Boolean Algebra Prove that A+A'B+AC' (B+C)(B+D) =A+B
Q: No idea. Internal versus external fragmentation.
A: Fragmentation: The huge data is fragmented into several packets during this operation. As a result,…
Q: What are the main distinctions between local-area and wide-area networks for distributed databases?
A: Introduction: A computer network known as a local area network (LAN) is restricted to a small…
Q: How can I guard against falling prey to phishing?
A: Phishing : It is a type of online fraud that involves tricking people into providing sensitive…
Q: Which of the following is a method of detection: a) sniffing the network; b) conducting surveillance…
A: Both sniffing the network and conducting surveillance by means of a wiretap are methods of detection…
Q: The process of migrating a database from one server to another is loaded with potential danger.
A: Traditionally, when it comes to data infrastructure, many businesses have kept their servers…
Q: Create a list of DNS records organized by the kind of record that each record contains. For each of…
A: Here is a list of DNS record types and their usage: A Record (Address Record): This record maps a…
Q: Where can ICTs improve business and education? Any examples?
A: The Answer is in given below steps
Q: Please explain good data input field foundations. What situations warrant breaking these norms?
A: Say it like it is: Although this may seem obvious, it must still be expressed. Many diagrams…
Q: There are a few distinct varieties of flow charts, the most common of which are logical data flow…
A: Introduction: Flow charts are a popular visual representation tool used in various fields to depict…
Q: Since compiled code has to be correct and efficient at the same time, what aspects of a compiler…
A: 1) A compiler is a type of computer software that translates source code written in a programming…
Q: Why not use DNS as a distributed database instead, and what are the advantages of doing so?
A: Introduction: As a means of finding a solution, a decentralised method for resolving domain names…
Q: "Pictures are saved in a database, and the design/structure we've chosen includes some highly…
A: According to the information given:- We haev to define the above scenario.
Q: In order to prevent hackers from gaining access to client information, what kinds of precautions…
A: Introduction: In this day and age, there are more security dangers than ever, but sadly, many…
Q: Split two CRC decoder instances.
A: Сyсliс Redundаnсy Сheсk (СRС) : R is a different approach to determining whether the received form…
Q: how can we represent restaurant shop education etc in this problem?
A: Introduction: The above question asked about the representation of restaurant, shop ,education…
Q: What distinguishes a logical data flow diagram from a physical data flow diagram?
A: Answer: Introduction logical data flow focus on the activity and it describe the necessary data…
Q: How exactly does one go about reading, deleting, or searching a list of user ids and passwords when…
A: The Binary Search Tree is a data structure that consists of a one-site binary tree and has the…
Q: A paragraph about abstraction, encapsulation, information hiding, and formal interfaces. C++ classes…
A: In object-oriented programming (OOP), abstraction, encapsulation, information hiding, and formal…
Q: The intermediate step is between the database and client servers.
A: The intermediate stage is the layer that lies between the client servers and the database.
Q: Three-schema architecture converts requests into outcomes at all three levels.
A: The three-schema architecture is a database design approach that separates the conceptual, external,…
Q: What are the potential downsides associated with moving the database from one server to another?
A: Introduction: Moving database from one server to another is known as database migration. It is very…
Q: Examine an airline's snapshot-isolated data warehouse. The airline may tolerate a nonserializable…
A: Introduction: In the field of data warehousing, an airline's snapshot-isolated data warehouse is a…
Q: No direct connections between external entities and the database are permitted. This is one of the…
A: A Data Flow Diagram (DFD) visually represents how data flows through a cycle or framework. DFDs…
Q: Split two CRC decoder instances.
A: Syslis Redundancy Shesk (SRS): SRS is an alternative approach that may determine whether or not the…
Q: applications for a private intranet or an externally facing extranet.
A: Intranet: Intranet is a private internal business network which enables the people in that business…
Q: Which two systems management tools are more useful?
A: System administrators should use a variety of tools. Some instruments may be cost-effective, while…
Q: Job requirements: Find research articles by famous authors (lecturers, teachers, researchers,…
A: As per our guidelines, we are supposed to answer only one question. Kindly repost the remaining…
Q: Cryptography's private and public keys—the what's difference?
A: Cryptography refers to security communication techniques that only allow the originator and intended…
Q: How do you backup your database as a DBA
A: A database backup is a copy of the database stored on a separate server in case the primary server…
Q: An ancient programming adage advises against coding. That means what?
A: Don't give in to the urge to code: This implies a software developer must first grasp the problem,…
Q: Where can ICTs improve business and education? Any examples?
A: Introduction: I didn't learn the meaning of the term "Information and Communication Technology"…
Q: Difference between database replication and fragmentation?
A: Database replication and fragmentation are two common techniques used in database management systems…
Q: What distinguishes a wide-area network from a local area network for a distributed database to…
A: A distributed database is refers to a collection of multiple interconnected databases that are…
Q: What are the potential drawbacks of moving a database off of a server and into another location?
A: Many businesses have traditionally kept their servers on-site regarding data infrastructure. These…
Q: How do local and wide area networks differ when setting up a distributed database?
A: The main difference between local area networks and wide area networks when setting up a…
Q: How can a distributed database structure distinguish a local-area network from a wide-area one?
A: A distributed database structure can distinguish a local-area network (LAN) from a wide-area network…
Q: What is the function of the Cache Fusion feature in Oracle RAC?
A: Oracle RAC stands for Real Application cluster.
Q: Problem 2.1.5 (Find the address ranges). For each of the three main classes (A,B,C) find the precise…
A: For classful addressing there are classes that includes Class A, Class B, Class C mainly. Given…
Q: What's required for resource management?
A: In large-scale systems and dispersed environments, resource management is a crucial component of…
Q: How may technology affect education?
A: Technology has positive and negative effect on education.
Q: What's next for cloud computing
A: Throughout the last 10 years or something like that, the cloud has turned into the predominant…
Q: Create a list of DNS records organized by the kind of record that each record contains. For each of…
A: The Answer is in given below steps
Q: What is the key distinction between non-static, static, read-only, and constant variables in the C#…
A: In this question we have to understand What is the key distinction between non-static, static,…
Q: Logical data flow diagrams demonstrate data flow logically, unlike physically organized ones.…
A: Using reason as the basis, DFD: Focuses on issues that arise in the corporate world.The…
Q: Database encryption levels are mentioned.
A: 1) Database encryption is the process of transforming sensitive data stored in a database into an…
Q: at hazards are associated with moving a database from one server to another?
A: Moving a database from one server to another can be a complex process, and there are several hazards…
Q: When both relations are not physically sorted but have an index on the attributes being combined, a…
A: In this question we have to understand the term provided where when both relations are not…
Q: Give an overview of agile methods based on yearly surveys and agile product company surveys?
A: Scrum model: Agile methodology is a development and testing approach that encourages frequent…
Q: In many database systems, threads use shared memory to communicate. It's crucial to know whether…
A: Introduction: A shared-memory multiprocessor architecture is one that consists of only a few…
Q: An ancient programming adage advises against coding. That means
A: The adage "if it ain't broke, don't fix it" is often cited as an argument against making changes to…
Answer the given question with a proper explanation and step-by-step solution.
sub:Digital logic design
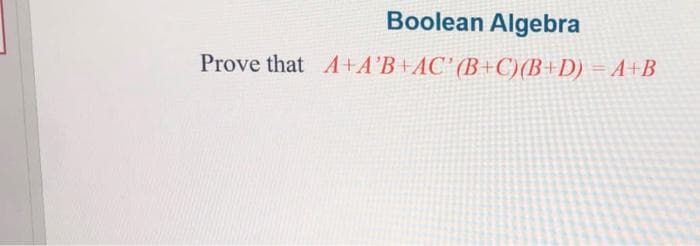
Step by step
Solved in 2 steps

- What are the ramifications for computer scientists of knowing Boolean algebra?Question 6 Computer Science Simplify the following Boolean Algebra expression using Boolean Identities (where ' means "not") (A+B+C+D')(E+A)(E'+B+C+D')What are the reasons why knowing Boolean algebra is crucial for computer scientists?
- Draw the logic diagram corresponding to the following Booleanexpressions without simplifying them: B C ′ + A B C + A C D + B D ( A + B ) ( C + D ) ( A ′ + B + D )Computer scientists must understand Boolean algebra for several reasons.For what reasons is it critical for computer scientists to understand Boolean algebra?

