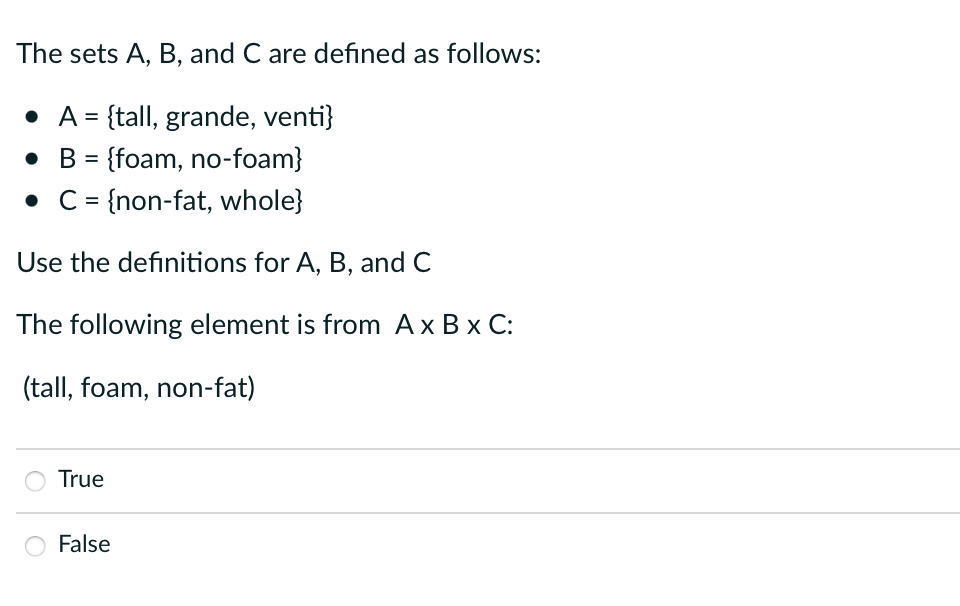
The sets A, B, and C are defined as follows: • A = {tall, grande, venti} • B = {foam, no-foam} • C = {non-fat, whole} Use the definitions for A, B, and C The following element is from A x B x C: (tall, foam, non-fat) True False
Q: 4.11 LAB: Number pattern Write a recursive function called print_num_pattern() to output the…
A: Number pattern using recursive function using the python programming language see the below code
Q: Write a C# Windows Form program that asks the user to enter a name (in a TextBox) and displays the…
A: Introduction C#: C# (pronounced "C Sharp") is a modern, object-oriented programming language…
Q: Participating in this course will help you get a deeper understanding of blogs, social media, and…
A: According to the information given. We have to define the deeper understanding of blogs, social…
Q: Text classification is one of the most commonly used text mining tasks. In this discussion, download…
A: Text classification is the process of categorizing text data into predefined categories based on its…
Q: primes.py: Write a program to find all prime numbers less than an integer n, where n is given as a…
A: 1. Get a number n as an argument from the command line2. Initialize a loop from 2 to n3. Within the…
Q: Please for thi question, kindly explain into details for me. This seems a new topic to me…
A: Introduction Bit strings are sequences of binary digits (bits) used in computing. They can be used…
Q: The word "Identifier attribute" seems to be thrown about a lot without a clear definition.
A: The term "Identifier attribute" shall be defined as follows: Solution: Identifiers, which are…
Q: 2. When the user continues, the console should display two static reports. One should show the…
A: Algorithm: Step 1: Start.Step 2: Declare variables to store input.Step 3: Declare variables to store…
Q: Mobile networks can't be built without using wireless technology in some capacity. For cell signal…
A: Given: It is challenging to construct a mobile network without utilising wireless technology in some…
Q: When a deadlock is identified, a strategy has to be developed to break it.
A: When several cycles are delayed down because each interaction is hanging onto an asset while it…
Q: That's where the toList method comes in. When called, this method returns a List representation of…
A: Copy function's internal part import java.util.List; import java.util.ArrayList; public class…
Q: illustrates the algorithm for search procedure on a skip list S for a key K. The algorithm employs…
A: Skip list is a type of data structure which consists of two types of layer which are lowest layer…
Q: It's important to talk about OOP ideas. How well do they fit within the C++ code overall?
A: General OOP concepts: Data Abstraction: Representing important properties without background…
Q: Intelligent modems can dial, hang up, and reply to incoming calls automatically. Who is accountable…
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: What are the two most common wireless networking technologies?
A: Dear Student, The answer to your question with sufficient explaination is given below -
Q: What is the purpose of discrete event simulation?
A: Discrete event simulation (DES) is a widely used approach in modeling and simulation to analyze and…
Q: To the contrary, could you provide a more comprehensive summary of the metrics associated with…
A: Given that: Could you offer a more complete view of software development metrics? Detail everything.…
Q: Analyze Ubuntu in relation to other Linux distributions. In what ways do you believe your proposal…
A: An operating system is a programme that runs application programmes and acts as a communication…
Q: An Optimal Tour Considering a Multimodal Transportation System – The Traveling Salesman Problem…
A: The Traveling Salesman Problem (TSP) is a classic optimization problem where a salesperson wants to…
Q: How simple or complicated is it to add or delete users in Windows 10 and Linux?
A: In accordance with the inquiry, we must determine the difficulties associated with adding and…
Q: Why is it that the bulk of multimedia content on the Internet today is sent via TCP rather than UDP?
A: Both UDP and TCP: The full name of "UDP" is "User Datagram Protocol." It allows the raising…
Q: In an IoT web stack, how important are protocols like UDP and IPV6? What is the difference between a…
A: Introduction: IoT or Internet of Things has revolutionized the way that we interact with devices and…
Q: In what four different ways is discrete event simulation capable of being depicted as critical?
A: Each associated event in the process occurs at a certain moment. The event's occurrence is what…
Q: Suppose we are performing a binary search on a sorted vector initialized as follows: // index Ø…
A: Here is your solution -
Q: Compress the following IPv6 addresses into their shortest expression…
A: Compress the following IPv6 addresses into their shortest expression…
Q: When it comes to linked files, what purpose does defragmentation serve?
A: The answer is given below step.
Q: What options do we have for semantic representations in NLP systems?
A: Introduction of NLP: NLP is a field of AI that focuses on the analysis, comprehension, and…
Q: there a way to utilize the internet for healthy living that really helps the person using it? What…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: Python Can you explain what you did with comments class linkedQueue: class _Node: def…
A: Given code: class linkedQueue: class _Node: def __init__(self, value, next = None):…
Q: What does it mean when we say "computer"?
A: Introduction In this question we are asked about computers
Q: Part 2: Development of a Java Project The ultimate goal of this section is to generate a Java based…
A: The following set of classes is developed: LibraryBook class which is the super class of TextBook…
Q: How is it possible for a single individual to be in charge of coordinating a distributed denial of…
A: A single person can orchestrate a distributed denial of service (DDoS) attack by utilizing a botnet,…
Q: please use c# (FormatExceptions) Create an app that inputs miles driven and gallons used, and…
A: Algorithm for "MileageCalculator" Program that written in C# : Start Display "Enter the miles…
Q: What kind of networks do universities often use? The question is, how does one variety vary from…
A: Introduction: Local area networks (LANs) link computers in a limited space, such as a classroom or…
Q: To what extent do Linux and Mac OS machines differ in how they handle software updates?
A: Introduction How are updates for Linux and Mac OS systems applied? Answer In Linux, there are two…
Q: The Problem: Strange things are happening to one of your classes. Data is getting corrupted somehow.…
A: Given: Strange things are happening to one of your classes and data is getting corrupted. Task:…
Q: What is the best tiered approach to building an OS? The pros and cons of this approach are…
A: Answer is
Q: Give an in-depth explanation of how memory management is affected by dynamic loading vs static…
A: Explain memory management's dynamic and static loading. Loading moves a programme from secondary…
Q: This is because regular In order to input a series of integers into an ArrayList, you'll need to use…
A: In order to input a series into an Arraylist, you will need to use a add() method and toArray…
Q: Where can I get a list of the three most important principles of the current software development…
A: Introduction : Software development is the process of creating, designing, coding, testing,…
Q: Discover how Ubuntu stacks up against other popular Linux variants. Is it for this reason that the…
A: Introduction: Ubuntu, Debian, and CentOS are some of the Linux distributions that are most…
Q: Gaussian Discriminant Analysis produces a classifier that measures the distance of a test data point…
A: The distance measures with respect to the centroid referred as the Mahalanobis distance. LDA(Linear…
Q: How do you handle the life cycle of a Linux distribution, and what are Linux distributions?
A: Distributions Windows, for example, bundles all code. Select a version. Linux is different. Linux is…
Q: Please code in JAVA Declare a decimal variable named average. This variable will be the numerical…
A: 1) Below is simple java program to calculate and display average of 3 numbers(a, b and c) It…
Q: Fix the following method printEvenIndex so that it will print out the Integers at even indices of…
A: Algorithm of the code: 1. Instantiate an empty ArrayList called values2. Create an array of integers…
Q: List some general categories of networks. Explain your idea by showing relevant examples and images.…
A: Digital devices connected in a network may exchange information. There are primarily four different…
Q: Explain the character set in simple terms
A: INTRODUCTION: The essential component that permits the display of text, numbers, and symbols on a…
Q: To what extent should several points of view be included when modeling software systems?
A: Software systems modeling refers to the process of creating abstract representations of a software…
Q: Entities within databases take on many forms. Provide three examples of entities you may encounter…
A: Introduction : Entities in a database are the objects, people, concepts, or events that are…
Q: The internet is held up as a model of effective use of ICT (information and communication…
A: ICTs stand for information and communication technologies where technological tools and resources…
please answer
A computer is a digital electronic machine that can be programmed to automatically perform a series of arithmetic or logical operations (calculations).
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Python You and your neighbor have equal sized gardens. Your gardens are represented as 2D-lists, where garden[i] [j] gives an element at position (i, j). Every element in a garden is represented as an string, and can be "grass", "moss", "strawberry" , "rock", "raspberry". Latley you have noticed more moss and rock in your garden and espects its to be your neighbor. To fix it, complete the function clean_mygarden(my_garden, neighbors_garden) At the end , swap every rock and moss in your garden with the first stawberry and raspberry from neighbor (they dont need to be at the same position MAKE A FUNCTION "find_items" that inputs two arguments: (garden, item) , and returns a (i, j) position as a tuple if item is in garden. If not, return None. Make a function swap_items that swaps two elements between two gardens. Let the function Input these arguments (garden1, garden2, pos1, pos2), where pos1 and pos2 is (i,j) tuples.def swap_items(garden1,garden2,pos1,pos2):Here you are not going…Design a function that consumes a natural number and produces a list ofstrings describing that many seats at a table. For example, (seats 3) shouldproduce the list (list "Seat 1" "Seat 2" "Seat 3"). Include all recipe elements. The body of your function definition MUSTUSE the build-list built-in abstract function. You may optionally use anadditional built-in abstract function. Using DrRacketRelational Thinking sets 25 students attend a programming workshop. 15 students study Python. 14 students study Java. 5 students changed to another field of study. How many students study both Java and Python. Use set diagrams to explain your answer. Draw the diagram showing the relationship A ⊆ B Draw the diagram to show the relationship A ∩ B Let E be the set of even numbers, and let P be the set of prime numbers. Use set notation to express the following statement: “2 is the only even prime number.” List the set operations most closely matching disjunction, conjunction, negation, conditional (if then), biconditional (iff if and only if)
- python assignment Matrix class Implement a matrix class (in matrix.py). a) The initializer should take a list of lists as an argument, where each outer list is a row, and each value in an inner list is a value in the corresponding row. b) Implement the __str__ method to nicely format the string representation of the matrix: one line per row, two characters per number (%2d) and a space between numbers. For example: m = Matrix([[1,0,0],[0,1,0],[0,0,1]]) print(m)> 1 0 0> 0 1 0> 0 0 1 c) Implement a method scale(factor) that returns a new matrix where each value is multiplied by scale. For example: m = Matrix([[1,2,3],[4,5,6],[7,8,9]])n = m.scale(2)print(n)> 2 4 6> 8 10 12>14 16 18print(m)> 1 2 3> 4 5 6> 7 8 9 d) Implement a method transpose() that returns a new matrix that has been transposed. Transposing flips a matrix over its diagonal: it switches rows and columns. m = Matrix([[1,2,3],[4,5,6],[7,8,9]])print(m)> 1 2 3> 4 5 6> 7 8…Define the 3 bolded functions for the following DynIntStack (linked list): class DynIntStack {private: struct Node { int value; // Value in the node Node *next; // Pointer to the next node }; Node *top; // Pointer to the stack toppublic: DynIntStack() { head = nullptr; } void push(int); //assume this is already defined void removeTop(); // removes the top element without returning it int topValue(); // returns the top element without removing it bool isEmpty() { return head == nullptr; } bool isFull() { return false; } void pushMany(int values[], int n); //add n values from the array}; Hints: void removeTop() (hint 3 lines of code) int topValue() (hint 1 line of code) void pushMany(int values[], int n) (hint 2 lines of code, use a for loop, call another function)What are disjoint sets?a. Disjoint sets are sets having common elements.b. Disjoint sets are sets having no common elements.c. Disjoint sets are sets that have only one elements.d. Disjoint sets are sets containing all the elements being considered.
- a) The preorder traversal of a Binary Search Tree (BST) is given below.40 20 10 15 25 30 60 50 80 100 Draw the BST and briefly explain the process you followed to build the tree. b) Write a function f1 that takes the root of a binary tree as a parameter and returns the sum of the nodes, which are the left child of another node. The root of the tree is not a child of any node. Consider the following class definitions while writing your code.class Node {public:int key;Node* left;Node* right;};If S = {1, 2, 3, 4, 5 }, A={2 ,4 } B={1, 3, 5 } C= {2, 5}. The sets corresponding to event (A’ or C) is _____ What are the elements of the sets corresponding to event (B’ and C) = _____ Note: Write your answer inside a pair of braces without space in between elementsDefine the function (doubleBubbleLst lst). This function should resolve to a list of sublists, where each sublist holds a single element from lst and all sublists from lst are also bubbled, so that every list and sublist has no atoms. This is the deep recursion version of bubbleLst. For example: (doubleBubbleLst '(1 2 (3 4)) ) resolves to '((1) (2) (( (3) (4) ))).
- Write a struct Student that has member variables: (string) first name, (int) age and (double) fee. Write the functions as described in the class for the following purposes.1. Write a c++ function to create a dynamic sorted (in ascending order according to the age)doubly linked list, where the data component of each node is an instance of the structStudent.2. Write a function to insert the instances in the linked list. You also need to write a function to find the spot for insertion of the nodes.3. Write a function to remove the node from the linked list.4. Write a function to count the elements of the linked list.5. Write a function to determine check whether an element belongs to the linked list.6. Write a function to print the linked list (from head node) on the console.7. Write a function to print the linked list (from tail node) on the console. Implement the above functions as follows.Initially, the list must have five nodes that are the instances of the struct whose member…in C++... kth Element Extend the class linkedListType by adding the following operations:a. Write a function that returns the info of the kth element of the linked list. If no such element exists, terminate the program.b. Write a function that deletes the kth element of the linked list. If no such element exists, terminate the program. Provide the definitions of these functions in the class linkedListType. PLEASE DON'T reject this question, this is the whole question that I have... so please do it however u can, Thank you!Discrete Mathematics Simplify each of the following expressions. Do not use the set difference operator in your simplifications. Note that the set U in the second item is the universal set, which includes all elements. Shade the indicated regions of the following Venn diagrams. please see attached photo for more details











