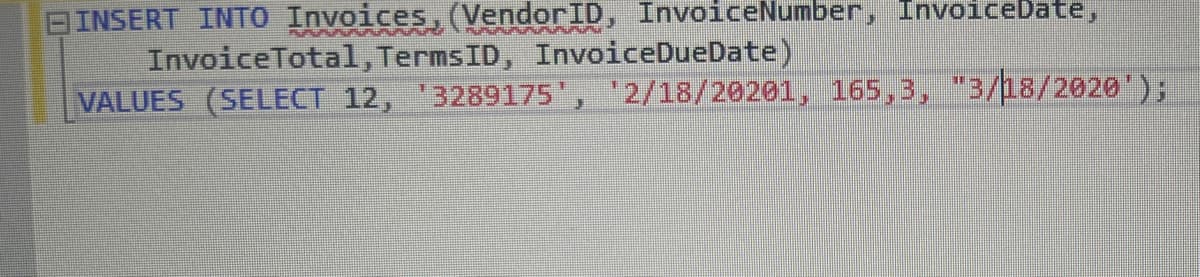
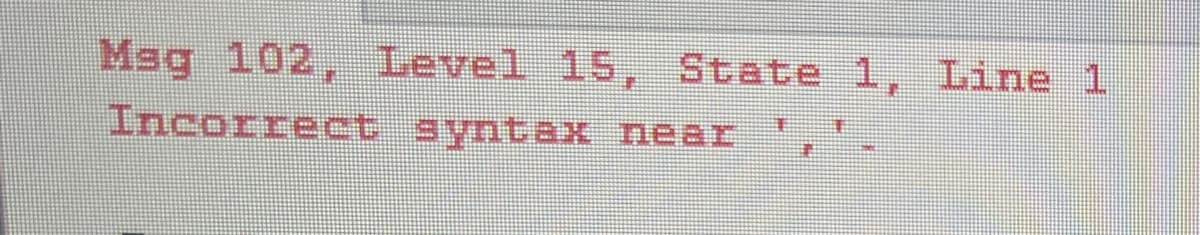
BINSERT INTO Invoices, (VendorID, InvoiceNumber, InvoiceDate, InvoiceTotal, TermsID, InvoiceDueDate) VALUES (SELECT 12, 3289175', '2/18/20201, 165,3, "3/18/2020');
Q: Should programmers offer code that can be maintained even if their employer doesn't need it?
A: Software engineers apply engineering principles to software development. Using software programming…
Q: How may the most important parts of an OS be summarized most effectively?
A: To put it as simply as possible, an operating system is a part of software that provides the…
Q: A double linked list may be implemented in a workspace array by utilising only one index next. That…
A: A double linked list is a data structure in which each node contains a value and two pointers, one…
Q: This is because regular In order to input a series of integers into an ArrayList, you'll need to use…
A: In order to input a series into an Arraylist, you will need to use a add() method and toArray…
Q: why can't output?
A: In this question we will code and check for the output which not working for you Let's code and…
Q: What checks can you do to ensure that each network device has a different MAC address? How about…
A: The answer is given below step.
Q: Define the sets A, B, C, D, and E as follows: • A = {x € R: x 2} • C = {x € R: |x| <2} E • D = {x €…
A: Given, A=x∈R:x<-2 A is the set of all real numbers x such that x is less than -2. In interval…
Q: module CircuitQ4(a, b, c, f, g); input a, b, c; output reg f, g; always@ (posedge Clk, posedge Rst)…
A: The Verilog code in Figure Q4(a) describes an asynchronous circuit with two outputs, "f" and "g".…
Q: Why is it necessary to separate a phone line and a communications adapter with a modem?
A: The answer is given below step.
Q: Explain in detail, using your own words and providing concrete examples to back up your claims, how…
A: Given: Provide some concrete examples to illustrate the key distinctions between application…
Q: What are the advantages of doing data analysis and storing data on the cloud?
A: Simply put, cloud computing is the provision of computing services such as servers, storage,…
Q: What are the goals of Artificial Intelligence (AI) research and development? Include two examples…
A: Object of AI Artificial intelligence (AI) combines technologies like machine learning and deep…
Q: A "distributed denial of service assault" is what we call this kind of attack, and it can be…
A: The above question that is a distributed denial of service assault is what we called this kind of…
Q: Given the following statements: s1 = 'Computational Thinking' s2= "Python Rocks!" Show the result of…
A: Note: The answer of the first three subparts are given in this solution. Kindly repoost the…
Q: Why does it seem like my disk is thrashing? What actions may you take to mitigate the consequences…
A: Computing thrashing is a problem brought on by the use of virtual memory. It happens when a…
Q: What exactly is the distinction between computer architecture and organization?
A: Computer architecture: A plan for the plan and execution of a computer system is known as computer…
Q: To demonstrate that you are aware of the importance of this topic, could you write up or come up…
A: Given: It not only helps to prevent mistakes and flaws from being introduced into the software that…
Q: Please share your opinions on the contemporary internet and its underlying technologies.
A: WHAT IS INTERNET The most significant tool and well-known resource used by practically everyone in…
Q: Exist within the realm of software engineering any subfields that you think may be interesting…
A: Introduction: The following are the primary categories of our research interests in the field of…
Q: segmentation of images and identification of edges via the use of contrast and contrast. What is…
A: Introduction: Edge detection is a method used in image processing to determine the borders of…
Q: Provide a brief background on the evolution of computing.
A: Introduction: The background of computers goes back 200 years. Mechanical computing devices were…
Q: What have been the most difficult or problematic circumstances you've experienced as a CMC?
A: As a result, students who lack self-discipline tend to fall behind quickly.so there exists many…
Q: Just what are the distinctions between layer 2 and layer 3 switches? Which switch would you choose…
A: Start: What is the difference between layer two and layer three switches? Which switch would you…
Q: The critical nature of continuous event simulation may be attributed to four factors.
A: SIMULATION OF CONTINUAL EVENTS - A continuous event simulation fundamentally refers to a simulation…
Q: When people talk about having a "memory vacuum," how do they mean it? Why does it happen, and how…
A: operating system verifies the memory access and aborts the program if it is invalid.
Q: The layered design of an OS may be stated as follows: If you have any thoughts on this method, I'd…
A: Introduction: A system structure is the layered approach of the operating system. The operating…
Q: What's the dissimilarity between managing a computer system and designing one?
A: Managing a computer system and designing a computer system are two different activities which…
Q: You are supposed to write production ready code with Proper Unit Test Cases, Modularizaton etc. You…
A: Introduction : As per the given question the inputs are n, m, s, x and y then we have beautyPath a…
Q: When describing the multiple stages of a communication process, technology allows for more…
A: Foundation: The process of communicating is referred to as the flow of information or a message from…
Q: What distinguishes remote authentication from local authentication in terms of user identification?…
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: It would be helpful if you could provide a list of the various hardware security and tracking…
A: Numerous goods are used nowadays for protecting and monitoring hardware. The primary goal of these…
Q: Identify the three instances of discrete event simulation from the list below.
A: The answer is given below step.
Q: It is necessary to do research on the effects that wireless networks have on developing countries…
A: The inquiry asks what impact wireless networks have in developed and underdeveloped countries. Why…
Q: Parallel Lists Summary In this lab, you use what you have learned about parallel lists to complete a…
A: Coded using Python 3.
Q: Why do embedded systems depend on microcontrollers for so much of their functionality?
A: Why are microcontrollers used in embedded systems so frequently?CPUs that have been combined with a…
Q: You are given an array with all the numbers from 1 to N appearing exactly once, except for one…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: # Roller coaster ride height Create a program that prompts the passenger for their height to…
A: The if-else statement also tests the condition. It executes if block if condition is true otherwise…
Q: What distinguishes remote authentication from local authentication in terms of user identification?…
A: Given: What is the difference between local and remote user authentication? Which presented the…
Q: What would occur if there were no programs that could be relocated? This could make memory paging…
A: In this question we have to understand what would occur if there were no programs that could be…
Q: We can wonder why we need cache memory since we already have RAM, which is a volatile memory similar…
A: cache is important because it improves the efficiency of data retrieval. cache is an extremely fast…
Q: The sets A, B, and C are defined as follows: • A = {tall, grande, venti} • B = {foam, no-foam} • C =…
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: In what ways could different elements influence the communication efficiency of a network?
A: Network communication Network communication, or between networking, characterizes a bunch of…
Q: You are given an array in which every number from 1 to N appears precisely once with the exception…
A: Introduction How is the missing number to be located in O(N) time and O(1) space?
Q: Is it possible, in your opinion, for two network interfaces to share a MAC address? What may be the…
A: MAC address is the physical address that is allocated to uniquely recognize the host in the network.…
Q: There are two major advantages of electronic mail over conventional mail for modern communication.…
A: Email isn't just for text messages. Any type of multimedia can be sent within mail, also helps in…
Q: To what do we refer when we say "operating system?" To what do the operating system's two main…
A: What do people refer to when they discuss operating systems? Identify the two fundamental purposes…
Q: Is it your opinion that the effect of good customer service on repeat business makes organizations…
A: Client Retention: In marketing, customer retention is the act of persuading current consumers to…
Q: The three components that make up a computer's von Neumann architecture. A wide range of…
A: Neumann Architecture is characterised by the fact that the key components, as well as the visibility…
Q: In the next part, we will discuss the definition of manual software testing as well as the…
A: Programs with a manual: The testing of software manually, both its benefits and drawbacks, has to be…
Q: B
A: Introduction: Pre-written software packages are computer programs that are developed and sold by…
Step by step
Solved in 2 steps

- Considering Vaccination Database, write queries to: Display the Subject CNIC, Name, Contact, Dose1 Center, and Dose2 Center as shown below: CNIC Name Contact Dose1 Center Dose2 Center 22401-6645321-1 Nasir 3409991112 Lachi Kohat 2 14301-6045321-5 Shahab 3409991112 kohat 3 Dara The subjects who have been vaccinated different types in Dose1 and Dose2. For instance, subjects who were vaccinated ‘Sinovac’ in the first dose, while Pfizer in the second dose.How many Viles of each type have been consumed so far. How many subjects are vaccinated from expired viles. Suggest the name of Incharge for the best performance award based on the highest number of subjects vaccinated on a single dayCreate a view of the Join of Deposit and Withdraw transactions to Bank Branch UNION with the join of Bill Payment and Debit Purchase, or Return transactions to Merchant (i.e., all transactions with appropriate reference name.). BranchNbr stores RefNbr of either 'D', OR 'W' transactions and MerchantNbr stores RefNbr of either 'B', 'P' or 'R' transactions. GIVEN THE BELOW: --THIS CREATES THE TRANSACTION TABLE: CREATE TABLE Transaction ( TxNbr INT PRIMARY KEY, AccountNbr INT, TxTypeCode VARCHAR(250), TxDate DATE, TxTime TIMESTAMP, TxAmount FLOAT, RefNbr INT, FOREIGN KEY (AccountNbr)REFERENCES Account(AccountNbr), FOREIGN KEY (TxTypeCode) REFERENCES TxType(TxTypeCode)); --THIS CREATES THE BANK BRANCH TABLE:CREATE TABLE BankBranch ( BranchNbr INT PRIMARY KEY, BranchName VARCHAR(250)); --THIS CREATES THE MERCHANT TABLE:CREATE TABLE Merchant ( MerchantNbr INT PRIMARY KEY, MerchantName VARCHAR(250)); -- Insert test data…Create a view of the Join of Deposit and Withdraw transactions to Bank Branch UNION with the join of Bill Payment and Debit Purchase, or Return transactions to Merchant (i.e., all transactions with appropriate reference name.). BranchNbr stores RefNbr of either 'D', OR 'W' transactions, and MerchantNbr stores RefNbr of either 'B', 'P' or 'R' transactions. List of each Account showing the first Transaction date, type, and amount. (Hint: This is a correlated sub-query.) Count and Total Amount for each Transaction Type within each Account (Hint: This is an extended GROUP BY.) PLEASE DONT NOT COPY THE EXISTING SOLUTION ON BARTLEBY IT IS WRONG AND DOES NOT WORK AND IS INCOMPLETE. GIVEN THE BELOW: --THIS CREATES THE BANK BRANCH TABLE: CREATE TABLE BankBranch ( BranchNbr INT PRIMARY KEY, BranchName VARCHAR(250)); --THIS CREATES THE MERCHANT TABLE: CREATE TABLE Merchant ( MerchantNbr INT PRIMARY KEY, MerchantName VARCHAR(250)); --THIS CREATES THE TRANSACTION…
- 4. Display the class roster, including student name, for all students enrolled in section 2714 of ISM 4212 (display StudentID, StudentName, CourseID, and SectionNo, use inner join): 5. How many courses in section 2714 during semester I-2021? 6. How many students were enrolled in section 2714?1- List all the users and their card name using union2- List all the users and their card name using Intersection 3- List all the card numbers with owner names and scheduled transactions, in case the user hasnever used scheduled transaction show null or zero in the transaction column. (Hint use ISNULLfunction)Changing the. EmployeeID = 1 to 10 in the table Employee. If it is rejected, explain EMPLOYEE( EmployeeID, EmployeeName, SupervisorID, DepartmentID) PROJECT (ProjectID, EmployeeID) DEPARTMENT( Department ID, DepartmentName) CREATE TABLE EMPLOYEE ( EmployeeID INT PRIMARY KEY, EmployeeName VARCHAR(50) NOT NULL, SupervisorID INT DEFAULT 9, DepartmentID INT. DEFAULT 6, FOREIGN KEY (SupervisorID) REFERENCES EMPLOYEE (EmployeeID) ON DELETE SET DEFAULT , FOREIGN KEY (DepartmentID) REFERENCES DEPARTMENT(DepartmentID) ON UPDATE SET NULL ); CREATE TABLE PROJECT ( ProjectID INT PRIMARY KEY, EmployeeID INT DEFAULT 9, FOREIGN KEY (EmployeeID) REFERENCES EMPLOYEE (EmployeeID) ON DELETE SET NULL ON UPDATE CASCADE ); CREATE TABLE DEPARTMENT( DepartmentID INT PRIMARY KEY, DepartmentName VARCHAR(50) EMPLOYEE EmployeeID EmployeeName SupervisorID DepartmentID 6 A 7 6 7 B 8 6…
- Which normal form requires that, no non-key attribute should functionally depend on a part of the primary key? 3rd Normal Form 4th Normal Form 2nd Normal Form 1st Normal FormEmp:- Id is Primary keyProject:- EmpId foreign key.Find out the output of the left outer join, right outer join and inner join.Take the below columns in output:-Emp table ID, name.Project table projectID, NAMEWrite the SQL command for followingi) Teams ( Teamcode , Teamname, Clubname, total_member, dateofstart, teammanager,teamcoach)ii) Players (Teamcode, playername, dateofbirth, specialposition, Numberofgoal, number of tournaments, Tshirtno)iii) Tournament (Tournament_code, Tname, Year, Hostcountry, numberofteams, winnerteam, goldenboot)iv) Tournament_teams (Tournament_code, teamcode, totalyellocard, totalredcard, numberofgoals)v) Matchdetail (tournament_code, Mtcode, Team1code,team2code, winnerteamecode, matchdate ,team1goal,team2goal,refree)a) Write commands to create the above tables.Teamcode in player table is primary key.Teamcode in players, tournament_Team table is foreign key.b) Show the players of winner team of the year 2010.c) Show the team details of the team which got maximum yellocard.d) Show the team name of the team which won with maximum goal difference with the opposite team in a match.e) Show the details of the oldest team
- please use the picture to answer the following question Normalize below user view to the third normal form. Show all steps (UNF, 1NF, Dependencies, 2NF, 3NF).Create a view of the Join of Deposit and Withdraw transactions to Bank Branch UNION with the join of Bill Payment and Debit Purchase, or Return transactions to Merchant (i.e., all transactions with appropriate reference name.). BranchNbr stores RefNbr of either 'D', OR 'W' transactions, and MerchantNbr stores RefNbr of either 'B', 'P' or 'R' transactions. List of only the Accounts that have multiple Clients associated Provide a count and total amount of Transactions for each Type Description PLEASE DONT NOT COPY THE EXISTING SOLUTION ON BARTLEBY IT IS WRONG AND DOES NOT WORK AND INCOMPLETE. GIVEN THE BELOW: --THIS CREATES THE BANK BRANCH TABLE: CREATE TABLE BankBranch ( BranchNbr INT PRIMARY KEY, BranchName VARCHAR(250)); --THIS CREATES THE MERCHANT TABLE: CREATE TABLE Merchant ( MerchantNbr INT PRIMARY KEY, MerchantName VARCHAR(250)); --THIS CREATES THE TRANSACTION TABLE: CREATE TABLE Transaction ( TxNbr INT PRIMARY KEY, AccountNbr INT,…Create a view of the Join of Deposit and Withdraw transactions to Bank Branch UNION with the join of Bill Payment and Debit Purchase, or Return transactions to Merchant (i.e., all transactions with appropriate reference name.). BranchNbr stores RefNbr of either 'D', OR 'W' transactions, and MerchantNbr stores RefNbr of either 'B', 'P' or 'R' transactions. List of only the Accounts that have multiple Clients associated Provide a count and total amount of Transactions for each Type Description PLEASE DONT NOT COPY THE EXISTING SOLUTION ON BARTLEBY IT IS WRONG AND DOES NOT WORK AND IS INCOMPLETE. GIVEN THE BELOW: --THIS CREATES THE BANK BRANCH TABLE: CREATE TABLE BankBranch ( BranchNbr INT PRIMARY KEY, BranchName VARCHAR(250)); --THIS CREATES THE MERCHANT TABLE: CREATE TABLE Merchant ( MerchantNbr INT PRIMARY KEY, MerchantName VARCHAR(250)); --THIS CREATES THE TRANSACTION TABLE: CREATE TABLE Transaction ( TxNbr INT PRIMARY KEY, AccountNbr INT,…











